
The safest place to hire a virtual assistant is the sourcing model that matches your classification exposure, data sensitivity, confidentiality needs, and continuity requirements. Define the role first, start with high-time, low-risk tasks, and choose between a managed provider, freelance marketplace, or direct regional hiring board based on required access and your ability to supervise.
If you're looking for virtual assistant support, start with risk, not rates, badges, or platform feature lists. The best place to hire a virtual assistant is the one that matches your exposure on classification and oversight, then your internal requirements around data access, confidentiality, and service continuity.
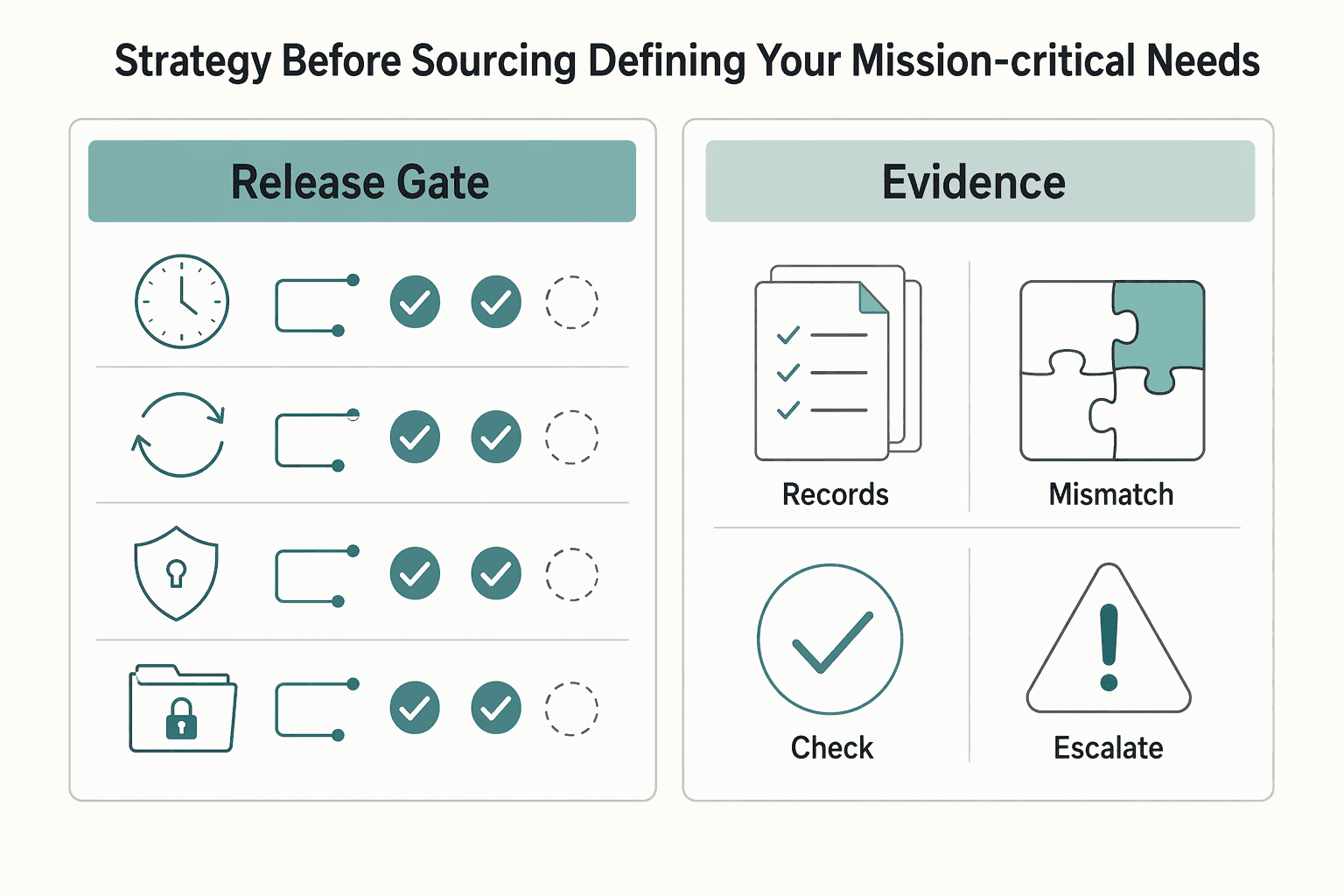
Use risk filters before you compare sources. Classification is the first gate because the Department of Labor has revised its interpretation of independent contractor status under the FLSA. Treat worker status as a live issue, not boilerplate. Then apply your operational filters for data access, confidentiality, and service continuity based on your policies and risk tolerance. Choose a hiring channel based on what could go wrong, not just how fast you can fill the role.
