
Mitigate permanent establishment risk by treating it as an operating control issue: keep authority boundaries clear, align daily conduct with the contract, track recurring in-country activity, and escalate when treaty or local-law rules are not verified. Use fixed place, dependent-agent behavior, authority to conclude, and service-activity exposure as screening labels, then keep current records showing how approvals, location, and activity actually work.
Before finalizing execution decisions, validate wording against guidance from irs.gov, ecfr.gov, opm.gov.
| Screening label | Prompt to ask |
|---|---|
| fixed place | how your work location is being presented and used in practice |
| dependent-agent behavior | whether other people are relying on you as the commercial interface |
| authority to conclude | whether you are being asked to make or signal final commitments |
| service-activity exposure | whether recurring in-country work is expanding faster than the review process |
You turn permanent establishment risk into an advantage by treating it as an operating control issue, not a drafting exercise. Keep role boundaries clear, keep records current, and escalate when the legal basis is unclear.
That approach matters because PE problems usually do not appear all at once. They show up as small operating drifts. A client starts routing commercial questions to you because you are responsive. A work location gets described too loosely. Recurring activity becomes normal before anyone checks the rule set. Or a contract says one thing while the day-to-day workflow says another. If you wait until someone asks for a final legal answer, you are usually working backward from a messy fact pattern. If you treat it as a control issue early, you can catch the drift while it is still fixable.
Use fixed place, dependent-agent behavior, authority to conclude, and service-activity exposure as screening labels, not final answers. Once a risk signal appears, verify how it applies under the relevant treaty and local law before you decide what to do next.
The practical point is not to become your own tax advisor. It is to make sure your facts are stable, your records are usable, and your workflow does not create avoidable ambiguity. These labels help you sort what needs a quick correction, what needs a documented review, and what needs outside advice before the pattern hardens.
Used properly:
Those are screening questions, not final legal outcomes. A useful control system keeps that distinction clear. It lets you move quickly on the facts you control, while reserving legal conclusions for the point where you have verified the actual rules that apply.
Start with what is happening in practice, not what the paperwork says. Use this triage first, then decide whether you can contain the issue internally or need legal review.
low-risk = behavior, approvals, and documents are aligned; review-needed = scope, location, or activity patterns are drifting; escalate-to-advisor = authority is shifting to you, or the answer depends on rules you have not verified.
| Risk signal | Immediate containment action | Evidence to retain | Escalation trigger |
|---|---|---|---|
| You are asked to discuss or settle price, scope, or terms with third parties | Pause at decision points and route approvals to the client's authorized team | Email thread, meeting notes, approval map | Repeated requests or you are presented as the decision-maker |
| Your address/work location is being treated like the client's local base | Remove that framing and restate external-provider status | Current SOW, invoices, corrected profile screenshots | The location is used in client-facing or operational positioning |
| In-country activity becomes recurring | Start a dated activity log and verify local thresholds before continuing pattern expansion | Travel/service log, project timeline, review notes | Local threshold may be implicated but is not yet verified |
| Contract says "no authority," but daily conduct says otherwise | Update workflow first, then align SOW and approvals immediately | Redlines, approval emails, revised process note | Client refuses to align behavior and documents |
| A key legal source is login-gated or only available as a title or summary | Do not rely on it until you obtain full text or written advisor support | Download/access record, full material, advisor memo | You still cannot verify the substantive source content |
If your legal support is only a title page or a login wall, treat it as insufficient for a final call. A good diagnostic process is simple enough to run quickly and disciplined enough to stand up later.
Start by pulling the materials that show what is happening now, not what happened when the engagement began. In practice, that usually means the current agreement, the active SOW, the approval route the team is actually using, recent meeting notes, recent email chains on scope or price, any travel or service log you already keep, and any public-facing profile or signature that could describe your role or location. You are not trying to build a legal brief at this stage. You are trying to see whether the facts line up.
Ask a short set of operational questions:
You do not need a perfect internal questionnaire. You need enough structure to catch drift before it becomes your normal operating model.
