Quick Answer
Choose the lightest control depth you can defend in production for liveness detection biometric kyc for platforms, then prove it in a pilot before broad rollout. Start with evidence gates such as ISO/IEC 30107-3 and iBeta artifacts, map approve-review-stop outcomes, and define owners for repeated failures or suspected spoof attempts. Keep low-friction checks for lower-risk cohorts, and reserve active or hybrid escalation for events with higher payout exposure.
Key Takeaways
- Gate vendor decisions on documented ISO/IEC 30107-3 and iBeta evidence before pricing or demo quality.
- Define cohort-based routing early so passive checks cover lower-risk users and step-up checks cover higher-risk actions.
- Store checkpoint-level results for ID authenticity, face match, and liveness instead of relying on a single final verdict.
- Assign escalation ownership for repeated PAD failures, suspected spoofing, and post-KYC risk changes before launch.
Why liveness decisions now shape payout risk outcomes#
Liveness now sits inside payout risk, not just onboarding UX. If you are evaluating liveness detection biometric kyc for platforms, the real job is to cut spoof-driven loss and compliance surprises without adding controls your team cannot run well in production.
| Checkpoint | What it covers | Article note |
|---|---|---|
| ISO/IEC 30107-1 | terms/concepts | Part of the ISO/IEC 30107 series |
| ISO/IEC 30107-2 | data reporting | Part of the ISO/IEC 30107 series |
| ISO/IEC 30107-3 | PAD performance testing | Use as an evidence checkpoint before comparing vendor experience or integration style |
| iBeta Level 1 | basic attacks | Examples given: photos and videos |
| iBeta Level 2 | more advanced attacks | Examples given: 3D masks and deepfakes |
- This is a payout-risk control, not just an onboarding check
Liveness detection checks whether biometric input comes from a real, present person rather than spoof media such as photos, videos, masks, or deepfakes. Static identity documents alone are often not enough against current spoofing tactics. In payout environments, weak liveness controls can become money-movement risk.
- The decision is cross-functional by design
Weak controls, or controls that are hard to operate, can create exposure for compliance, legal, finance, and risk teams at the same time. Poor standards alignment can create compliance gaps, let attacks through, and raise false rejections that damage trust. The practical test is straightforward: your team should be able to verify outcomes, handle exceptions, and escalate decisions consistently.
- Standards evidence is the first checkpoint
Before you compare vendor experience or integration style, confirm the testing basis behind the liveness claim. In the ISO/IEC 30107 series, 30107-3 covers PAD performance testing (30107-1 terms/concepts, 30107-2 data reporting). iBeta PAD Level 1 tests basic attacks such as photos and videos, while Level 2 tests more advanced attacks such as 3D masks and deepfakes. Use these as evidence checkpoints, not as a universal compliance guarantee across every jurisdiction or payout scenario.
- This article is practical guidance, not a universal ranking
What follows is selection and operating guidance to help you ask better questions and choose a control depth that fits your threat profile and operating capacity. It is not a cross-vendor performance ranking.
Who this shortlist is for and how to score options#
This shortlist is most useful when your team owns the line between identity checks and payout access. For platform biometric KYC, score evidence first, operating fit second, and demo polish last.
