Quick Answer
Build your contractor compliance program around risk-tiered market and flow decisions, then block payout release whenever required controls are unresolved. Use one stable onboarding order (identification, AML/KYC review, required documentation, completion decision), and require timestamped records for each stage. Keep U.S. federal material in a tagged lane until federal scope is confirmed, rather than importing it into global defaults. For reporting, keep Form 8938 and FBAR decisions explicit in each cycle pack so finance, compliance, and tax teams can reconstruct why a payout moved or stayed on hold.
Key Takeaways
- Tier markets and payout flows in writing, then publish light and strict control modes with owners and review dates.
- Hold payouts when AML or other required control records are unresolved, stale, or contradictory, and require time-bound approval for overrides.
- Keep U.S. federal references such as OFCCP and DFARS Part 252 in a separate federal lane unless scope is confirmed.
- Build one retrievable cycle pack that links control decisions, execution records, and Form 8938/FBAR relevance notes.
- Automate deterministic status checks first, but keep interpretation-heavy classification and tax judgments in manual review.
What a Contractor Compliance Program Needs to Scale#
If you are building a contractor compliance program across multiple countries, use this guide as an operating model, not a policy memo. Define control gates, reporting checkpoints, and escalation rules that operations, finance, legal, and compliance teams can actually run.
Start where risk tends to surface: contractor onboarding, payout operations, documentation readiness, and audit evidence. For each country and payout flow, be clear about what is in scope, what must be true before funds move, and what artifact proves each check happened.
Set the core tradeoff early. You want fewer regulatory surprises without forcing every market into the strictest process. Contractor models can improve speed and cost, but compliance gets harder as rules change and your footprint expands. If you underbuild, you may struggle to explain decisions later. If you overbuild, routine onboarding and payouts can slow down.
Keep framework boundaries clear. Federal references can improve control discipline, but they are not a default template for global contractor payouts. CMMC Level 1 is focused on Federal Contract Information, and FAR 2.101 definitions apply within FAR unless context changes them.
Use this guide to standardize controls, evidence, and escalation points, then validate market-specific legal and tax decisions with counsel where jurisdiction facts differ.
What to prepare before you start#
Before you draft new controls, build a working baseline of flows, artifacts, evidence, and ownership. That keeps the program from being shaped by whichever market or team speaks first.
| Preparation area | What to gather or define | Examples / notes |
|---|---|---|
| Jurisdiction and operating-flow inventory | Record how contractor onboarding and payouts happen in practice | Flag where requirements may differ by jurisdiction or industry |
| Current policy artifacts | Gather the live documents and checklists teams already rely on | Examples: Contract Compliance Review Checklist; Pre-Construction Meeting Checklist; Field Audit Report |
| Evidence baseline | Decide what proves each control ran | Retained checklists, approvals, and retrievable records tied to the underlying contractor activity |
| Ownership and failure risks | Record who owns each control artifact and the escalation path | Capture known failure modes, including misclassification risk when contractor/employee distinctions are not followed |
- Map where compliance risk differs.
Create a jurisdiction and operating-flow inventory for the markets in scope. Record how contractor onboarding and payouts happen in practice, and flag where requirements may differ by jurisdiction or industry.
- Collect current policy artifacts.
Gather the live documents and checklists your teams already rely on, including concrete review artifacts where available, for example a Contract Compliance Review Checklist, Pre-Construction Meeting Checklist, or Field Audit Report. If government-contract work is in scope, include your written code of business ethics and conduct and related internal-controls documentation.
- Define your evidence baseline.
Decide in advance what proves each control ran, such as retained checklists, approvals, and retrievable records tied to the underlying contractor activity. Named artifacts are easier to defend than verbal confirmation.
- Document ownership and known failure risks.
Record who currently owns each control artifact and the escalation path used when an issue appears. Capture known failure modes explicitly, including misclassification risk when contractor/employee distinctions are not followed.
For a step-by-step walkthrough, see How to Build a Contractor Referral Program Paying Existing Contractors to Recruit.
Set scope and risk tiers by market and payout flow#
Treat each market and flow pair as its own risk decision, not as part of one global bucket. A scalable program sets different control depth by documented risk profile so operators can act consistently under pressure.