The most common mistake at this stage is over-weighting contract language and under-weighting behavior. A contract can say no authority, but if people consistently send you to settle commercial points, the behavior is what needs attention first. The reverse is also true. A slightly rough document set is usually fixable if behavior is already controlled and approvals are clearly routed. That is why triage should begin with conduct, then move to documents, then move to legal verification.
If you find mixed signals, classify the issue at the highest risk level that is currently visible. For example, if your title and SOW still look clean but counterparties are already treating you as the decision-maker, this is not low-risk just because the paperwork is better than the behavior. Similarly, if there is no sign of shifting authority but a recurring activity pattern is expanding and no one has checked the relevant rule set, that is at least review-needed until verified.
It also helps to assemble a small evidence pack as you go rather than waiting until someone asks for it. The pack does not need to be elaborate. It just needs to be current and internally consistent. Useful items usually include:
That pack does two jobs. First, it lets you answer client questions without reconstructing history. Second, it makes it easier to spot where one piece of the system has drifted away from the rest.
Treat each row in the table above as a real operating control, not just a warning sign.
When you are asked to discuss or settle price, scope, or terms with third parties, the issue is not necessarily that you joined the conversation. The issue is whether you are becoming the point where commercial uncertainty gets resolved.
Many people slide into that role accidentally because they know the project best, they respond quickly, or the authorized client team is hard to reach. That is where the containment step matters. You do not need to make the interaction awkward. You need to pause when the conversation moves from explanation into commitment and route that decision back to the client's authorized team. If this happens once, document it. If it happens repeatedly, the pattern itself is the signal.
Evidence matters here because memory turns soft very quickly. Keep the email thread, meeting notes, and approval record that show where the decision actually landed. If you verbally redirected the issue during a call, follow up in writing so the record reflects that the commercial decision stayed with the client. Otherwise, everyone may later remember only that you handled the conversation.
When your address or work location is treated like the client's local base, small wording choices can do more damage than people expect. This often starts innocently. Someone lists your location in a profile, directory, pitch deck, or email signature in a way that implies local presence for the client. Or a client starts describing you operationally as their local point in a market when what they really mean is that you happen to work there.
The immediate fix is not theoretical. Remove that framing and restate external-provider status anywhere it appears. Then keep the corrected materials. If the location language is already being used in client-facing or operational positioning, that is no longer just a wording cleanup. It needs escalation.
In-country activity becoming recurring is another area where teams often react too late. The problem is rarely the first activity in isolation. The risk is the pattern that forms when similar activity repeats and no one is logging it carefully enough to review. If the work is starting to look recurring, begin a dated activity log before the pattern expands further. Keep it plain and factual: when the activity happened, where it happened, what the activity was, who requested it, and whether there were approval or decision points involved. You are not drafting legal conclusions in the log. You are preserving facts that can later be checked against the relevant treaty and local law.
This is also where discipline beats confidence. If local thresholds may be implicated but have not been verified, do not rely on casual assumptions. Mark the issue for review before the next expansion in pattern, not after. It is much easier to pause and verify early than to explain later why the team kept scaling an activity without checking the local rule set.
The row about a contract saying no authority while daily conduct says otherwise is often the clearest example of why PE risk is an operating issue. Paper does not cure behavior. If commercial commitments are effectively running through you, fix the workflow first. That means changing who answers, who approves, and how requests are routed in real time. After that, align the SOW and approval materials so the documents catch up to the corrected process. If you reverse that order and update paper first, the team may feel protected while still operating the same way. That is exactly the sort of false comfort that creates later problems.
If the client refuses to align behavior and documents, treat that refusal as its own escalation trigger. At that point the issue is not a minor drafting mismatch. It is a control failure the client is choosing to leave unresolved.
The final row, on login-gated or partial legal sources, seems narrow but matters more than people think. A surprising amount of bad decision-making starts with someone citing a title, a summary, or an inaccessible source as though it settled the issue. If you cannot see the substantive content yourself, or you do not have written advisor support that clearly addresses the point, you do not have a reliable basis for a final call.
