
Start by treating your sow for mobile app development as an execution control document, not a template. Define in-scope outcomes, list exclusions, and require written change approvals before extra work begins. Connect billing to objective evidence and a documented acceptance process with pass/fail checks. For cross-border deals, lock currency, payment rail, fee allocation, and required invoice fields in writing. Then close legal gaps by stating IP transfer timing, retained materials, governing law, venue, and dispute path across the full agreement set.
A strong SOW for mobile app development protects your margin, reduces legal ambiguity, and shows the client you run a controlled project. For an experienced freelance developer, technical skill is table stakes. What usually separates a high-value consultant from a replaceable pair of hands is the structure of the engagement, and the Statement of Work sits at the center of it.
This guide breaks the job into three layers: financial control, legal protection, and delivery authority.
In app projects, margin often leaks in four places: vague scope, weak billing triggers, sloppy cross-border payment language, and subjective sign-off. Fix those in writing before kickoff. Once the build starts, small asks and payment friction get expensive fast.
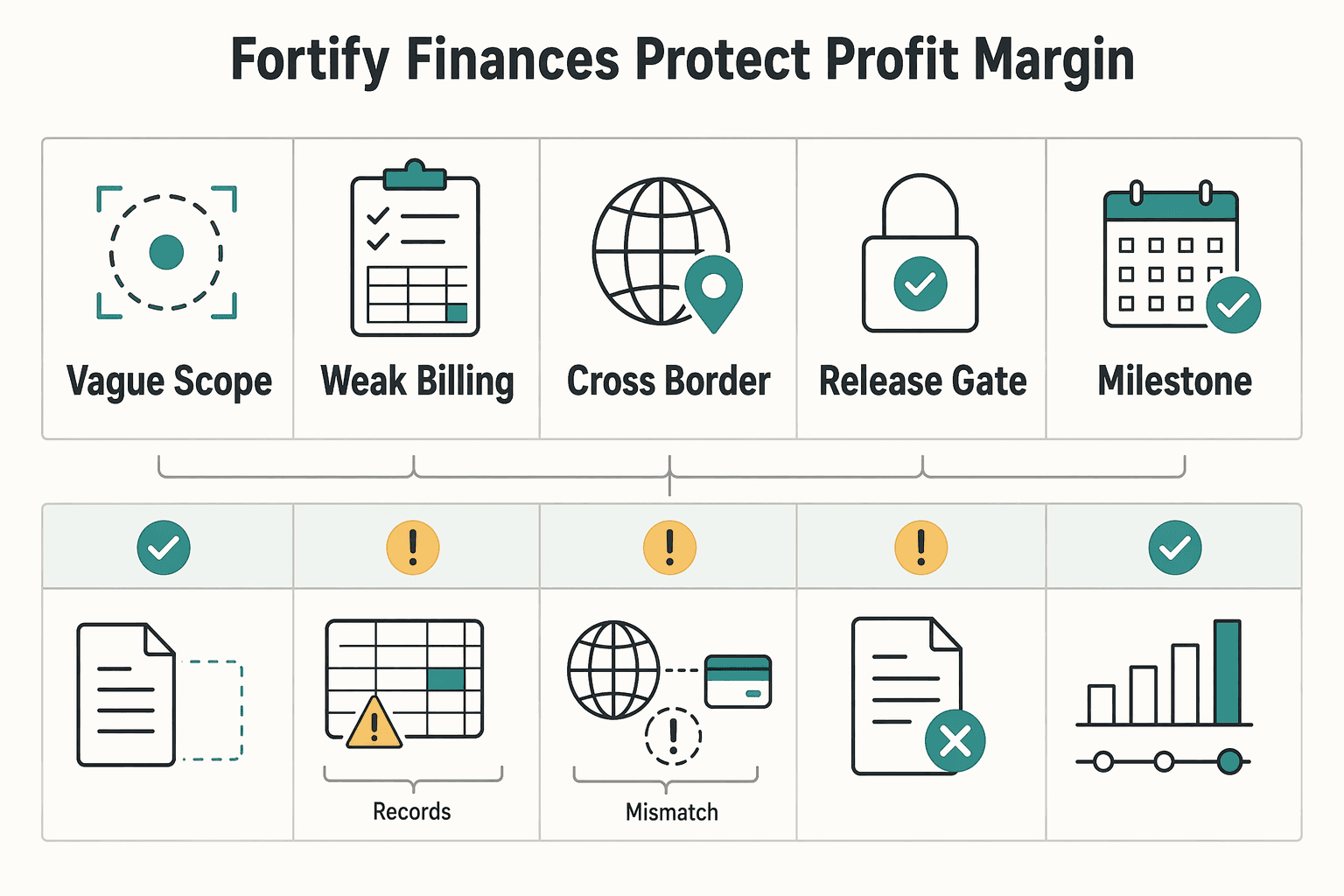
| Margin leak | What to define | Article rule |
|---|---|---|
| Vague scope | In-scope deliverables, out-of-scope items, dependency assumptions, and a change-order path | If a request cannot be traced back to an included deliverable or an assumption you already priced, treat it as a change |
| Weak billing triggers | Payment events tied to accepted deliverables with a dated artifact | If you cannot evidence the trigger, you may face friction from procurement or finance |
| Cross-border payment language | Invoice currency, payment rail, transfer charges, FX handling, and required invoice data | State who bears intermediary, conversion, and receiving-bank costs |
| Subjective sign-off | Test environment, pass/fail conditions, revision boundaries, and sign-off trigger | Require written acceptance or a written defect list tied to the stated pass/fail criteria before payment is held back |
1. Define scope by results, then fence it in. Write the work as required results, not your internal method. Each in-scope deliverable should name the outcome the client is buying, the platform or feature covered, and the handoff artifact you will provide. Right below that, add an explicit out-of-scope list. A good SOW says not only what the work is, but what it is not.
Keep the structure simple: in-scope deliverables, out-of-scope items, dependency assumptions, and a change-order path. Dependency assumptions should be explicit. If your timeline depends on client-supplied API docs, design assets, test accounts, app store access, or stakeholder feedback within a stated review window, say so. A useful checkpoint is this: if a request cannot be traced back to an included deliverable or an assumption you already priced, treat it as a change.
