
Use a three-tier vetting process. Keep low-sensitivity roles in Tier 1 for identity, business presence, references, and scope checks; move higher-access U.S.-based contractor decisions to Tier 2 if you may order a third-party consumer report; and treat any cross-border case as Tier 3 with country-level intake, minimal data collection, provider proof, and a documented audit trail.
Start by deciding whether you need formal screening at all. If the contractor will do low-sensitivity work with least-privilege access and no control over money, customer data, production systems, or live client relationships, Tier 1 may be enough. If any of that changes, or you expect to use a formal third-party background study or screening report, stop and move the case to Tier 2.
Step 1. Define the real scope. Write down exactly what the contractor can see, change, approve, or say on your behalf. Good scope notes name the tools, data sets, spending authority, and client exposure. Your checkpoint is simple. If you cannot describe the access in one clear paragraph, you are not ready to clear the role as low sensitivity.
Step 2. Verify the basics with more than one source. The COPS background screening guide (published 2021) recommends using a variety of resources, not a single check. It specifically includes written applications or interviews and reference checks.
| Tier 1 check | What you confirm | Common failure pattern | Escalate now when |
|---|---|---|---|
| Identity and business presence | Legal or working name, contact path, consistent business footprint | Names, emails, and portfolio records do not line up | You cannot tie the person cleanly to the engagement |
| Experience and references | Relevant work history and references that match the assignment | Vague references, inflated role claims, no similar work shown | Core claims remain unverified after follow-up |
| Access fit | Requested access matches the narrow task | Scope quietly expands after discussion | They need admin rights, payment approval, or client-facing authority |
Step 3. Log unresolved risk. Keep one intake record with the person or entity name, role summary, exact access requested, evidence reviewed, open gaps, decision owner, review date, and next trigger for re-review. Make the engagement owner responsible. Review the file before credentials are issued and again if scope expands.
Step 4. Make the go or escalate call. Proceed only if the facts line up and access stays narrow. Escalate if verification conflicts remain, access broadens, or the role may trigger formal screening by law. For example, Minnesota child care rules require background studies for some people with direct-contact services or access to vulnerable adults and children. In that process, if fingerprinting is required by law, the subject has 14 days from study initiation to be fingerprinted at a DHS-approved location and must present acceptable identification. Before using this example, verify the current state and local rule with counsel or an official source.
If you cannot keep the case inside that narrow lane, do not improvise. Move to a formal process and document why. Related: Best Virtual Mailbox Services With Check Depositing.
Use Tier 2 when you are considering a third-party consumer report for a high-access, U.S.-based contractor decision. Your main control is simple: define your standards before you order anything, then run the same sequence every time.
Create a dated screening note first so another reviewer could apply it the same way. Include:
| Standard | What to document |
|---|---|
| Role access profile | Document exactly what access the role gets (systems, data, payment authority, production credentials, admin rights, client-facing authority). |
| Job-relevant findings criteria | State which findings matter for this role and why they connect to actual access or risk. |
| Individualized assessment rubric | Set how you will review context, timing, accuracy questions, and role relevance before any final decision. |
Document exactly what access the role gets (systems, data, payment authority, production credentials, admin rights, client-facing authority).
State which findings matter for this role and why they connect to actual access or risk.
Set how you will review context, timing, accuracy questions, and role relevance before any final decision.
If a second reviewer cannot reach a consistent decision from this note, tighten it before moving forward.