Tier markets with written criteria#
Tier markets using criteria you can defend in writing, then assign ownership and review dates. For U.S. classification questions, use the legal lens of economic dependence, and account for the fact that state law can be broader than federal law.
When classification is unclear, treat the market as higher risk until you document the legal position. The downside can include back wages, DOL civil money penalties, and litigation costs.
If you rely on U.S. federal rulemaking context, do not treat FederalRegister.gov text as official by itself. Verify against an official Federal Register edition and keep that check in the record.
Split scope by payout flow#
Split scope by payout flow before assigning controls. For each market, mark each flow as approved, restricted, or pending, and state what evidence is required to move status.
Your scope record should let an operator answer, without escalation, which flows can run now, which are blocked, and what checkpoint is missing.
Use one escalation rule for ambiguity#
Use one escalation rule for ambiguity and apply it consistently. When classification is uncertain, pause expansion on that market and flow path until legal or compliance review is recorded and the required controls are explicit.
This is an internal policy choice, not a universal legal rule, but it prevents ad hoc approvals when the risk picture is incomplete.
Publish light and strict control modes#
Define light and strict control modes once, then publish them for operations.
| Tier | When to use it | Operator expectation | Evidence to retain |
|---|---|---|---|
| Light | Low ambiguity with stable, well understood flow | Standard checks and normal approval path | Tier rationale, reviewer, completion record |
| Strict | High ambiguity or high consequence if wrong | Escalated review before launch or scale on that flow | Decision record, reviewer approval, legal verification notes |
Keep contract-specific obligations separate from baseline market tiers. For example, where DOD contract requirements apply, track CMMC and DFARS checkpoints as contractual controls so they do not distort your general market model.
Separate US federal contractor rules from global payout compliance#
Keep U.S. federal contractor material in a separate lane. Do not treat it as the default control set for every country, entity, or payout path in your program.
Tag federal-only controls before they reach ops#
Create a federal-only tag in your control inventory before controls reach operations. Place OFCCP references and federal citations there, including Executive Order 13673 materials tied to federal contracting guidance.
For each federal-tagged control, require the related program or contract, approving owner, and review date. If those fields are missing, keep that control out of onboarding, payout release, and operator training.
Apply federal guidance in the right lane#
Apply federal guidance in its federal context. The materials referenced here are framed around parties contracting with the U.S. Federal Government and agency oversight of contractor responsibility, integrity, and business ethics, including contractor and subcontractor reporting frameworks.
Your global payout lane answers different operational questions: whether the payee can be onboarded, what documentation is required, what screening blocks release, and how the decision trail is retained. Keeping those lanes separate prevents federal citations from becoming universal hold reasons in non-federal flows.
Treat federal references as context until scope is confirmed#
Set and publish one hard rule. If applicability to a federal-contractor regime has not been confirmed, treat federal references as context, not default operating controls. Do not automatically add checklist items, template clauses, or escalations based only on an OFCCP or executive order citation.
If a team uses FederalRegister.gov for legal research, require one extra verification step before the item affects operations. The XML rendition is informational, so verify against an official Federal Register edition and store that verification in the decision record.
Design onboarding controls that do not bottleneck growth#
Design onboarding so most low-ambiguity cases move quickly, while conflicting or higher-risk records route to deeper review with a clear decision trail.
Run checks in a stable sequence#
Use a consistent sequence so identity details stabilize before downstream checks. Start with customer identification, then run your AML/KYC review flow, then collect any additional required onboarding documentation.
| Stage | What to capture | What to record | Escalate when |
|---|---|---|---|
| Identification | Identity information required by your policy | Verification outcome, decision owner or service, timestamp | Document mismatch or unresolved identity conflict |
| AML/KYC review | Information required by your AML/KYC process, including enhanced due diligence when needed | Review result, match or risk status, timestamp | Possible match or unresolved risk signal |
| Additional documentation (if required) | Additional onboarding documentation required by your process | Documentation status, validation outcome, timestamp | Missing, inconsistent, or unresolved details |
| Completion decision | Final status only | Final decision owner and timestamp | Any prior stage is unresolved |
A stable order can reduce rework by avoiding downstream cleanup on records that are still changing at identification.
Set evidence requirements before intake goes live#
Define evidence requirements before intake goes live. If approvals are untracked, you cannot evidence the control. If checks are not consistent and retrievable, you are not audit-ready.