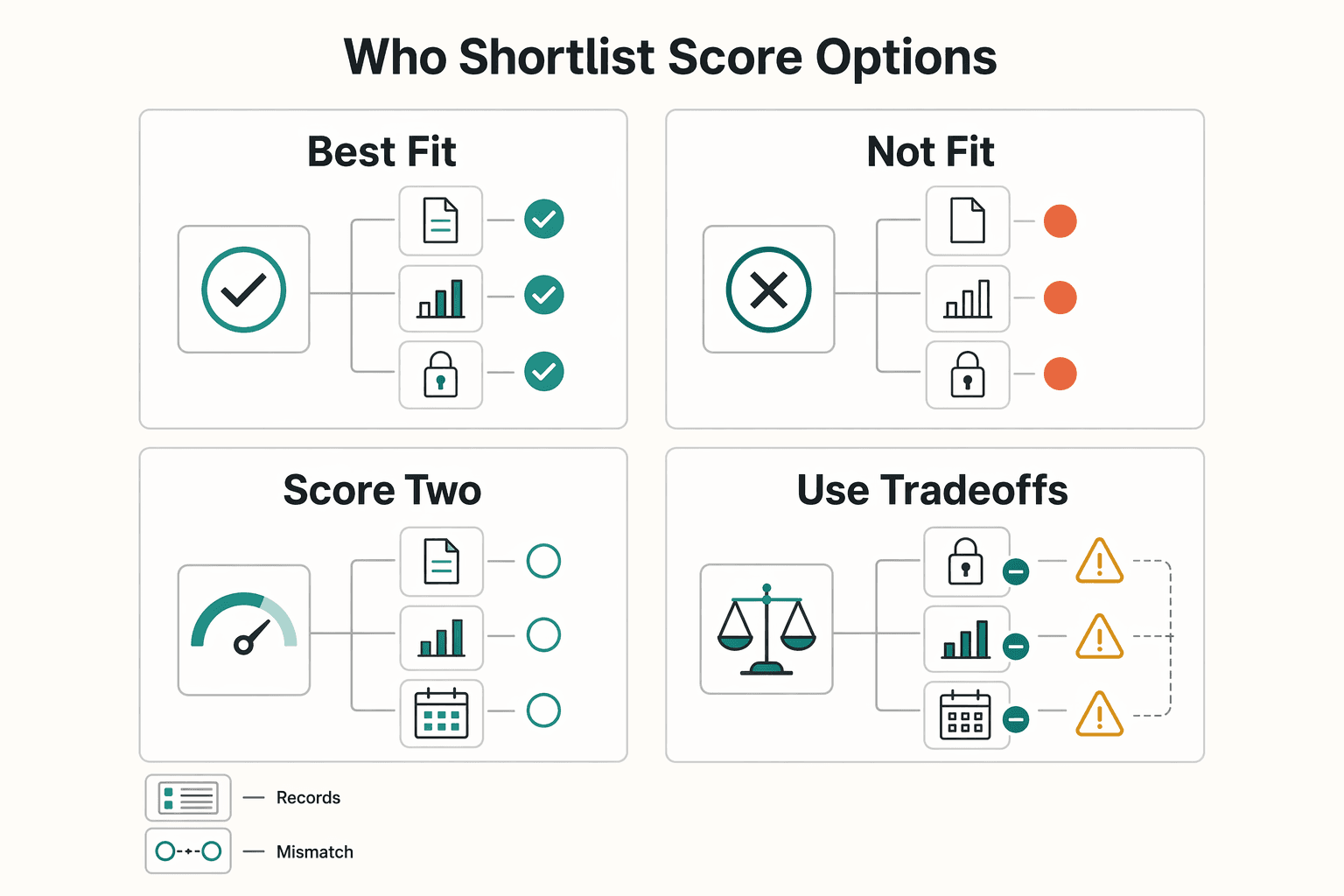
- Best fit teams
This section is for teams that own Biometric KYC and payout policy gates under KYC/AML obligations across multiple markets. Cross-country compliance requirements are often the hardest part of provider selection, so ownership matters. If your team has to justify pass, fail, or escalation decisions before funds move, you need verifiable decision evidence, not just a smooth capture flow.
- Not a fit
This shortlist is not for buyers who only want a low-friction front-end widget and do not need auditability or escalation logic. Over-reliance on automation without enough oversight is a known failure mode, so vendor evaluation should include how exceptions and repeated failures are handled in practice.
- Score in two passes
Start with an evidence pass. Ask vendors to show the artifacts behind their liveness claims. Also confirm whether they support testing before integration so you can validate behavior with your users, devices, and review flow.
Then score operating fit using grounded criteria: coverage, accuracy, scalability, pricing, and compliance certifications. For multi-market programs, verify required countries and document types directly rather than relying on headline breadth claims.
- Use tradeoffs to break ties
When options look similar, compare architecture and operations, not just conversion demos. Fragmented KYC stacks can slow operations and increase onboarding drop-off, while a more unified flow may reduce handoffs. Some teams still use multiple providers to reduce single-vendor outage risk, but that can increase compliance cost.
Finish with one decision test: choose the option your team can verify, operate, and defend when risk, compliance, and conversion pressures conflict.