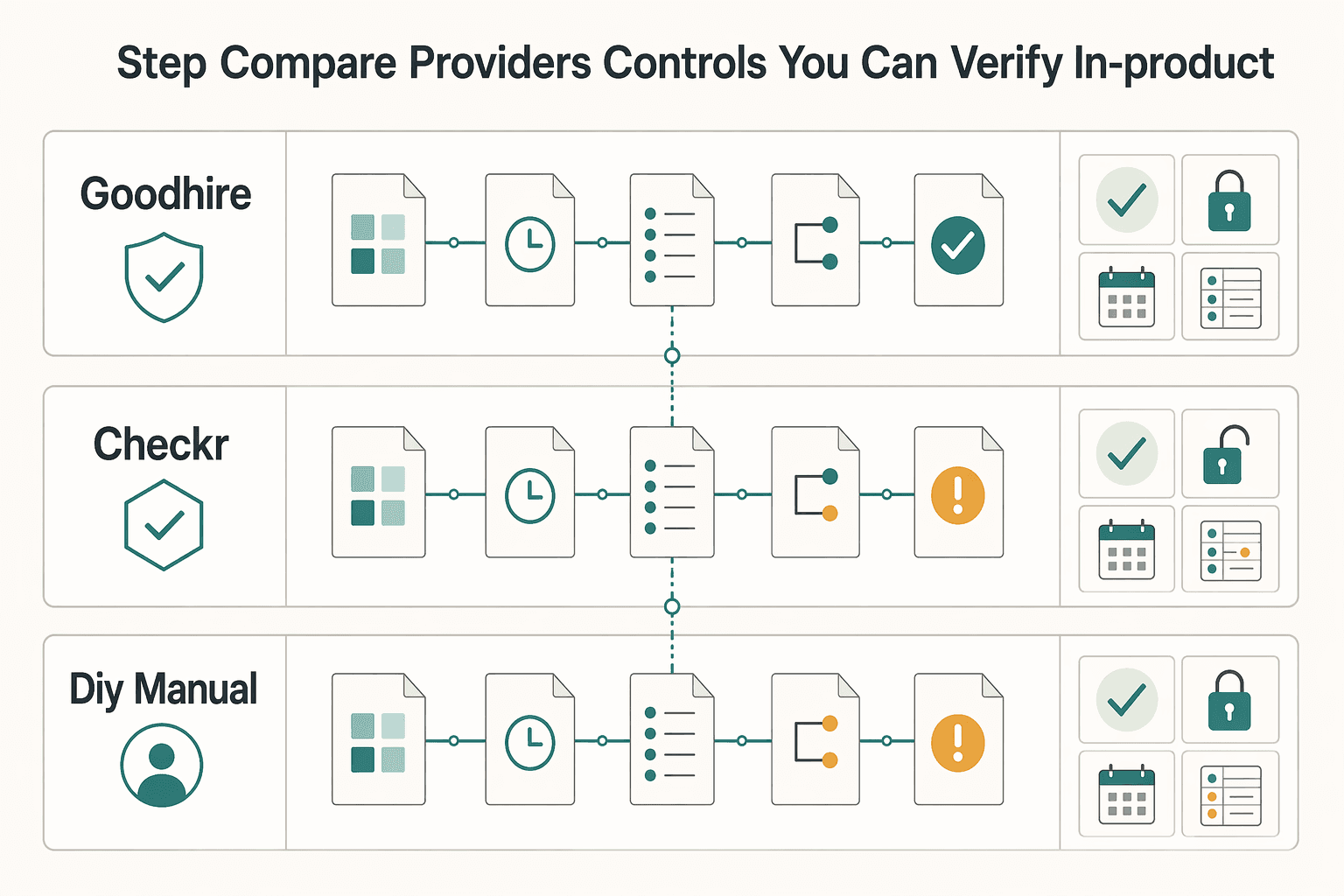
Do not rely on positioning or sales language alone. Validate what your team can actually run, review, and export in your account.
| Option | Disclosure and authorization flow | Adverse-action workflow controls | Audit-log exportability | Role-based package configurability |
|---|---|---|---|---|
| GoodHire | Verify how disclosure and consent are presented and versioned in your workflow | Verify pause, review, and release controls plus ownership points | Verify timestamped case history export for the full file | Verify you can map package scope to role risk |
| Checkr | Verify candidate flow, template governance, and change control | Verify handling paths for disputes, delays, and manual review | Verify exportable history of actions, notices, and user activity | Verify package and approval-path differences by role |
| DIY/manual process | Build and maintain your own disclosure and consent process | Manually run every hold, review, and notice step | Maintain your own timing and delivery records | Enforce role-based scope discipline internally |
Run one test case and confirm you can produce a complete evidence pack: approved template version, timestamps, user actions, notice history, and final decision note.
Use a fixed internal order for comparable cases:
| Sequence step | What to do |
|---|---|
| 1 | Confirm written criteria and check for stricter state/local conflicts. |
| 2 | Prepare disclosure and authorization materials using current approved versions. |
| 3 | Order only report components tied to the documented role access. |
| 4 | Review results against written criteria, not ad hoc judgment. |
| 5 | If a negative decision is under consideration, send your pre-decision packet and hold the final decision until the current waiting window is verified by counsel and official sources. |
| 6 | Review disputes/corrections, apply the individualized assessment rubric, then issue final notice if the decision stands. |
Escalate immediately when you see stricter state/local rule conflicts, contractor-classification uncertainty, disputed report data, or any cross-border touchpoint (person, records, consent flow, or notice path). If classification risk appears, hand it off early and use What to Do If You've Been Misclassified as an Independent Contractor.
Also escalate legal wording changes. Contract edits can affect party rights, and in the TREC context, adding rights-affecting language can be treated as unauthorized practice of law and may lead to disciplinary action, including possible administrative penalties of $500-$3,000 per violation per day and possible license suspension or revocation. Practical rule: if wording changes legal effect, route it to counsel instead of drafting your own addendum.
