
Start with the independent report: a SOC 2 report shows how a service auditor evaluated controls against the Trust Services Criteria. For vendor decisions, confirm whether it is Type I or Type II, check the auditor opinion, and review listed exceptions before approving use. If key controls are carved out through subservice organizations, request additional evidence and document your follow-up.
You are still accountable for third-party risk, so reviewing a SOC 2 report should be treated as an operating control, not a paperwork task.
A SOC 2 examination is an independent service auditor's report on a service organization's controls against the Trust Services Criteria. Use it to validate vendor claims with assurance evidence, not marketing language.
First, confirm that you have the independent report. Then identify the report type. Type 1 is as of a point in time, while Type 2 covers a specified period and helps you judge whether controls operated effectively over time.
| Vendor promise | SOC 2 evidence to verify | Your decision/action |
|---|---|---|
| "We take security seriously." | Independent service auditor's report and the Trust Services Criteria in scope | Treat the claim as unproven until the report supports it |
| "Our controls work consistently." | Type 2 period coverage and any listed deviations | If deviations are listed, ask for remediation details before relying on the vendor |
| "Our cloud partners are covered too." | System description listing subservice organizations and whether they are inclusive or carve-out | If carved out, run a second review of those providers or request separate evidence |
Subservice organizations require extra attention in due diligence. Vendors can depend on third parties such as data-center hosting providers or managed service providers. If the report uses the carve-out method, those third-party controls are excluded from testing in that report, even though your vendor relies on them. Accountability for third-party risk does not transfer away from you.
Keep your first-pass checklist simple: the system description, report type and period, listed deviations, and subservice treatment. Once you have that, you can judge what was tested, what was excluded, and where the real trust risk sits.
Start with scope, not assumptions. In SOC 2, Security is always in scope, while Availability, Processing Integrity, Confidentiality, and Privacy are included only if the service organization chose them. Map each criterion to how you use the vendor. If a criterion you rely on is missing, treat that as an uncovered risk area.
SOC 2 is principle-based, so you are not checking a single universal control list. You are checking whether the scoped criteria match your real use case and whether the auditor reviewed documentation and operating evidence over time.
| Criterion | What it covers | Risk if weak | Scope signal |
|---|---|---|---|
| Security | Baseline control environment for system and data protection (mandatory) | Unauthorized access, weak risk follow-through, inconsistent response when issues happen | Required in every SOC 2 report |
| Availability | Whether service availability was part of the examined scope | Work disruption when the tool is unavailable | Prioritize when uptime is critical to your operations |
| Processing Integrity | Whether processing reliability was part of the examined scope | Errors or unreliable outputs in workflows that depend on the tool | Prioritize when your workflows depend on the service's processing outputs |
| Confidentiality | Whether protection of restricted information was part of the examined scope | Exposure of sensitive business information | Prioritize when restricted business information is part of your workflow |
| Privacy | Whether personal-data handling was part of the examined scope | Limited assurance on personal-data handling if not included | Prioritize when personal data is part of your use case |
Security: Treat this as your baseline trust check because it is mandatory. Review whether the report shows periodic risk assessment, monitoring to keep controls effective over time, and access limits for both digital and physical environments. Also check system-operations coverage such as incident response and disaster recovery. The Common Criteria (CC-series) are the core structure here, and the list includes nine subcategories.
| Criterion | Use this when | Extra check |
|---|---|---|
| Security | Treat this as your baseline trust check because it is mandatory | Review periodic risk assessment, monitoring, access limits, and system-operations coverage such as incident response and disaster recovery |
| Availability | This vendor sits in your critical path | Confirm that Availability is actually in scope |
| Processing Integrity | Your work depends on the tool's processing | Confirm it is in scope before assuming the service's outputs were examined for reliability |
| Confidentiality | Restricted business information is part of your workflow | Confirm it is in scope and check how the report describes the protected information and related controls |
| Privacy | The service handles personal data | If personal data is part of your use case and Privacy is out of scope, treat that as a separate assurance gap |
Availability: If this vendor sits in your critical path, confirm that Availability is actually in scope. If it is not, the report may still support Security, but it does not give the same assurance on service dependability.
Processing Integrity: Confirm it is in scope before assuming the service's outputs were examined for reliability. If your work depends on the tool's processing, this is a direct risk-control check, not a nice-to-have.
Confidentiality: Use this when restricted business information is part of your workflow. Confirm it is in scope and check how the report describes the protected information and related controls.