For changes, require a written request. Then respond with a revised price and timeline, and start only after a bilateral written modification is approved by both parties. That is a reliable way to reprice work without arguing later about whether a Slack message changed the deal. A quick extra can turn into unpaid QA, device support, or backend coordination you never scoped.
2. Choose a payment model that matches delivery risk. Do not pick billing terms by habit. Pick the model that keeps your cash flow aligned with uncertainty, and tie payment events to accepted deliverables wherever possible.
| Payment model | Main risk | Cash flow impact | Best fit |
|---|---|---|---|
| Milestone | Disputes if milestones are vague or acceptance is subjective | Good if milestones are frequent and evidence-based | Fixed-scope builds with clear design, build, and release stages |
| Retainer | Client may expect unlimited pull on your time unless capacity is capped | Smoother monthly cash flow when capacity and scope are defined | Ongoing product support, iterative roadmap work, bug fixing |
| Hybrid | More drafting effort up front | Balanced: predictable base plus progress billing | Projects with defined core scope but uncertain integrations or post-launch support |
A good verification point is whether you can prove each invoice trigger with a dated artifact: approved wireframes, a testable build, a signed acceptance note, or a monthly service log. If you cannot evidence the trigger, you may face friction from procurement or finance.
3. Lock down cross-border payment mechanics. If your client is abroad, name the invoice currency, the payment rail, who pays transfer charges, how FX is handled, and what invoice data is required. Do not stop at "USD by bank transfer."
If you are billing in euro within the SEPA Credit Transfer scheme, that rail applies across 41 SEPA scheme countries. It supports full-original-amount transfers, and each party is charged by its own payment service provider. If you are billing large, time-critical USD amounts, Fedwire is designed for immediate, final, irrevocable settlement once processed.
Outside those cases, do not rely on assumptions. Rail and corridor details can affect whether the full invoice amount arrives and how fees are applied. Your contract language should say who bears intermediary, conversion, and receiving-bank costs, with any bank-specific wording marked for confirmation. If EU VAT invoicing rules apply to your B2B invoice, include at least the issue date and a unique sequential invoice number. Confirm any required VAT identifiers or tax wording in the signed agreement or with counsel before using that invoice language.