At each stage, keep a minimum decision record: what was reviewed, what decision was made, who made it, and when. Informal approvals in chat or ticket comments are not enough if they cannot be retrieved and defended later.
Use narrow triggers for manual review#
Use narrow, observable triggers for manual review. Escalate cases with conflicting records, unresolved AML outcomes, or other clear risk signals that your policy defines.
Keep triggers specific enough that operators can apply them consistently and explain them later. If routine low-risk cases are piling up in manual review, tighten trigger logic or improve intake data quality.
Build control evidence into intake#
Make intake fields and stage transitions support retrievable evidence from day one. Use timestamped ownership and decision records at each stage so checks stay consistent and defensible as volume grows.
Define onboarding complete as an explicit operational state with all required checks resolved and a final timestamped decision. That helps prevent partial records from moving forward on ambiguous status alone.
Set pre payout gates and release rules#
No payout should move on an unresolved record. If payout urgency conflicts with control status, default to hold and release only after the control is cleared or a named compliance approver grants a time-bound exception.
Read release readiness from control states#
Gate releases on retrievable control states, not memory or raw documents. Before release, require the payable record to show resolved statuses for the checks your policy requires. That can include AML controls, other required compliance records, and market-specific holds.
Read release readiness from a current gate snapshot that includes control result, decision owner or service, and timestamp. If a required field is blank, stale, or contradictory, the record is not payable.
Keep release rules, evidence, and AML decision trails separate and retrievable. IRS IRM 4.26.9's structure, covering reporting, recordkeeping, and AML program requirements, is a practical model for that separation.
Make hold and release logic explicit#
Make hold and release logic explicit so ops can apply it consistently. Use clear defaults like these:
| Trigger | Default action | Required before release |
|---|---|---|
| Unresolved AML outcome | Hold | Cleared review result with timestamped decision record |
| Blank, stale, or contradictory required control record | Hold | Current and internally consistent control snapshot |
| Missing or inconsistent required compliance record | Hold | Status resolved in the payable record |
| Market specific legal or compliance hold | Hold | Hold lifted by responsible owner and logged |
Documented overrides should require compliance approval. If commercial urgency is cited, keep the default as hold unless legal or compliance signs a time-bound exception tied to specific payout IDs.
Match approvals to the payment execution unit#
Match approval evidence to the payment execution unit. For single payouts, approval should map to that single instruction. For Payout Batches, approval should map to the batch ID, included population at approval time, and the freeze timestamp.
If batch membership changes after approval, treat it as a new decision and log the change.
Define retry handling before failures happen#
Define retry handling before failures happen. When checks are delayed or submissions fail, move the payout into a retryable hold state and rerun gate evaluation before issuing a new instruction.
Track retries as a transaction-style log: original hold reason, remediation note, recheck timestamp, new approval reference, provider response, and final disposition. IRS IRM 4.26.9's reference to multiple transaction logs and evidence review supports this approach.
Verify legal sources before adding new gates#
Verify legal source reliability before encoding new market-specific gates. Do not treat FederalRegister.gov's web version alone as final legal authority. Verify against an official Federal Register edition.
For example, the 09/04/2024 rule at 89 FR 72156 is important, but cited scope language names registered investment advisers and exempt reporting advisers. Confirm applicability with counsel before turning that text into a payout release rule.
Expected outcome: when you hold a payout, you can show the unresolved control and evidence. When you release one, you can show the gate snapshot, approval trail, and execution record, whether it was a single payout or a batch line. For a related look at payout friction, see Invisible Payouts: How to Remove Payment Friction for Contractors Without Sacrificing Compliance.
Before rollout, map each hold/release rule to concrete status events, approval ownership, and replay-safe retry behavior in Gruv Docs.
Build the post payout evidence and reconciliation pack#
After release, your control objective is proof. Each payout cycle should have one retrievable pack that lets finance, compliance, and tax reconstruct what happened without relying on memory.
