
Yes, this risk is manageable if you run it as an operations control loop. Start with § 12 AO and § 13 AO screening, then check whether workspace patterns, approval paths, and contemporaneous day records still match your active MSA and SOW. If the file shows drift, contain first: stop undefined expansion, move signoff back to the client’s authorized team, and escalate before renewal rather than trying to repair evidence later.
Your client’s concern can be straightforward: the contract says one thing, but the day-to-day record may start showing another. In permanent establishment risk germany, that mismatch can make a file harder to assess quickly and escalate for advice.
Use a simple decision flow: review what your records actually show, separate that from any legal conclusion, then escalate early if the story is inconsistent or unclear. A common operational issue is drift rather than one dramatic event.
Files can drift over time. Occasional on-site work may become routine, message wording may blur approval authority, and calendars, invoices, and scope records may stop lining up. Run three blunt checks:
If any answer is weak, contain first and review before expanding scope. Then use the table below to choose the immediate containment step.
| Risk signal (operational, not a legal test) | What good control looks like | Immediate containment action |
|---|---|---|
| Workspace use is becoming regular, named, or expected | Records show where work happened, why it happened there, and whether access was temporary or task-specific | Stop casual repeat use, document any on-site purpose, and retain access and visit records while facts are fresh |
| Approval wording makes you sound like the final decision-maker | Contracts and message threads show named client approvers issuing final commercial signoff | Shift final approvals back to the client in writing and fix template and email phrasing that implies you approved for them |
| Records are thin, delayed, or inconsistent | Calendar, invoice, scope, and approval records align in one evidence file | Pause new scope, reconcile recent records, and fill gaps with dated support items |
| Scope expands informally via chats or calls | New tasks start only after written scope or change approval | Treat informal asks as pending until the change is documented |
These controls do not remove legal risk by themselves. They can give you an earlier, cleaner decision point before convenience hardens into a pattern.
Start with one recent month and test your operating proof against the active MSA and SOW. If approvals, calendars, invoices, and access or travel records tell one consistent story, you have a clearer base for legal review. If they conflict, treat that as an escalation trigger, not something to clean up during renewal week.
Source quality is part of the diagnosis. A parliamentary Q&A compilation is not tax guidance for this question. That publication itself notes language mismatches can occur between questions and answers. The September 2024 Commission competitiveness report also states it should not be treated as the Commission’s official position.
Verification note: confirm the exact document, date, and language version with qualified advice before relying on administrative or treaty interpretation. If your uncertainty sits at the treaty layer, review this companion guide on the US Germany tax treaty.
You might also find this useful: The Role of a Permanent Establishment in International Tax.
Use the same three-bucket review each cycle, in this order: fixed place, dependent agent, then service-day records. Treat it as an internal consistency check, not a legal conclusion. Here, these buckets are organizational labels for file quality, not confirmed legal tests. In this framework, the first two align with common PE trigger patterns, while the third is a documentation-control bucket.
Run this monthly and again after any change in scope, travel, or approval path. Do not move to duration tracking until you can clearly show where work happened and how final commercial decisions were handled.
The order matters because later checks can be weak if the earlier record is incomplete. If you cannot explain workspace use or who held final approval, day counting will not rescue the file. A clean duration log helps only when it sits inside a broader record that already makes sense. To run the cycle, ask one question per bucket before you move on:
| Review bucket | What counts as drift in practice | Lower-risk default | Minimum evidence before you move on |
|---|---|---|---|
| Fixed place | Your workspace pattern is no longer clearly documented in current records | Keep workspace use intentional and documented each time | Current agreement, visit or work record, and a short note on purpose and access context |
| Dependent agent | Your records do not clearly show who made the final commercial decision | Keep final commercial approval visibly with the client in the working record | Recent approval trail, signature or acceptance path, and one clear example of client final approval |
| Service-day records | Day tracking is incomplete, delayed, or reconstructed from memory | Log days in real time and confirm interpretation with an adviser | Day log, calendar match, and one support item per trip or work block |
If any answer is no, fix that bucket first. Do not let an incomplete first bucket create false comfort just because later tabs in the folder look fuller.