4. Make acceptance objective enough that payment release is mechanical. Acceptance is the client's acknowledgment that the deliverable meets the contract's quality and quantity requirements. The contract can define the timing. Your acceptance section should read like a test script, not a promise of general satisfaction. Use this checklist for each major deliverable:
Use these clause controls in your SOW, then customize the exact terms before signing:
For a related example, read How to Write a Scope of Work for a Web Development Project. If you want a quick next step, try the SOW generator.
You reduce legal risk in this layer by replacing implied assumptions with explicit contract controls. In practice, your SOW should clearly state ownership, dispute structure, and confidentiality/compliance duties across the full agreement set.
Before you draft, assemble the full document stack in one place: master agreement, Statement of Work (Exhibit A), proposal, NDA, payment exhibit, and any Data Processing Agreement. Contracts often pull outside documents into scope by incorporation language, so you need one version-controlled set before you finalize terms.
Do not rely on shorthand like "client owns the app." In your SOW, state each item directly: what transfers, what you retain, when transfer happens, and how pre-existing or reusable materials are licensed. Then map those terms to named deliverables in Exhibit A so a reviewer can trace ownership line by line.
| IP model | Project type fit | Reuse risk to you | Negotiation friction |
|---|---|---|---|
| Full assignment | Custom build with client expectation of broad ownership | Higher if transfer language is broad | Usually lower |
| License-first | Work that depends on your reusable assets or existing components | Lower if license scope is precise | Often higher |
| Hybrid | Custom deliverables plus retained reusable components | Medium, depending on drafting clarity | Medium |
These are commercial drafting patterns, not default legal rules. Pick deliberately, then verify enforceability in your jurisdiction.
Treat these as separate controls in the SOW:
| Control | What it answers | Term to confirm |
|---|---|---|
| Governing law | Which law applies | Confirm the governing law in the signed agreement |
| Forum/venue | Where a dispute is filed | Confirm the court, arbitration seat, or forum in the signed agreement |
| Dispute path | Negotiation, mediation, arbitration, court, or staged sequence | Confirm the dispute process with counsel before use |
Spell these terms out instead of leaving them implied: governing law, forum or venue, and dispute path all need to be confirmed in the signed agreement or by counsel before use. Then check precedence across all incorporated documents so one exhibit does not quietly override the dispute process you intended.
Your clause should answer five practical questions: what data is confidential, what use is allowed, how it must be handled, whether subcontractors may access it, and how long obligations survive after termination, with the survival period confirmed in the signed agreement or by counsel before use. If personal or regulated data is in scope, reference the relevant DPA or security exhibit directly instead of leaving it implied.
Keep this test in mind: can you track who accessed information, where records and invoices are stored, and who owns close-out actions? That is the difference between manageable compliance and late-stage surprises from terms you did not scope or price.
Once legal terms are set, authority shows up in execution control. In your SOW, that means written accountability for who decides, how changes are approved, what gets tested, and what counts as done.
Do not stop at "regular updates." Your SOW should map who gets what information, when they get it, and which channel is valid for each message type.
Use a clear operating map that names owners and channels before work starts:
Use one practical test: could a third party reconstruct project decisions from the record? If not, you do not have traceability.
Treat the SOW as a runbook, not a file you archive after signature.
| Kickoff item | What to do | Record or output |
|---|---|---|
| Scope confirmation | Confirm in-scope deliverables and delivery timing against Exhibit A or the deliverables schedule | Exhibit A or deliverables schedule |
| Dependency handoff | List what the client must furnish versus what you provide | Credentials, assets, access, copy, designs, approvals |
| Day-one risk register | Open a risk register with owner, impact, status, and next action | Risk register |
| Meeting cadence | Set meeting cadence and reporting method, including who attends each checkpoint | Cadence and reporting plan |
| Late-input handling | If required inputs miss the agreed deadline, log the dependency block, document timeline impact, and send written notice in the approved channel | Written notice in the approved channel |
| Change approval | Route any scope, timeline, or cost impact through written change approval; if you use a formal modification, get both sides to sign | Written change approval or signed modification |
Run kickoff in this order:
Your QA model is credible only when each phase names responsibility, sign-off evidence, and defect-versus-request triage. Put acceptance criteria and pass/fail criteria in the SOW so sign-off is tied to evidence, not impressions.
