
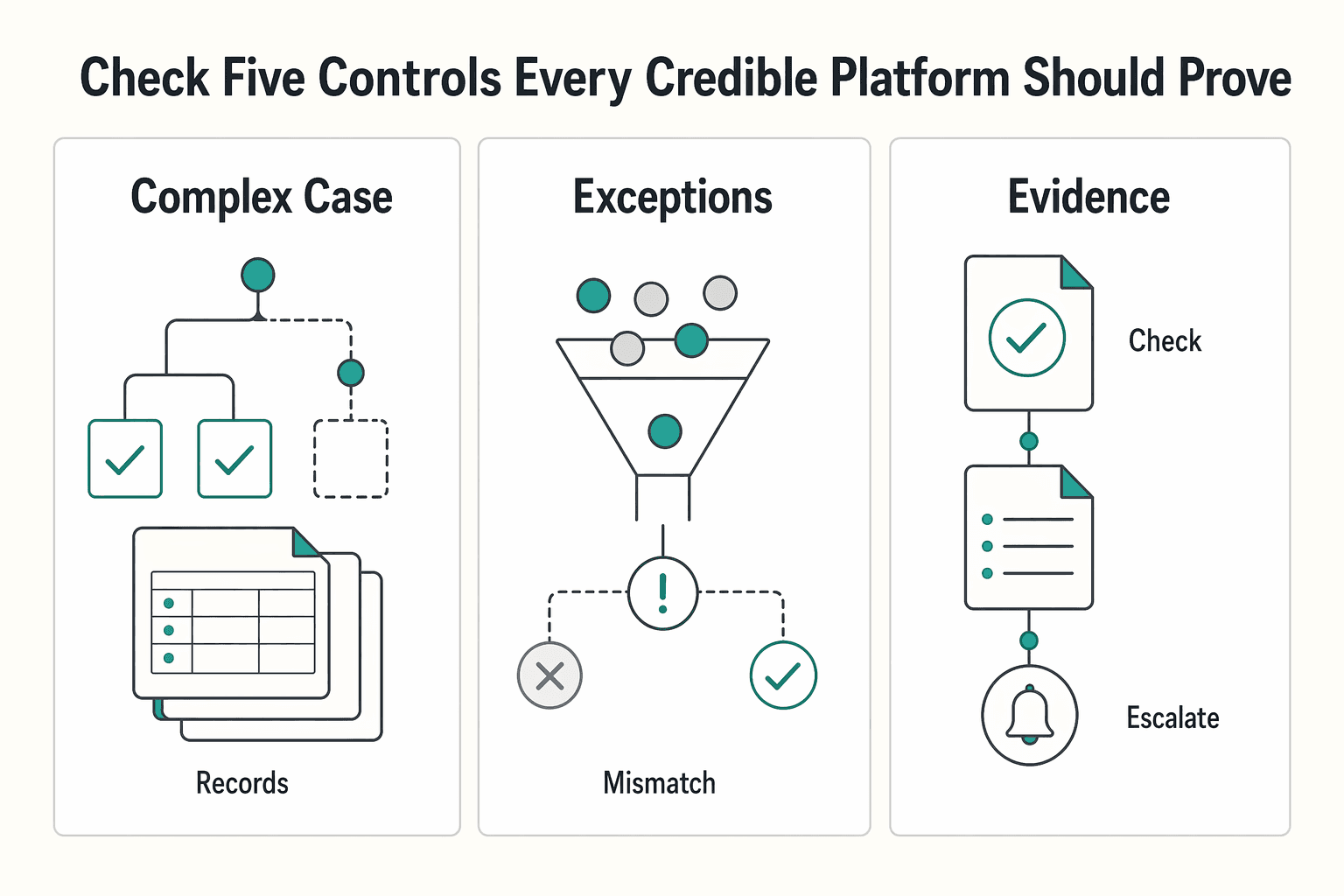
Use a 30-minute due diligence check to select a compliance-first fintech platform: prove five controls in live behavior before you commit. Confirm KYC onboarding, AML monitoring, audit-trail depth, code-level control enforcement, and fee-disclosure consistency, then run one failure-path test and one cross-border scenario with the vendor team. If any critical control cannot be demonstrated with retrievable records, mark it unproven and pause procurement.
