
Yes. If you accept or process payment cards, PCI DSS likely applies to your business, and your burden depends on where cardholder data is entered and whether your systems store, process, transmit, or can affect that data path. Hosted processor checkout can reduce direct exposure, but it does not remove merchant responsibility, so map the payment flow and confirm your validation route with your acquirer.
If you accept or process payment cards, treat PCI DSS as a current business requirement, then narrow your scope on purpose. The goal is to keep cardholder data from spreading into tools and workflows you never meant to involve, so the work stays manageable instead of turning into surprise cleanup later.
That is the tradeoff you are managing. You want easy checkout and steady growth, but payment account data carries specific risk. Vulnerabilities can show up across the card-processing network, not only on the payment page.
Start with one question: do you accept or process payment cards? If yes, PCI DSS likely applies in some way, so your next step is to map exactly what your setup touches.
Use this checkpoint: can you identify where card details are entered, name the provider handling that entry, and confirm whether card data passes through your site, app, inbox, logs, or support tools? If not, treat your scope as uncertain until you can answer clearly.
Most avoidable pain starts when teams guess scope too early. Common failure patterns include assuming a processor removes all responsibility, or adding payment features before checking where card-related data might surface in internal tools, traces, or custom code.
A right-sized path matters more than an overbuilt one. If your environment stores, processes, or transmits cardholder data or sensitive authentication data, your PCI DSS scope is typically broader. If not, the path may be simpler, but it still needs validation. Either way, non-compliance can lead to penalties, fines, and related costs.
Use this rule: if you cannot prove a tool is outside the cardholder-data path, do not assume it is out of scope.
By the end of this article, you should have:
The operating principle is simple: keep your cardholder-data footprint as small as you can justify, then document and maintain that boundary.
Related reading: Good Strategy/Bad Strategy for Freelancers: A 3-Tier System for Compliance, Profit, and Delivery.
PCI DSS is a standard for protecting cardholder data in card-processing environments, not a label for your entire security program. Before you buy tools, confirm where your flow may store, process, or transmit cardholder data.
Scope is a core PCI DSS checkpoint. Start with the systems and workflows that touch card data directly, then include connected components and service-provider or acquirer systems that can affect that path.
Use this quick check before committing to a payment tool:
If those answers are unclear, treat your scope as unresolved until the data flow is visible.
Teams often buy based on broad security claims instead of card-data architecture. Marketing language can help with context, but it does not replace clear evidence of how card data moves through the stack.
Use PCI SSC quick-reference material the same way. It helps frame scope and reporting, but it does not replace official PCI documents.
If you accept electronic card payments as a merchant, assume PCI DSS responsibilities apply now, then size your scope correctly. The key decision is how much of your environment sits in the card-data path versus how much is handled on processor-hosted infrastructure.
Your scope follows cardholder data. If any part of your setup processes, stores, or transmits cardholder data, your scope is broader. If the processor fully hosts card entry, your direct exposure may be lower, but responsibilities are not automatically removed.
Use this fast rule: if you accept electronic card payments, compliance is an active operating requirement, not a later cleanup task.
Start by mapping where card data can appear and which systems could affect that path. You should also be able to show evidence if your acquirer, processor, or card-brand program asks for it.
Ask this first: does any part of your environment process, store, or transmit cardholder data?
If yes, expect broader scope. That can include point-of-sale devices, servers, personal computers, wireless hotspots, and web shopping applications connected to the payment path.
If no, and card entry happens only on processor-hosted pages or links, your direct handling may be reduced. Reduced does not mean removed, because vulnerabilities can still extend into service-provider and acquirer-operated systems.
