
Draft your msa for indian it outsourcing around enforceability, not template habit: include explicit IP assignment terms, tie invoices to accepted deliverables, and use dispute language you can execute across borders. The article highlights CPC Section 13 and Section 44A limits for foreign judgments and frames arbitration structure as a practical route when seat, rules, and interim-relief wording are clear. Keep core protections in the MSA, then run delivery details through each SOW.
If you reuse a local vendor template, you are probably leaving real gaps. A defensible msa for indian it outsourcing must account for Indian ownership defaults, India-specific enforcement mechanics, contract certainty rules, and cross-border privacy exposure.
Under Section 17 of India's Copyright Act, the author is the first owner of copyright unless an exception applies or the contract says otherwise. The employment exception refers to work created under a contract of service, so do not assume a vendor relationship gives you automatic ownership.
That is where generic templates break down. Broad work-for-hire wording, or language that assumes payment alone transfers rights, may not be enough without explicit assignment language. The practical risk is simple: you pay, ship, and still end up arguing over code, documentation, models, or integrations at handover or exit.
Foreign judgments can be conclusive in India under CPC Section 13, but only subject to statutory exceptions. Direct execution under Section 44A depends on whether the country is a reciprocating territory notified by India's Central Government. The Section 44A decree route also excludes arbitral awards.
That makes a generic "home court only" clause weaker than it looks. The risk is not losing on paper. It is winning on paper and then fighting again to enforce. Cross-border arbitration can be a practical option because New York Convention awards are recognized and enforced through local procedure. India's arbitration statute also includes a New York Convention enforcement chapter. Pick a neutral seat and rules based on enforceability, not habit.
Section 29 of the Indian Contract Act treats uncertain agreements as void. So vague scope language is not just inconvenient. It can undermine enforceability.
This is another place where standard templates usually underperform. Phrases like "industry standard," "timely," or "as requested" do not give you objective specs, milestones, dependencies, acceptance tests, or change control. The result is predictable. You get scope creep, acceptance disputes, and weaker breach arguments because the expected outcome was never pinned down.
The DPDP Act, 2023 (Act 22 of 2023, dated 11th August, 2023) includes a territorial hook in Section 3 text. It can reach processing outside India when connected to offering goods or services to people in India. That does not replace your home-jurisdiction duties.
