
Start by structuring your README in execution order: purpose and boundaries first, then onboarding, then contribution and handoff guidance. For how to write a good readme, include explicit in-scope and out-of-scope lines, required environment variable names without secret values, and a single verification checkpoint a new reader can run. Add links to `CONTRIBUTING.md`, `CODEOWNERS`, and your decision log so requests and reviews do not depend on side conversations.
A strategic README does three jobs: it defines boundaries, guides a first run, and preserves decision context. If it only lists commands, it leaves out the parts that actually reduce friction. If you are working out how to write a good readme, start by deciding what a new reader should understand without asking you in chat.
| Pillar | Add now | Defer until it becomes real | What to verify |
|---|---|---|---|
| Boundaries | State what the repo does, current scope boundaries, key assumptions, owner or maintainer, license or private-use terms, and where change requests go | Detailed process docs, long FAQ, edge-case policy | A reader can tell whether a request belongs here or needs a separate approval path |
| Onboarding | List prerequisites, required environment variable names, run steps, one success check, common failure notes, and links to CONTRIBUTING.md or deeper docs | Full troubleshooting matrix, environment-specific variants for every platform | Someone on a clean machine can get to a first successful run without secret values or Slack help |
| Professionalism | Add business context, support route, CODEOWNERS or review ownership, and a link to ADR-style decision notes | Full architecture narrative, historical changelog, broad governance docs | A new maintainer can explain not just what to change, but why earlier choices were made |
Start by drawing the repository's edges in plain English. A short opening should answer five things quickly:
This does not need legal prose, but it does need clarity. One short paragraph on purpose followed by a tight checklist is usually enough. If the repo is private client work, state that project-specific ownership and reuse wording must be verified against the contract, counsel note, or approved project record before use. Do not imply a universal private-use template, because that wording is project-specific.
Be explicit about rights. If you publish code without a license, copyright restrictions still apply. If a repository later changes to private visibility, existing copies that were already forked or cloned can still exist, so ownership and use terms still matter in handoff notes. A common failure mode is a vague line like "internal use only" with no owner, no maintainer, and no path for new requests.
Use this checkpoint: can a new reader classify a feature request as in scope, out of scope, or needing change approval without asking you? If not, your boundaries are still too soft.
Write onboarding as a sequence you can test, not as notes from memory. Include prerequisites, required tools, environment variable names, run steps, and one clear verification step. That can be as simple as "server starts and health route responds" or "test suite completes." Never put secret values in examples or hardcode a secret.
| Item | Add | Note |
|---|---|---|
| Prerequisites | List prerequisites | Test the steps on a clean machine or container |
| Required tools | List required tools | If setup only works because you already have unstated tools installed, the instructions are not done |
| Environment variable names | List the variable names without values | Note where the real secrets are managed |
| Run steps | Write onboarding as a sequence you can test | Not as notes from memory |
| Verification step | Add one clear verification step | "server starts and health route responds" or "test suite completes" |
| Common failure notes | Add one or two common failure notes | Missing database migrations, the wrong runtime version, or a background service that must be running first |
This is where many READMEs break down: they say "copy .env" but do not name the variables, or they assume local state you forgot you had. List the variable names without values, note where the real secrets are managed, and add one or two common failure notes. Good examples are missing database migrations, the wrong runtime version, or a background service that must be running first.
Link outward when a deeper document is the better home. CONTRIBUTING.md is where pull request expectations belong, and GitHub surfaces that file when someone opens an issue or PR. A SUPPORT file is also worth using if you want a clear help route instead of ad hoc issues.
What matters most here is verification, not completeness. Test the steps on a clean machine or container. If setup only works because you already have local credentials, cached packages, or unstated tools installed, the instructions are not done.
This is what makes a repo feel professional instead of merely usable. Add two short pieces of context near the top: why the project exists from a business point of view, and where major technical decisions are recorded. An ADR-style note is enough. It only needs the decision, context, and consequences.
Then make ownership visible. If review responsibility matters, say so in the README and back it with CODEOWNERS. GitHub can automatically request those reviewers when matching files change, and repository admins can require approvals before merge. That turns "ask the right person" from tribal knowledge into a repository control.