Define the minimum evidence pack#
Create one minimum evidence pack per payout cycle and keep it complete. For U.S.-linked foreign-asset cases, include artifacts that support your Form 8938 relevance decision, the underlying asset/account records, filing status, and any overlap review with FBAR (FinCEN Form 114).
| Artifact | What it should show | Quick check |
|---|---|---|
Form 8938 relevance decision | Why the case was treated as in scope or out of scope | Decision is tied to the period and filer context |
| Asset/account snapshot | Specified foreign financial assets considered, including foreign financial accounts where applicable | Account counts or max-value checkpoints are traceable to the filing period |
| Filing status record | Whether Form 8938 was attached to the annual return, or why it was not required | If required, timing aligns with the return due date (including extensions) |
FBAR overlap check | Whether separate FBAR review was needed | No assumption that Form 8938 replaces FBAR |
| Guidance review note | The rule interpretation date used for the cycle | Notes reflect that FATCA guidance can change |
Treat the cycle as incomplete if a Form 8938 relevance or filing decision cannot be tied to supporting asset records.
Reconcile from the ledger outward#
Reconcile from your records first, then confirm filing outcomes. Start from the asset/account population you identified and validate outward so filing decisions are supported by a clear evidence trail.
Use checkpoint-style fields from Form 8938, for example account counts, maximum values, and status changes, as part of that trail. Keep any exception notes in the same cycle pack so multi-step outcomes remain auditable in one place.
Add tax and reporting artifacts when relevant#
Include tax and reporting artifacts when relevant, and document the relevance decision. For U.S.-linked foreign-asset cases, store FATCA / Form 8938 relevance flags and separate FBAR overlap review records where applicable.
Form 8938 is used to report specified foreign financial assets and is filed with the annual return by that return's due date, including extensions. This requirement does not replace FBAR (FinCEN Form 114). The IRS cites aggregate value exceeding $50,000 as a baseline reference for certain U.S. taxpayers, but thresholds differ by taxpayer context and guidance continues to evolve. If no income tax return is required for the year, Form 8938 is not required for that year. Non-reporting of covered foreign financial assets can carry serious penalty risk.
Set retention and retrieval rules now#
Define retention and retrieval rules now, before audit pressure. Set where the pack lives, who owns it, and how it is indexed so requests do not become ad hoc investigations.
At minimum, index by tax year, filer context, and reporting-form relevance decision. Validate with a retrieval drill, for example one in-scope Form 8938 case, one out-of-scope case, and one case with FBAR overlap review. If that request still requires manual cross-tool digging, the evidence layer is not ready.
Assign ownership and escalation points before incidents happen#
Indecision is a control failure, so assign decision ownership and escalation routes before cases stack up.
Give each decision one accountable owner#
Use one clear ownership matrix so each decision has a clearly accountable owner. One team may split legal interpretation, control decisions, financial impact, and case execution across different owners; another may use a different structure. The key is clarity, not a specific org chart.
| Area | Primary owner | Decision to make | Quick verification |
|---|---|---|---|
| Regulatory interpretation | Named risk owner | Whether a rule applies and how to interpret it in context | Case has a named owner and written interpretation |
| Control operation | Named control owner | Whether checks pass, fail, or require review | Case shows control status, reviewer, and decision time |
| Operational impact | Named process owner | What action is required before release | Escalated case ties to the underlying records |
| Case execution | Named queue owner | What happens next and when to escalate | Queue shows owner, next action, and escalation reason |
Define escalation triggers before incidents#
Define escalation triggers around repeated gaps, serious risk, and unresolved uncertainty. Do this before incidents so risk drives escalation instead of inbox noise.
Use trigger language your teams can apply consistently, such as repeated control failures, serious unresolved risk, or missing required records before release. In construction contexts, repeated gaps or serious risks can trigger site shutdown actions; in any context, these issues should move out of routine queue handling quickly.
Set response priorities by severity#
Set severity-based handling rules so high-risk cases are handled first. You do not need one universal deadline, but you do need explicit priorities and ownership by severity.
High-severity cases should route immediately to the accountable owner. Medium- and lower-severity cases can remain in queue, but each case still needs a named owner and a documented next action.
Record escalation outcomes in one audit trail#
Record every escalation outcome in a centralized audit trail. Capture the trigger, facts reviewed, rationale, approver, decision time, and release, hold, or reject outcome. Keep it in one centralized evidence trail so reviews are traceable.
If you allow exceptions, document the rationale and follow-up plan in the same record. Clean, complete logs are what let you prove what was done and when. Fragmented records are what create avoidable audit and timeline risk. For more on tax form controls, see W-8BEN and W-8BEN-E Platform Compliance for Contractor Payouts.