A generic "comply with applicable law" clause is too thin for that setup. In practice, it leaves teams operating on different compliance assumptions, incident response obligations half-defined, and post-incident disputes much more expensive than they need to be. Keep verified thresholds and effective dates current where relevant, including any home-law thresholds you rely on.
| Generic MSA wording pattern | India-ready contract intent | Practical downside if missing |
|---|---|---|
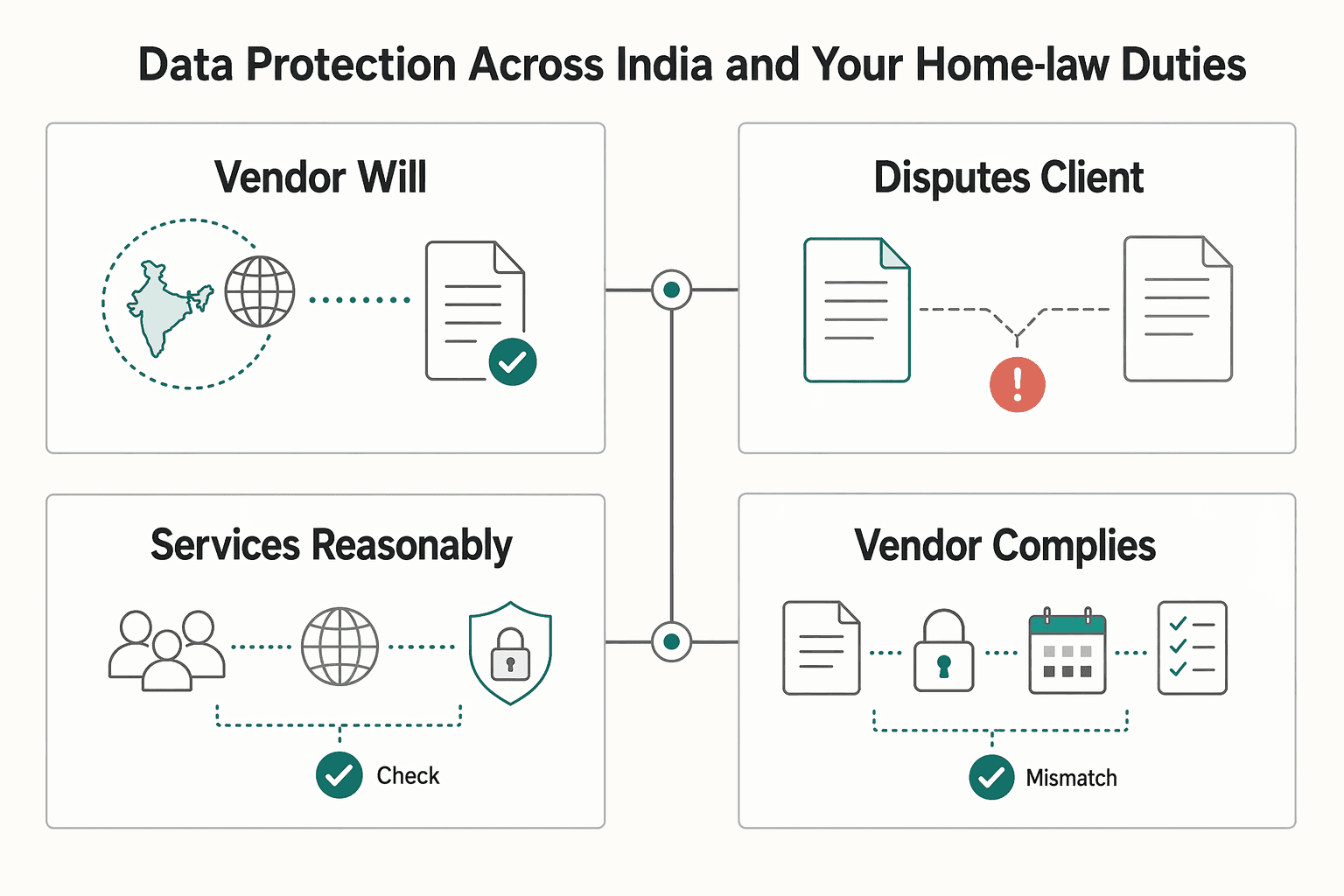
| "Vendor will create deliverables for client" | Express assignment covering all deliverable categories across MSA + SOWs | Ownership disputes after payment or at exit |
| "Disputes go to client's courts" | Forum design tied to verifiable India-side enforceability; arbitration structured for cross-border award recognition where appropriate | Costly second-stage enforcement fight |
| "Services as reasonably requested" | Defined scope, milestones, dependencies, acceptance criteria, and change control | Scope creep and weak breach position |
| "Vendor complies with applicable privacy law" | India obligations plus home-jurisdiction obligations, roles, security, incident notice, subprocessors, and exit data handling | Compliance gaps and post-incident finger-pointing |
Fix these clauses before you negotiate price:
Those fixes do more than clean up drafting. They set up practical controls that protect both your IP and your cash.
For a step-by-step walkthrough, see A Guide to TDS (Tax Deducted at Source) for Payments to Indian Freelancers.
Before you sign, get three controls in writing: party ownership and obligations, payment release mechanics, and confidentiality handling. If any of them stays vague, the MSA starts acting like a pricing sheet instead of a risk-control document.
The first checkpoint is basic but often missed. Confirm which legal entity is actually bound at each contract level. The MSA sets the framework, but work is often placed through a Service Agreement. Subsidiaries are not automatically bound unless they expressly join.
| Check | Requirement |
|---|---|
| Contracting Party | Name the client and supplier Contracting Party in each Service Agreement |
| Affiliate or subsidiary | State whether any affiliate or subsidiary is also a party; if yes, require it to sign |
| MSA vs Service Agreement | Mark which obligations apply at MSA level versus Service Agreement level |
| No local Service Agreement | Confirm what happens if a local Service Agreement is not in effect, including which parent entities remain obligated |
Local service agreements may be modified for local law or commercial custom, so do not assume obligations carry over unchanged.
Verify: the entity doing the work is the same Contracting Party, or the Service Agreement expressly binds the delivery entity. Red flag: a parent signs, an affiliate delivers, and the affiliate never accepts the key obligations.