Quick comparison of vendor options for platform KYC#
Use this table to screen vendors, not rank them. Gate first on documented certification or PAD signals, then on integration fit and operational caveats. In the reviewed materials, ISO/IEC 30107-3 and iBeta references are the clearest cited assurance signals. FAR/FRR comparability, pricing transparency, and independent benchmark methods are mostly unknown in these excerpts.
| Vendor | Certifications or cited assurance signals | Liveness mode | Integration model | Known caveats from provided materials | Unknowns to force into diligence | Operational risk if wrong |
|---|---|---|---|---|---|---|
| Microblink | ISO/IEC 30107-3 is cited in comparison materials | Not clearly specified in provided excerpts | SDK integration required; on-device/privacy-first positioning is cited | SDK-heavy effort; premium pricing noted; third-party snapshot claims 3,500+ document types and $0.50/verification | FAR/FRR not comparable; no independent benchmark method shown; pricing snapshot is third-party (published March 25, 2026) | You may underestimate implementation effort while assuming assurance and cost are already settled |
| Sumsub | No certification detail confirmed in provided excerpts for this section | Not confirmed in provided excerpts | Not confirmed in provided excerpts | Third-party snapshot lists $1.35/verification only | FAR/FRR unknown; benchmark methodology unknown; certification evidence should be requested directly | You could approve a control set that does not match your risk tolerance |
| Jumio | No ISO/IEC 30107-3 or iBeta claim supported in this section's excerpts | Not confirmed in provided excerpts | Not confirmed in provided excerpts | Third-party article claims 5,000+ ID types, without comparable liveness evidence here | FAR/FRR unknown; benchmark methodology unknown; pricing transparency unknown; certification artifacts need direct verification | Strong document-coverage claims can mask unresolved PAD evidence gaps |
| FaceTec | iBeta Level 1 & 2 cited; 3D FaceMap technology cited | Not explicitly labeled passive or active in the excerpt | Not confirmed in provided excerpts | Higher friction due to zoom action | FAR/FRR unknown; no independent benchmark method in excerpt; pricing not transparent here | Higher-assurance flow may add user friction if applied too broadly |
| ID R&D | iBeta Level 2 cited | Passive liveness detection | Not confirmed in provided excerpts | No additional row-specific caveat in provided snippets | FAR/FRR unknown; no independent benchmark method shown; pricing not transparent here | Passive-first controls can be mis-scoped without clear escalation paths |
| Regula | ISO/IEC 30107-3 cited | Not explicitly specified; positioned as forensic-grade identity verification | Not confirmed in provided excerpts | Forensic capabilities can be overkill for simple apps | FAR/FRR unknown; benchmark methodology unknown; pricing not transparent here | You can overbuy forensic depth and add review burden without clear fit gains |
| Identomat | iBeta Level 2 referenced in comparison-table notes | Not clearly specified in provided excerpts | Not confirmed in provided excerpts | No row-specific caveat supported in provided excerpts | FAR/FRR unknown; benchmark methodology unknown; pricing transparency unknown; integration details need direct confirmation | Assuming parity with better-documented vendors can create control gaps |
| Vouched | No supported certification details in provided excerpts | Not supported in provided excerpts | Not supported in provided excerpts | No supported caveats in provided excerpts | FAR/FRR unknown; pricing transparency unknown; benchmark methodology unknown; core liveness evidence must be requested directly | Shortlisting on familiarity without evidence can leave the decision hard to defend |
What this table can and cannot prove#
The strongest signal here is cited PAD posture, not demo polish. In the reviewed excerpts, FaceTec shows the clearest iBeta depth. ID R&D has a specific passive-liveness signal. Regula is positioned around ISO/IEC 30107-3 plus forensic depth.
Comparability is still weak. One source explicitly frames itself as a buyer's guide, not a ranking, so treat this table as triage until you collect direct evidence for the exact product variant you would deploy.
Minimum diligence before final round#
Before you move vendors into a final round, request documentary support for every ISO/IEC 30107-3 or iBeta claim and mark anything unverified in your scorecard. Then score each option against the buyer criteria called out in the reviewed guidance: security, standards compliance, supported documents, automation level, and whether it must work online/offline.
If you need the shortest evidence-first shortlist from current materials, start with vendors that already show a concrete checkpoint: FaceTec, ID R&D, Regula, and Microblink. Keep the rest open only after direct evidence collection closes certification, method, and operating-fit gaps.
For a related walkthrough, see Best Platforms for Creator Brand Deals by Model and Fit.
Microblink for on-device verification with tight privacy controls#
Microblink is a strong fit here when your main requirement is on-device privacy control in a mobile KYC flow. In the reviewed materials, the strongest supported signals are on-device processing, a unified document-and-biometric journey, and an ISO/IEC 30107-3 checkpoint relevant to PAD diligence.
