
Build a defensible moat for saas by combining four operating layers: referral quality, embedded workflow ownership, inspectable proof, and procurement readiness. Use CRM source tags and referral handoff assets to improve lead fit, then maintain shared records like KPI dashboards and decision logs so your work is harder to replace. Support reputation with use-case evidence and testimonials tied to outcomes and execution quality. Keep contract and billing hygiene current with a maintained MSA/SOW stack and consistent entity details.
If you want a defensible moat for SaaS, start by treating your solo practice like an asset, not a job. That shift changes what you sell, how you deliver it, how clients experience the work, and where risk shows up.
In this framing, a freelancer is usually hired for effort, while a business-of-one is chosen for a repeatable outcome. That does not mean acting bigger than you are. It means being deliberate about who you serve, when they are ready to buy, and how you grow without losing control.
If you cannot answer those three points clearly, do not add more services yet. A common SaaS failure mode is weak retention: if customers do not stay past month six, new customer acquisition does not fix the underlying model.
| Decision area | Freelancer mindset | Business-of-One operating model |
|---|---|---|
| Value proposition | "I do skilled work for clients" | "I solve a specific problem for a defined buyer" |
| Pricing logic | Mostly tied to hours or output volume | Tied to scope, risk removed, and repeatable business value |
| Process ownership | Client often drives intake, priorities, and handoffs | You own intake criteria, delivery steps, and decision points |
| Moat potential | Low, because replacement is easy to imagine | Potentially higher, because your method and embedded operating logic are harder to copy |
In practice, the shift is less glamorous than the label suggests. Your offer gets narrower and clearer. Delivery stops depending on memory and improvisation. The client relationship moves from "tell me what you need" to "here is how we work when the problem looks like this." Risk management gets sharper too. You define red flags, dependencies, and what you will not take on.
The least defensible layer can be the visible one. In SaaS, that can be the interface. In a solo business, it is your website, proposal, or polished deck. The harder-to-copy layer is what happens underneath: how you collect inputs, clean and interpret them, rank priorities, and trigger action without constant manual chasing.
That is the part worth documenting. A simple checkpoint is to map your delivery path on one page: inputs, review steps, decision rules, trigger points, and client handoffs. If you cannot describe that clearly, your service is probably still too dependent on you reacting in real time.
Before you move into referrals, integration, brand, or compliance, check the foundation against three things.
| Checkpoint | Question | If not |
|---|---|---|
| Expertise | Can you name one buyer, one problem, and one readiness signal? | Your positioning is still too broad |
| Process | Can you show how work moves from intake to result, including what you collect, what you standardize, what you rank, and what happens automatically or by rule? | Your delivery is still a craft, not an operating asset |
| Growth control | Can you explain how you will fund growth without losing control as demand increases? | Scale pressure can outrun your operating structure |
Use the table as a hard gate, not a thought exercise. If your answer to expertise needs a paragraph, your positioning is still too broad. If you cannot show how work moves from intake to result, your delivery is still a craft, not an operating asset. If you cannot explain how growth gets funded without losing control, demand can outrun your structure.
This shift will not make your business invulnerable. It does give you a clearer base to build from, so you are not selling availability alone. If you want a deeper dive, read Digital Nomad Health Insurance: A Comparison of Top Providers. This also pairs well with our guide on ABM for SaaS When Your Team Is Lean.
Once your offer and delivery path are clear, the next moat is who brings you into the room. Referral-led demand matters because trust and context are transferred before you have to sell, which helps when visible capabilities are easier to copy and content volume is now closer to baseline than differentiation.
AI has weakened parts of older moat logic, but that does not make relationships optional. It makes relationship quality more important. A strong introduction will not fix a weak offer, but it can move you into serious consideration faster than cold outreach.
| Channel | Lead quality | Sales cycle friction | Trust transfer | Effort sustainability |
|---|---|---|---|---|
| Cold outreach | Mixed until fit is proven | Higher, because credibility starts at zero | Low | Hard to sustain if you are the only seller |
| Referral engine | Context-rich when the intro is relevant | Lower, because trust exists before first contact | High | More sustainable when relationships are maintained |
Good referrals come from clarity, not goodwill alone. People refer well when they know exactly who you help, what problem you solve, and what a useful introduction looks like.