Decide what to automate and what to keep manual#
Automate repeatable, status-based controls with clear evidence, and keep interpretation-heavy decisions manual until outcomes are consistently reviewed and understood. This is where the ownership model from the last section matters. Once decision rights are clear, you can automate what is repeatable, traceable, and low ambiguity instead of forcing one process onto every case.
Automate deterministic controls first#
Automate deterministic controls first. Prioritize checks where the system confirms presence, status, approvals, evidence collection, or other policy-gated conditions with a clear pass/fail outcome.
For each automated decision, keep the source record, decision timestamp, and policy context in the same audit trail. If you cannot reconstruct why a rule fired, the control may be fast, but it will be weak in an audit.
Automation helps here because manual checks tend to become periodic, reactive, and fragmented. A structured digital process can trigger, monitor, and track actions in real time.
Keep high-ambiguity judgments manual#
Keep high-ambiguity judgments manual. If a case depends on legal interpretation, conflicting facts, or narrow context, route it to a human reviewer and record the rationale.
The core risk is not only a wrong decision. It is scaling the same wrong decision across many cases before it is corrected.
Judge automation by reliability before speed#
Judge automation by reliability first, then speed. Evaluate each candidate control by outcome consistency, turnaround time, and audit defensibility together.
Move a control into automation when reviewers usually reach the same outcome from the same evidence and exceptions are limited and understood. If reviewers frequently disagree or escalations often reverse initial outcomes, fix the policy or evidence standard before expanding automation.
Use shared platform controls only when they stay auditable#
Use shared platform controls only where they reduce local variation and remain auditable. Treat this as a scoped design choice, not a blanket shortcut.
Confirm who performs each check, what evidence you can retrieve, and whether outputs are detailed enough for your audit trail. Keep a recurring review cadence to reassess manual exceptions and promote only stable, well-evidenced controls into policy-gated automation.
Track the metrics that predict compliance surprises#
Once obvious checks are automated, watch for drift. If a metric has no owner and no corrective action threshold, it is reporting, not control.
Watch leading indicators of stress#
Track leading indicators that show stress before an incident. Monitor unresolved foreign-asset classifications, missing Form 8938 support data, and open FBAR applicability decisions, then split each by filing entity type and tax year. Assign clear owners for each metric so rising exceptions trigger action, not just discussion.
Separate tax intake from filing readiness#
Separate tax document intake from filing readiness risk. Keep general intake metrics distinct from foreign-asset reporting readiness so FATCA/Form 8938 exposure stays visible.
| Status area | What to track | Key note |
|---|---|---|
| Form 8938 threshold status | Whether applicable thresholds are exceeded for certain U.S. taxpayers | Foreign financial assets must be reported on Form 8938 under FATCA when applicable thresholds are exceeded |
| Form 8938 support data | Whether Form 8938 support data is complete | Keep general intake metrics distinct from foreign-asset reporting readiness |
| Form 8938 filing readiness | Whether the form is ready to be attached to the annual return | Track by the return's due date, including extensions |
| FBAR applicability status | Whether a separate FinCEN Form 114 filing applies | Filing Form 8938 does not remove a required FinCEN Form 114 filing |
| No income tax return required | Whether no income tax return is required | Form 8938 is not required in that situation |
For certain U.S. taxpayers, foreign financial assets must be reported on Form 8938 under FATCA when applicable thresholds are exceeded. Operationally, track support-data completeness, filing readiness by the return's due date, including extensions, separate FBAR applicability status, and cases where no income tax return is required.
Measure control quality, not just volume#
Measure control quality, not just volume. Track threshold determination quality and rework rate on Form 8938/FBAR decisions, and pair each with a documented corrective action threshold. When thresholds are breached, require a rule review or sample case audit.
Your evidence should let a reviewer reconstruct why the metric moved. Keep case IDs, decision timestamps, reviewer or rule source, hold or release outcomes, and foreign-asset threshold or support-data status for Form 8938 and FBAR.
Fix common failure modes without restarting the entire program#
When metrics show drift, fix the failing control path directly instead of restarting the whole program. In the EA review context, significant control weaknesses led to a directed pause in operations, targeted correction work, and readiness assessments run alongside the review.