The containment action is simple. Do not rely on the source until you obtain the full material or a written advisor memo you can actually review. Keep a record of the access issue as well, so there is a clear reason the matter stayed open.
A workable rule of thumb for diagnostic use is this:
That distinction keeps you from overreacting to every stray signal and from underreacting to repeated operating drift.
The key control point is authority. Your contract helps only when daily conduct matches it.
| Element | Should show |
|---|---|
| Agreement | describes you as an external provider rather than part of the client's local organization |
| SOW | reflects the work you are actually doing now, not the work you were originally expected to do |
| Approval path | shows exactly who handles commercial decisions |
| People involved | know how to redirect requests in the moment |
| Documents, signatures, profiles, and invoices | do not imply a broader local role than the engagement supports |
Keep the boundaries explicit. You should not own final commercial approvals, sign or verbally commit for the client, or act as the client's local representative. When authority requests come in, redirect them in plain language: you support delivery, while commercial approval and signature stay with the client's authorized team.
The reason authority is the main control point is practical. Many engagements can tolerate some document cleanup, some process refinement, or some location clarification without immediately becoming unstable. They become unstable when the market starts treating you as the person who can commit the client. Once that expectation forms, every rushed call, every casual confirmation, and every undocumented handoff becomes harder to explain.
A useful contract firewall does more than include the right sentence. It connects the contract to the actual path a decision follows from request to approval. If you want the contract to work in practice, build the operating steps around it.
That usually means checking whether the following are all aligned:
If even one of those pieces is materially out of line, the contract firewall is weaker than it looks.
The cleanest way to make the boundary real is to design for handoff. Do not wait until a negotiation or scope issue appears and hope you remember to step back. Set a simple operating rule in advance for what happens when a conversation moves into price, scope, terms, or commitment. Decide who receives those questions, who answers them, and how you document the transfer. If the client has an authorized team, make sure the route to that team is obvious and consistently used.
This does not require a formal policy memo to be effective. Often a short written process note is enough if people actually follow it. The note can cover who approves commercial matters, where signature authority sits, when you should pause a discussion, and what kind of change requires the SOW or approval route to be updated. The value comes from use, not length.
In live discussions, the firewall should be visible through behavior. If you are on a call and the other side asks for a decision you do not own, do not blur explanation and approval. You can explain the project context, delivery implications, or operational impact. You should not present the final commercial answer as yours to give. The safest pattern is to make the boundary clear when the issue becomes a commitment question, then follow up with the authorized client team copied into the process.
The same logic applies to written communication. Drafts, redlines, and summaries can all be part of your support role, but the record should show where commercial authority sits. If you circulate language, make sure it is obvious whether it is a draft for review or an approved position from the client. If the workflow hides that distinction, the document trail will not help much later.
Location control belongs inside the contract firewall too. If your work location or address is being used in a way that suggests you are the client's local base, fix the wording and the materials at the same time. It is not enough to change a single profile and leave the same implication in invoices, bios, directories, or operating notes. People rely on small signals when they decide how to treat a relationship. If those signals conflict, the broadest one often wins.
When scope, location, or delivery patterns change, update the SOW, approval route, and activity records right away. If you use an EOR, treat it as an added control layer, not a complete shield.
That timing point matters. A lot of teams treat change management as paperwork that can wait until the project settles down. For this issue, that delay is risky because the new pattern becomes normal before the controls are updated. If the work moves location, becomes more recurring, or starts including activities with more client-facing or commercial sensitivity, the agreement materials and approval process should be reviewed while the change is happening. Do not wait until several cycles of the new arrangement have already passed.
A practical update sequence usually looks like this:
That sequence keeps the legal review anchored to real facts instead of a mix of old paperwork and new behavior.
It also helps to watch for common firewall failures that do not look serious at first:
None of these failures needs dramatic language to be dangerous. Their risk comes from repetition. The more often they happen, the more they redefine your role.
If you use an EOR, the same discipline applies. An EOR can improve structure and documentation, but it does not replace authority boundaries or consistent conduct. If the operating facts still show shifting authority, local positioning, or recurring activity that has not been reviewed under the applicable rules, the existence of an EOR does not answer the core issue. Treat it as one layer in the control stack, not the whole stack.