Start with a short referral partner profile in your CRM or notes: who they serve, what they do, overlap risk, who they know, what problems they hear first, and what a good intro looks like. If every partner is just "someone with a network," you usually get vague intros and low-fit calls.
| Sequence | Trigger | Action | Follow-up |
|---|---|---|---|
| Give-first | You see a useful resource, introduction, or opportunity that fits a partner's work | Send it with a specific note on why it fits their audience or client | Log the touchpoint and follow up when context makes sense |
| Niche community visibility | A focused community you are already in raises a problem you solve repeatedly | Answer publicly with concrete guidance, including what inputs matter and where execution usually breaks | Save strong responses, note who engaged, and move relevant contacts into your CRM |
| Relationship farming | A past client hits a milestone, launches, hires, or has gone quiet long enough to lose momentum | Send a short, useful check-in tied to their current context | Update likely next needs and whether they are a repeat-work source, intro source, or both |
Execution notes:
Give-first: quality check is motive clarity. If every touchpoint hides an ask, trust drops.Niche community visibility: risk is generic posting. Keep and reuse only answers that earned replies or follow-up questions.Relationship farming: red flag is only reaching out when pipeline is thin. Keep contact continuous, not transactional.Make handoffs easy enough that a referrer does not need to explain you from scratch. Two assets do most of the work: an Ideal referral brief (buyer type, problem, readiness signals, exclusions, best first step) and a Handoff message template someone can paste in two minutes. If you want a broader partner model beyond one-to-one intros, read Channel Sales for SaaS Without Losing Control.
If you want a referral engine you can improve, track where trust came from with four consistent tags.
| Tag | What to capture | Example |
|---|---|---|
| Source | How the lead entered your pipeline | referral, direct search, community, repeat client |
| Relationship owner | The person connected to the lead | Named partner, client sponsor, founder, or advisor |
| Stage | Current deal state | introduced, replied, qualified, proposal, won/lost |
| Fit | Match quality | strong, maybe, poor |
This is the key checkpoint: can you trace a real opportunity back to the person or place that created it? If not, you cannot tell whether your moat is strengthening or just producing noise.
You do not need industry benchmarks to run this well. You do need your own baseline and a regular review cycle.
Ideal referral brief and save a Handoff message template.Interpretation:
For a related angle, see Network Effects for Community-Based Products as a Professional Moat. For search-side support, see Link Building for SaaS Companies: Build a Defensible Backlink Asset.
A defensible integration moat means becoming part of the client's real workflow and shared record, not creating confusing lock-in. You are harder to replace when your work improves continuity, decision speed, and handoff reliability.
That matters more now because UX-only or convenience-led tools can be matched quickly, and some buyers can substitute point solutions with cheaper AI or internal builds. The stronger position is the one closest to a system-of-record role, where switching is operationally severe, not cosmetic.
| Area | Commodity vendor behavior | Embedded partner behavior |
|---|---|---|
| Workflow depth | Delivers tasks around the edges | Supports a defined, recurring workflow inside daily operations |
| Data and context | Context is scattered across chats and inboxes | Decisions, changes, and rationale are captured in a shared record |
| Replacement friction | Another tool/provider can replicate visible output fast | Replacement requires rebuilding workflow continuity, not just output |
Embed by improving continuity, not dependence: build a performance dashboard, a knowledge vault, and one reliable core process.
| Method | Client value | Practical test |
|---|---|---|
| Performance dashboard | Less status chasing and faster decisions | The client can interpret progress before your call |
| Knowledge vault | Less relearning when priorities or people change | A new stakeholder can find rationale and current state without your help |
| One core process | Fewer delays/errors in a high-impact handoff | Work still moves when you are unavailable |
Use this continuity check:
Treat this as resilience planning: step away briefly and see whether the client can still find the numbers, context, and next action.