Remove U.S. federal references from global paths#
Split U.S. federal references out of global operating paths. One common failure mode is copying U.S. federal references, including DFARS Part 252, into default controls for every market. Keep DFARS Part 252 in a clearly labeled U.S. federal branch, since it is organized around instructions for using provisions and clauses and the text of those provisions and clauses.
Recovery: separate controls by jurisdiction, then retrain owners who approve holds and exceptions. Validate the fix by sampling non-U.S. cases and confirming U.S. federal references are not present unless a federal trigger exists.
Require a written record for every override#
Require a written exception record for every override. If overrides can happen without a standard record, your exception process is not controlled.
Use one exception template for each release against a failed or incomplete control. Capture the affected item, reason, approving role, timestamp, expiry, and required follow-up check, then review exceptions within one reporting cycle. Keep an explicit Items for Follow-up register so repeated patterns are tracked to closure.
Rebuild the evidence chain end to end#
Rebuild the evidence chain so each decision is traceable both ways. Complete data is not enough if a reviewer cannot connect approval, review activity, and operational outcome.
Use shared references across review records and execution records so the trace is exportable as one audit path. An Appendix B style evidence record is a practical format: list key documents reviewed, interviews, and observations. Test recent cases and confirm reverse trace works without manual reconstruction across teams.
Run readiness checks before restart#
Run formal readiness checks before restarting impacted work. The EA review process included readiness assessments performed concurrently with the review, rather than relying on closure statements alone.
Before restart, compare corrective actions against readiness checkpoints and open follow-up items. If gaps appear, hold only the affected scope and fix the linkage before resuming full operations.
For team enablement, see How to Build a Payment Compliance Training Program for Your Platform Operations Team.
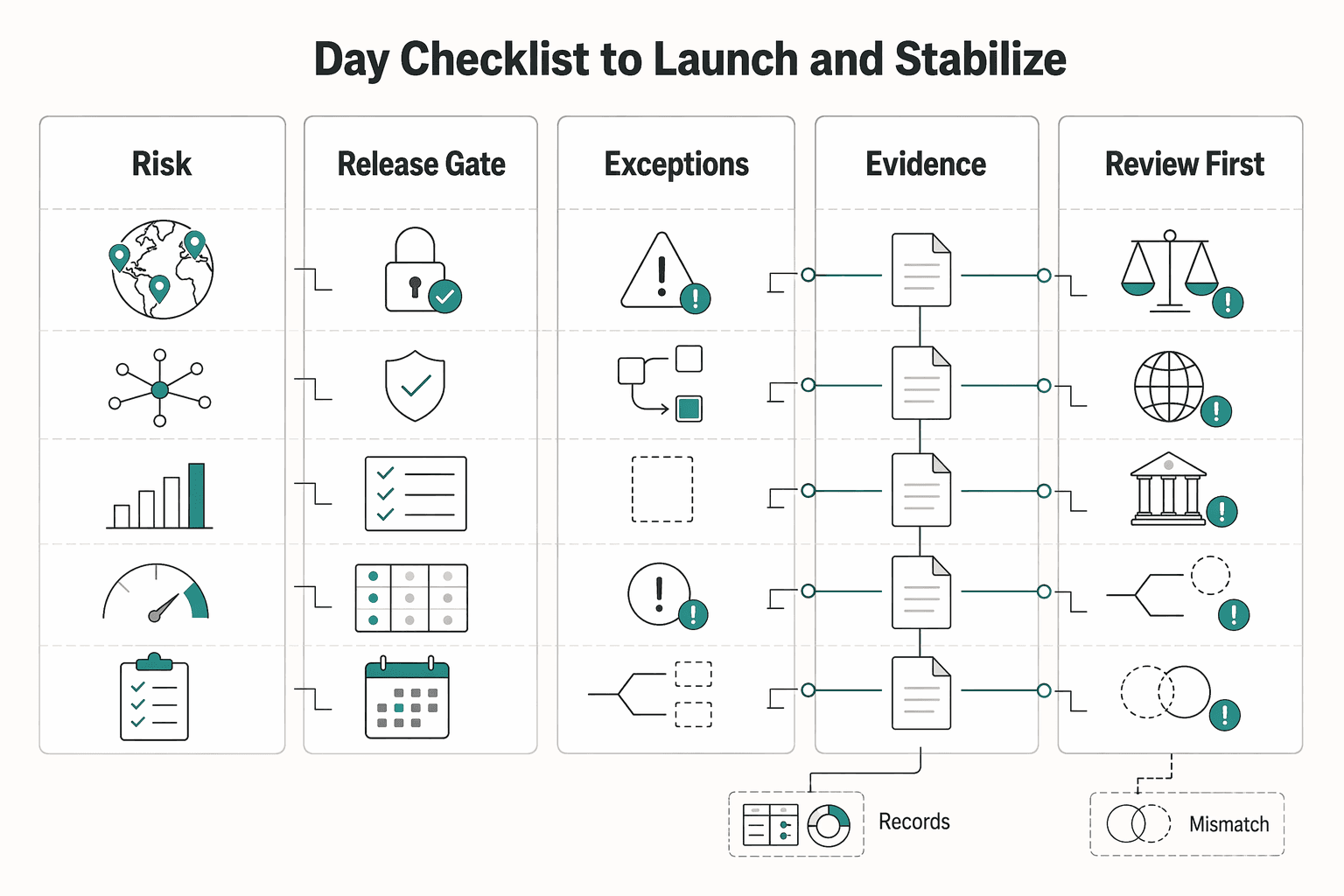
30 day checklist to launch and stabilize#
Keep day 1 to 30 narrow and auditable. You should be able to show what is in scope, what blocks release, what evidence exists for reporting, and when tax review is required.
| Day 1-30 action | What to do | Key detail |
|---|---|---|
| Confirm scope by market, payment flow, and risk tier | Create one inventory for active countries, payout paths, and review depth | Flag any flow still pending legal or tax design review |
| Implement reporting gates with explicit completion states | Define what counts as complete for each filing decision, record who made the decision, and timestamp it | Document whether an income tax return is required and whether Form 8938 and FBAR are each in scope |