Privacy: Use this when the service handles personal data. If personal data is part of your use case and Privacy is out of scope, treat that as a separate assurance gap.
Keep the boundary practical, and confirm how the report scopes each one: teams often use Confidentiality for restricted-information controls and Privacy for personal-data handling controls. You may need both for the same vendor. If only one is in scope, do not assume it fully covers the other.
Related: How to Create a Disaster Recovery Plan for a SaaS Business.
Use the same three-step review every time: confirm scope first, review exception signals second, then run targeted follow-up. That keeps your attention on decision evidence instead of polished language.
A SOC 2 examination is performed by an independent auditor against one or more Trust Services Criteria. Security is always included, while other criteria may be out of scope. Your review should separate "not included" from "included and evaluated."
Start in the auditor section before you read control detail. That is where you confirm whether the document supports the vendor and product you are evaluating.
Find: auditor section, covered service or product, reporting entity, and included criteria. Record: vendor name, report date, covered service, criteria in scope, and scope notes that affect your use case. Decide: proceed, proceed with conditions, escalate, or pause approval.
| What you see in the auditor section | What to record | Decision before moving on |
|---|---|---|
| Scope and covered service clearly match what you use | Auditor name, report date, exact covered service/product, included criteria | Proceed |
| Scope is clear, but a criterion you rely on is not in scope | Missing criterion, affected workflow, and current risk | Proceed with conditions |
| Wording is unclear about entity, product, scope, or included criteria | Exact wording and page reference for follow-up | Escalate |
| Only a summary or marketing claim, or an incomplete package | Missing artifact and date requested | Pause vendor approval |
Operator check: make sure the report covers the exact product and entity you buy from, not just a related brand or parent.
If the report includes testing results and listed exceptions, use that detail as a decision signal. Focus there before you accept broad claims about maturity.
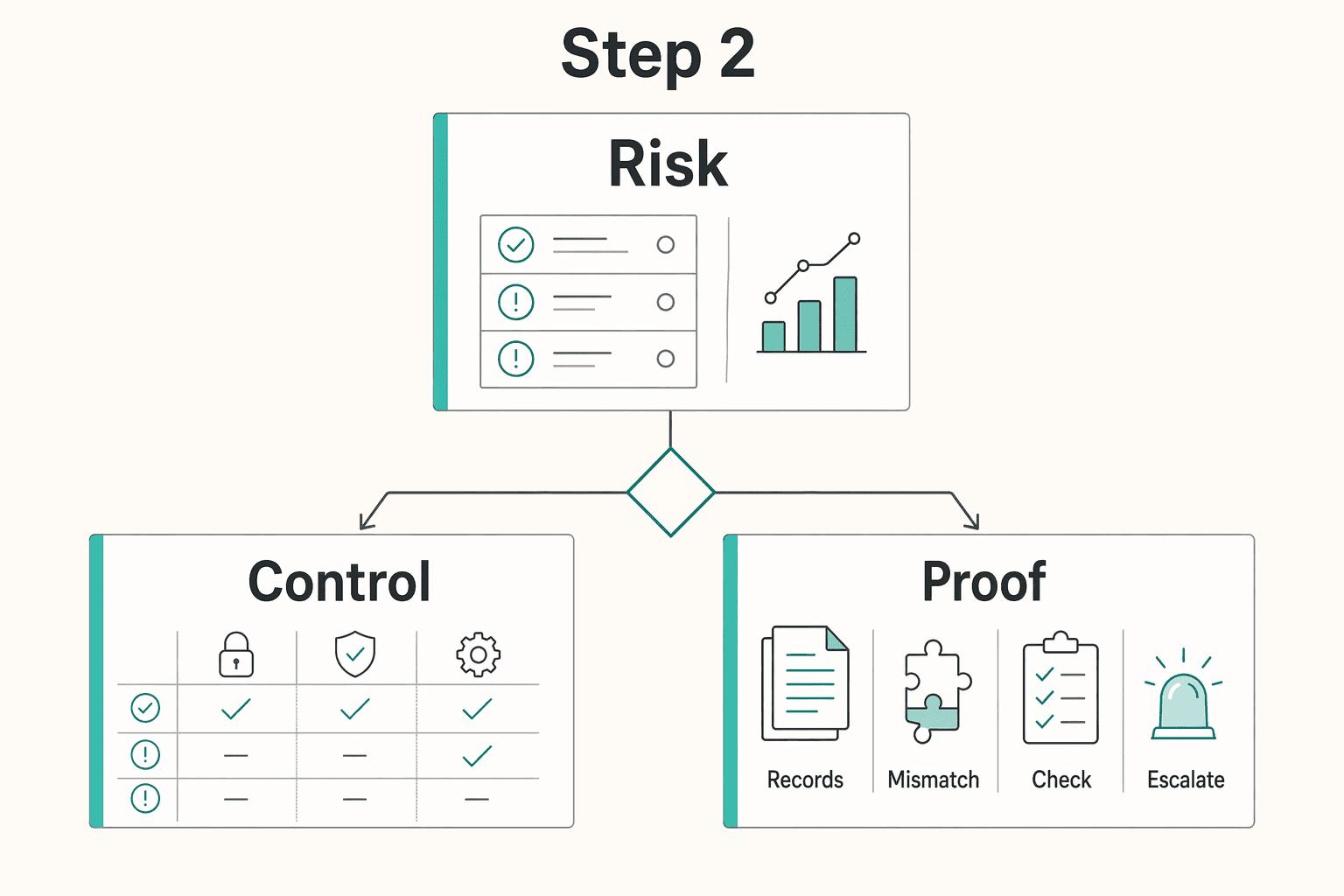
Find: each exception, the control area, and whether it repeats. Record: page, control area, isolated versus recurring pattern, and whether it touches criteria you rely on. Decide: manageable issue or evidence-needed risk before approval.
| Exception pattern | Business impact | Vendor evidence to request |
|---|---|---|
| One isolated exception in a non-critical area for your use case | Limited immediate exposure, but closure still matters | Cause summary, correction date, and confirmation the control is now operating |
| Repeated exceptions in the same control family | Control may not be operating consistently | Remediation summary, retesting proof, and affected period/scope |