Use this as a buyer guide, not a vendor-pitch decoder. Compliance-first fintech means compliance controls are built into product architecture from day one, not added after launch. If a platform cannot show where KYC checks, AML monitoring, and transaction controls happen in the product flow, treat that as added risk. In practice, that means live behavior, not policy documents: how users are verified, how access is controlled, how suspicious activity is handled, and how actions are logged when money moves.
A simple checkpoint is whether the vendor can prove the software enforces limits and logs actions. Ask them to show where a user is stopped, reviewed, approved, held, or escalated. If you only hear broad claims like "we monitor everything," you still have not verified that the product is doing the work.
This article looks at platform trust and operational risk in payout workflows. The key question is not which tool looks smoothest. It is which one can clearly explain what happens before a payout is sent, when activity is flagged, and how status history is preserved.
This matters even for smaller teams. A common failure mode is launching without real compliance staffing, then trying to add controls later while still shipping and expanding. Another is prioritizing low-friction UX over compliance safeguards. If onboarding is "very light" and verification steps are unclear, treat that as a warning.
A useful early test is a short walkthrough of one gated action. Ask to see where KYC is triggered, then ask for a masked action log tied to a payout status change. You are checking whether controls are visible, product-level, and traceable.
By the end, you should have:
If you keep one rule from this section, keep this: when money moves, trust demonstrable control points over polished compliance messaging.
The line is practical. Compliance-first puts control gates inside day-to-day transaction handling, while compliance-later relies on cleanup after issues surface. If customer due diligence or monitoring checks exist in policy language but do not clearly change onboarding, payout decisions, or escalation flow, that is reactive risk management.
Built-in control means compliance requirements are part of normal operations, not a separate after-the-fact function. You should be able to see first-line ownership in both product behavior and team practice: who owns an action, what procedure applies, and where escalation goes.
Ask for evidence, not labels. A useful demo is one masked path from onboarding to payout review that shows where checks were completed, where monitoring changed the path, and how status history records key decisions and escalations. If that trail is missing, controls may not be embedded in day-to-day operations.
Feature names are not proof of control design. Labels like "monitoring" only matter when they change transaction handling and leave a usable record for review.
Baseline compliance can still be too generic for your actual risk profile. When first-line ownership is weak, gaps can sit undetected for a long time, and teams can drift into complaint-driven or incident-driven cleanup instead of prevention.
The fastest way to separate embedded controls from cleanup later is to run a short live check:
If they can describe policy but cannot show control points in the transaction lifecycle, you are looking at compliance-later behavior.
Before you compare pricing or product polish, verify the controls that matter most. If a vendor cannot show these in live system behavior, treat the control as unverified.
| Control to verify | What they should show you live | Evidence to ask for |
|---|---|---|
| KYC onboarding | One masked onboarding path where identity verification changes what happens next | Onboarding status history, review states, and one masked case record |
| AML monitoring | A transaction path where monitoring can flag suspicious activity and change handling | Masked alert/case record, escalation notes, and tied action logs |
| Audit trail depth | A timestamped record of who did what and when across onboarding and transaction handling | Action logs, decision records, status changes, and case comments |
| Code-level control enforcement | A live example showing limits enforced by code and the resulting system behavior | Control/rule settings, execution logs, and one exception example |
| Fee-disclosure consistency | Standardized disclosure language across digital interfaces, contracts, and customer communications | Current disclosure samples, change log, and latest review record |
The core check is operational proof, not policy language. Regulators increasingly examine how systems behave in real time. Ask whether the platform can show that controls are enforced in code, limits are applied, and actions are logged.