Verify legal-status and oversight claims instead of trusting summaries. If you are reading classification guidance on FederalRegister.gov, note that the site itself says researchers should verify against an official Federal Register edition on govinfo because its XML rendition does not provide legal notice. The 09/25/2020 proposed rule entry is cited as 85 FR 60600 and tied to RIN 1235-AA34. If a firm or partner leans on federal credibility, check the business name or UEI in FPDS.gov, USAspending.gov, and GSA eLibrary. A common failure mode is mistaking guidance for oversight. GSA says its OSDBU provides partnership guidance, not direct oversight.
Follow this guide in sequence, not all at once. First define the role and its guardrails. Then compare sourcing models. Then onboard using contract terms and access controls that fit your legal and compliance requirements. Order matters. If your scope and guardrails are still fuzzy, platform comparisons are just noise.
If you want a deeper dive, read What to Do If You've Been Misclassified as an Independent Contractor.
Your first decision is internal: define the role, its risk boundaries, and success criteria before you compare platforms.
Use a Total Cost of Delegation checklist that includes management time, rework risk, compliance exposure, and data-handling risk, not just labor price. A low rate is not low cost if you spend too much time correcting work or cleaning up avoidable exposure.
Use a simple worksheet that leaves unverified inputs blank until you can confirm them from operating records: your hourly value, an acceptable rework threshold, and an exposure assumption based on your business. The goal is practical decision quality, not fake precision. If supervision stays heavy beyond a short ramp, your scope is likely wrong, and in many freelance marketplace setups that correction burden sits with you.
Start in the Delegation Zone: high-time, low-risk tasks first. This lets you test consistency and judgment before you expand access.
| Time / risk | Low security or compliance risk | High security or compliance risk |
|---|---|---|
| High time consumed | Delegate now: calendar coordination, travel research, CRM cleanup, content formatting | Delegate later: inbox triage, bookkeeping prep, invoice follow-up |
| Low time consumed | Automate: reminders, meeting confirmations, routine file moves | Retain: bank-account control, contract signing, final approval on legal or financial records |
Keep task descriptions specific enough to assign and review. If a task touches payment authority, contract authority, or primary accounts, keep it with you until trust and controls are proven.
Define access controls before writing the job ad. Set non-negotiables: password-manager sharing, role-based least-privilege access, an off-limits account list, and a documented revoke process.
Share credentials through a password manager, not email or chat. Grant the lowest role needed for each tool, and keep sensitive accounts off-limits until there is proven reliability. Test your revoke process once before hiring; if you cannot remove access quickly, tighten setup first.
Decide your document set at this stage. At minimum, include an Independent Contractor Agreement. If the role includes personal-data processing, decide whether a DPA belongs in your setup and review your obligations. If EU client data is part of your work, GDPR for Freelancers: A Step-by-Step Compliance Checklist for EU Clients is the right companion read.
Set onboarding criteria in four buckets: quality, turnaround, escalation rules, and communication cadence.
Define each onboarding criterion from workflow records before you use it: current review standard, response or completion target, escalation triggers, and check-in cadence all need operating verification. Escalation rules should be explicit about when the assistant must pause and ask. Hire and review against observable outcomes.
With this in place, platform comparison becomes more straightforward in the next section: you will evaluate options against a defined role, known risk profile, and pre-set controls, not branding or price alone.
For a step-by-step walkthrough, see The Best Virtual Phone Number Services for Freelancers.
Choose your sourcing model based on what you can safely control, not what looks cheapest. No channel is automatically safer; risk changes with task sensitivity, required access, and your ability to supervise.