Why it stands out#
The practical appeal is the combined document-and-biometric flow, which can reduce handoffs between ID capture and liveness checks. Since remote liveness is typically performed during selfie or short-video capture, that unified path can make onboarding behavior and review queues easier to manage.
Its privacy positioning is also central. On-device processing is presented as a control for handling sensitive biometric and ID data. Treat the scale and speed claims as vendor-stated context, not guarantees in your environment: +10 million IDs/month, 140+ countries, and <1 second capture/extraction.
What to verify before committing#
Start with the ISO/IEC 30107-3 claim. Confirm the exact SDK or product variant and version, then verify that the evidence maps to PAD performance-testing scope for what you plan to deploy.
Then test real operating conditions: low light, older devices, and weak connectivity. Microblink is positioned around strong on-device speed and low-light accuracy, but the real question is whether your device mix holds conversion without overloading manual review.
Main tradeoffs and practical fit#
The main tradeoff is implementation effort. The materials describe an SDK-based, premium-priced model, which can mean heavier delivery work and tighter coordination across product and app releases.
Risk cuts both ways if tuning or controls are off. Weaker PAD can let advanced spoof attempts through, while aggressive tuning can increase false rejections and user harm, and PAD gaps can still create KYC/AML risk.
For mobile-first creator onboarding, Microblink can be a practical choice when you can support native SDK work and need tighter control over biometric and ID data handling in-app. Pass or defer if your near-term priority is the lightest implementation path.
Sumsub for broad integration and all-in-one verification ops#
Sumsub fits teams that want one platform to run liveness and face matching alongside broader KYC/AML operations across markets. The core caveat is that many speed and ROI outcomes in this section are vendor- or release-reported, so procurement should treat them as screening inputs, not proof.
Why it fits multi-geo platforms#
The clearest strength is platform breadth. Sumsub presents an all-in-one KYC position, explicitly lists Liveness & Face Match, and says workflows can be configured by market, risk level, and requirement in one platform.
For platforms expanding across geographies, that can reduce tool sprawl across onboarding and adjacent policy operations. BiometricUpdate also describes a "full-cycle verification platform" with an API first technical approach, and reports Mesh availability across KYC, KYB, and Transaction Monitoring.
Marketing coverage is broad: 14,000+ documents from 220+ countries and territories, 30 seconds on average, 90%+ pass rates on average, and up to 75% lower manual effort. Use these as vendor-stated indicators until you validate performance against your own user mix and fraud profile.
What to verify before you buy#
Before sign-off, separate scope claims from performance evidence. Then verify the operating details that matter most:
- Confirm the exact deployment configuration, including how Liveness & Face Match are triggered and how rules vary by market and risk tier.
- Request methodology behind 30 seconds on average, 90%+ pass rates on average, and up to 75% manual-effort reduction, including cohorts, exclusions, document mix, and geography splits.
- Validate external screening integration details. If Mesh BYOK is part of your control design, confirm support for your own ComplyAdvantage Mesh API credentials.
- Get use-case pricing directly from the vendor. A third-party page lists $1.35/verification, but that is not vendor-confirmed in the reviewed excerpts.
The main tradeoff#
A unified stack can simplify operations, but it also increases concentration risk. If onboarding checks and screening-adjacent controls sit with one provider, weak evidence in one area can affect a larger control surface.
Also note the evidence type. Some integration and outcome statements are explicitly release-driven, including language such as "A release says" and partner outcome claims. Sumsub is practical when unification is the main goal, but do not treat breadth as proof of liveness assurance quality without testable evidence.
Jumio for risk-scored decisions tied to ID and selfie flow#
If you need a documented chain from ID check to selfie plus liveness and then to approval or rejection, Jumio is a practical fit. It is especially relevant for compliance-led teams that must show how a user moved from submitted ID to approval, review, or rejection.
Why it fits decision-heavy programs#
Jumio's flow is explicit: check whether the ID is authentic and valid, whether the selfie matches the ID photo, and whether the person is physically present rather than a spoof. Jumio then ties that evidence to a risk-based decision. It states it can approve or reject identity transactions in seconds based on predefined risk tolerances.
That structure matters when your policy is not a single pass or fail gate. If finance, risk, and compliance split users into auto-approve, manual review, or block paths, this sequence is easier to defend than a black-box pass result.
