Quick Answer
Start with a controls-first rollout: map the payout path, enforce pre-disbursement gates, and require evidence for approvals, status, and ledger treatment before scaling. For nonprofit teams tackling nonprofit financial automation grant-making disbursements compliant decisions, the practical sequence is one cohort, one control matrix, and one reproducible reconciliation cycle, then expansion only after failed or reversed payouts keep linked audit history and documented closure.
Key Takeaways
- Map intake-to-closeout flow before tool selection, and label every handoff where CRM, spreadsheets, and accounting diverge.
- Treat any control as missing if it cannot produce retrievable evidence such as approval history, policy-gate output, and closure notes.
- Choose architecture by failure pattern: rising volume with frequent exceptions favors centralized orchestration, while low stable volume favors control hardening first.
- Enforce fund, grant, and reporting-period tagging before release so month-end close does not depend on manual relabeling.
- Scale only after sampled payouts can be reconstructed end to end and high-risk exceptions are resolved.
What Compliant Grant Disbursement Operations Require#
Nonprofit teams do not need another generic automation pitch. They need a grant disbursement process that answers basic questions clearly: why a payout went out, which rules applied, and what evidence shows it was handled correctly.
This article treats compliant disbursements as a controls problem first, not a speed problem. In the U.S. federal award context, 2 CFR 200.303 requires recipients and subrecipients to establish, document, and maintain effective internal control over the award. It also requires prompt action when noncompliance is identified. If your process cannot show those controls in records, approvals, and remediation notes, it is not ready to scale.
The goal here is practical: give finance, ops, and engineering a shared path for running grant disbursements while managing operational risk. You will see what to implement first, what to defer, and how to show compliance evidence to internal and external reviewers.
Use this as an early checkpoint on one recent payout. Ask whether your team can retrieve, without stitching together inbox threads:
- award terms
- recipient checks
- approval history
- payment status
- ledger treatment
- exception notes
If not, that gap matters more than adding another dashboard or payout option. A process that sends payments but cannot produce evidence on demand carries more risk.
Program and award requirements are not uniform. Federal guidance states that grant award processes vary by program, and 2 CFR 200.211 requires award terms and conditions to define how performance will be assessed. Controls that work for one grant, funder, or program design may not transfer cleanly to the next.
Jurisdiction adds another layer. State nonprofit obligations differ, and fundraising rules can vary state to state; the majority of states (40) require charitable solicitation registration. Depending on your organization and program, you may also face separate federal, state, contractual, or tax considerations, including UBTI in some unrelated business activities. Use this article as an operating model, not legal or tax advice.
The working recommendation is simple: automate repeatable checks and evidence capture before you automate for scale. Start with documented policy gates, approval paths, transaction records, and reconciliation proof. Then optimize once exceptions and failures leave a clear trail and are resolved promptly.
Related reading: Accounts Payable Automation for Dummies for Platform Operators.
What compliant nonprofit financial automation actually means#
Compliant disbursement automation is not just about speed. It is about proving, payout by payout, which award rules applied, what approvals and controls were required, what source records support the transaction, and how it was classified in reporting.
- Grant disbursements: In the federal context, this is the process of requesting and receiving payment under an award, not just sending money. That is why payment timing controls belong in the design. Under 2 CFR 200.305, advance payments are limited to the minimum amounts needed.
- Grant compliance: Compliance is documented evidence, not intent. For federal awards, 2 CFR 200.303 and 2 CFR 200.302 center on internal controls plus records that identify amount, source, and expenditure, supported by source documentation.
- Fund accounting: "Restricted" and "unrestricted" treatment should stay consistent from posting through reporting and reconciliation, consistent with reporting net assets with donor restrictions and without donor restrictions (ASU 2016-14). If classification lives only in summaries or manual cleanup, the process is fragile.
- Reporting and transparency: Real-time reporting is not universally required by law, but explainable visibility is increasingly expected. Public inspection obligations and donor-facing accountability reviews raise the bar from narrative updates to retrievable evidence.
That definition matters because it shapes every later decision, from workflow design to tool choice to reconciliation.
Map the end-to-end money path before buying tools#
Map the full money path before procurement, because software cannot fix steps you cannot trace. If you cannot show how a grant moves from eligibility review through payout and closeout, you are likely automating blind spots.