Start with what you can observe: workspace behavior and the quality of your documentation. If the file cannot show where work happened, why it happened there, and how that setup was handled, treat that as drift and fix it before moving on.
Keep the approach practical. Document each use case while it is current, and do not rely on labels alone to explain the pattern later.
Specificity matters here. A note saying "on site for project work" is weaker than a note showing the date, the task block, and the reason the work was done there. You do not need a long memo each time. You need enough detail to keep the pattern bounded when someone reviews it later.
This is also where routine habits quietly weaken a file. Repeated presence without a stated purpose is one sign. Recurring use of the same space without current records is another. If recordkeeping has shifted from real-time capture to end-of-month reconstruction, treat that as a warning sign, not an administrative inconvenience.
A simple habit works well. After each on-site block or location-specific work block, save the calendar entry, add a short purpose note, and file any access support the same day. That gives you a contemporaneous record and reduces the chance that later explanations depend on memory.
Next, test the real approval path. If the file does not show who made the final commercial call, the review is weak even if the contract language looks clean.
Use current threads, redlines, and acceptance records to confirm that the final step is visible and attributable. If conduct and wording diverge, treat that as a documentation gap and escalate.
This bucket usually breaks down because work moves faster than the record. You may start by preparing options, summarizing terms, or coordinating next steps. The problem starts when the file stops showing where your role ended and the client's authority began. If the last visible message in the chain comes from you and there is no clear client approval after it, the record may look more final than you intended.
Look for drift in how messages are phrased and routed. Are you telling third parties that something is approved when the client has not visibly approved it in the file? Are colleagues or counterparties treating your message as the final answer? Are redlines being closed out in a way that leaves no current record of the client's final step? Those are the moments to correct in writing, not just in conversation.
A strong working record usually has three pieces. First, the client comment or decision. Second, the path showing how that decision was communicated. Third, one recent example that clearly shows the client as the final approver on a material point. You do not need dozens of examples each cycle. You need enough current evidence to show the approval path is active, visible, and consistent with the contractual boundary.
Review this bucket only after the first two are documented. The goal is defensible tracking, not guesswork. This article does not provide a usable day-count rule or Germany-specific threshold, so confirm any legal interpretation separately before relying on the log.
Keep the process simple: log each Germany day with the date, location, business purpose, and whether client work was performed, then attach one support item. If you need background context, review A Freelancer's Guide to the US-Germany Tax Treaty.
What usually weakens this bucket is delay. A log built from memory after several weeks is harder to trust than one updated as travel or work happens. If you worked partly on travel days, note that while it is fresh. If you were in Germany but not doing client work on a given day, record that distinction at the time rather than trying to infer it later from a calendar title.
Support items do not need to be complicated. The point is to anchor each entry to something external to memory: a calendar entry, travel support, access record, work note, or another dated artifact. At month-end, check whether each line has a clear support item and matches the calendar. Do not ask whether you can still remember what happened.
Stay disciplined here. If days are missing, mark them as needing confirmation rather than quietly filling gaps with assumptions. An incomplete but honest log is easier to escalate than a polished log that cannot be supported.
Keep one folder and update it every month so another reviewer can follow the story without reconstructing it later:
Consistency matters more than perfect archiving. Use the same subfolders every month, keep file names dated, and avoid storing the only useful evidence inside an email inbox where another reviewer cannot easily find it. The goal is that someone else can open the folder and understand the facts without asking you to rebuild the timeline. A workable monthly sequence is:
That final step matters. A clean folder is useful only if you act on what it shows. If records, conduct, and contract language no longer line up, stop and escalate. Pause new commitments until an adviser reviews the file. For a broader operating context, read The Ultimate Digital Nomad Tax Survival Guide for 2025.
For a step-by-step walkthrough, see Permanent Establishment Triggers for Platforms: When to Escalate From Monitoring to Formal Review.
The client shield is a consistency test. If your contracts, operating behavior, and retained evidence stop matching, pause scope expansion and route the file for adviser review.
For PE screening, start by testing German domestic-law triggers under § 12 AO and § 13 AO, then layer treaty analysis as needed instead of assuming relief. Because cross-border outcomes are not always treated consistently, verify current status before relying on any single threshold.