| Phase | Primary responsibility | Evidence required for sign-off | Triage rule |
|---|---|---|---|
| Developer QA | Developer | Build/version, test notes, device/environment list, pass/fail results against acceptance criteria | Requirement failures are defects; added behavior goes to feature request log |
| Client UAT | Client, with developer support | Client issue log with reproduction steps and supporting screenshots/video where relevant, plus written review against agreed criteria | Failures against stated requirements remain in scope as defects; new functionality is a separate request |
| Fix verification | Developer | Confirmation testing results and regression notes for affected areas | Only verified defect fixes move forward; enhancement requests stay outside the remediation batch |
| Final acceptance | Client | Written approval in approved channel naming build/version, date, approver, and deferred items | Unmet acceptance criteria block acceptance; deferred enhancements are documented for a later phase |
Before signature, check three authority signals:
This is how premium positioning is earned: clients can follow the work, verify decisions, and accept outcomes without guesswork.
You might also find this useful: A Guide to the Statement of Work (SOW) for a SaaS Development Project.
Before you send the draft, tighten it around what you can control: predictable cash flow, clear legal terms, and credible delivery decisions.
Before you send it, confirm these five controls:
Run one final pre-signature pass against your template and remove every unresolved marker or editor note. The value comes from execution discipline: document decisions, keep approval trails, and enforce the same terms consistently.
For a step-by-step walkthrough, see How to Perform User Acceptance Testing (UAT) for a Mobile App.
The highest-value parts are the ones that prevent disagreement: scope boundaries, acceptance criteria, payment triggers, and change control. Those are the terms that usually protect delivery clarity and reduce project friction. In practice, include a deliverables list, an explicit out-of-scope list, clear acceptance criteria, invoice trigger dates, and a written change approval rule.
Define what is included and what is not, then give new requests a path instead of turning them into a fight. A vague or incomplete SOW is what usually creates disputes, schedule problems, and scope creep. Include out-of-scope items, a change request section, who can approve changes, and a rule that added work starts only after written approval on price and timeline.
Tie payment to objective events you can prove, not to loose promises like “when the client is happy.” If the project is phased, match invoices to named milestones or acceptance of a specific deliverable. Your SOW should state the currency, payment method, invoice trigger, due date, tax responsibility, and any late-fee wording, with late-payment terms confirmed in the signed agreement or by counsel before use.
Do not leave dispute handling implied, especially if you work cross-border. The right choice depends on the deal, but the document should clearly state the governing law and where disputes will be handled. Include a clause naming the governing law, jurisdiction or venue, and any escalation steps you want before formal proceedings.
Include execution specifics, standards, responsibilities, and quality checkpoints. For a mobile app, that usually means defining the app scope, key integrations, who provides required access, and how quality will be monitored. Avoid unsupported version cutoffs or policy-deadline claims unless verified.
Yes. Assumptions protect you when timing or quality depends on client inputs you do not control. They also give you a clean checkpoint when a dependency blocks progress. Put in assumptions for assets, approvals, credentials, API access, legal review, and response times, plus the effect of missed assumptions on schedule and price.
Do not assume the answer is obvious. Default ownership rules are not universal, so your document should separate pre-existing materials from the final project deliverables. Define “pre-existing materials,” state who owns them, spell out what rights the client gets to use them, and state when ownership of final deliverables transfers.
Use a written acceptance process tied to agreed criteria, and keep a clear record of what was accepted. Then define the rule clearly: if the app fails a stated requirement, treat it as a defect; if it asks for behavior not in the agreed scope, treat it as a new request. Your SOW should name the acceptance criteria, approver name or role, what record will be kept, and a defect-versus-enhancement triage rule.
A career software developer and AI consultant, Kenji writes about the cutting edge of technology for freelancers. He explores new tools, in-demand skills, and the future of independent work in tech.
Priya is an attorney specializing in international contract law for independent contractors. She ensures that the legal advice provided is accurate, actionable, and up-to-date with current regulations.
Educational content only. Not legal, tax, or financial advice.

Choose your track before you collect documents. That first decision determines what your file needs to prove and which label should appear everywhere: `Freiberufler` for liberal-profession services, or `Selbständiger/Gewerbetreibender` for business and trade activity.

Use your SOW as a pre-work control document, not a project diary. Before work starts, make sure the key project documents describe the same deliverables, responsibilities, and timing.

Move fast, but do not produce records on instinct. If you need to **respond to a subpoena for business records**, your immediate job is to control deadlines, preserve records, and make any later production defensible.