| Exceptions tied to access, change activity, monitoring, or service reliability for the product you use | Higher chance of broader weakness affecting your data or operations | Impact scope, compensating controls, and closure evidence |
| Multiple exceptions mapping to the same criterion you depend on | Assurance gap in a workflow you rely on | Customer-impact explanation, remediation status, and next validation point |
Do not score exceptions by count alone. Judge whether the pattern affects the part of the service your business depends on.
Before final approval, run a short follow-up sequence tied directly to the report. The goal is not more paper. It is to learn whether the vendor can explain the issue, show remediation, and close the loop.
| Request | Prompt | Key output |
|---|---|---|
| Context request | For [covered service], explain the exception in [control area] at [page/reference], including what happened and which customer-facing process was affected. | What happened and which customer-facing process was affected |
| Remediation proof request | Share evidence the issue was corrected, such as [updated control description], [retest result], or another verification artifact. | Evidence the issue was corrected |
| Owner and timeline request | Who owns this remediation, and what was the completion date or planned completion date for [issue]? | Owner and completion date or planned completion date |
| Revalidation trigger | Confirm when we should re-check this item: [next report issuance], [stated remediation date], or when [verification artifact] is available. | Next report issuance, stated remediation date, or when a verification artifact is available |
The quality of the response is part of the risk review. Apply the same template across critical vendors so procurement, renewal, and client-trust decisions stay consistent.
You might also find this useful: How to Prepare for a SOC 2 Audit.
Use this framework as your live vendor review checklist, then standardize how you log findings and follow-ups in your operating docs. Browse implementation patterns in Gruv Docs
If you do not maintain your own SOC 2 report, you still need a procurement-ready answer backed by evidence. Enterprise clients may be testing data-handling maturity, not just asking for a document.
This approach fits best when you primarily deliver professional services and rely on third-party tools for storage, communication, invoicing, and delivery. In SOC language, those tools are subservice organizations, and your client may still hold you accountable across that full toolchain.
It may not be enough when procurement treats you as an in-scope service organization and asks for formal assurance, including assurance about your own controls. If that happens, ask early whether they allow an exception path, alternate evidence, or NDA-gated materials. If their policy explicitly requires your own attestation, confirm that immediately so the deal does not stall late.