We covered this in detail in A Guide to International Expansion for SaaS Businesses. You might also find The Protégé Effect for Freelancers: Teach Your Method to Build a Defensible Business useful.
For a defensible moat for SaaS, reputation works only when buyers can inspect it. It becomes harder to replace when your credibility is specific, verifiable, and mapped to a buyer's exact use case, not just polished messaging.
| Routine | Inputs | Cadence | Checkpoint |
|---|---|---|---|
| ICP-aligned positioning statement | ICP, core problem, delivery context | Revise only when the buyer, problem, or offer changes | Ask one current client to paraphrase your statement without prompts, then note where they generalize it |
| Evidence stack by use case | Case notes, deliverables, before-and-after artifacts, outcome notes | One asset update monthly or one case refresh quarterly | Every claim has attached proof or a visible pending-verification label |
| Testimonials | Client quote, engagement context, implementation notes | Ask at closeout or at a clear milestone | If a testimonial praises you personally but says nothing about result or execution quality, request a rewrite |
As AI narrows execution differences, generic claims are easier to copy and harder to trust. In that environment, vertical and segment expertise is a stronger credibility signal than broad authority language.
| Decision factor | Generalist positioning | Specialist authority |
|---|---|---|
| Trust transfer | Buyer has to infer fit from broad claims | Buyer can map your proof directly to their use case |
| Sales friction | More explanation and more context-check calls | Less education because niche depth answers objections earlier |
| Premium pricing | Hard to justify beyond availability | Easier to justify when expertise is tied to outcomes and implementation quality |
Your positioning statement should let the right buyer self-select in one pass: who you help, which problem you solve, and in what operating context. If a current client reads your homepage hero or LinkedIn headline and repeats it too broadly, your market signal is still weak.
Operating routine
A stronger evidence stack beats a louder claim. Use the same proof framework for every case: claim, artifact, outcome, buyer relevance, verification status. Each case should show the client context, what changed, what you produced, why it matters to a similar buyer, and whether the metric has been verified from source records or is still pending verification before use.
If your proof says only "improved operations" or "faster reporting," rewrite it until a buyer can inspect something concrete. Attach a dashboard screenshot, process artifact, named deliverable, or before-and-after operating note. If a number is not verified, do not imply certainty; mark it as pending and publish the rest. For adjacent reputation assets, see Link Building for SaaS Companies: Build a Defensible Backlink Asset. For compliance-led trust signals, see The 'Compliance Moat': Why RegTech is a Defensible Strategy.
Operating routine
A strong testimonial should reduce two doubts at once: whether you can produce the result and whether you are reliable to work with while doing it. Ask for both. Useful testimonials state the starting problem, why the client chose you, what changed, and what execution looked like in practice.
Operating routine
Use this credibility-risk check before publishing:
That discipline helps buyers trust what they can inspect, not just what they are told. It also pairs well with A Guide to Revenue Operations (RevOps) for Scaling SaaS Companies. For a step-by-step walkthrough, see A Guide to Continuous Integration and Continuous Deployment (CI/CD) for SaaS.