In practice, the shield is not a single clause or a single script. It is the combined effect of clear boundaries plus behavior that respects those boundaries. When it works, a reviewer sees the same story in the MSA, the SOW, approval messages, presence records, and client-facing communications. When it fails, each document needs a separate explanation.
Your MSA and SOWs should set boundaries you can actually enforce. The point is to define your role clearly and keep final client authority with the client.
| Contract control | Boundary to enforce in MSA/SOW language | Evidence to retain |
|---|---|---|
| Role and scope | Define specified services and deliverables, not open-ended business functions | Signed MSA, active SOWs, negotiated redlines |
| Approval-path ownership | Keep final commercial approval, commitment, and signature authority with named client personnel | Approval emails, signature paths, acceptance records, one recent example of client final approval |
| Workspace terms | Define who controls access, who pays, and whether use is ongoing or occasional; keep on-site access tied to defined tasks, dates, or business purpose | Site-access terms, calendar entries, visitor records, short purpose note per on-site block |
| Change-control discipline | When scope or approval duties change, document the change before taking on new commitments | Change requests, amended SOWs, dated approval trail |
Use a quick check before the file drifts further: compare your current MSA, current SOW, and one live approval thread. If they do not show the same role and approval path, the shield is already weakening. At minimum, retain one support item per work block.
Read the documents against the work you are actually doing now, not the work you originally expected to do. A contract can start out appropriately bounded and still become stale if the engagement evolves informally. If the client now expects recurring tasks, broader coordination, or decision-handling that the signed documents do not reflect, that is not just a drafting issue. It signals that the operating model changed without matching documentation.
If you have negotiation history, keep it when it helps explain boundary choices. If a reviewer later needs to understand why approval authority stayed with named client personnel or why on-site access was limited to defined tasks, that record can add context.
Strong drafting does not help if day-to-day conduct points the other way. Treat these as real-time escalation signals.
| Observable signal | Immediate corrective action | Evidence to retain |
|---|---|---|
| Authority drift | Correct in writing and route final approval to the named client approver | Message rerouting approval, updated approval thread |
| Regular on-site pattern | Reset to defined work blocks with documented business purpose | Dated log, calendar entries, access records |
| Role ambiguity in working threads | Re-state the limited role and route final approvals back to the client approver | Client-facing thread showing correction |
| Undefined scope | Stop new work until documented through change control, or decline it | Change request, amended SOW, or refusal trail |
If your contract says one thing but your conduct shows delegated authority, routine place use, or approvals handled outside the documented path, stop role expansion and escalate.
Drift often shows up first in small operational moments. You get copied on more approvals. On-site attendance becomes the default rather than a defined exception. None of those moments should be ignored just because the contract still looks careful.
Correcting behavior is usually straightforward if you do it early. Move approvals back to the named client approver in writing. Confirm that your role is to prepare, not finalize. Reset on-site work to a stated task block with a documented purpose. Ask for a change request before starting anything outside the current SOW. The correction should leave an artifact, because a private understanding is not much help later if the written record points the other way.
One useful test is whether a third party reading only the current working threads would understand your limited role and the client's final approval authority. If not, the shield needs reinforcement immediately.
Short scripts work best when they are tied to a clear boundary and a documented handoff:
| Short script | Outcome | Handoff |
|---|---|---|
| I can prepare the recommendation, but final approval needs to come from your authorized team. | Authority stays with the client. | Keep the message that routes approval back. |
| I can be on site for this defined task, but I am not using the location as a standing base. | Access stays purpose-specific. | Log date, purpose, and related calendar entry. |
| That sounds outside the current SOW. Please send the change through the contract owner before I start. | Scope expansion is documented or stopped. | Retain the change request or refusal trail. |
These guardrails work best right after an ambiguous moment, especially after calls or meetings where roles can blur. If the conversation became fuzzy, send the follow-up note the same day. A short written summary that routes approval back, limits the on-site task, or requests formal change control does two jobs at once. It corrects the operating path and creates evidence that the boundary was reasserted.
Keep the scripts short because long explanations are harder to use consistently. The goal is not to sound defensive. It is to keep the file clear. If the same situation keeps recurring, that usually means contract terms, staffing expectations, or work design need attention, not just better wording in one email.