For KYC and AML, ask for one complete masked path from onboarding through transaction handling. You should see where checks can change the path, what state is assigned, and what record remains after review.
For transaction workflows, use one practical buyer rule: require clear AML decision points and an auditable status history before you sign. If they cannot produce a masked alert or case record tied to a transaction decision, "monitoring" is still just a claim.
For audit trails and reporting records, ask one exception-first question: "Show me a real flagged transaction and the full record behind it." If that record is incomplete, the risk is being deferred rather than controlled. For a related read, see A Guide to Singapore's EntrePass for Foreign Entrepreneurs.
Once you verify the five controls, make the structural choice first. In this grounding set, model-level speed/control comparisons are not established, so treat them as due-diligence questions.
| Model | What you usually get first | Main tradeoff | Dependency risk to watch | Where burden tends to show up |
|---|---|---|---|---|
| All in one stack | Not established in this grounding set; verify actual onboarding, payments, and reporting scope | Not established here; review contract limits and change process | Check export access, workflow flexibility, and turnaround for change requests | Confirm permissions and record visibility in live operations |
| Modular stack | Not established in this grounding set; verify each provider role and handoff | Not established here; map integration and ownership boundaries | Check whether IDs, statuses, and timestamps stay consistent across tools | Confirm who reconciles cross-system records end to end |
| Merchant of Record (MoR) | Not established in this grounding set; verify supported program scope | Not established here; review control and exception visibility | Check contract scope, out-of-scope paths, and escalation handling | Confirm what evidence you can retrieve when issues arise |
Treat this table as a starting hypothesis, not a guaranteed outcome. Coverage, responsibilities, and record access vary by market, program, and contract terms.
A platform choice may not remove all obligations. It can change where operational work sits and how easily you can retrieve evidence when a payment is held, returned, or reviewed.
Use regulator references as a proof checkpoint, not a trust signal. If a vendor references FCA, FinCEN, NYDFS, or MAS, ask which market or program that applies to and which records you can actually access. In this grounding set, only FinCEN is supported in detail.
FinCEN's FBAR rules are a concrete example of burden that can remain with you. FinCEN states an FBAR must be filed when a single account or aggregate maximum exceeds $10,000. No FBAR is required when the person did not have a $10,000 maximum or aggregate maximum during the year. FinCEN also says maximum value is a reasonable approximation of the greatest value during the year. For non-U.S.-currency accounts, use Treasury's year-end rate, or another verifiable rate with the source documented if Treasury's rate is unavailable. For certain U.S. persons with fewer than 25 accounts that cannot determine aggregate maximum value, FinCEN allows the "amount unknown" indicator (item 15a).
Operationally, ask whether exports let you reconstruct maximum account value. A smooth payout flow is not enough if records are too thin to support your own reporting and audit needs.
FinCEN also signals that filing timelines can change. It states April 15, 2026 remains the due date for other individuals with an FBAR obligation. Certain signature-authority cases for 2025 calendar-year reporting were extended to April 15, 2027 because proposed rulemaking is not finalized. Plan for updates rather than assuming obligations stay fixed.
Two buyer scenarios help here. Different models fit different operating realities.
For a solo freelancer with low volume, prioritize low setup friction without giving up visibility. This grounding set does not establish a default winner among MoR, all-in-one, or modular for that case.
For a small, ops-heavy team with batch payouts and reconciliation, prioritize explicit controls and evidence quality. The best fit depends on contract scope, record access, and how reliably you can trace IDs and status changes across systems.
A practical rule for choosing: validate scope, evidence access, and obligation boundaries before choosing a model. Do not assume one model is always faster or always gives better control.
Choose the model only after you confirm where the burden sits, what evidence you can retrieve, and what still stays with you.