Keep payment release mechanics explicit in each Service Agreement. Treat acceptance language as something you confirm in your own template and legal review. For scope and prioritization changes, require written updates before they flow into billing.
| Payment control | Contract mechanics to require | Failure exposure if missing | Best-fit use case |
|---|---|---|---|
| Scope changes | Written change process aligned to service scope terms | Extra charges can appear without clear scope history | Projects with evolving requirements |
| Priority changes | Written work-prioritization process before reprioritized work is billed | Schedule and cost shifts are harder to challenge later | Multi-workstream delivery |
| Acceptance trigger (if used) | Clear acceptance criteria and review flow in the Service Agreement | Payment disputes increase when acceptance language is vague | Deliverable-based engagements |
Use the section checkpoints as a contract-quality test. If your draft lacks mechanisms comparable to 3.4 Services Variable in Scope and Volume and 3.5 Work Prioritization, scope and billing changes become much harder to control. Set the acceptance review window in the Service Agreement, then fill the exact business-day number only after internal verification.
Verify: every billed change can be tied to the written scope or prioritization process in the Service Agreement. Red flag: billing references "requested changes" or "priority shifts" with no signed written record.
Confidentiality should operate like a handling rule, not a short NDA paragraph. A dedicated clause structure, similar in function to 3.12 Protection of ACI Information, works better because it makes the handling model explicit.
Make the operating limits explicit:
If your policy requires deletion certification or incident-notice timing, keep those thresholds pending official verification until the exact values are confirmed.
Verify: identify the people, repositories, cloud environments, and subcontractors that will handle your information before signing. Red flag: shared accounts, unnamed subcontractors, or no return or deletion duty at exit.
Once ownership and payment are under control, performance has to be enforceable too. Your SLA should do four jobs: define done, define measurement, define communication rules, and define remedies when performance misses.
Do not leave completion to opinion. Put acceptance criteria and the acceptance procedure inside each SOW, alongside scope, timing, and price. For each deliverable, use pass-or-fail language:
| Acceptance item | SOW detail |
|---|---|
| Artifact | Deliverable artifact |
| Specification or standard | Required specification or standard |
| Test method | Test method |
| Evidence | Evidence required |
| Approver | Your approver |
| Acceptance window | Acceptance window |
If a deliverable fails, require rework at no extra charge and resubmission within the verified business-day threshold. If you want deemed acceptance after silence, say so explicitly. If you do not, avoid wording that implies silence equals acceptance.
Keep the operating sequence simple. The vendor submits, you test against the SOW criteria, and acceptance happens only when the deliverable conforms to the quality and quantity requirements. That trigger should control payment release and the start of warranty or support periods.
Verify: every deliverable has a named approver, evidence requirement, and written accept-or-reject path. Red flag: "industry standard," "high quality," or "best efforts" with no objective test.
SLA packs often fail because they measure too much and prove too little. Track a small set of commitments that affect continuity, delivery reliability, and intervention speed. Then tie each one to evidence you can review independently.
| Metric category | What to measure | Evidence source | Fallback remedy |
|---|---|---|---|
| Availability for hosted/managed services | Monthly Uptime Percentage, downtime minutes, agreed exclusions, target threshold pending official verification | Monitoring logs, incident records, uptime exports | Service credit percentage pending official verification, claimed under contract procedure |
| Incident handling | Acknowledgment time, update cadence, restoration target by severity, each threshold pending official verification | Ticket timestamps, email records, phone or console logs | Credit on affected services, root cause report, corrective action plan |
| Delivery performance | Milestone delivery on SOW date and acceptance result (first pass or after rework) | Milestone tracker, repo tag, test results, acceptance notice | Rework at vendor cost; milestone payment withheld until acceptance |
| Communication and handoff | Response time in defined business hours, handoff completeness across time zones, blocker escalation | Shared ticketing data, timestamped messages, handoff notes | Escalation to management; repeated misses count toward cure or termination triggers |
Keep placeholders until thresholds are verified. Unverified numbers create false certainty and weaken enforcement.
Informal updates are not enough in a cross-border delivery model. Put the operating controls in the contract text:
For time-zone handoffs, require an end-of-day written update for open critical items. It should cover current status, last action, next owner, blocker, and the next expected update window pending official verification.