If you need treaty context before adviser review, A Freelancer's Guide to the US-Germany Tax Treaty is a companion read. It does not replace a current § 12 AO and § 13 AO check. For related planning, see How to Create a Financial Safety Net as a Freelancer.
Want cleaner scope and sign-off boundaries before your next renewal? Use this freelance contract generator to draft clauses you can review with your advisor.
For related treaty mechanics, see US-Germany Treaty Dividends and LLC Classification for German Residents.
Run one worksheet each month: collect current facts, test for drift, then decide whether to continue or escalate. The goal is simple: if records, conduct, and contract boundaries no longer align, pause scope expansion and route the file to qualified tax and legal review before taking on more work.
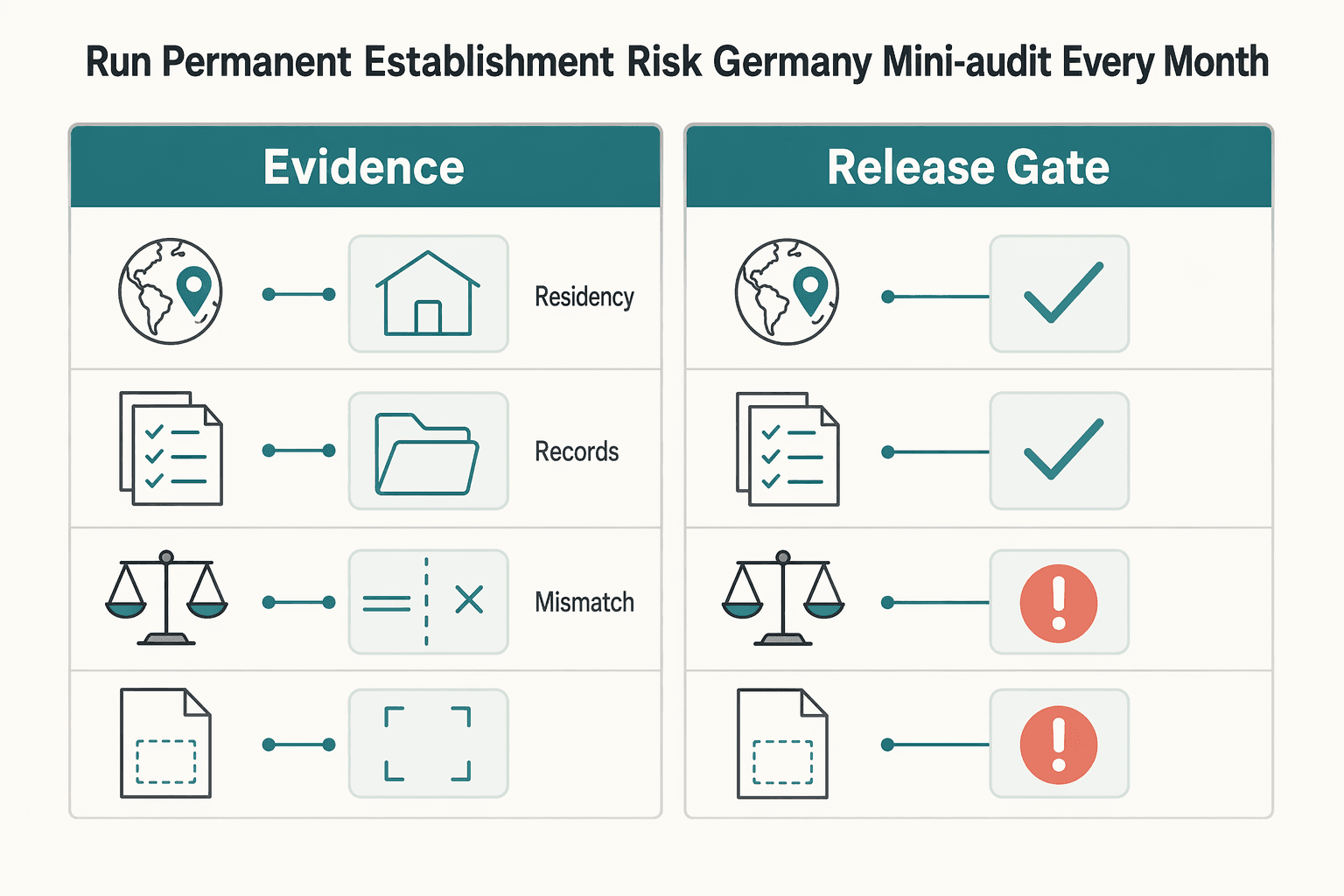
Treat this mini-audit as an internal risk-control process, not a legal determination of German permanent-establishment status. When you rely on legal source text, verify it against an official legal edition before treating it as authoritative.