Grants.gov frames the grant lifecycle in three phases, which can serve as a baseline structure for your workflow map: pre-award, award, and post-award. In practice, map your flow from request to award, reporting, stakeholder engagement, and disbursement receipt, with explicit handoffs across teams.
| Stage | What to document | Minimum check |
|---|---|---|
| Intake and eligibility review | submitter, program rules, required recipient data, supporting records | complete recipient record and policy match |
| Compliance checks | budget availability, restrictions, approval requirements, hold reasons | pass/fail result with timestamp |
| Disbursement approval | approver, approval date, amount, funding source | named approver and review evidence |
| Payout execution | payment method, transfer date, amount, recipient, status | status tracked with amount, recipient, dates, and status |
| Post-payout reporting and closeout | confirmation, ledger posting, exception notes, reporting outputs | payout tied to reporting period and closeout record |
Internal controls are meant to function as checks and balances, so each checkpoint should have an owner and retrievable evidence. If eligibility is approved, identify the record that proves it. If posting is complete, show the trace back to the approved grant and fund classification.
Find the fracture points#
A lot of process risk shows up at system boundaries, not just in the happy path. Map every system jump explicitly, especially when intake sits in CRM, approvals happen in Excel or email, and posting happens in accounting. Also mark every export, re-entry, upload, and manual match.
Disconnected systems and endless reconciliations are described in nonprofit finance commentary as recurring close pain points. Some integration guidance treats CRM-to-accounting integration as foundational, with a goal of a process where no human manipulation is required. Whether or not you can get there immediately, it is a useful target state for control design. At each handoff, keep one practical record: the source system, destination system, transferred fields, and who resolves mismatches.
Define failure states before they happen#
Do not wait for the first bad payout to decide how failure works. Define failure states up front, assign a response path to each one, and define the evidence you retain so the resolution is auditable:
- missing recipient data before approval
- failed disbursement after release
- duplicate payout attempt from retry or re-entry
- delayed confirmation that leaves finance unsure whether to post, reverse, or wait
What this tells you before procurement#
If Excel is carrying approval logic or manual reconciliation is determining final accounting treatment, fix that operating model before adding more payout rails. That is not just an efficiency problem. It is a control signal, and it tells you where the control state should live next.
For a step-by-step walkthrough, see Best Excel Financial Modeling Tools by Tier: Auditing, Automation, and Scenario Analysis.
Decide your system architecture and ownership model#
Choose the architecture that makes control evidence easy to retrieve, not the one with the best demo. If your process already spans grant tools, accounting, and spreadsheets, decide whether you will keep stitching records together or move to a model that centralizes approval state, payout status, and audit evidence.
For federally funded programs, this is a compliance design decision. 2 CFR 200.303 requires documented internal controls, and 2 CFR 200.302 requires source-backed records. Your model has to let you prove who approved what, what was paid, and which source record supports each posting.
| Option | Best fit | Main upside | Main risk | What to verify before you commit |
|---|---|---|---|---|
| Patching point tools, such as Foundant GLM plus QuickBooks Online | Lower complexity operations with stable patterns | Less disruption and faster near-term rollout | More reconciliation points and status drift across systems | Foundant's QuickBooks Online integration is a paid add-on, and its documentation says the systems do not sync automatically. Confirm who owns sync, mismatch handling, and evidence retrieval. |
| Platform-led consolidation, such as Gruv modules | Growing payout operations with recurring exceptions and stronger evidence needs | Fewer silos and clearer end-to-end status and audit retrieval | Migration effort and change management | Validate one full disbursement path, from approval through posting and exception handling, in one view, including status history and source records. |
| Custom orchestration around the existing stack | Teams that must keep current grant, CRM, and ERP systems but need tighter orchestration | Keeps existing systems while improving process control | Ongoing engineering load and brittle cross-system status if not maintained | Fluxx describes the common split between approvals and financial operations. Confirm how payment status, retries, and reconciliation exceptions are surfaced without spreadsheet or email fallback. |
Pick the model that matches your failure pattern#
A patched stack can work when your team can still trace each payout cleanly. The warning sign is when the record of truth appears only after export, spreadsheet edits, and re-upload.