This is where many otherwise solid evaluations fail. "Global coverage" is not proof of usable coverage for your corridors. A single remittance corridor can involve at least two, and often more, legal and regulatory environments, so validate scope before you onboard.
| Checkpoint | What to confirm | If missing |
|---|---|---|
| Country/program matrix | Written matrix naming the jurisdictions and programs you care about, plus known constraints | Expect surprises during onboarding or when activity is already in motion |
| Regulator context | How controls change across contexts such as FinCEN, FCA, and VARA, and where local dependencies affect execution | Producing usable regulatory evidence later can become harder if logs are fragmented |
| Regional hub claims | Which origin and destination pairs are supported, what is restricted, and how restrictions are surfaced | You still need a live walkthrough of a restricted-case path |
| Live scope vs roadmap | What is enabled now versus roadmap, with a named owner and update cadence | Treat unverified coverage as unsupported |
Ask for a written matrix that names the jurisdictions and programs you care about, plus known constraints. It should separate what is live now from what is not, instead of relying on broad "worldwide support" language.
Use it to confirm practical scope, including where KYC/KYB checks apply and where restrictions are already known. If restrictions are not stated up front, expect surprises during onboarding or when activity is already in motion.
You do not need a legal lecture, but you do need an operational answer. Ask how controls change across regulator and market contexts such as FinCEN, FCA, and VARA, and where local dependencies affect execution.
Also ask whether checks run through one orchestration layer with a consistent audit trail, or across multiple providers with fragmented logs. That difference directly affects how hard it is to produce usable regulatory evidence later.
If a vendor uses a regional hub claim, turn it into corridor-level detail: which origin and destination pairs are supported, what is restricted, and how restrictions are surfaced. Then ask for a live walkthrough of a restricted-case path so you can see status visibility and escalation in practice.
Get written confirmation of what is enabled now versus roadmap, with a named owner and update cadence. This is a buyer-protection step, not a legal requirement.
When a vendor will not confirm current scope and known constraints in writing, pause onboarding. The safer default is to treat unverified coverage as unsupported.
Related reading: Good Strategy/Bad Strategy for Freelancers: A 3-Tier System for Compliance, Profit, and Delivery.
A polished happy-path demo tells you little about operating risk. Stress-test exception paths before onboarding, not after your first serious incident. If a vendor cannot explain key exception paths in plain English, treat that as a major risk signal.
Stress testing matters because it forces the product and the team to show how failures are handled under pressure. Smooth demos and confident forecasts can create false confidence.
Ask the team to walk one realistic case for each high-impact exception path relevant to your operations. You are not asking for one universal script. You are checking whether they can clearly show the path from first alert to final resolution, including ownership, visible status, and captured evidence.
| Scenario | What to ask them to show | Red flag |
|---|---|---|
| Failed payout | Trigger, status changes, remediation path (if any), and final outcome | They cannot explain why the failure happened or how it was resolved |
| Compliance hold | Trigger, reviewer workflow, decision inputs, and how decisions are recorded | "Ops reviews it" with no case history |
| Return | How the return links to the original transaction and balance impact | Return appears as a generic failure with no traceable link |
| Reversal or correction | How the correcting entry ties to the original transaction and final end state | Multiple exception types are treated as one vague category |
The real question is whether an incident can be rebuilt later without guesswork. Ask for proof that records and audit logs are complete enough to reconstruct what happened end to end.
Request a demo or masked historical case that shows the event timeline, who made key decisions, and the final resolution. Ask them to trace one case across internal and external records, then show timestamped status history with actor and decision traceability from alert to closure.
If they have standardized evidence exports, that is a strong signal. The SEC-hosted companion submission dated February 17, 2026 frames these as non-normative design patterns. Its evidence-pack approach is still a useful benchmark for operational readiness. A practical evidence set should include:
Before you sign, get incident expectations in writing: who is notified, what artifacts are shared, how updates are communicated, and how manual overrides are governed. This is an operating-model check before you depend on the system.
The OCC Payment Systems handbook (Version 1.0, October 2021) is examiner guidance, and its structure is practical for diligence: policies and procedures, internal controls, and risk assessment. Use those buckets directly, and ask how controls are assessed for institution-specific risk. If override handling depends on "a senior person can sort it out," you are looking at key-person risk, not a controlled process.