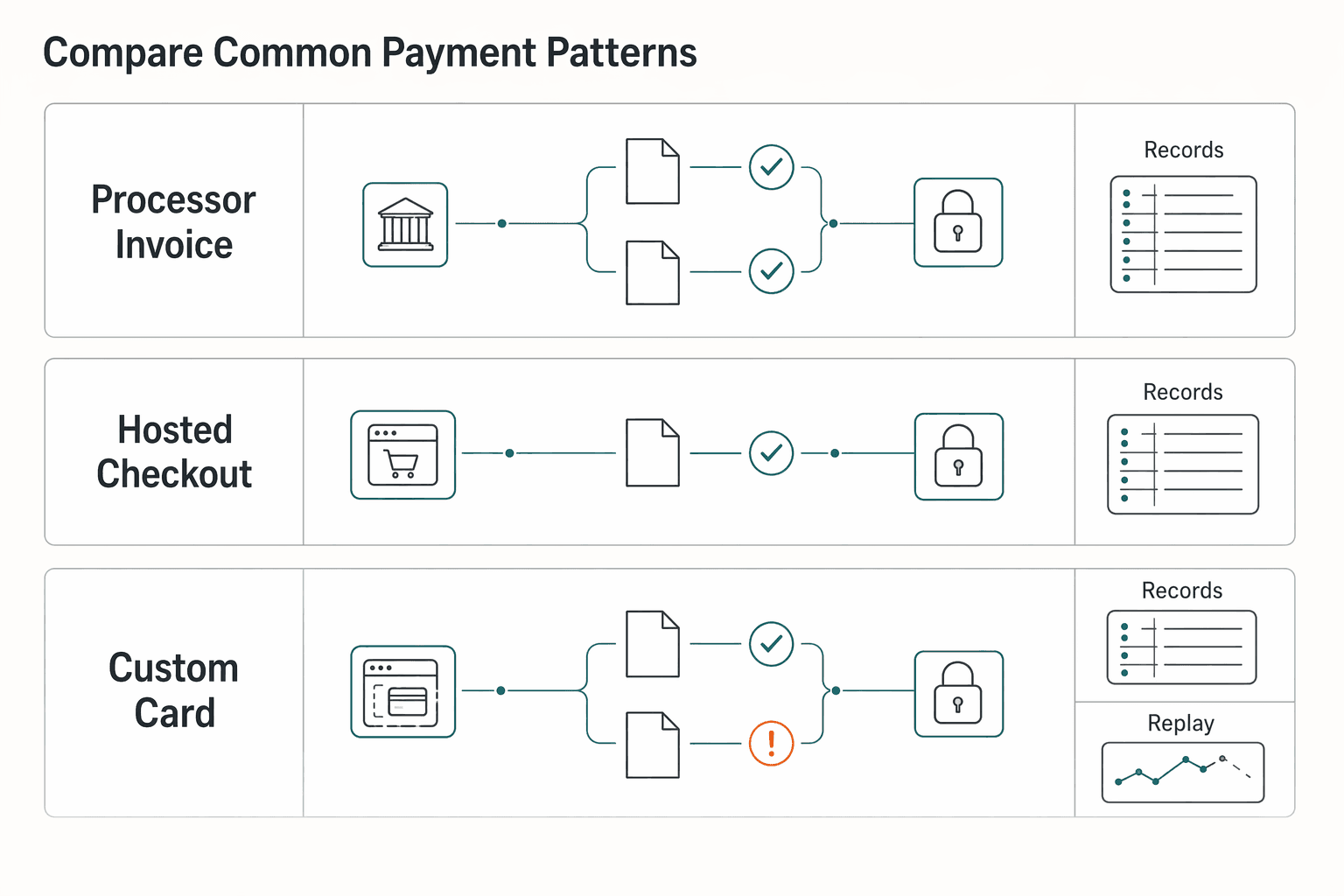
| Payment pattern | Who receives card entry | Likely direct exposure in your environment | Verify first |
|---|---|---|---|
| Processor invoice link | Processor-hosted page | Can be lower | Confirm card details are entered only on the processor-hosted page |
| Hosted checkout | Processor-hosted checkout flow | Can be lower | Confirm your environment does not process, store, or transmit cardholder data |
| Custom card form on your site | Your app and connected systems may touch the flow | Higher | Confirm whether your web app or connected systems process, store, or transmit cardholder data |
The common mistake is treating outsourced processing as outsourced responsibility. Processor-hosted flows can reduce direct card-data handling, but you still need to understand and prove your actual scope.
A practical checkpoint is to trace where card details are entered, then verify whether they pass through systems you control. If you cannot answer that clearly, treat the setup as higher risk until you can.
Related: A Guide to Stripe Radar for Fraud Protection.
Map the full payment flow before you make any scope decision. For PCI DSS, scope follows where cardholder data can exist or move, so a one-page flow map is usually more useful than assumptions.