If your process depends on repeated exports plus manual spreadsheet correction, treat that as a consolidation signal before adding new payout rails. Salesforce AppExchange positioning for Accounting Seed makes the same point in practical terms: a Salesforce-native accounting design is meant to reduce siloed data and reconciliation time.
Custom orchestration is viable only if engineering can own reliability over time. Fluxx also notes that disconnected systems can lead to delayed disbursements, manual workarounds, and unclear payment status. Plan for those failure modes. Do not treat them as edge cases.
Make ownership explicit in writing#
Control design breaks down fast when ownership is implied instead of named. Grants-oriented internal control guidance points to written assignment of responsibilities, so avoid vague shared ownership. A practical starting split is:
- Assign a named owner for policy rules, approval requirements, fund coding, and evidence standards.
- Assign a named owner for execution timing and exception handling.
- Assign a named owner for integration reliability, status visibility, and divergence alerts.
This is a starting model, not a universal rule. Adjust it to fit your team, but make it explicit enough that blocked payouts, missing documentation, and record mismatches have clear decision and resolution paths.
Use a simple decision rule#
As a practical heuristic, if payout volume and exception pressure are rising, centralizing orchestration and audit evidence may reduce risk. If volume is low and stable, strengthening controls before a major migration can be a reasonable first step.
Use a quick sample to test the choice. Pull five recent disbursements and try to retrieve, in one sitting, the approval record, source support, payout status history, and accounting outcome. If that requires hunting across exports, spreadsheets, email, and accounting systems, the issue is both architecture and ownership.
Build the minimum control set before you scale payouts#
Set the control baseline before adding volume, and treat any control without auditable evidence as missing. If you cannot show who performed the check, when it happened, and which source record supports it, the process is not control-ready, even if payouts are moving.
For federal award programs, this is a compliance requirement: documented internal control and source-backed records are required. Outside federal awards, apply the same discipline as a control standard and align it to your funder terms and policies. Do not scale a payout path that depends on memory, inboxes, or spreadsheet comments as proof.
Start with a control matrix you can operate#
Start with a matrix that ties each risk to a concrete control, a named owner, and one retrievable evidence artifact.
| Risk event | Required control | Owner | Evidence artifact |
|---|---|---|---|
| Recipient is ineligible or incorrectly identified | Pre-disbursement recipient verification under policy, including entity checks and, where relevant, IRS TEOS review and OFAC SDN screening | Operations executes; finance defines policy | Verification record, TEOS result, screening result, timestamped audit log |
| Payout is charged to the wrong fund or exceeds budget | Budget-availability gate by restricted funds bucket and award budget before release | Finance | Fund coding record, budget check output, approval chain entry linked to award or grant |
| Unauthorized payout or policy bypass | Approval chains with required approver levels and policy-defined second-level approval for edge cases | Finance or program approver, with operations routing | Approval history, audit logs, documented exception record |
| Duplicate payout risk | Policy-defined duplicate screening before release and during post-payout review | Operations | Duplicate-check output, blocked-attempt log, exception handling record |
| Failed, reversed, or blocked payout remains unresolved | Exception handling with named owner, corrective action, and documented closure rationale | Operations, with finance signoff when policy or funds are affected | Exception case record, payout status history, closure notes, linked source documentation |
If "show me the proof" ends in chat history or tribal knowledge, the control is not in place.
Make pre-disbursement gates hard to skip#
Pre-disbursement gates should block release until checks pass. The minimum set is recipient verification, policy eligibility, budget availability in the correct restricted-funds bucket, and second-level approval for policy-defined edge cases.
Recipient verification should store the actual check outputs, not only a pass or fail label. Budget gating should confirm the payout aligns to the correct award or restriction category, not just total cash availability.
Second-level approval is a policy design choice, not a universal legal requirement. Define exactly when it is required so reviewers apply it consistently. Controls are incomplete at "submitted." After the payout, confirm status, apply any policy-defined post-payout duplicate checks, and close exceptions with documented rationale.
Status evidence should show the progression of payout states and tie the settled transaction back to the originating record. When duplicate flags or exceptions are cleared, keep the resolution note and owner decision in the record.
For federal awards, keep records long enough for review. The baseline is three years from submission of the final financial report. If approval chains, audit logs, and exception records cannot be exported and retained for that period, the control set is not durable.