| Publish threshold and exception rules | Set clear triggers for when Form 8938 analysis is required, who can approve exceptions, and when ambiguous cases must escalate for tax review | Use current Form 8938 instructions for threshold checks rather than relying on older summary language |
| Stand up evidence packs before month-end | Keep FATCA/Form 8938 and FBAR as separate tracks | Where in scope, confirm thresholds using current Form 8938 instructions, including the cited $50,000 last day / $75,000 anytime test for certain specified domestic entities |
| Finalize ownership and escalation triggers across legal, compliance, finance, and ops | Assign clear owners before incidents occur | Define when ambiguous FATCA/Form 8938 or FBAR questions must escalate out of operations |
| Review the first monthly cycle before scaling | Fix the top three repeat failure points first | Threshold misclassification, incomplete account-value evidence, and late reporting decisions |
- Confirm scope by market, payment flow, and risk tier.
Create one inventory for active countries, payout paths, and review depth. Flag any flow still pending legal or tax design review.
- Implement reporting gates with explicit completion states.
Define what counts as complete for each filing decision, record who made the decision, and timestamp it. At minimum, document whether an income tax return is required, since if no income tax return is required, Form 8938 is not required, and whether Form 8938 and FBAR are each in scope.
- Publish threshold and exception rules.
Set clear triggers for when Form 8938 analysis is required, who can approve exceptions, and when ambiguous cases must escalate for tax review. Use current Form 8938 instructions for threshold checks rather than relying on older summary language.
- Stand up evidence packs before month-end.
Keep FATCA/Form 8938 and FBAR as separate tracks: Form 8938 is attached to the annual return and filed by that return's due date, including extensions, and it does not replace FBAR (FinCEN Form 114). Where in scope, confirm thresholds using current Form 8938 instructions, including the cited $50,000 last day / $75,000 anytime test for certain specified domestic entities. Retain account-level support such as account counts and maximum values. IRS materials warn there are serious penalties for failing to report required foreign financial assets.
- Finalize ownership and escalation triggers across legal, compliance, finance, and ops.
Assign clear owners before incidents occur, and define when ambiguous FATCA/Form 8938 or FBAR questions must escalate out of operations.
- Review the first monthly cycle before scaling.
After one full cycle, fix the top three repeat failure points first, especially threshold misclassification, incomplete account-value evidence, and late reporting decisions.
This pairs well with our guide on How to Build a Trust and Safety Program for Your Contractor Marketplace.
Frequently Asked Questions
What is the minimum viable contractor compliance program for a platform paying across many countries?