Treat this as a data flow diagram: customer entry point, payment processor, outbound and inbound events, and each internal system tied to cardholder-data handling. Ask where payment-related data could actually appear, not just where you expect it to go.
Map it left to right. Start with the customer entry point and payment processor. Then add events back to you, such as webhooks, exports, alerts, or notifications. Finish with internal systems such as your site, backend, CMS, CRM, ticketing, analytics, logs, finance tooling, and admin screens.
Mark any component that stores, processes, transmits, or can influence cardholder-data handling. The cardholder data environment includes systems, networks, and processes tied to that handling, not only the card-entry screen. Accurate scoping also includes third-party integrations and indirect dependencies, not just the obvious checkout component.
| Payment pattern | Who handles card entry | Systems in scope | Likely PCI DSS assessment burden | Biggest failure mode |
|---|---|---|---|---|
| Processor invoice link | Processor-hosted page | Your link-out channels, processor handoffs, and internal tools that may receive payment-related data | Varies by actual data flow; confirm with your map and dependencies | Assuming processor involvement alone defines scope |
| Hosted checkout redirect or embedded hosted flow | Processor-hosted collection experience | Your checkout launcher page, integrations, webhook/event paths, and downstream systems | Varies by integrations and indirect dependencies | Checklist-only scoping without end-to-end flow evidence |
| Custom card form on your site or app | Your environment may handle entry before processor transmission | Web app, backend services, APIs, storage, logs, monitoring, endpoints, connected networks, and third-party dependencies | Commonly broader because your systems may store, process, or transmit cardholder data directly | Missing internal or third-party data paths in scope mapping |
Use this as a template, then replace the generic labels with your real stack.
For each box and arrow, mark whether cardholder data can appear in transit, storage, or debug traces. Do the same for sensitive authentication data, including security codes, PINs, and magnetic stripe data that should never be stored.
Pay extra attention to potential exposure points:
You are not assuming all of these are in scope by default. You are checking whether any of them can receive payment-related data and widen exposure. Include transmission handoffs to service providers in the map as well.
If you cannot show a system is out of scope, treat it as in scope until you verify otherwise. That is a practical operating posture, even if it is not phrased as a direct PCI SSC rule.
Keep the working output simple: one current flow diagram, one list of touched components, and one note per component on what data may appear there and how you verified it. That gives you a defensible scope boundary for assessment and a reliable baseline when your payment flow changes.
If your scope map is still ambiguous after you trace every payment touchpoint, get a practical second pass before you lock architecture: Talk to Gruv.
Choose the pattern that minimizes direct cardholder data handling in your environment first, then optimize fees and conversion. In practice, that often means favoring processor-hosted collection flows unless you have the operational depth to support a broader, continuously maintained control surface.
Custom checkout can be a valid choice, but it can expand what you must secure and explain. Once card entry or transmission touches your stack, scope can spread beyond the payment UI into connected systems and processes.
Hosted processor flows usually reduce that exposure, but they do not remove your responsibilities. Vulnerabilities can still appear across the payment network, including service-provider and acquirer-operated systems, so you still need clear boundaries and oversight.
Use this decision rule: if you do not have dedicated security operations, choose the integration pattern that keeps direct cardholder data handling to a minimum.
The hard part of a more custom integration is not only the security controls. It is proving, over time, that the controls still match reality. PCI guidance emphasizes continuous compliance, so your design needs to stay auditable after launch, not just at review time.
For retries, webhooks, and reconciliation, treat idempotency as an engineering guardrail. It is not a PCI DSS requirement by itself, but it can make duplicate-event handling easier to explain during reviews.
Keep the evidence model simple and current:
A practical way to reduce exposure is to avoid collecting data you do not need. If a field is unnecessary for authorization, support, or reconciliation, remove it from forms, scripts, and support workflows.
Apply the same discipline to payment-related data and checkout changes. Do not add features that increase handling complexity unless there is a clear, necessary, documented reason.
A practical red flag is checkout drift. A team can pass an audit in June and still face a script-related incident by September if checkout changes are not tightly controlled. Before you add new checkout features, confirm who can change the flow, what scripts are present, and how those changes are reviewed and logged.
You might also find this useful: A Guide to SOC 2 Compliance for SaaS Companies.
Do not guess your validation route after choosing an integration pattern. A mismatch usually creates either unnecessary audit effort or a compliance gap between your real architecture and what you reported.