With the control baseline in place, reconciliation becomes a test of whether those controls actually hold under pressure.
If your control matrix is defined and you need a system that can enforce policy gates with traceable payout states, review how Gruv Payouts is structured.
Set reconciliation rules that survive month-end pressure#
Reconciliation holds up under month-end pressure when fund accounting is enforced at payout, not repaired later. Tag each disbursement before release with its grant or award, fund classification, and reporting period. That helps keep activity in the correct fund and reduces the risk of blending resources with and without donor restrictions.
For federal awards, this is more than good practice: records must identify the amount, source, and expenditure of funds, and actual expenditures must be compared to budget by award. Your payout record should make three basics clear: which award was charged, which fund type it hit, and which reporting period it belongs to.
Make the daily check light and the month-end check formal#
Use daily checks to catch variance early, then run formal reconciliation monthly against source records such as bank statements. Daily checks are an operating design choice, not a universal legal requirement. A practical checkpoint set is:
| Cadence | Check | Article note |
|---|---|---|
| Daily | Status-to-ledger check: flag released, failed, reversed, or settled payouts that do not match expected posting state | Daily checks are an operating design choice, not a universal legal requirement |
| Daily | Classification check: flag payouts missing grant, fund type, or reporting period tags | Daily checks are an operating design choice, not a universal legal requirement |
| Month-end | Reconciliation: tie bank activity, payout records, and ledger balances | When possible, assign this to someone other than the person writing checks or making deposits |
Do not rely on dashboard status alone. Keep dated exports that show what was checked, what matched to source records, and which exceptions remained open.
Build a mismatch queue that forces follow-through#
Your mismatch queue should make unresolved variances visible and owned. For each item, store a reason code, owner, open date, and linked source record.
Typical categories include posted-not-settled, settled-not-posted, missing fund classification, budget mismatch by award, and uncleared reversals. Apply aging rules so items cannot roll into the next close silently. There is no universal nonprofit standard, but month-end guidance does call for investigating and resolving outstanding checks and uncleared deposits once they are 60-90 days old.
Shape outputs for the people who will actually use them#
Shape your reconciliation output around the people who have to act on it: controller close, board oversight, and donor-facing transparency.
Controller-facing output should show reconciled totals by grant, fund type, and period, plus aged exceptions and open items. Board-facing reporting can stay aggregated, but it should preserve the distinction between net assets with donor restrictions and net assets without donor restrictions so fiduciary review stays usable. For donor and public transparency, keep summaries consistent with filed disclosures, including the Form 990 public-availability three-year period.
Design exception handling so failed payouts do not become compliance incidents#
Exception handling should be treated as a compliance control, not just an ops queue. If you retry the wrong failure or close an item without evidence, you raise duplicate-payment, policy-breach, and sanctions risk.
Start by classifying failures by cause so response paths stay clear: data-quality errors, provider failures, policy blocks, and duplicate attempts. Keep a named owner and target response time for each category as an internal operating standard. Then verify the failure code, provider response, and payout status match before retry or closure.
Classify by cause and assign an owner#
Clear categories prevent bad retries and bad accounting. Data-quality errors usually mean incorrect or incomplete payout details. Provider failures are technical conditions such as connection errors, socket timeouts, TCP disconnects, and transient HTTP responses like 408, 429, and 5xx. Policy blocks include eligibility and sanctions outcomes. Duplicate attempts should stay separate because they can come from both retry behavior and true payment risk.
| Cause | What it means | Owner |
|---|---|---|
| Data-quality errors | Incorrect or incomplete payout details | Data ops or onboarding |
| Provider failures | Technical conditions such as connection errors, socket timeouts, TCP disconnects, and transient HTTP responses like 408, 429, and 5xx | Ops or engineering |
| Policy blocks | Eligibility and sanctions outcomes | Finance or program operations |
| Duplicate attempts | Can come from retry behavior and true payment risk | Payments or treasury |
A practical ownership split is:
- Ops or engineering: provider failures and retry logic
- Finance or program operations: policy blocks and eligibility remediation
- Payments or treasury: duplicate attempts and reversals
- Data ops or onboarding: recipient-data corrections
Make the audit record survive the failure#
For grant disbursements, keep a linked audit trail for failed or reversed items so the decision path is reconstructable. In audit logs, preserve the original request, decision result, provider response, timestamps, actor or service account, and follow-up actions. When exceptions are closed manually, add a brief closure note on what changed and why the item is safe to release, reverse, or abandon.