If your engagement touches a regulated Indian financial entity, these controls can matter even more. RBI's 2023 outsourcing direction includes monitoring, control, and cross-border outsourcing chapters, and some NBFC agreements must align at renewal or by April 10, 2026, whichever is earlier. Treat that as a sector-specific compliance signal, not a universal rule for all private deals.
Verify: run a mock escalation before signing using real contacts and channels. Red flag: one chat group, one project manager, and no backup incident path.
Do not let service credits swallow every other remedy. Credits are useful for measurable misses, but some templates make them the sole and exclusive remedy unless you preserve other rights. If you need payment protection, termination rights, or other claims, say so directly.
Add a cure-notice mechanism with a defined cure window. A common reference point is 10 days or more, but set the window based on service risk. Then connect uncured or repeated SLA breaches to explicit termination rights in the SOW and, where relevant, the MSA.
Use penalty language carefully. Under Section 74 of the Indian Contract Act, recovery tied to a named amount is framed as reasonable compensation up to that amount, not automatic penalty payout. The stronger structure is usually this: credits for measurable service misses, rework for failed deliverables, cure notice for nonperformance, and termination for uncured or repeated breach.
Finally, define the credit-claim mechanics. Some SLAs require requests within 30 days or by the second billing cycle after the incident, with supporting logs. State who submits claims, what evidence is required, and whether credits are automatic or notice-based.
Before you lock acceptance criteria, map each deliverable and dependency into a project-ready statement of work.
A workable exit clause should do three things: let you exit, require an orderly handover, and make disputes more predictable. Here, termination and dispute terms are not boilerplate. They are control points.
The clause should answer these points in plain language:
If the vendor resists convenience termination, reduce your exposure somewhere else by shortening the term, narrowing scope, or limiting prepayment. If you cannot tell in one read what you owe when you exit, the clause is still too vague.
Termination without a handover plan can leave you exposed. Require a transition plan that is executable and time-bound, with any unresolved deadlines kept pending official verification.
| Handover item | Vendor obligation |
|---|---|
| Access | Revoke access you specify, including user, admin, API, repo, cloud, VPN, and shared tools |
| Client-owned assets | Return or transfer client-owned assets, including code, artifacts, credentials, project files, and ticket history |
| Operating documentation | Deliver current operating documentation, including environment details, dependencies, deployment steps, and known issues |
| Transition cooperation | Provide transition cooperation, including handoff meetings, Q&A, and export support |
| Retained copies | Confirm deletion or destruction of retained copies, except legally required retention, in writing |
Also attach an exit inventory so the return obligation is concrete. One practical failure pattern is partial handover: code is delivered, but keys, admin rights, or current runbooks are not.
For cross-border disputes, define the mechanics up front: forum, seat, governing law, language, and the interim-relief pathway. If arbitration is selected, state which court can grant urgent relief while arbitration is pending.
| Dispute route | Enforceability risk | Speed | Cost burden | Practical control |
|---|---|---|---|---|
| Home-court litigation | Jurisdiction-specific; verify recognition and enforcement steps before relying on this route | Depends on court timelines | Can involve added cross-border coordination costs | Familiar process for you, but outcomes still depend on where counterparties and assets are |
| India-court litigation | Jurisdiction-specific; treat enforceability details as a legal-review item | Depends on court timelines | Local counsel and coordination can add burden | Closer to counterparty operations; process may be less familiar for you |
| Neutral arbitration | Not automatic; depends on clause quality and applicable law | Can be structured in contract, but timing still varies | Forum or tribunal fees plus counsel costs | More procedural control when drafting is tight |
Final checkpoint: run a legal carve-out check on any pre-dispute arbitration clause. Some laws can void pre-dispute arbitration for specific claim types, and mandatory arbitration can remove jury-trial access in covered cases. Also decide deliberately on transparency tradeoffs, since forced arbitration can reduce public accountability.
We covered this in detail in How an Indemnification Clause in an MSA Can Create Unlimited Liability.
Use your MSA to lock core risk terms once, then run each project through SOW-level details. If IP rights, payment terms, SLAs, dispute handling, and contracting-entity coverage are not explicit, you are still operating on assumptions.