Before you choose, run four quick tests against your Delegation Zone:
If your answers conflict, pick the model that gives you tighter control.
| Decision point | Managed provider | Freelance marketplace | Direct regional hiring board |
|---|---|---|---|
| Contract responsibility | Usually one provider agreement with you; verify who contracts with the worker | You typically contract with the freelancer and carry classification review | You contract directly and carry classification review |
| Data-processing obligations | Ask for NDA and DPA where personal data is involved; provider controls do not replace your access limits | You need your own NDA, Independent Contractor Agreement, and DPA where appropriate | Same as marketplace, with added cross-border diligence if relevant |
| Replacement continuity | Possible, but verify backup or substitution terms in writing | Usually no built-in continuity unless you create it | Usually no built-in continuity unless you create it |
| Quality control burden | Lower sourcing burden, but ongoing review is still yours | High: screening, test tasks, feedback, and follow-up sit with you | High: direct screening and performance management sit with you |
| Dispute handling path | Usually through provider contract or account contact; verify terms | Often split between platform process and your contract terms; verify boundaries | Usually handled through your direct contract terms; verify jurisdiction and notice clauses |
Use this model when support is ongoing, access needs are meaningful, and you want less sourcing overhead. You get a more centralized operating setup, but you still own scope, permissions, and review quality.
Do not assume provider vetting replaces your controls. You still need least-privilege access, password manager use, and clear off-limits systems. If personal data is in scope, confirm NDA and DPA coverage early and read the service terms closely.
The common failure mode is outsourcing judgment along with hiring. Also verify continuity terms in writing instead of assuming replacement is guaranteed.
Use a marketplace like Upwork when the work is tightly scoped, access can stay narrow, and you are ready to run vetting yourself. This is often practical for trial tasks in the Delegation Zone.
You gain speed and flexibility, but you own most of the risk controls: screening, security setup, quality checks, and client-side worker-classification responsibility. Keep your legal baseline in place with an Independent Contractor Agreement and NDA, then verify current jurisdiction-specific rules where classification specifics matter.
Weak controls usually show up early here. A common mistake is hiring a vague "general VA," then granting high-access accounts before low-risk performance is proven. If you use AI-heavy screening, keep human review in the loop.
Use a board such as onlinejobs.ph when you want a direct relationship and can handle diligence yourself. This can work well for recurring support, but only if you plan for the full Total Cost of Delegation, not listing price alone.
Your document pack is core: Independent Contractor Agreement and NDA at minimum, plus a DPA where personal data is processed. If EU client data is involved, review obligations before granting access. GDPR for Freelancers: A Step-by-Step Compliance Checklist for EU Clients is the right companion if that applies.
The failure mode is treating direct hiring as "flexible" without structure. You still need role-based access from day one, a tested revoke process, and a basic continuity plan if the relationship ends suddenly.
Platform choice is only step one. Whether the model stays safe depends on the onboarding controls you apply once someone gets access. If you are comparing collaboration tools around that workflow, see The Best Tools for Virtual Whiteboarding and Brainstorming.
Your onboarding controls determine whether delegation stays safe and useful. Focus on three things you control from day one: contract terms, data-protection rules, and staged access.
| Area | What to confirm | Timing |
|---|---|---|
| Contract terms | Scope boundaries and clear deliverables, confidentiality expectations, IP ownership terms, payment workflow, termination and offboarding steps, dispute framework, and current jurisdiction-specific terms for governing law, classification, and other location-specific requirements pending legal/source/adviser verification | Before any account is provisioned |
| Data protection | Whether a DPA is required for your client profile and geography; if not, equivalent privacy controls for permitted data use, storage, sharing limits, incident reporting, and return/deletion obligations at exit | Before granting access |
| Access ramp | High-time, low-risk tasks first, named accounts where possible, a password manager instead of direct password sharing, and role-based permissions set to least privilege | From day one |
| Workflow controls | What can be sent, changed, published, or spent without approval; what requires escalation; and where activity is logged for review | Upfront |
| Offboarding | Revoke accounts, rotate shared credentials where used, remove vault access, confirm return/deletion of sensitive files, and record the access end date | At exit |
Use your Independent Contractor Agreement as an operating checklist, not legal theater. Confirm these items before work starts:
If you cannot define what "done" means, how payment is approved, and what happens at exit, pause onboarding. That gap usually turns into rework and access mistakes.
If the assistant will process personal data, confirm whether a Data Processing Agreement (DPA) is required for your client profile and geography before granting access. If a DPA is not required after verification, include equivalent privacy controls in contract terms anyway: permitted data use, storage expectations, sharing limits, incident reporting, and return/deletion obligations at exit.
Run a quick data map first: systems used, data types inside them, and the minimum data needed for each task. This keeps convenience from driving unnecessary access.