What stands out in the product story#
The liveness position focuses on modern attack types, including deepfakes and injection attacks, and references patented active illumination. Treat that as product direction, not proof of better performance across vendors.
The other differentiator is decisioning logic. Jumio Risk Signals describes real-time onboarding decisions based on customer risk scores, with step-up checks that start from background signals such as Device Risk and trigger added checks only when needed. It also states access to 500+ data sources for PII confirmation and risk assessment. For teams tuning friction by risk tier, this is the core capability to test.
What to verify before procurement#
The excerpts support a coherent decision model, but not cross-vendor FAR/FRR/accuracy comparisons, pricing, or ROI claims. They also do not independently validate deepfake or injection-attack performance.
Request a concrete evidence pack with sample decision records that include these fields, and confirm audit export details at the same time. In regulated programs, the decision log should preserve a clear audit trail from submitted evidence through any escalation triggers.
- ID authenticity result
- selfie-to-ID match result
- liveness or spoof outcome
- risk score or risk band
- final action - approve, reject, or review - tied to your tolerance settings
A common failure mode is excess friction. Over-applying onboarding checks can increase legitimate-user abandonment, so do not default every user to the highest-friction path. Define which cohorts start with background risk signals, which move to selfie plus liveness step-up, and where manual review applies.
A third-party comparison dated Jan 21, 2026 labels Jumio biometrics as "ISO/IEC Level 2 liveness," but that is not primary certification evidence. If your controls require ISO/IEC or iBeta artifacts, make those explicit procurement gates and request the underlying documents directly.
FaceTec for high-assurance liveness in stricter threat models#
FaceTec is a fit when you need higher-assurance liveness controls and can accept more user challenge in some flows. Use it as a step-up control for high-risk account actions, not as the default gate across all onboarding.
Where it fits#
Reserve FaceTec for cases where spoof resistance matters more than a low-friction experience. Active liveness uses prompted actions, which can improve spoof resistance but can also raise friction. One vendor comparison explicitly notes "higher friction due to zoom action," so this approach is usually better reserved for risk-tiered step-up events rather than low-risk cohorts.
What supports the case#
The strongest support here is testing posture, not any claim of cross-vendor superiority. A Dec. 1, 2025 announcement states FaceTec completed all five levels of third-party liveness anti-spoofing lab testing in 2025. It says the testing was done by labs and security firms described as NIST/NVLAP and ISO/IEC 17025 accredited. The same announcement says BixeLab tested Levels 1-3 and Level 5, Ingenium tested Level 3 and Level 5, and reports 0% APCER with 100% rejection of 48 injection attacks.
Separately, a vendor comparison lists FaceTec with iBeta Level 1 and 2 references and 3D FaceMap technology. Treat those references as procurement checks, not final proof of certificate scope, validity dates, or deployment relevance.
What to verify before rollout#
Before rollout, request the underlying lab reports, the exact SDK version tested, device and test conditions, and the scope behind any iBeta Level 1 and Level 2 claim. Confirm coverage for both PAD (physical spoof attempts) and IAD (digital injection attempts).
The main operational risk is overuse. Applying a high-assurance flow to low-risk users can increase user friction and implementation burden, especially where integration is described as more complex for proprietary, larger-deployment setups. Define high-risk triggers first, then attach FaceTec to those events. Related reading: The Best Platforms for Selling Digital Products.
ID R&D for low-friction passive liveness at high volume#
ID R&D is a practical baseline when your priority is high-throughput onboarding with low user friction, and you reserve stronger checks for higher-risk events. It fits high-volume biometric KYC flows that start with passive liveness, then escalate when risk signals justify step-up controls.
Why it stands out#
The core advantage is passive, single-frame liveness designed for speed and minimal user action. One comparison describes ID R&D as using texture and light analysis, lists iBeta Level 2, and frames it for "high-volume B2C apps, step-up authentication, kiosk verification."
Speed evidence is useful, but still context-specific. In a February 18, 2025 press release tied to a DHS S&T remote identity evaluation, the vendor reports 100% imposters blocked and a maximum transaction time of 1 second. The same release says 21 systems were evaluated across active and passive PAD approaches.
Where the limits show up#
The main tradeoff is that passive performance depends heavily on capture quality. One comparison explicitly says results are "dependent on image capture quality," so lower-quality inputs may reduce reliability and increase retries or manual review.