This grounding does not establish a single globally sufficient minimum control set, so the practical baseline is a program tailored to your size, complexity, resources, and culture. At minimum, your process should support documented payout decisions, periodic screening after engagement, and evidence you can trace from decision to payout outcome. If you cannot show why a payee was eligible and reconstruct that decision path, the program is likely too thin.
How should a multi-country program differ from U.S. federal contractor compliance requirements?
Treat U.S. federal contractor requirements as a separate scope, not a default global template. OFCCP Section 503 requirements include specific documentation expectations, such as documenting the design and implementation of an audit and reporting system for an affirmative action program. Apply those requirements when they are in scope, and avoid copying them into markets where they do not apply.
When should we block a payout versus release it with monitoring?
There is no globally valid rule for every jurisdiction, so set explicit block-versus-release criteria in your control policy and escalate edge cases to legal or tax counsel. One documented failure mode is screening only at onboarding and missing later list updates, so stale or missing screening evidence should not be treated as routine. If you use monitored release, keep it bounded, documented, and time-limited.
Which controls should be centralized globally and which should be localized by market?
There is no universal global split, but a practical approach is to centralize control mechanics and localize legal interpretation. Keep evidence structure, screening cadence, and traceability rules consistent across markets, while adapting market-specific legal and reporting requirements locally. This helps reduce fragmentation that can create audit and timeline risk.
What should trigger escalation to legal or tax counsel immediately?
Escalate when uncertainty could change who can be paid, how payment is reported, or which legal framework applies. Typical triggers include unclear tax or classification treatment, requests to apply U.S. federal contractor rules outside confirmed scope, and external challenges that put prior release decisions in doubt. Do not let operations teams resolve those ambiguities by assumption.
What audit evidence should we be able to produce within 24 hours of a regulator or partner request?
Do not assume a universal 24-hour legal duty across jurisdictions, but design for fast retrieval as an operating standard. Your evidence pack should let a reviewer trace decisions through outcomes, including audit/reporting-system documentation, screening records, and decision records tied to payout outcomes. Run this as a recurring test so evidence assembly does not depend on rebuilding history from inboxes.
Try a related tool
Daniel writes about contractor classification, cross‑border hiring basics, and compliance-first operating models for global clients and independent contractors.
Priya specializes in international contract law for independent contractors. She ensures that the legal advice provided is accurate, actionable, and up-to-date with current regulations.
Sources
- acquisition.gov/far/2.101trusted
- dodcio.defense.gov/Portals/0/Documents/CMMC/AG_Level1_V2.0_Fina...trusted
- dodcio.defense.gov/Portals/0/Documents/CMMC/AssessmentGuideL2.pdftrusted
- dol.gov/agencies/ofccp/faqs/section-503trusted
- dot.ri.gov/business/contractor_compliance.phptrusted
- eastvalleywater.gov/media/cj3hyxca/resolution-201816-signed-with...trusted
- federalregister.gov/documents/2026/02/27/2026-03962/employee-or-...trusted
- federalregister.gov/documents/2014/08/08/2014-18557/government-c...trusted
Educational content only. Not legal, tax, or financial advice.
Related Posts

Build a Global Contractor Payment Compliance Calendar for Monthly, Quarterly, and Annual Obligations
A usable first version of your **global contractor payment compliance calendar monthly quarterly annual** should work as a control document, not just a list of dates. Keep monthly, quarterly, and annual obligations in one place, assign clear owners and reviewers, and define when unclear rules or missing evidence must be escalated. If you are building version 1, we recommend starting with the obligations your team can evidence today and marking the rest for legal review.

Invisible Payouts: How to Remove Payment Friction for Contractors Without Sacrificing Compliance
Invisible payouts should make life easier for contractors without hiding the controls your team needs. Contractors should get a predictable, low-friction flow, while internal teams can still enforce and document payout decisions when needed. If you run contractor payouts at scale, you need both outcomes at once. We recommend treating every easy payout as a controlled release path your team can replay later.

GDPR for Marketplace Platforms: How to Handle Contractor and Seller Personal Data Compliantly
Treat this as an operating decision, not a policy exercise. If you own compliance, legal, finance, or risk for a platform, your job is to decide who owns each GDPR duty. You also need to define what evidence must exist, what your team reviews on a recurring basis, and which issues need escalation before a launch or vendor change goes live.