For freelancers, tax and document readiness is a go or no-go check. If a platform is clear on payouts but vague on forms, access, and exports, the cleanup burden can land on you at filing time.
Do not accept "we support tax documents" by itself. Ask for a live walkthrough of how tax-form data is collected, who can access it, and what export output your accountant can use.
Use a simple pass/fail test: can they show one example record from collection to retrieval to export and explain access boundaries? If not, plan for documentation risk and manual follow-up later.
Also require plain-language answers on retention, download permissions, and access logging. There is no single universal rule in this grounding set for storage controls, so the key question is whether the boundaries are explicit and usable.
Some tooling can track dates, residency facts, payment timing, and reminders. It does not determine tax eligibility.
| Tax point | Rule | Reminder |
|---|---|---|
| FEIE filing | You still file a U.S. tax return reporting the income | Tooling can track dates, residency facts, payment timing, and reminders; it does not determine tax eligibility |
| Physical presence test | Threshold is 330 full days in any 12 consecutive months | A full day is 24 consecutive hours from midnight to midnight |
| Day-count failure | Missing the day count fails the test | This applies even for reasons like illness, family problems, vacation, or employer orders |
| Bona fide residence test | Requires an uninterrupted period that includes an entire tax year | Living abroad for one year does not automatically make you a bona fide resident |
| 2026 maximum FEIE | $132,900 per person | That number matters only if qualification and filing conditions are met |
For FEIE, the IRS is explicit: you still file a U.S. tax return reporting the income. Under the physical presence test, the threshold is 330 full days in any 12 consecutive months, and a full day is 24 consecutive hours from midnight to midnight. The test is time-based. Missing the day count fails the test even for reasons like illness, family problems, vacation, or employer orders.
The bona fide residence test is also fact-specific, not a checkbox. It requires an uninterrupted period that includes an entire tax year, and living abroad for one year does not automatically make you a bona fide resident.
For 2026, the maximum FEIE is $132,900 per person, but that number matters only if qualification and filing conditions are met. Ask vendors what facts they help track and what remains with you and your advisor.
Confirm reporting boundaries early, before you rely on the platform for anything tax-related. For FBAR, use FinCEN's page to verify current filing timing and extension notices. A platform may help with reminders, account data, or exports, but do not assume it files for you unless they show that clearly.
Apply the same boundary check to any 1099, VAT, and GDPR features a vendor advertises: what they validate, what they store, what they export, and what remains your legal responsibility. If you work with EU clients, review GDPR for Freelancers: A Step-by-Step Compliance Checklist for EU Clients during vendor diligence.
Leave the call with a small evidence pack: one sample tax-form record, one export sample, one access-control explanation, and one written statement of tax or legal responsibilities that stay with you and your advisor. If they cannot provide that, treat it as an operational risk.
Choose based on your real operating burden, not the best demo. Baseline compliance requirements are generic by design, so your decision should match your risk tolerance and the resources you have now and expect to have next.
Solo freelancer. Pick the simplest option that still demonstrates workable AML and KYC controls for your current capacity. A practical test is whether you can consistently run customer due diligence and transaction monitoring without cutting corners, since weak execution raises enforcement and reputational risk.
Small team. Buy for coordination, not just speed. Generic baseline compliance may not be enough once responsibilities are shared across people. Use one checkpoint: can your current team operate the platform's controls with your actual resources and planned growth? If not, treat that as a risk signal.
Finance-minded operator. Start with evidence and control coverage, then evaluate price. Ask which frameworks are covered now, including SOC 2, ISO 27001, PCI DSS, GDPR, and relevant local financial laws. Then verify regulator exposure by model and geography, since oversight can span multiple regulators.