Coverage limits also matter when you model higher-level bypass methods. One excerpt says lab tests are available only for the first two attack levels, and that higher PAD bypass levels are missing from ISO 30107-3 coverage. In practice, that supports a risk-based escalation design rather than relying on passive checks alone.
What to verify before rollout#
Request the exact iBeta artifact, tested version, and capture conditions, then confirm they match your intended capture flow. Also validate your document-check path. ID R&D is described as lacking built-in document verification workflows, so your KYC stack needs a separate document layer and clear routing into active checks or deeper review when risk rises.
Regula for forensic-heavy identity environments#
Regula can be a fit when your priority is evidence quality for review and investigation, not only the lowest-friction onboarding path. It is aligned with identity flows where review teams need document-level evidence, not just a selfie outcome.
Why it fits stricter evidence standards#
Regula has a document-first component. Its Document Reader SDK is described as cross-platform for reading and verifying identity documents, with extraction from visual zones, MRZs, barcodes, and RFID chips where supported. It also includes document liveness checks to help confirm the ID is a physical document rather than a copy or digital reproduction.
This can be useful when a case needs multiple identity signals together, such as selfie comparison, MRZ data, chip data, and document authenticity outputs.
What to verify before you buy#
Do not buy from marketing summaries alone. Confirm the exact Face SDK scope in your real flow. That includes 1:1 face matching, any 1:N use, liveness, and PAD, plus which spoof types are covered in production capture.
A practical verification pack should include the tested product variant, version, and capture environment, along with sample decision outputs for document checks, selfie matching, and PAD, plus fallback handling when document liveness or chip reading is unavailable.
- tested product variant, version, and capture environment
- sample decision outputs for document checks, selfie matching, and PAD
- fallback handling when document liveness or chip reading is unavailable
If ISO/IEC 30107-3 is a hard requirement in your scorecard, request the artifact directly rather than inferring status from related claims.
The tradeoff to keep in mind#
Regula may be more than you need for straightforward seller or creator onboarding. Its value rises when you must manage risks such as screenshots, video replays, injected streams, masks, and document reproduction, but that can also increase implementation and review complexity.
Keep external benchmarks in scope. A Sep 9, 2025 report on NIST FATE age-estimation results is a useful checkpoint, but it does not by itself establish superior PAD or biometric KYC performance.
Integration order and go-live checkpoints that prevent avoidable failures#
Many avoidable verification failures come from capture-quality issues, and selfie verification itself includes multiple checks in real time. Set go-live criteria around what you can verify in production, and treat unresolved escalation rules as a pre-launch gap.
| Checkpoint | What to do | Grounded detail |
|---|---|---|
| Decision flow | Use a clear three-part structure | ID document authentication, biometric face match, and liveness confirmation; document what each result means for approval, review, or stop |
| Stage-level visibility | Keep outputs that show where a failure occurred | Selfie verification runs multiple checks in real time; prioritize fraud-detection accuracy, API integration flexibility, and standards alignment for user-data protection, including SOC 2 and ISO 27001 where relevant |
| Adverse-condition tests | Run tests for common input problems | Test glare, blur, and covered information; confirm clear retry guidance and that the team can distinguish capture-quality issues from other verification failures |
| Escalation design | Treat it as a required pre-launch control | Define PAD thresholds, deepfake workflows, and fixed ops and compliance ownership models internally before broad rollout; map escalation triggers to payout statuses and exception paths |
- Define the decision flow around the three-part verification process.
Use a clear three-part structure in your control design: ID document authentication, biometric face match, and liveness confirmation. Document what each result means for approval, review, or stop.
- Integrate for stage-level visibility, not just one final verdict.
Selfie verification runs multiple checks in real time, so preserve outputs that show where a failure occurred. During vendor and implementation review, prioritize fraud-detection accuracy, API integration flexibility, and standards alignment for user-data protection, including SOC 2 and ISO 27001 where relevant.
- Test preventable failure conditions before wider traffic.
Run adverse-condition tests for the common input problems called out in the grounding: glare, blur, and covered information. Confirm the user gets clear retry guidance and your team can distinguish capture-quality issues from other verification failures.
- Treat escalation design as a required pre-launch control.
The material here does not establish specific PAD thresholds, deepfake workflows, or fixed ops and compliance ownership models. Define those internally before broad rollout so unclear outcomes do not become unmanaged exceptions.