A strong contract firewall is less about legal phrasing in isolation and more about whether the engagement can survive close factual scrutiny. If someone reviewed your agreement, your SOW, your emails, your meeting notes, your profile, and your activity record together, would they all tell the same story about your role? That is the standard worth aiming for.
After you reset the contract and approval path, make sure the client can see the same control model. Keep the discussion short and operational.
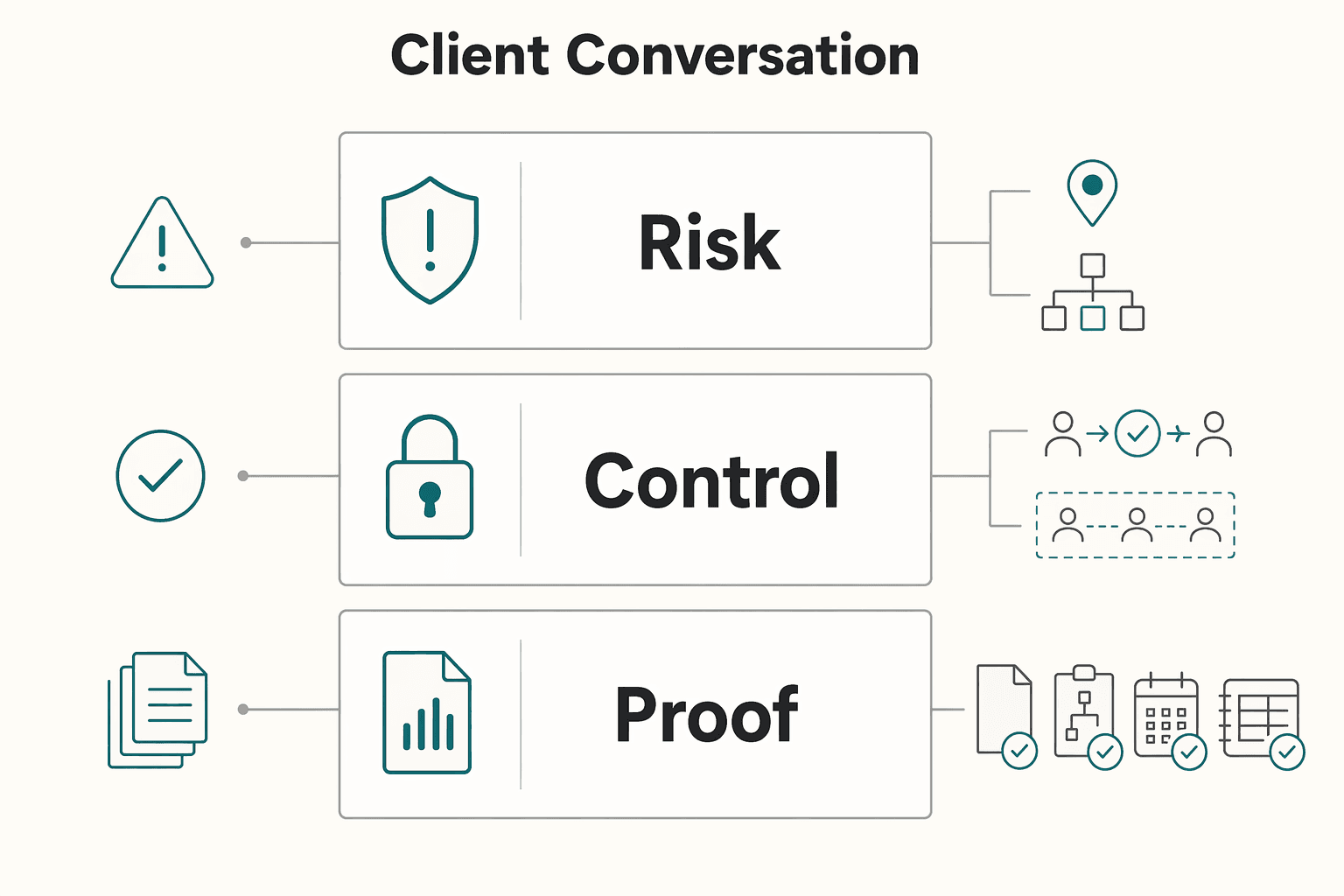
Explain the structure in simple terms: you are an external provider, authorized client staff handle commitments, and material pattern changes trigger treaty and local-law review. Then show evidence instead of theory: the current agreement, SOW, approval path, and dated activity records. That keeps the conversation on controls the client can actually validate.