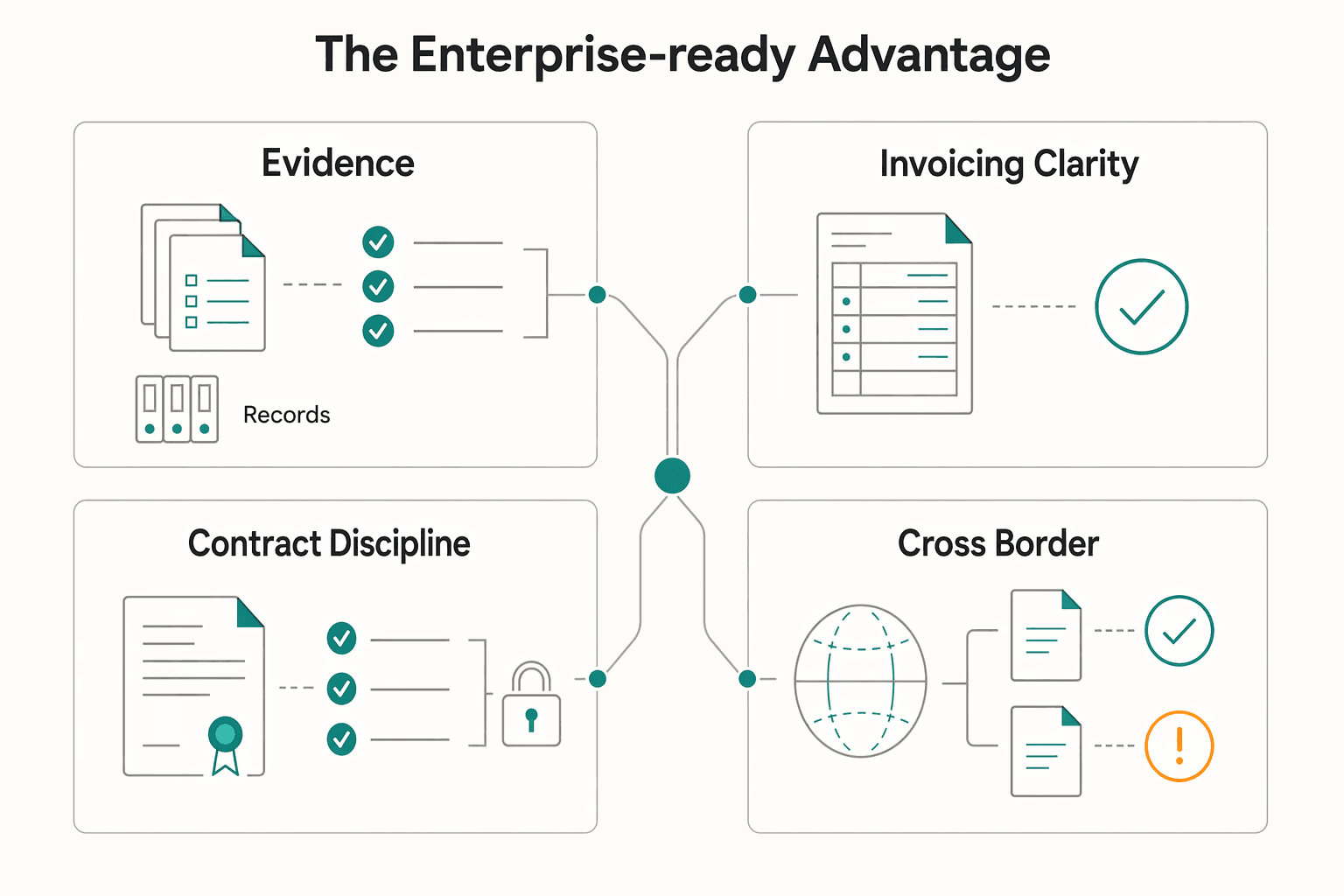
Compliance can be a defensibility moat when it reduces procurement friction, but it is not a guarantee of approval. Once your proof is credible, buyers usually shift from "Can you do this?" to "Can you pass review without extra back-and-forth?" Your edge here is operational hygiene, contract readiness, and clear buyer-confidence messaging.
That matters because thin execution advantages are easier to copy, while compliance infrastructure is often treated as a more durable moat category. For a solo operator, disciplined operations can be as defensible as visible capability.
| Area | Friction signal | Enterprise-ready signal you can maintain |
|---|---|---|
| Documentation quality | Entity details differ across proposal, invoice, and contract | One current source record for legal name, address, billing contact, payment terms, and owner |
| Invoicing clarity | Vague line items and unsupported charges | Invoice template with stable terms, clear descriptions, and backup docs available on request |
| Contract discipline | Work starts from email approval or unsigned PDFs | Current MSA, SOW, and data terms with version date, signing status, storage owner, and escalation owner |
| Cross-border readiness | Tax or payment questions answered ad hoc | Prepared tax packet, with current requirements pending policy or source-record verification |
A small evidence pack is usually enough if it stays current. Quarterly, verify that your proposal template, invoice, contract header, bank instructions, and email signature all match the same entity record. The common failure mode is polished sales material paired with stale billing details or unclear payment instructions.