Review the active MSA and current SOW against only the last month of activity. Focus on whether your documents, communications, and delivery behavior still tell the same story.
| Check | Evidence | Mismatch signal | Immediate containment action |
|---|---|---|---|
| Workspace | Calendar entries, visitor logs, site-access records, short purpose note for each on-site block | Germany presence is becoming regular, open-ended, or not tied to a defined task | Reset on-site work to dated task blocks and document business purpose in writing |
| Authority flow | Approval emails, signature paths, one live thread showing final client approval | You are giving final approvals, committing scope, or being treated as the client approver | Route approval back to the named client owner and retain the rerouted thread |
| Delivery behavior | Current deliverables, invoices, meeting notes, change requests, client-facing messages | Work appears embedded, undefined, or broader than signed scope | Stop the new workstream until documented through change control or declined |
Workspace: confirm where work happened and why. Save at least one support item per work block so the month does not need reconstruction later.
Authority flow: compare your contract role with one recent approval chain. If authority drift appears, correct it the same day and keep the written handoff back to the client approver.
Delivery behavior: test whether your work still matches specialist support under the signed scope. If treaty assumptions are part of your file, use A Freelancer's Guide to the US-Germany Tax Treaty for internal prep, then confirm legal conclusions with qualified advisors before month-end. Then attach the evidence packet to the permanent establishment risk mitigation checklist.
Related: A German Freelancer's Guide to Permanent Establishment Risk in the US. Turn your monthly PE mini-audit into a dated paper trail with the Tax Residency Tracker.
If facts changed since your last review, do not treat renewal as routine. For permanent establishment risk germany, run a pre-renewal gate in order. Align the MSA and SOW to the real work, verify approval flow, verify Germany footprint and compliance records, then decide whether to renew or pause.
The key check is MSA and SOW alignment, not generic contract language. If signed scope says specialist support but invoices, meetings, and change requests show embedded or undefined delivery, the file is already inconsistent. Renewal urgency can delay paperwork and lock that mismatch into the record.
Start with domestic-law screening based on current operating facts. Then run treaty analysis with A Freelancer's Guide to the US-Germany Tax Treaty. Do not assume a universal PE threshold: triggers can be unclear and differ by country, so verify any current threshold or rule before relying on it.
Use the OECD Model Tax Convention 2025 update, adopted 18 November 2025, as a treaty-analysis refresh checkpoint, not as binding German law. Avoid archived government pages for current-rule detail.
Pause scope expansion, route approvals back to the named client authority, and trigger advisor review before signing. This is where back taxes, penalties, and audit exposure can move from theoretical to practical.
Save one dated corrective note in the renewal file covering:
If you want a deeper dive, read Home Office Permanent Establishment Risk for Consultants in 2026.
Once you have the pre-renewal gate in place, run the same review loop every cycle. This is a file-discipline process, not a legal conclusion. Use the file in front of you to decide whether to continue, contain, or escalate without rebuilding facts from memory.
Treat this as a programmatic standard: keep a documented plan and run it the same way each cycle.