In federal-award contexts, this aligns with expectations to maintain effective internal controls and retain financial and supporting documentation. If a payout is reversed, link it to the original transaction and reason. Duplicate payments are an explicit ACH reversal scenario, and reversal data generally mirrors the original erroneous payment except where processing differences are required.
Retry only what is safe to retry#
Auto-retry only technical failures that are likely transient, and do it with idempotency so retries do not create duplicate operations after connection errors. Route policy failures, invalid data, and authorization or configuration errors to manual remediation first, since those conditions usually require changes before retrying.
If your remediation changes material payout details, use your internal control policy to determine whether re-approval is needed before release. Treat sanctions-related blocks separately from routine technical failures. An OFAC block is not timeout noise, and sanctions exposure can be strict liability. Do not auto-retry those items based on queue age alone.
Once exception handling is stable, you can package the evidence instead of rebuilding it every time someone asks.
Create the evidence pack auditors and funders will ask for#
Define one internal evidence pack for every disbursement so proof is ready on demand. There is no single legally mandated format across all nonprofit programs. If a payout cannot be traced from approval through status confirmation to reconciliation support, treat the record as incomplete.
Your baseline pack can link:
- Approval record
- Payout status history
- Policy-gate outputs
- Reconciliation proof
- Exception-closure record (if applicable)
This structure supports federal-award control and documentation expectations, including documented internal control and source-supported records, and aligns with IRS recordkeeping expectations that receipts, expenditures, and compliance can be substantiated.
For high-risk disbursements, keep both machine and human evidence in the same chain. Machine evidence can include transaction history, timestamps, and actor or service-account details. Human evidence can include approval decisions, approval level (where applicable), and any post-approval payout changes.
Build two views from the same underlying record:
- Audit-depth view for internal control testing, including reversals and closure notes
- Concise oversight view for funders and boards: what was approved, what was paid, whether it reconciled, and how it tied to program goals
Keep PII exposure minimal: retain only the personal information needed for verification, and exclude protected PII from single-audit reporting packages. In federal-award contexts, retain records for 3 years from final financial report submission unless an exception applies.