For adjacent pricing decisions, see Value-Based Pricing: A Freelancer's Guide. For platform options, Browse Gruv tools.
Tier 3 starts as soon as your screening touches another country through the person, records, provider, or data path. Pause ordering until you have one written intake record that defines scope, jurisdictions, role-relevant checks, and everyone who will receive, store, or process screening data.
Keep the Tier 2 discipline, but make it country-first. In cross-border cases, the goal is not to collect more data. The goal is to collect only what is role-relevant, keep scope minimal, and keep an audit trail you can defend.
Use one intake format for every global case so a second reviewer can quickly confirm readiness.
| Intake field | What to record before ordering |
|---|---|
| Country touchpoints | Every country connected to the person, role, records, provider operations, and storage location |
| Transfer route | How data is expected to move between parties and locations |
| Lawful-basis assumptions | The assumptions your team is relying on for this review |
| Role-relevant checks | Only the checks tied to actual access and risk in this role |
| Data-handling parties | Internal users and external providers involved in processing |
| Ready-to-order gate | Owner, date, and explicit approve/hold decision |
If this artifact cannot clearly show countries, checks, and handling chain in one place, hold the case.
Set a country-by-country input checklist and mark each field as mandatory, optional, or not collected before ordering. Keep the list limited to what your provider or local reviewer says is needed for that jurisdiction, and avoid turning optional fields into default collection.
| Input | How the article frames it | Limit |
|---|---|---|
| Full legal name used in that country | A practical checklist can include this field. | Set status as mandatory, optional, or not collected before ordering. |
| Alternate/local-script name | Include if your process needs it. | Avoid turning optional fields into default collection. |
| Date of birth | A practical checklist can include this field. | Keep the list limited to what your provider or local reviewer says is needed for that jurisdiction. |
| Address history | A practical checklist can include this field. | Keep the list limited to what your provider or local reviewer says is needed for that jurisdiction. |
| Additional identifier | A practical checklist can include this field. | Collect only if the provider requires it. |
A practical checklist can include full legal name used in that country, alternate/local-script name if your process needs it, date of birth, address history, and any additional identifier the provider requires. If field status is unclear, pause and resolve it first.
Treat recommendation lists as leads, not decision evidence. Some pages separate employer use cases from individual use cases, and some disclose that commission can affect placement order, so ranking position alone is not enough.
| Proof point | What to verify in a walkthrough or dummy case |
|---|---|
| Country-level availability detail | Specific country/check matrix for your use case |
| In-country verification method | How each check is actually verified in each country |
| Localized consent artifacts | Candidate-facing consent/disclosure materials used for your country pair |
| Dispute handling path | Who pauses, reviews, and resolves challenged results |
| Exportable audit evidence | Timestamps, template versions, consent records, user actions, and case history exports |
Ask to see the artifacts directly. As one example of the kind of traceable evidence to look for, a public consent component may show cookie categories, retention periods (such as 1 hour, 6 months, and 1 year), and a statement that its consent-preference cookie does not store personal information.
Do not force a check when core controls are weak. Escalate and hold instead.
| Risk condition | Fallback control | Escalation trigger |
|---|---|---|
| Records appear restricted or incomplete | Pause ordering and document what is unavailable | Escalation path pending provider and policy verification. |
| Transfer basis or handling chain is unclear | Freeze case until intake assumptions are reviewed | Escalation path pending provider and policy verification. |
| Dispute workflow is weak or undocumented | Do not proceed until dispute ownership and steps are clear | Escalation path pending provider and policy verification. |
Current review interval pending internal policy verification; recheck sooner if access expands. If worker classification risk appears, route it separately and early: What to Do If You've Been Misclassified as an Independent Contractor.
You might also find this useful: How to Do a Background Check on a New Client Before Signing.
Run every case with one owner, one intake record, and one tier decision. If any one is missing, pause until it is complete.
| Action | What to do | Outcome |
|---|---|---|
| Assign the owner and finish intake | Capture role scope, actual system/data/money access, countries involved, identity fields used for matching, proposed tier, and why that tier fits. | Intake is complete enough that a second reviewer can follow the tier choice without follow-up. |
| Execute the tier and produce its artifact set | Use a separate workflow by case type instead of forcing one path. | Tier work is done and handoff artifacts are ready. |
| Escalate with an action-ready packet | Send verified facts with evidence, unresolved items, temporary controls in place, and the exact decision needed next. | Escalation can be processed without back-and-forth. |
| Close with governance controls | Record final decision, dispute path, retention period pending counsel and policy verification, disposal method pending approved-policy verification, and review cadence pending internal policy verification. | Case is auditable, reviewable, and ready for renewal/closure tracking. |
Capture role scope, actual system/data/money access, countries involved, identity fields used for matching, proposed tier, and why that tier fits. Outcome: Intake is complete enough that a second reviewer can follow the tier choice without follow-up.