A good final check is to map each control point to the risk it prevents:
In practice, the cleaner structure is two documents. Put durable risk terms in the Master Services Agreement (MSA). Put project-specific scope, delivery, and pricing in each Statement of Work (SOW) or Service Agreement, if that is your contract structure.
| Generic template mindset | Intentional India-ready MSA mindset |
|---|---|
| One template tries to do everything | MSA holds durable risk terms; SOW handles project specifics |
| Scope, pricing, and legal protections are mixed together | Scope and pricing can change without silently changing core protections |
| Operational controls stay in email threads | QA, billing, reporting, and service rules are documented in contract documents or manuals |
| Assumes related entities are covered automatically | Confirms the exact contracting entity, affiliate, or subsidiary that is actually bound |
Before your next outsourcing engagement, review your current template against these five control points and flag any clause gaps for legal review. Related: How to Write a Master Service Agreement (MSA) for Long-Term Client Engagements.
Once your MSA is signed, make sure execution follows those contract controls too.
You should not assume payment gives you ownership. In India, the author is the first owner by default, so your contract needs a written, signed assignment that identifies the work and specifies the rights, duration, and territory. In practice, require a full assignment chain from the vendor and all personnel who create the work, address residual moral-rights risk in contract language to the extent permitted, define pre-existing IP and related license scope, and require disclosure of open-source or third-party components plus an SBOM (or equivalent) at acceptance and handover.
Choose the enforcement path deliberately, because litigation and arbitration are not interchangeable in cross-border disputes. If you rely on court judgments, treat enforcement in India as conditional and run a Section 13 and Section 44A check, including reciprocating-territory status and exceptions. If you rely on arbitration, enforcement is still not automatic, refusal grounds are limited under the foreign-award route, and you can still preserve court interim relief under Section 9 before or during arbitration and after the award before enforcement. For governing law, venue, seat, institution, and rule version, keep each choice pending counsel review until the dispute clause is finalized.
The useful SLAs are the ones you can measure, verify, and enforce without argument. Define each service level, the measurement evidence, the owner of verification, and the acceptance window, then state exactly what happens on a miss. Remedy mechanics should cover rework, service credits or charge deductions, escalation, and repeated-failure termination triggers.
Tie payment to accepted deliverables, not effort alone. Set acceptance criteria first, identify who approves, define rejection and cure mechanics, and make invoices payable only for accepted work. A 30-day-after-acceptance timeline can work as a drafting benchmark, but it is not a default legal rule. Also assign responsibility for withholding tax, indirect tax, bank charges, and currency conversion so invoice shortfalls do not become a recurring dispute.
Keep durable risk controls in the MSA and project-specific execution terms in each SOW. Use a clear order-of-precedence rule so a rushed SOW cannot silently override core protections. If you want a project document to change a core protection, require explicit amendment language and signatures from both parties. | Put this in the MSA | Put this in the SOW | |---|---| | IP assignment chain, confidentiality, data security baseline, liability limits, indemnities, governing law, dispute method, notice, termination, audit or records duties | Scope, deliverables, milestones, timeline, staffing assumptions, acceptance tests, SLA targets, fees, invoicing schedule, dependencies, project contacts |
An international business lawyer by trade, Elena breaks down the complexities of freelance contracts, corporate structures, and international liability. Her goal is to empower freelancers with the legal knowledge to operate confidently.
Priya is an attorney specializing in international contract law for independent contractors. She ensures that the legal advice provided is accurate, actionable, and up-to-date with current regulations.
Educational content only. Not legal, tax, or financial advice.

Choose your track before you collect documents. That first decision determines what your file needs to prove and which label should appear everywhere: `Freiberufler` for liberal-profession services, or `Selbständiger/Gewerbetreibender` for business and trade activity.

If you expect repeat work with the same client, set the contract architecture first: one reusable MSA for standing terms, then project documents for each engagement. The point is not just speed. It is making sure your baseline terms are set before they repeat across future projects. Treat each document as a separate layer:

Treat this article as a pre-send gate, not background reading. Use CASL as the baseline. If you are in Canada, or you send a Commercial Electronic Message to Canadian residents, the message is in scope. The same applies when a CEM is sent from or to computers or devices in Canada. This material treats messages routed only through Canadian systems as not subject to CASL, so flag those for separate review before you send.