Before go-live, map escalation triggers to payout statuses and exception paths so ownership is explicit and auditable. Review Gruv docs for implementation patterns
Audit evidence and escalation triggers your team should document#
If your team cannot show how a decision was made and why a case escalated, the control is hard to defend. Document the evidence and escalation rules before you expand coverage.
| Decision area | What to document | Grounded detail |
|---|---|---|
| Per decision path | Keep separate records for approve, reject, and exception outcomes | At minimum keep the policy version in force, automated decision logs, and any exception or reviewer notes; include retry history when it affected the outcome |
| Escalation rules | Write triggers as explicit case rules | Use defined warning signals, risk factors, or inconsistencies from automated checks; grounded example: low liveness scores |
| Post-approval changes | Treat later risk changes as new decision points | Keep onboarding proofing records linked to post-approval monitoring and document whether escalation addressed identity risk or other risk signals |
| Automation handoff | Document where automation stops and manual review starts | Define when automated results can close a case and when the flow should escalate to human review; records should show which checkpoint passed or failed and why the case did or did not escalate |
- Build one evidence pack per decision path.
Keep separate records for approve, reject, and exception outcomes rather than one generic case file. At minimum, keep the policy version in force, automated decision logs, and any exception or reviewer notes. Include retry history when it affected the outcome.
NIST SP 800-63A is a practical baseline for audit structure. Evidence validation means submitted evidence is genuine, authentic, and accurate. Identity verification means the applicant is the genuine owner of the evidence and attributes. Logs that only show "pass" or "fail" may not show which checkpoint failed or whether the result matched your intended assurance-level context.
- Write escalation triggers as explicit case rules.
Manual review should be triggered by defined warning signals, risk factors, or inconsistencies from automated checks, not reviewer intuition alone. Keep those triggers visible in queueing or case-management logic so reviewers can see why a case escalated and what to assess next.
A grounded example is low liveness scores as a manual-review trigger. Reviewer records should show warning assessment, document inspection, biometric verification, and risk-signal analysis so outcomes stay consistent and auditable.
- Treat post-approval risk changes as new decision points.
A one-time KYC pass does not remove later identity or risk blind spots. Keep onboarding proofing records linked to post-approval monitoring so the team can compare original verification with new risk signals and document whether escalation addressed identity risk or other risk signals.
- Document where automation stops and manual review starts.
Automation improves efficiency, but it is not foolproof for every case. Define when automated results can close a case and when the flow should escalate to human review, then record that handoff in the case file.
If you can only show a final verdict, fix that before expanding coverage. Records should show which checkpoint passed or failed and why the case did or did not escalate.
Choose the lightest control set that still stands up to audit#
For liveness detection biometric kyc for platforms, the right answer is usually the lightest control depth you can defend with evidence. A lighter flow is acceptable when it covers your real risk and you can document why it is appropriate, how you handle uncertainty, and who owns exceptions.
- Match control depth to real exposure
Start with a risk-based approach and keep only the controls that address your actual failure modes. Lower-risk cohorts can use lighter-touch checks, but only with documented justification and a clear response when confidence drops. Higher-risk services and actions should get stronger assurance.
The key test is whether your KYC and AML program can show documented risk assessments, decisioning logic, monitoring, and incident response. The lightest acceptable setup is the one your team can justify under review.
- Pilot for evidence, not just pass rates
Before broad rollout, run a documented pilot with a scorecard focused on audit evidence, not just approvals. Keep decision logs, exception records, escalation reasons, and an auditable onboarding trail. If a vendor cites independent review, keep that artifact, but treat it as supporting evidence, not final proof.
Make escalation ownership explicit during the pilot. Assign owners for repeated liveness failures, suspected spoof cases, and unclear outcomes requiring manual review. Regulatory direction is toward verifiable, auditable onboarding with mandatory human oversight, not automation alone.
A useful pilot scorecard answers four questions: did the control catch observed attacks, were false positives manageable, can compliance explain each decision path, and can operations handle escalations without backlog. Go-live should depend on evidence quality and escalation ownership, not demo performance.
- Use liveness as one layer, not the whole defense
Poor liveness implementation can be both a compliance gap and a fraud pathway. But overbuilding biometric checks alone can still miss broader control gaps. Keep liveness in a layered control model with adjacent controls your team has separately validated, such as fraud detection logic and, where appropriate, device fingerprinting or source-of-funds checks.