For many merchants, a common validation artifact is a Self-Assessment Questionnaire (SAQ). It was designed by the PCI Security Standards Council to help merchants validate and report compliance without a full audit, but accurate submission still depends on scoping and documentation.
An SAQ works when your cardholder data environment is clearly defined. It is a self-validation path for simpler, well-defined setups, yet many teams still find it complex because modern architectures do not always map cleanly to older SAQ categories.
There are seven SAQ types, from SAQ A to SAQ D. You do not need to memorize them all upfront. You do need to distinguish common patterns like SAQ A versus SAQ A-EP:
Classify the customer payment experience, then verify whether your systems, pages, scripts, and support tools truly stay out of the payment-data path.
| Setup pattern | Likely SAQ complexity | When to involve a QSA | ASV scanning note |
|---|---|---|---|
| Full redirect or processor-hosted checkout where your systems do not touch payment data | Lower complexity, often at the simpler SAQ end, commonly SAQ A if facts fit | Involve if scope is disputed, eligibility is challenged, or evidence is weak | Do not assume; confirm requirements with your acquirer and processor |
| You host the payment page, but processing happens elsewhere | Higher complexity, often closer to SAQ A-EP | Involve early if scripts, tags, page ownership, or browser-side responsibilities are unclear | Do not assume; confirm requirements with your acquirer and processor |
| Custom or mixed setup where your environment handles payment data, or scope is unclear | Often beyond lighter SAQ paths and may require deeper validation | Involve early before collecting evidence against the wrong route | Do not assume; confirm requirements with your acquirer and processor |
The middle pattern is often misclassified. If you host the payment page, browser-side security remains your responsibility, and even one added JavaScript snippet can invalidate an assumed SAQ A posture.
Use a hard checkpoint: if checkout is on your domain, or scripts can be injected on pages presenting payment fields, do not assume the lightest SAQ path. Recheck the architecture first.
Follow this order:
If your acquirer or platform partner asks for assessor-led validation, involve a Qualified Security Assessor early instead of rebuilding later. Proper preparation, including scoping and documentation, is what keeps submissions accurate.
Volume and merchant-level framing can be useful context, for example common references to Level 2-4 and fewer than 6 million annual transactions, but it is not a standalone rule. Architecture fit still matters.
Submission and enforcement details can differ by program. When unclear, confirm with your acquirer and processor support channels.
If you are unsure what to submit, start with your acquirer channel and any contracted service provider involved in your card environment. PCI SSC maintains PCI standards and publishes educational guidance, but its quick-reference material explicitly says that guidance does not replace or supersede the standards or supporting documents.
PCI SSC governs the standard. In the broader card network, the five brands commonly associated with PCI DSS are Visa, Mastercard, American Express, Discover, and JCB.
Your operational requirements are generally communicated through the merchant relationship, not directly by PCI SSC. PCI SSC defines acquirers as the financial institutions that initiate and maintain merchant card-acceptance relationships, so the acquirer channel is typically where submission requirements are communicated.
Use this rule in practice: the standard defines possible validation artifacts, but your contract path can determine which artifact you submit and when. That can include SAQ-related reporting steps or a request to involve a Qualified Security Assessor.
Before you prepare evidence, confirm which party maintains your merchant card-acceptance relationship and align your submission to that party's request. If your channels conflict, resolve the mismatch before you file anything.
For a step-by-step walkthrough, see Best Merch Platforms for Creators Who Want Control and Compliance.
Build a living evidence pack early, then keep it current. For PCI DSS, this is one of the fastest ways to reduce rework when your acquirer or program channel asks for SAQ or reporting artifacts.
A strong starter pack is about traceability, not volume. You should be able to show scope, ownership, and recent control activity without digging through old tickets.
A practical starter set can include:
| Artifact | What it should show |
|---|---|
| Network or data-flow diagram | Where payment data enters, where it is sent, and which services can affect the cardholder data environment |
| Asset inventory | In-scope or potentially in-scope components |
| Access-control evidence | Who has admin access, how approval works, and the latest review |
| Incident process | Who is notified and how containment and escalation work |
| Change records | Payment-related code, infrastructure, plugins, or configuration changes |
If a SAQ answer depends on a diagram or record, keep that artifact dated and easy to find. If your documentation conflicts with operational reality, treat scope as unresolved until the mismatch is fixed.