Keep it practical: one owner, one folder, and the same four checkpoints each time. The owner is accountable for completeness, not for personally generating every input. If one cycle depends on scattered inboxes, chat threads, and reconstructed calendars, the process will break under pressure.
| Checkpoint | Pass if | Fail if | Action |
|---|---|---|---|
| Contract position | Executed MSA, current SOW, and written changes still match live delivery, approval boundaries, and access terms | Scope expanded informally, approval lines blurred, or live work no longer fits signed documents | Pass: continue. Fail: contain by freezing undefined work and fixing the paper trail |
| Operating behavior | A recent approval chain shows final client signoff stayed with named client approvers, and your role presentation matches that record | You are effectively committing, approving, or presenting beyond what the file supports | Pass: continue. Fail: contain by routing approvals back to named client authority |
| Physical and access footprint | Each recent on-site block has date, purpose, calendar support, and one dated support item, for example an access record or invite | Presence appears open-ended or hard to tie to defined tasks | Pass: continue. Fail: contain by narrowing future visits and documenting purpose before the next trip |
| Record completeness | Another reviewer can follow what changed, when it changed, and which files support it | Dates are missing, versions conflict, attachments are out of order, or key periods depend on memory | Pass: continue. Fail: repair the file now, then escalate if core facts cannot be reconstructed |
A small process detail helps: number related attachments in sequence when one issue has multiple files. For example: 2026-03-12_visit_01_calendar, 02_access, 03_followup. That keeps the file reviewable by someone other than the person who assembled it.
If contract, behavior, and records align, keep your normal cadence. If one checkpoint fails, contain first and fix what you can. As an internal control, if two or more checkpoints diverge, or the same mismatch repeats across cycles, pause expansion and route the file to qualified legal or tax review before renewal, broader scope, or additional in-country activity.
If the file is clean but you still have treaty or permanent-establishment questions, escalate to qualified legal or tax counsel before making the next commitment.
One person should own completeness each cycle. That owner gathers the current MSA and SOW set, one recent approval example, footprint records, and dated change notes so decisions are based on one coherent file. Shared ownership can still work, but only if one named owner is accountable for final completeness.
Do not fill a missing month or visit from memory alone. Mark the gap, save what you do have, and state why the record is incomplete so the next reviewer sees the same risk picture. If the gap touches scope, approval authority, or on-site pattern, treat it as contain-or-escalate, not routine admin cleanup.
Escalate before renewal, before scope expansion, or when the same mismatch appears in more than one checkpoint. Clean documents do not offset behavior drift, and clean behavior is hard to defend with thin records. If pausing work creates cash-flow pressure, stabilize operations first. Then proceed after review with a plan that includes a basic buffer approach like How to Create a Financial Safety Net as a Freelancer.
If your renewal terms or on-site pattern changed this quarter, use contact Gruv to confirm operational coverage and controls before you expand scope.
One person should own completeness each cycle. That owner gathers the current MSA and SOW set, one recent approval example, footprint records, and dated change notes so decisions are based on one coherent file. Shared ownership can still work, but only if one named owner is accountable for final completeness.
Do not fill a missing month or visit from memory alone. Mark the gap, save what you do have, and state why the record is incomplete so the next reviewer sees the same risk picture. If the gap touches scope, approval authority, or on-site pattern, treat it as contain-or-escalate, not routine admin cleanup.
Escalate before renewal, before scope expansion, or when the same mismatch appears in more than one checkpoint. Clean documents do not offset behavior drift, and clean behavior is hard to defend with thin records. If pausing work creates cash-flow pressure, stabilize operations first. Then proceed after review with a plan that includes a basic buffer approach like How to Create a Financial Safety Net as a Freelancer. If your renewal terms or on-site pattern changed this quarter, use contact Gruv to confirm operational coverage and controls before you expand scope.
A financial planning specialist focusing on the unique challenges faced by US citizens abroad. Ben's articles provide actionable advice on everything from FBAR and FATCA compliance to retirement planning for expats.
With a Ph.D. in Economics and over 15 years of experience in cross-border tax advisory, Alistair specializes in demystifying cross-border tax law for independent professionals. He focuses on risk mitigation and long-term financial planning.
Educational content only. Not legal, tax, or financial advice.

With digital nomad taxes, the first move is not optimization. It is figuring out where you may be taxable, where filings may be required, and what proof supports that position.

Your **freelance financial safety net** is more than a savings balance. It is the set of controls that lets you cover fixed obligations on time when receipts are uneven, and it keeps invoiced revenue separate from cash you can actually spend. The goal is not to predict every slow month. The goal is to reduce the chance that one late client payment turns into missed bills, tax pressure, or borrowing.

---