Fragmented manual KYC operations can increase friction, costs, false positives, and human error. More consolidated flows can speed onboarding while letting teams focus effort on complex, higher-risk cases, as long as hard cases still route to trained reviewers. Strong designs usually combine a modest liveness baseline with targeted step-up controls for higher-risk cases.
Use this closing rule: adopt the minimum control depth that reliably handles your attack profile and regulatory exposure, then prove it through a documented pilot before broad rollout. Related: Device Fingerprinting and Fraud Detection: How Platforms Identify Bad Actors.
If you need to validate your liveness escalation model against real payout operations and market-specific constraints, talk through your rollout with Gruv.
Frequently Asked Questions
What is liveness detection in biometric KYC for platforms, and where does it sit in onboarding?
Liveness detection checks whether a biometric sample comes from a live person present at capture time rather than a spoof. In remote onboarding, it is typically performed during selfie or short-video capture. Its role is to reduce successful spoofing attempts in the identity decision flow.
How should teams choose between passive, active, and hybrid liveness models?
Choose the model from your risk tiers, not from vendor preference alone. Lower-risk cohorts can use passive checks to reduce friction, while more sensitive flows typically require active checks. A hybrid setup can use passive defaults with stronger step-up checks for higher-risk cases.
Which standards matter most in vendor due diligence, and what does ISO/IEC 30107-3 actually prove?
Use vendor standards claims as due-diligence inputs, not as standalone proof of production performance. From this evidence pack, you should not assume certification scope, cross-vendor comparability, or specific accuracy outcomes. The operational test is whether the control evidence supports the exact workflow and escalation paths your team will run.
What should compliance and risk teams ask before go-live to avoid weak controls?
Before go-live, confirm you have a formal Customer Acceptance Policy (CAP) that is documented, published internally, and reviewed regularly. Confirm users are risk-tiered, for example, low/medium/high, based on factors like jurisdiction and product type. Also confirm written escalation paths specify what additional evidence is required for higher-risk cases.
What events should trigger immediate escalation after a user initially passes KYC?
Escalate when new information suggests a user no longer fits your CAP risk appetite or should be reclassified into a higher-risk tier. Escalation paths should already define what additional evidence is required in those cases. Do not rely only on the original onboarding result when risk context changes.
What remains unknown in vendor claims, and how should teams validate it independently?
Key unknowns include cross-vendor comparability and whether reported results match your attack mix and operating conditions. Vendor-cited market signals, including a reported fourfold rise in AI-driven fraud and deepfake usage from 2023 to 2024, show urgency but do not validate one product for your setup. Validate claims through your own documented testing and decision controls before broad rollout.
Try a related tool
Fatima covers payments compliance in plain English—what teams need to document, how policy gates work, and how to reduce risk without slowing down operations.
Priya specializes in international contract law for independent contractors. She ensures that the legal advice provided is accurate, actionable, and up-to-date with current regulations.
Sources
Includes 4 external sources outside the trusted-domain allowlist.
- d.lib.msu.edu/etd/50570trusted
- pages.nist.gov/800-63-4/sp800-63a.htmltrusted
- psgtech.edu/NAAC/criteria_1/21-22/files/1.1.2.pdftrusted
- scholarlycommons.law.wlu.edu/cgi/viewcontent.cgitrusted
- arxiv.org/html/2601.04583v1external
- basekyc.in/blog/liveness-detection-api-integration.htmlexternal
- beverified.org/providers/regulaexternal
- biometricupdate.com/202603/sumsub-integrates-ai-risk-intelligenc...external
Educational content only. Not legal, tax, or financial advice.
Related Posts

Fraud Detection on Payment Platforms with Rules and Machine Learning
For cross-border payout platforms, effective fraud detection is less about a single model or rule than about controls you can document, explain, and defend under audit or incident pressure.

Device Fingerprinting Fraud Detection Platforms for Payment Risk Teams
For payment platforms handling contractor, seller, or creator payouts across markets, the starting point is not vendor hype. It is control design. Device fingerprinting can help detect suspicious behavior and reduce fraud risk, especially when the same device appears across repeated sign-ups or refunds. But it only works if risk, compliance, legal, finance, and payments ops agree on what the signal can support and what evidence must exist when a decision is challenged.

When High-Risk Payout Accounts Need Source of Funds Checks Beyond KYC
A one-time KYC check may not be enough for higher-risk payout accounts. Risk can change after onboarding as transaction behavior shifts and customer risk profiles change.