Name clear owners for scans, alert review, asset updates, and SAQ or reporting submission. Also define who approves final submission through your required channel.
QSA and ASV are not universal requirements. But if your route requires either one, keep those outputs in the same evidence pack. In some higher-validation tracks, this may include an annual Report on Compliance and quarterly ASV scans, based on card-brand and acquirer expectations.
Use a quick ownership check:
Do not limit evidence to clean system diagrams. PCI SSC quick-reference material, which is supplemental to formal PCI standards, highlights exposure risk in paper-based storage, transmission to service providers, and remote access connections. It also notes that vulnerabilities may extend to service-provider and acquirer-operated systems.
Before you call the pack ready, run one internal verification pass. For each SAQ or assessment control you plan to answer, map it to a named document and a named owner as an internal readiness check. This makes gaps and stale evidence easier to catch before filing.
Need the full breakdown? Read GDPR Compliance Checklist for Freelancers Working With EU Clients.
To reduce rework, use a scope-first sequence: confirm scope, complete the SAQ, collect any required scans or reports, review with stakeholders, then submit through your required channel. Rework usually starts when teams answer SAQ items before scope facts are stable.
Start by confirming where card data is collected across your real channels, such as website checkout, terminal, virtual terminal, and phone orders. Scope is about which systems touch payment card data directly or indirectly. If those scope facts are still disputed, SAQ answers can be unstable.
A practical rule is simple: if you cannot clearly explain where cardholder data goes, the assessment is not ready.
Once scope is stable, complete the SAQ from current evidence that shows controls are in place and operating. The proof matters as much as the technical implementation.
PCI SSC quick-reference guidance separates scope, SAQ, and reporting as distinct compliance steps, with v3.2.1 listing SAQ on page 33 and reporting on page 35. Use that as a sequencing check, not a paperwork exercise.
If you find signs of sensitive authentication data being stored after authorization, remediate before you represent control status in submission.
After the SAQ is complete, gather the external outputs your route requires, such as scans or assessor outputs where applicable. Do not assume ASV or QSA is universal, but if your acquirer or program path expects one, bring it in before submission.
If answers are uncertain or disputed, escalate early through the right assessor path instead of guessing. That matters even more when service-provider or acquirer systems affect exposure.
Before filing, do one stakeholder review with the people who own the relevant facts. Then keep assessment evidence and key stakeholder decisions organized internally.
Treat PCI maintenance as continuous operations, not a once-a-year task. One practical operating model is a light monthly internal check, a deeper quarterly review, and an added scope check when meaningful changes occur. That helps keep your controls aligned with reality throughout the year.
| Timing | Focus | What to check |
|---|---|---|
| Monthly | Catch drift early | Whether documented PCI scope, data-handling position, and assigned responsibilities still match current operations |
| Quarterly | Retest assumptions | Whether current operations still match documented controls and ownership model; whether retention and deletion management is checked at least every 3 months |
| After meaningful change | Rerun scope | Changes that could affect payment collection, transmission, storage, or administrative access, such as checkout changes, new plugins, platform migrations, and staffing changes |
Keep the monthly pass simple. Focus on whether your documented PCI scope, data-handling position, and assigned responsibilities still match current operations.
Check evidence, not memory, against your PCI assumptions. If you state that you do not store cardholder data, your policy should say why, and you still need a way to verify that position is being managed correctly.
Use the quarterly review to retest assumptions, not just complete tasks. Confirm that current operations still match your documented controls and ownership model.
For retention and deletion controls, keep a process that checks management is working correctly at least every 3 months. If you store account data, keep a procedure document for how it is stored. If you do not, state why in policy and keep the verification process active.
Do not wait for the calendar if a change could affect payment collection, transmission, storage, or administrative access. As an internal operating model, checkout changes, new plugins, platform migrations, and staffing changes can be useful scope-review triggers, even though PCI DSS does not prescribe that exact trigger list.
Compliance drift can come from unclear ownership. Required activities should be documented, assigned, understood, and embedded in real job duties.
Keep ownership visible in your operating records so tasks do not lapse when people change roles or leave.