This conversation usually goes better when you resist the urge to make it sound like a general tax lecture. Most clients do not need a broad explanation of PE concepts from you. They need to understand how the engagement will be run so that responsibilities are clear and avoidable ambiguity is reduced. Keep the discussion tied to who does what, what changed, and what records support the current structure.
A practical flow is:
That is usually enough. Long theoretical discussions often create more confusion than clarity, especially if the client starts treating your explanation as legal advice rather than operational risk management.
It also helps to bring the client back to observable facts. If the issue was authority drift, show the approval map and the corrected routing. If the issue was location framing, show the corrected materials. If the issue was recurring activity, show the dated log and the point at which review is being requested. When the conversation stays tied to records, it is easier for the client to validate the structure and harder for anyone to fall back on vague assumptions.
You do not need to be defensive in this discussion. The tone can be calm and practical. You are not accusing the client of creating risk. You are making the operating model explicit so the team can keep moving without avoidable confusion. That often makes the conversation easier for everyone involved, because most drift starts from convenience rather than intent.
One useful discipline is to avoid leaving the meeting with only a verbal understanding. If the client agrees that commercial approvals stay with authorized staff, that role framing needs to appear in the actual workflow and supporting documents. A concise follow-up email can do a lot of work here. It can confirm the role split, attach or reference the current approval path, note any corrected materials, and record any open point that still needs treaty or local-law review. That way, the discussion produces a usable record rather than just a good meeting.
If the client pushes the conversation into broad hypotheticals, bring it back to the current facts. The question is not every possible PE scenario in the abstract. The question is how this engagement is being run now, what has changed, and what still needs verification. That focus keeps you within a responsible lane and prevents the conversation from drifting into unsupported conclusions.
No. They are separate analyses and should be documented separately. Keep one file for personal residency records and conclusions, and a separate file for the engagement's PE facts, controls, and review notes, with dated updates and open questions clearly marked.
No. Profit attribution is jurisdiction-specific and should be reviewed under the applicable rules before anyone estimates impact. Until that review happens, document the fact pattern, note what has and has not been verified, and avoid broad statements based on headlines, summaries, or incomplete legal sources.
No. An EOR can improve structure and documentation, but it does not replace authority boundaries or consistent conduct. If authority blurs, location framing drifts, or recurring activity expands without review, the EOR does not solve those underlying facts by itself. You still need a current SOW, approval path, activity records, corrected role descriptions, and escalation when treaty or local-law analysis has not been verified.
Tomás breaks down Portugal-specific workflows for global professionals—what to do first, what to avoid, and how to keep your move compliant without losing momentum.
With a Ph.D. in Economics and over 15 years of experience in cross-border tax advisory, Alistair specializes in demystifying cross-border tax law for independent professionals. He focuses on risk mitigation and long-term financial planning.
Educational content only. Not legal, tax, or financial advice.

With digital nomad taxes, the first move is not optimization. It is figuring out where you may be taxable, where filings may be required, and what proof supports that position.

Your **freelance financial safety net** is more than a savings balance. It is the set of controls that lets you cover fixed obligations on time when receipts are uneven, and it keeps invoiced revenue separate from cash you can actually spend. The goal is not to predict every slow month. The goal is to reduce the chance that one late client payment turns into missed bills, tax pressure, or borrowing.

Your client’s concern can be straightforward: the contract says one thing, but the day-to-day record may start showing another. In permanent establishment risk germany, that mismatch can make a file harder to assess quickly and escalate for advice.