Contract readiness is mostly governance: one owned storage location, a simple version rule, visible signing status, and clear ownership for updates. If a client redlines privacy, IP ownership, worker classification, or cross-border tax language, escalate to licensed counsel in the relevant jurisdiction instead of improvising.
For adjacent operational readiness, see How to Create a Disaster Recovery Plan for a SaaS Business. For a process lens on ownership and handoffs, see A Guide to Revenue Operations (RevOps) for Scaling SaaS Companies. For the wider strategy angle, read The 'Compliance Moat': Why RegTech is a Defensible Strategy. We covered this in detail in A Guide to SOC 2 Compliance for SaaS Companies.
Your moat is defensible only when each layer is visible as an operating asset a buyer can trust. Treat this as a repeatable cycle: diagnose the weakest layer, fix one asset competitors cannot simply buy, verify it, and iterate.
| Area | Freelancer mode | Fortress mode |
|---|---|---|
| Opportunity | Work arrives through sporadic outreach or luck | You run repeatable referral paths, clear fit signals, and audience trust that consistently improves lead quality |
| Integration | You complete tasks | You maintain documented process, client context, and decision history that buyers rely on and are harder to replace |
| Reputation | You sound broadly useful | You are known for a specific problem, with proof tied to delivered value and clearer pricing power |
| Compliance | Documents are gathered late | Your proposal, invoice, MSA, SOW, and entity details are current before buyer review starts |
Use your next operating review in this order:
If compliance is the bottleneck, The 'Compliance Moat': Why RegTech is a Defensible Strategy is a useful next read. For a practical compliance baseline, see A Guide to SOC 2 Compliance for SaaS Companies.
Start with the moat that most affects buyer confidence in active deals. Pick one correction, verify it, and then move to the next layer so progress is measurable instead of scattered.
Not on their own. AI tools are widely available, so defensibility comes from your expertise, audience trust, proprietary process, and the operating assets buyers depend on.
Keep the same sequence: identify the next weakest layer, apply one concrete fix, and verify it before expanding scope. That discipline is what turns scattered execution into a durable system.
If you want a deeper dive, read A Guide to Singapore's EntrePass for Foreign Entrepreneurs.
Start with the moat that most affects buyer confidence in active deals. Pick one correction, verify it, and then move to the next layer so progress is measurable instead of scattered.
Not on their own. AI tools are widely available, so defensibility comes from your expertise, audience trust, proprietary process, and the operating assets buyers depend on.
Keep the same sequence: identify the next weakest layer, apply one concrete fix, and verify it before expanding scope. That discipline is what turns scattered execution into a durable system. If you want a deeper dive, read A Guide to Singapore's EntrePass for Foreign Entrepreneurs. Want to confirm what's supported for your specific country/program? Talk to Gruv.
A former tech COO turned 'Business-of-One' consultant, Marcus is obsessed with efficiency. He writes about optimizing workflows, leveraging technology, and building resilient systems for solo entrepreneurs.
Includes 7 external sources outside the trusted-domain allowlist.
Educational content only. Not legal, tax, or financial advice.

Use focused time now to avoid expensive mistakes later. Start with a practical `digital nomad health insurance comparison`, then map your route in [Gruv's visa planner](/tools/visa-for-digital-nomads) so we anchor policy checks to your real plan before pricing pages pull you off course.

RegTech becomes a moat only when it makes compliance decisions easier to execute and defend. The buying decision comes down to one question: does this investment create durable capacity, or does it add overhead your team must carry?

Treat the Singapore EntrePass as a work pass decision first, not a paperwork sprint. It is described as a work visa for foreign entrepreneurs, innovators, and experienced investors who want to start and run a business in Singapore, and foreign professionals need a valid work pass before starting work there.