Your approach is probably under-scoped if payment changes or vendor changes are moving faster than your evidence can keep up. Use these red flags as a signal to rescope before your next PCI DSS assessment.
Start with scope. A practical path is to confirm scope first, keep a reusable evidence artifact, and run ongoing reviews. The key question is whether your payment flow puts any of your systems in scope for handling cardholder data or sensitive authentication data.
Map the real payment path before you touch SAQ answers. PCI DSS applies to organizations that accept or process payment cards, and scoping comes before downstream validation.
Use this quick check:
If scope is unclear, flag the component as potentially in scope and resolve that ambiguity before choosing your validation route.
Create a scoped flow diagram and evidence checklist tied to your SAQ or assessment path. Keep it simple, but make it clear enough that someone else can follow the flow and see what is handled by you versus your processor.
For each component, capture:
This makes assessment completion and SAQ documentation submission easier.
Treat PCI as ongoing operations, not a one-time form task. Set a recurring control check and scope review, assign an owner, and document what changed.
Recheck scope any time payment pages, scripts, plugins, processors, or payment logic change. If submission expectations or validation obligations are unclear, request written clarification from your processor or acquirer and keep that response in your evidence records.
When you are ready to turn this checklist into an implementation plan with clear status handling and audit-friendly records, start with the integration patterns in the Gruv docs.
PCI DSS compliance means meeting the Payment Card Industry Data Security Standard requirements to protect payment card data. It focuses on card-processing environments and should not be treated as your entire security program.
Yes. If you accept card payments as a merchant, PCI responsibilities still apply. Using a processor can reduce direct handling, but it does not remove responsibility. Your scope depends on whether your site, tools, or providers store, process, transmit, or can affect payment card data security.
Yes. Hosted checkout can lower direct exposure if card entry happens only on processor-hosted pages, but merchant responsibility remains. Keep a current payment-flow map and verify which pages, scripts, vendors, and downstream systems can influence payment-data security.
QSA and ASV are part of PCI validation workflows. Whether you need them depends on your acquirer, card-brand program requirements, and your actual validation route. If your route requires assessor output or scans, confirm that early and keep those results with your evidence pack.
Start with the real data flow, not product labels. If your systems do not touch payment data and checkout is fully processor-hosted, the path may be simpler, often at the lighter SAQ end if the facts fit. If you host the payment page, run custom checkout, or your scripts and vendors can materially affect card-data security, expect a deeper path and confirm it with your acquirer.
Revisit scope whenever payment pages, scripts, plugins, processors, or payment logic change. A practical cadence is a light monthly internal check, a deeper quarterly review, and an added scope check after meaningful changes. Where scanning applies, PCI DSS requires internal and external vulnerability scans at least once every three months.
There is no universal first contact for every case. Use PCI SSC resources for standards interpretation, but align with your acquirer on submission and program requirements, since the merchant relationship typically drives what you must submit. If validation is affected, ask in writing and keep the response in your evidence records.
Kofi writes about professional risk from a pragmatic angle—contracts, coverage, and the decisions that reduce downside without slowing growth.
Priya specializes in international contract law for independent contractors. She ensures that the legal advice provided is accurate, actionable, and up-to-date with current regulations.
Educational content only. Not legal, tax, or financial advice.

Low-stress compliance in Germany comes from decision order, not tax tricks. Use this sequence: confirm core facts, apply conservative temporary assumptions, verify the few points that can break invoices or filings, and keep one evidence file that explains each decision.

**Treat Stripe Radar for fraud as a cashflow protection system, not a vanity fraud score.** Stripe Radar gives you real-time screening with AI and no extra development setup, but outcomes still depend on your rules and operations. Your job is simple: decide when to `Block`, `Review`, or `Allow`, then tie those decisions to fulfillment timing and client communication so fraud protection supports more predictable revenue.

**Build your SOC 2 playbook before sales pressure hits, so you control scope, evidence, and audit timing instead of reacting under stress.** If you're pursuing **[soc 2 compliance for saas](https://www.cobalt.io/learning-center/soc-2-compliance-for-saas)**, treat this guide as a system, not a policy exercise. As the CEO of a business-of-one, you need a SOC 2 plan that protects your calendar as much as your customers. Use it to decide what to implement first, keep the right proof, and connect the work to clearer security controls, cleaner buyer conversations, and fewer fire drills.