Use deeper controls when requirements are rising. If client or regulatory expectations are increasing, consider the option that already shows stronger controls and clearer evidence, even if onboarding is slower. The practical check is simple: can the vendor clearly show covered frameworks, regulator exposure, and how controls are applied?
Before you commit, run a short, risk-focused check that forces the vendor to show evidence instead of talking around it. Use a three-phase cadence as a working structure, and spend the deepest review on the highest-risk parts of your setup.
Before the call, draft a planning memo. Define your actual scope: who will use the platform, which workflows are in scope, which markets or programs matter now, and where your highest risks sit. This keeps the review anchored to your operations instead of the vendor's default demo path.
Phase 1. Assess your critical controls using demonstrable evidence only. If a control cannot be shown in live product behavior and retrievable records, mark it as unproven.
Policy documents can add context, but they are not enough on their own. You need proof of how controls operate in practice and what records you can retrieve later.
Phase 2. Run one failure scenario and one cross-border scenario live. The goal is to see the sequence of actions, ownership, and artifacts created at each step.
For the cross-border scenario, ask exactly what changes by market or program, what happens when a corridor is restricted, and how escalation works. If the answer depends on roadmap promises or manual follow-up, treat it as unresolved risk.
Phase 3. Finish by locking down boundaries. Confirm scope limits and responsibilities in writing, by market or program.
End with a clear go or no-go rule: proceed only if critical controls are proven, both scenarios are answered clearly, and scope limits are documented. If any one of those is missing, pause and reassess.
Before your vendor call, use this as a practical checklist for what to ask about status tracking, control gates, and audit evidence: Review Gruv docs.
Compliance-later behavior usually shows up as a pattern of vague answers, not one dramatic miss. If a vendor cannot show specific scope, ownership, and retrievable evidence, the claim is still unproven.
| Red flag | What it looks like | Why it matters |
|---|---|---|
| "Global" claims without clear boundaries | They cannot map what is live, what is excluded, and what is still roadmap by jurisdiction or program | You still cannot measure operating risk |
| No clear owner for policy, incidents, or exports | Ownership collapses into "the compliance team" or a generic queue | Accountability is likely weak when an issue needs a fast, documented response |
| Tax and document flows described broadly, not operationally | There is no artifact-level proof, exact retrieval path, or sample records | Pause until document handling is shown operationally |
| Trend language replacing control detail | The pitch leans on policy headlines or "innovation" without concrete controls, exception handling, and exportable evidence | Innovation should strengthen AML compliance programs, not replace compliance work |
| Speed promises without visible verification checkpoints | Fast workflows are not tied to visible verification status, decision records, and clear escalation paths | Treat skipped verification points as risk |
"Global" is marketing language until they can map what is live, what is excluded, and what is still roadmap by jurisdiction or program. If they reference multiple regulators or jurisdictions but cannot explain practical boundaries, you still cannot measure operating risk.
A credible team can name who owns AML policy updates, who handles incidents, and who can produce evidence exports. If ownership collapses into "the compliance team" or a generic queue, accountability is likely weak when an issue needs a fast, documented response.
If document handling is described in general terms with no artifact-level proof, pause. Ask for the exact retrieval path and a sample of what records look like. Precision matters: FinCEN FBAR guidance expects verifiable exchange-rate sourcing, allows "amount unknown" handling in specific cases (item 15a), and structured submissions can be rejected when required elements are missing. FBAR timing can also vary by filing status, so static deadline claims should be checked carefully.
Be cautious when the pitch leans on policy headlines or "innovation" without concrete controls, exception handling, and exportable evidence. FinCEN's framing is that innovation should strengthen AML compliance programs, not replace compliance work.
Fast workflows are not a problem by themselves. The red flag is speed claims that cannot be tied to visible verification status, decision records, and clear escalation paths.
A practical decision rule: one red flag means request written proof and a live walkthrough. Two or more means pause the deal until gaps are resolved.
Choose the platform that can show its controls under pressure, not the one with the strongest compliance messaging. If two vendors sound similar, prefer the one that can show where KYC and AML checks run in the product and what evidence you can retrieve later.