Phase rollout in three releases with verification gates#
Use a three-release rollout, and treat each release as a control test before a scale milestone. If controls, reconciliation, and evidence do not hold on a small cohort, scaling can spread defects faster.
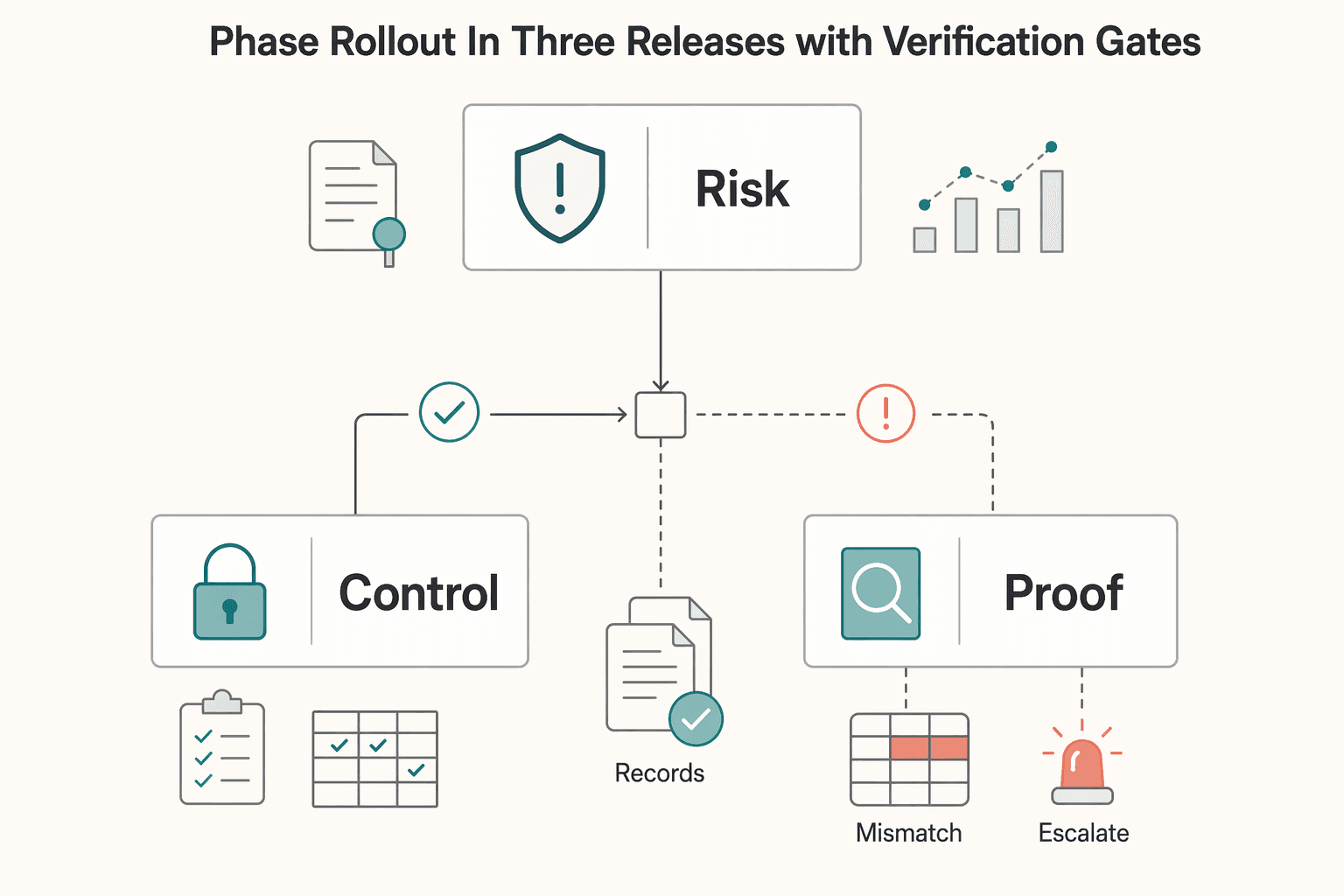
| Release | Primary scope | Gate |
|---|---|---|
| Release 1 | Core payout flow for one limited grant cohort, with compliance checks before funds move | For sampled live payouts, reproduce eligibility and approval, show policy-gate results, confirm payment status, and tie each step to source documentation; do not expand while high-risk exceptions remain unresolved |
| Release 2 | Automated reconciliation, exception queues, and standardized evidence outputs for internal reporting | Sample normal, failed, and corrected payouts and confirm reconciliation reruns from the same records produce the same result; confirm exception queues clearly separate technical failures from policy blocks |
| Release 3 | Routing logic improvements and deeper CRM and accounting integrations | Verify evidence packs stay complete after cross-system data movement, sampled payouts still reconcile end to end, and unresolved high-risk exceptions are not carried forward |
That sequence aligns with common grant operations. Lifecycle activity is commonly grouped into three phases, and federal-award contexts require documented internal controls, accurate and complete financial disclosure, and source-supported records. Build in that order: explainable money movement first, reporting automation second, broader system integration third.
Release 1#
Start with the core payout flow for one limited grant cohort, with compliance checks before funds move. Keep the cohort small enough for finance and ops to review exceptions and confirm ownership in written procedures. If policies predate the October 1, 2024 Uniform Guidance updates, review them before launch.
The gate is traceability, not speed. For sampled live payouts, you should be able to reproduce eligibility and approval, show policy-gate results, confirm payment status, and tie each step to source documentation. You should not have to rebuild the record in email or spreadsheets. Do not expand while high-risk exceptions remain unresolved.
Release 2#
Once the core flow is stable, add automated reconciliation, exception queues, and standardized evidence outputs for internal reporting. Faster reporting only helps if underlying records are accurate, current, complete, and source-supported.
Gate Release 2 on reproducibility, not dashboard freshness. Sample normal, failed, and corrected payouts and confirm reconciliation reruns from the same records produce the same result. Confirm exception queues clearly separate technical failures from policy blocks so retries do not create compliance issues.