Do not lead with "SOC 2 does not apply to me." Give them a short security posture statement they can actually review. Include:
| Component | What to include |
|---|---|
| Service model | What you do, what you host yourself, if anything, and whether you operate mainly as a professional service |
| Data-flow summary | What client data you receive, where it enters, where it is stored, who can access it, and how it is deleted or exits your workflow |
| Subservice organization list | Each critical tool, what it does, and the exact covered service you use |
| Control ownership model | Which controls you own directly versus which controls are handled by vendors |
| Incident and continuity commitments | Primary contact, escalation path, and continuity expectations if a critical tool is unavailable |
For each critical vendor, track the covered service, report date, included Trust Services Criteria, and opinion type. If a report shows an adverse opinion, readers should not rely on the scoped system. If it shows a disclaimer of opinion, there is no opinion to rely on.
| Client request | What you can provide now | What it demonstrates | Follow-up artifact if requested |
|---|---|---|---|
| "Send your SOC 2 report" | Security posture statement plus clear service-model scope | You are transparent about what assurance you do and do not hold | Procurement exception request or written confirmation of acceptable alternate evidence |
| "List all subprocessors" | Tool list with each tool's function and covered service | You can account for where data is processed | Vendor assurance materials shared under NDA |
| "Explain how our data is handled" | One-page data-flow summary | You can trace intake, storage, access, and deletion paths | Contract exhibit, architecture note, or redacted process diagram |
| "Show security and continuity commitments" | Named contact, escalation route, and continuity commitments | You have defined ownership and response process | Incident-response summary or continuity documentation |
"We do not currently maintain our own SOC 2 attestation. Our work is delivered through identified subservice organizations. We can share a security posture statement covering our service model, data flow, subservice organizations, control ownership, and incident and continuity commitments. For critical vendors, we can provide supporting assurance materials under NDA and route follow-up through a named operations or security contact. If your policy requires our own SOC 2 report specifically, please confirm that now so we can review an exception path or decide whether the engagement can proceed."
The advantage is not becoming an auditor. It is running a repeatable vendor-review process every time. When a provider says they have SOC 2, confirm the report type, read the auditor opinion, review any exceptions or deficiencies, and document what the vendor has remediated or still needs to address.
That is what protects client trust in practice. SOC 2 is an auditor's opinion on controls related to the five Trust Services Criteria, not a certificate to file away. Type I covers control design at a point in time, while Type II often gives a stronger basis because it evaluates how controls operated over a multi-month period. If you only get a badge, summary page, or "certified" language, treat it as incomplete until you review the independent auditor-issued report.
The highest-value part of your review is usually the findings and your follow-up record. Exceptions do not automatically make a vendor unsafe, and the goal is improvement, not perfection. The real risk is repeated issues or vague remediation answers you never close out. Keep your notes with the report date, scope, and decision rationale so you can explain why you approved, limited, or rejected the tool.
That is the competitive advantage: consistent operating discipline that stands up to client scrutiny. For continued execution, read A Guide to SOC 2 Compliance for SaaS Companies. Then continue with the disaster recovery planning resource to keep vendor risk review and resilience planning aligned.
The provided excerpts do not contain dependable definitions for this difference. Next step: mark this as unresolved and review primary SOC documentation before making a decision.
The provided excerpts do not confirm whether "certification" is accurate terminology. Next step: treat the term as unverified until you can inspect the underlying document directly.
The provided excerpts do not provide a dependable comparison between these labels. Next step: keep the review open until you have primary documentation that supports your decision criteria.
A career software developer and AI consultant, Kenji writes about the cutting edge of technology for freelancers. He explores new tools, in-demand skills, and the future of independent work in tech.
Priya is an attorney specializing in international contract law for independent contractors. She ensures that the legal advice provided is accurate, actionable, and up-to-date with current regulations.
Educational content only. Not legal, tax, or financial advice.

Low-stress compliance in Germany comes from decision order, not tax tricks. Use this sequence: confirm core facts, apply conservative temporary assumptions, verify the few points that can break invoices or filings, and keep one evidence file that explains each decision.

**Build your SOC 2 playbook before sales pressure hits, so you control scope, evidence, and audit timing instead of reacting under stress.** If you're pursuing **[soc 2 compliance for saas](https://www.cobalt.io/learning-center/soc-2-compliance-for-saas)**, treat this guide as a system, not a policy exercise. As the CEO of a business-of-one, you need a SOC 2 plan that protects your calendar as much as your customers. Use it to decide what to implement first, keep the right proof, and connect the work to clearer security controls, cleaner buyer conversations, and fewer fire drills.

A usable **disaster recovery plan for saas** starts with one plain fact: your provider is responsible for restoring its service, and you are responsible for keeping your business running when that service is unavailable. For a business of one, that is not abstract. If a key app is down for hours or days, you need to know what stops, what can wait, and what you can do by hand.