That is the practical test. Compliance is operational, not just policy text. Legal, regulatory, and cybersecurity obligations need to show up in how the platform works.
Before procurement moves, run your due diligence check and document the result while the vendor is still in front of you. The format can be simple, but it should capture the points that matter later:
Evidence quality is the separator. Marketing claims, trust-page language, or named frameworks are context, not proof. What you need is a product walkthrough that shows where controls trigger and what record remains when decisions are reviewed.
This is where speed versus control becomes real. Faster launch paths can help, but they still require careful due diligence. If speed claims skip verification points, treat that as risk.
The recommendation is straightforward: pick the option whose controls, evidence trail, and failure handling fit your real operating risk profile. If a vendor cannot show those controls clearly during diligence, expect more risk when stakes are higher.
For a step-by-step walkthrough, see The 'AI Co-Pilot' for Global Compliance: A Product Vision.
If you want to pressure-test your exact corridors, compliance gates, and operational ownership before deciding, contact Gruv.
In plain terms, compliance-first fintech treats compliance as part of how the product works, not a fix after growth. The core checks are visible AML/KYC controls: identity verification at onboarding, transaction monitoring after onboarding, and a defined suspicious-activity reporting path. If those controls only appear after a problem, the posture is likely compliance-later.
These sources focus on fintech firms and their obligations. For smaller customers, including freelancers, it still matters because you rely on the platform to move money legally and securely. Fintech compliance covers legal, regulatory, and cybersecurity obligations, and non-compliance can lead to reputational damage, customer loss, and penalties. Even as a smaller customer, weak vendor controls can become your operating risk.
Start with the clearest baseline controls: AML/KYC verification at onboarding, ongoing transaction monitoring, and a defined suspicious-activity process. Then ask the vendor to show how those controls appear in the product and what evidence can be retrieved later. If they cannot demonstrate that clearly, treat the claim as unproven.
Use the same practical checks for both vendors instead of trying to interpret every rule yourself. Ask what they verify at onboarding, how they monitor transactions, how suspicious activity is handled, and what evidence they can provide to support decisions. Oversight can involve multiple regulators, so the stronger vendor is usually the one that can explain controls in clear product terms, not broad assurances.
A common pattern is vague answers where concrete controls should be. Watch for broad “global” claims without clear scope, speed claims without visible verification points, and trend language that replaces operational detail. If direct compliance questions keep turning into marketing copy, pause the decision.
Assume variation by default, because fintech compliance is not one-size-fits-all across regulatory frameworks. Ask for written scope that separates what is live now from what is excluded or planned, and confirm who maintains that scope. A verbal “yes” is weaker than a durable record you can refer back to later.
No. Automation helps, but it does not prove trust by itself. RegTech can scan for regulatory changes, map impacts across processes, and in some cases cut response time from weeks to hours. Trust still depends on whether the vendor can show clear controls and retrievable evidence when asked.
Nathan writes about choosing vendors safely—due diligence, compliance cues, and how to evaluate platforms when your business depends on them.
With a Ph.D. in Economics and over 15 years of experience in cross-border tax advisory, Alistair specializes in demystifying cross-border tax law for independent professionals. He focuses on risk mitigation and long-term financial planning.
Educational content only. Not legal, tax, or financial advice.

Start by separating the decisions you are actually making. For a workable **GDPR setup**, run three distinct tracks and record each one in writing before the first invoice goes out: VAT treatment, GDPR scope and role, and daily privacy operations.

RegTech becomes a moat only when it makes compliance decisions easier to execute and defend. The buying decision comes down to one question: does this investment create durable capacity, or does it add overhead your team must carry?

Treat the Singapore EntrePass as a work pass decision first, not a paperwork sprint. It is described as a work visa for foreign entrepreneurs, innovators, and experienced investors who want to start and run a business in Singapore, and foreign professionals need a valid work pass before starting work there.