Keep external reporting expectations separate from internal visibility: more frequent internal reporting can be useful, while federal performance reporting generally is not required more frequently than quarterly unless a specific condition applies.
Release 3#
Add scale features here: routing logic improvements and deeper CRM and accounting integrations. The goal is fewer manual handoffs, less duplicate entry, and cleaner status and coding flow across systems.
Integrate only after controls survive boundary crossings. Before promotion, verify evidence packs stay complete after cross-system data movement, sampled payouts still reconcile end to end, and unresolved high-risk exceptions are not carried forward.
Use one gate across all releases: promote only when sampled payouts have complete evidence packs, reconciliation is reproducible on demand, and high-risk exceptions are resolved with documented corrective action.
How to evaluate vendors without getting trapped by demos#
Use the same gate for procurement that you use for rollout. Whether you are evaluating Crowded, Fluxx, Foundant Technologies, or Accounting Seed, choose only after a scorecard review, not after a polished demo.
Weight the scorecard on three items first: control depth, reconciliation quality, and integration effort. For each item, require the vendor to show what is native versus delivered through add-ons, integrations, or custom development, because the delivery model changes implementation effort. Accounting Seed's Salesforce-native positioning may reduce CRM-to-GL integration dependency if Salesforce is already core for your team. Fluxx also needs cost scrutiny beyond subscription pricing, since cited onboarding packages range from $10,000 to more than $54,250.
Ask for proof artifacts, not feature promises:
- Sample audit logs for one successful disbursement, one failed disbursement, and one corrected disbursement
- One exception case with closure notes and approval history
- A reporting export that ties a disbursement back to restricted funds
- Where due-diligence or status-check results are stored, whether in the grant record, organization record, or both
- Whether checks are manually triggered or automated
Treat vendor marketing claims as unverified until you see record-level evidence in your own workflow context. Crowded markets recipient compliance checks and real-time reporting, but you still need artifact-level validation. Foundant Technologies is described with a more predetermined workflow, which may fit some teams and constrain teams with program-specific approval or reconciliation paths.
If federal awards are in scope, make that explicit in procurement. You need documented internal controls under 2 CFR 200.303 and record retention that supports the three-year baseline in 2 CFR 200.334. Require a pilot with real approval chains, a real reconciliation cycle, and peak-period exception handling before sign-off. If the vendor cannot reproduce the evidence pack on demand, stop procurement.
Conclusion#
The better path is not more automation. It is auditable automation: controlled grant disbursements, clear compliance evidence, and reconciliation that still holds when payouts fail or questions come in.
Use one blunt test: can your team reconstruct a sampled payment end to end from system records alone, including eligibility, approval, payment outcome, ledger impact, and exception closure? If the answer depends on inboxes, side spreadsheets, or memory, you have speed but not control. For federal-award programs, that gap matters because 2 CFR 200.303 requires documented and maintained internal control, and 2 CFR 200.302 requires records that identify amount, source, and expenditure with source documentation.
Shared ownership is as important as tooling. Finance defines policy gates and evidence standards. Ops owns execution and resolution of failed, reversed, or corrected payouts. Engineering owns status integrity so approval, payment, and ledger states do not drift. When ownership is unclear, errors compound quietly and become hard to defend later.
Your next step should be narrow and testable: start with one grant cohort, apply documented controls and reconciliation checkpoints, and pressure-test sampled payouts before broader rollout. At minimum, confirm:
- The approved recipient and approved amount match the payout record.
- Fund, grant, and reporting-period tags carry into reporting without manual relabeling.
- Failed or reversed payments keep linked audit history and closure notes.
- Budget-to-expenditure comparison is shown from records, not rebuilt after the fact.
Be strict about readiness. A flow is not ready to scale just because money moved most of the time. If high-risk exceptions remain unresolved, corrected payments break traceability, or one sampled case cannot be reconstructed cleanly, stop and fix that first.
Keep record obligations in scope. For federal awards, records must be retained for three years from submission of the final financial report. Tax-exempt organizations must keep records that show tax-rule compliance and support reported receipts and expenditures. Form 990 public-disclosure requirements also increase the need for consistency between reports and underlying records.
Prove the model on one cohort, require evidence that stands on its own, and expand in stages only after finance, ops, and engineering agree the controls are real.