Start with high-time, low-risk tasks and low-risk systems. Use named accounts where possible, a password manager instead of direct password sharing, and role-based permissions set to least privilege. Expand access only after documented checkpoints show reliable quality and judgment.
Define workflow controls upfront: what can be sent, changed, published, or spent without approval; what requires escalation; and where activity is logged for review. Keep offboarding explicit: revoke accounts, rotate shared credentials where used, remove vault access, confirm return/deletion of sensitive files, and record the access end date.
Autonomy without exposure checklist
If you need a place to organize sensitive files during that process, The Best Virtual Data Room (VDR) Software may help.
You should feel confident hiring only when three things are true: you have defined the role clearly, chosen a sourcing model that fits your risk tolerance, and planned onboarding and access sequencing before any real access is given. That is what lowers stress, not a lower fee, not a prettier platform ranking, and not a promise that someone can "do everything."
A practical closeout looks like this:
Do not chase a universal winner. One publisher frames the market as 16 VA websites, while another lists 11, which tells you rankings vary and your decision should rest on fit, not list position. The real differentiator is whether you want to manage sourcing and oversight yourself or buy more structure from the provider.
Confirm role scope, communication expectations, and your onboarding checklist before an account is created. Timing is the key point here: setup first, credentials second. If you're still figuring out basic terms after the hire decision, you're already behind.
Begin with low-risk administrative tasks such as sorting emails, scheduling meetings, booking flights, preparing agendas, and filing expense reports. Your checkpoint is simple: review real work quality before expanding permissions. A common failure mode is letting old or unnecessary access and personal data linger longer than needed.
Post the job, review profiles, interview, then hire. After that, keep updating online accounts and cleaning up old access as part of normal security hygiene.
This is how cost stays in perspective: you reduce security and process surprises, create cleaner handoffs, and free more time for owner-only work instead of fixing preventable mistakes. For the handoff itself, use How to Delegate Work to a Virtual Assistant next, then keep your account follow-through current after the hire. We covered a similar decision process in The best 'book cover design' services for indie authors.
Have clear written terms in place before any account is created. At minimum, define scope, deliverables, payment workflow, confidentiality expectations, approval flow, termination, and offboarding steps. If personal data will be processed, confirm whether a DPA is required for your client profile and geography before granting access.
Use a staged access ramp instead of giving full access on day one. Start with high-time, low-risk tasks, use named accounts where possible, share credentials through a password manager, and set least-privilege permissions. Expand access only after documented checkpoints show reliable quality and judgment.
It is not automatically better to hire locally or overseas. Treat it as an operating-model choice and decide first whether you need a freelancer or a dedicated VA. Then compare providers based on the work you need covered and the level of oversight, data access, and compliance control you can manage.
Yes, use clear confidentiality terms in writing. Make sure both sides understand how sensitive information should be handled. If you need jurisdiction-specific legal language, confirm it with qualified counsel.
Do not anchor on a single hourly rate or listing price. Compare cost to scope, support level, accountability, management time, rework risk, compliance exposure, and data-handling risk. The right price depends on the sourcing model and how much oversight and continuity you need.
virtual assistant or VA is the defined term. VEA is not presented as a formal separate category. Focus on the actual scope, autonomy, and approval process you need rather than the label.
A former tech COO turned 'Business-of-One' consultant, Marcus is obsessed with efficiency. He writes about optimizing workflows, leveraging technology, and building resilient systems for solo entrepreneurs.
Priya is an attorney specializing in international contract law for independent contractors. She ensures that the legal advice provided is accurate, actionable, and up-to-date with current regulations.
Educational content only. Not legal, tax, or financial advice.

Start by separating the decisions you are actually making. For a workable **GDPR setup**, run three distinct tracks and record each one in writing before the first invoice goes out: VAT treatment, GDPR scope and role, and daily privacy operations.

Treat this as a protection problem first, not a label debate. If your work was treated as an independent contractor arrangement even though the relationship functioned differently, your first goal is to protect pay, rights, and records while you choose the least risky escalation path. You can do that without making accusations on day one, which often keeps communication open while you document what happened.

As a professional, you are the engine of your business. Your expertise brings in revenue, your standards shape quality, and your judgment sets direction. That is a strength, but it is also a limit. When growth is capped by the number of hours you can personally work, you are not operating as a CEO. You are operating as a high-performing bottleneck.