Use a separate workflow by case type instead of forcing one path. The Wisconsin Caregiver Program Manual (P-00038, 10/2025) uses distinct process tracks, incident reporting, complaint handling, and a 4-Year renewal checkpoint; apply that same process discipline here. Outcome: Tier work is done and handoff artifacts are ready.
| Tier | Execute now | Escalate when | Artifacts ready before handoff |
|---|---|---|---|
| Tier 1 | Verify identity, business presence, references, and scope fit | Facts conflict, access expands, or risk rationale is unclear | Intake record, verification notes, scope note, initial decision |
| Tier 2 | Follow your verified employer-screening process for this role | Identity match is weak, report content is disputed, or classification risk increases | Intake record, consent record, search scope, provider output, dispute status |
| Tier 3 | Map countries, provider coverage, consent path, and data-handling chain | Current jurisdiction trigger pending counsel and official-source verification, coverage gaps, or unclear dispute handling | Jurisdiction map, provider feasibility notes, open-risk list, control plan |
Send only what the next reviewer needs to act immediately: verified facts with evidence, unresolved items, temporary controls in place, and the exact decision needed next. Outcome: Escalation can be processed without back-and-forth.
Record final decision, dispute path, retention period pending counsel and policy verification, disposal method pending approved-policy verification, and review cadence pending internal policy verification. If the role now looks like employment, pause and use A Guide to Background Checks for Employees. Outcome: Case is auditable, reviewable, and ready for renewal/closure tracking.
For reference-workflow details, use How to Check References for a Potential Hire. For country/program confirmation, route through your approved path: Talk to Gruv.
Yes, if the person is effectively part of your workforce and the role creates real access, safety, money, or client risk. For low-sensitivity work, Tier 1 may be enough for identity, business presence, and reference checks. If you plan to order a third-party consumer report for a U.S.-based engagement, move to Tier 2 and complete disclosure, authorization, and notice steps first.
For hiring decisions, start in the employer-use lane, not with a people-search or individual-use product. Confirm which results are database pulls, which are verified through court records or other direct sources, and whether you can keep the scope tied to the role. If a provider cannot explain the verification method clearly, treat that as a red flag.
Start with a country-level intake before any order is placed. Document the jurisdictions, exact checks, and the handling chain, and keep the scope minimal and role-relevant. If country coverage, consent artifacts, or dispute handling are unclear, stop and escalate.
Yes, but only in Tier 1 as signal discovery. Use it to surface issues worth verifying, not to make a final decision. If a result matters, move it into a proper employment screening process with role-relevant, auditable verification.
A baseline package can include an address and name history trace, a county court criminal search, a criminal database search, and a sex offender registry search. Depending on the role, you may also add motor vehicle records or federal court searches when the access risk supports them. Before consent goes out, ask for the exact search list and save your scope note and approval.
Many U.S. checks typically finish in two to four business days, but that is not a promise. Court backlogs and hard-to-reach prior employers can slow the file. Ask the provider to separate instant database results from court-verified components, and tell the candidate what documents may help if employment verification stalls.
Pause and treat that as an escalation point. If your screening starts to mirror employee screening, use employee-style controls and consider a separate classification review. Do not treat it as a minor paperwork issue.
An international business lawyer by trade, Elena breaks down the complexities of freelance contracts, corporate structures, and international liability. Her goal is to empower freelancers with the legal knowledge to operate confidently.
Priya is an attorney specializing in international contract law for independent contractors. She ensures that the legal advice provided is accurate, actionable, and up-to-date with current regulations.
Includes 2 external sources outside the trusted-domain allowlist.
Educational content only. Not legal, tax, or financial advice.

Value-based pricing works when you and the client can name the business result before kickoff and agree on how progress will be judged. If that link is weak, use a tighter model first. This is not about defending one pricing philosophy over another. It is about avoiding surprises by keeping pricing, scope, delivery, and payment aligned from day one.

Treat this as a protection problem first, not a label debate. If your work was treated as an independent contractor arrangement even though the relationship functioned differently, your first goal is to protect pay, rights, and records while you choose the least risky escalation path. You can do that without making accusations on day one, which often keeps communication open while you document what happened.

**How elite consultants and contractors transform a compliance hurdle into a strategic advantage.** For an independent professional operating at a high level, a client-requested background check can feel like an awkward last hurdle. After weeks of strategic conversations, proposal refinement, and building peer-level rapport, a formal request for personal data can change the tone. It does not have to.