When you are ready to validate jurisdiction coverage, approval flow fit, and rollout constraints for your grant program, talk with Gruv.
Frequently Asked Questions
What makes grant disbursements compliant in practice?
In practice, a disbursement is compliant when the required control steps, payment result, and supporting records are demonstrable. For U.S. federal awards, 2 CFR 200.303 requires documented internal control, and 2 CFR 200.302 requires records that identify the amount, source, and expenditure of funds with source documentation. If a failed, reversed, or corrected payout cannot be reconstructed from records, treat it as a likely control gap.
How do we automate disbursements without losing control?
Automate repeatable execution and evidence capture, but keep compliance monitoring and exception handling explicit. For U.S. federal awards, operations must monitor compliance and take prompt action when noncompliance is identified. Design automation so exceptions can be reviewed and corrected under the award’s terms and conditions.
What should finance and engineering implement first?
Start with shared definitions for the award (including the Notice of Award), reporting period, fund classification, payout status, and exception reason. Then implement records and workflows that identify the amount, source, and expenditure of funds and support required reporting. If teams use different identifiers or status meanings, reconciliation and reporting can break down.
Do we need real-time reporting from day one?
No. A polished executive dashboard is not a day-one legal requirement. You do need timely visibility into transactions and exceptions so noncompliance can be identified and corrected promptly. Prioritize status and exception views that support monitoring and correction, then expand presentation layers after evidence quality is stable.
How do restricted and unrestricted funds change system design?
They require allocation and reporting logic that preserves fund classification, not just better dashboard labels. Under FASB ASU 2016-14, not-for-profits report net assets with donor restrictions and without donor restrictions, so disbursement flows should preserve that distinction. If classification is being fixed later in spreadsheets, misclassification and control risk increase.
When should we replace spreadsheets?
There is no universal federal rule that says you must replace spreadsheets at a specific point. The requirement is that records and source documentation support the amount, source, and expenditure of funds and permit required reporting. If spreadsheet workflows prevent clear reconstruction of a payout from records, they are a control risk.
How do we handle country or program variation safely?
Parameterize policy gates by program and jurisdiction, then validate the legal basis before rollout. For federal awards, the Notice of Award is legally binding, and program-specific statutes or regulations can override general 2 CFR Part 200 definitions. Also account for state-law requirements where they apply, rather than copying one program’s controls into another unchanged.
Try a related tool
Fatima covers payments compliance in plain English—what teams need to document, how policy gates work, and how to reduce risk without slowing down operations.
With a Ph.D. in Economics and over 15 years of experience in cross-border tax advisory, Alistair specializes in demystifying cross-border tax law for independent professionals. He focuses on risk mitigation and long-term financial planning.
Sources
- congress.gov/crs-product/IF12924trusted
- congress.gov/crs_external_products/IF/PDF/IF12924/IF12924...trusted
- ecfr.gov/current/title-2/subtitle-A/chapter-II/part-2...trusted
- ecfr.gov/current/title-2/subtitle-A/chapter-II/part-2...trusted
- epa.gov/grants/grants-management-guidance-non-profit...trusted
- grants.gov/learn-grants/grants-101/the-grant-lifecycletrusted
- guides.gaoinnovations.gov/greenbook/2025/principle-10-design-control-a...trusted
- irs.gov/charities-non-profits/eo-operational-require...trusted
Educational content only. Not legal, tax, or financial advice.
Related Posts

How to Automate Your Personal Finances
Build a risk-first financial system that handles timing uncertainty first, then automates the rest. If you want to automate personal finances, the real upgrade is moving from "try harder" habits to a system that keeps working when real life gets messy. If you run a business-of-one, you want rules, triggers, and checks that still hold up when money shows up later than expected.

Managing Student Loans Abroad With FEIE and Reliable Payments
Before you change a repayment plan, make extra payments, or refinance, build one complete loan inventory. Open `StudentAid.gov` for your federal overview, each servicer dashboard for billing and status, and your latest statements for rate terms and capitalization language.

How Controllers Use AP Automation to Drive Financial Control Across Departments
A faster close only helps if your AP design also strengthens controls, audit-trail visibility, and reconciliation confidence. If automation moves invoices faster but makes approvals, exceptions, or payment records harder to trace, it replaces visible delay with hidden risk.