Handoff is the real test. A new maintainer should be able to answer three questions after ten minutes of reading. What this repo is for. How to run it. Why the odd-looking choices were made. If those answers still live in your chat history, the file is not finished.
You reduce non-billable back-and-forth when your README stays current on the few details people need to self-serve. Maintain only the facts that change often, and make each one easy to verify before you publish updates.
Keep a short "current release facts" checklist and publish each release-specific line only after it has been verified against the repository's approved release source.
| Release line | Update rule | Check |
|---|---|---|
| Current artifact name | Verify against the approved release source before use | Matches what the repository currently shows |
| Current release marker | Verify against the approved release source before use | Use MAJOR.MINOR.PATCH format if your project follows it |
| Current release asset creation date | Verify against the approved release source before use | Matches what the repository currently shows |
Current release or CHANGELOG link | Verify against the approved release source before use | Matches what the repository currently shows |
Your pass/fail check is simple: each release-specific line in the README matches what the repository currently shows.
Write onboarding in execution order so a new reader can run it without asking you for missing context.
If setup depends on local state, call that out directly so the reader knows what to verify before retrying.
Make role-specific next steps explicit so each stakeholder can complete one concrete task and confirm they are done.
| Role | Primary task | Completion signal |
|---|---|---|
| Builder | Follow onboarding and run the project | The documented success check passes |
| Reviewer | Use CONTRIBUTING.md, CODEOWNERS, and required review policy during review | PR meets the documented checklist and required approvals |
| Business owner | Use support and request-routing paths | Can route a request without reading code |
Then keep the operating links owned.
| Link or doc | What it helps someone do | Who updates it | Refresh when |
|---|---|---|---|
| Latest release / artifact link | Find the current downloadable build | Maintainer or release owner | A new release asset is published |
CHANGELOG or release notes | Confirm what changed | Maintainer | A release is cut |
SUPPORT.md | Route help requests correctly | Project owner or maintainer | Support channel changes |
CONTRIBUTING.md | Standardize issue and PR quality | Maintainer | Submission rules or templates change |
You might also find this useful: The Best Tools for Building a Knowledge Base.
For a private repo, write your README for the exact client team using it, not anonymous contributors. Your opening should tell each stakeholder what the project is, who owns decisions, and where to start without a side conversation.
Step 1 Write an opening block for known stakeholders. Make the first block scannable and role-specific:
README files are often the first thing a visitor sees, so this block should answer what the project does, why it matters, and how to get started.
Step 2 Use a responsibility matrix, not just a contact list. A short governance table is easier to maintain and clearer in handoffs.
| Area | Decision owner | Approver | Escalation path | Channel | RACI (optional) |
|---|---|---|---|---|---|
| Delivery changes | Verify owner from the governance record | Verify approver from the governance record | Verify escalation path from the approved source | Verify channel from the approved source | Use RACI only if the project maintains it |
| Access requests | Verify owner from the governance record | Verify approver from the governance record | Verify escalation path from the approved source | Verify channel from the approved source | Use RACI only if the project maintains it |
| Production changes | Verify owner from the governance record | Verify approver from the governance record | Verify escalation path from the approved source | Verify channel from the approved source | Use RACI only if the project maintains it |
Then align this with CODEOWNERS and branch protection settings. If an owned path changes, CODEOWNERS should route review, and protected branches should enforce review gates before merge. In personal-account private repos, GitHub permission levels are only owner and collaborators, so your README should still state approval authority explicitly.
Step 3 Document access paths, never secret values. Your access section should make onboarding and audits easier without exposing credentials.
Use least-privilege language so access planning is specific to role and task, not broad by default.
Step 4 Keep a lightweight ADR-style decision log. Add a one-hop link near the codebase and use a minimal entry format: date, decision, context, options considered, chosen option, consequence, owner. Add an entry when you change approval rules, introduce a new environment, or choose between real alternatives, so future handoffs do not depend on chat history.
Use your README to make boundaries explicit before work starts. Under delivery pressure, the same warning signs keep showing up: tighter deadlines, half-finished features, and bugs that keep moving. A README will not enforce a contract by itself, but it gives you a repeatable first check when requests and pull requests arrive.
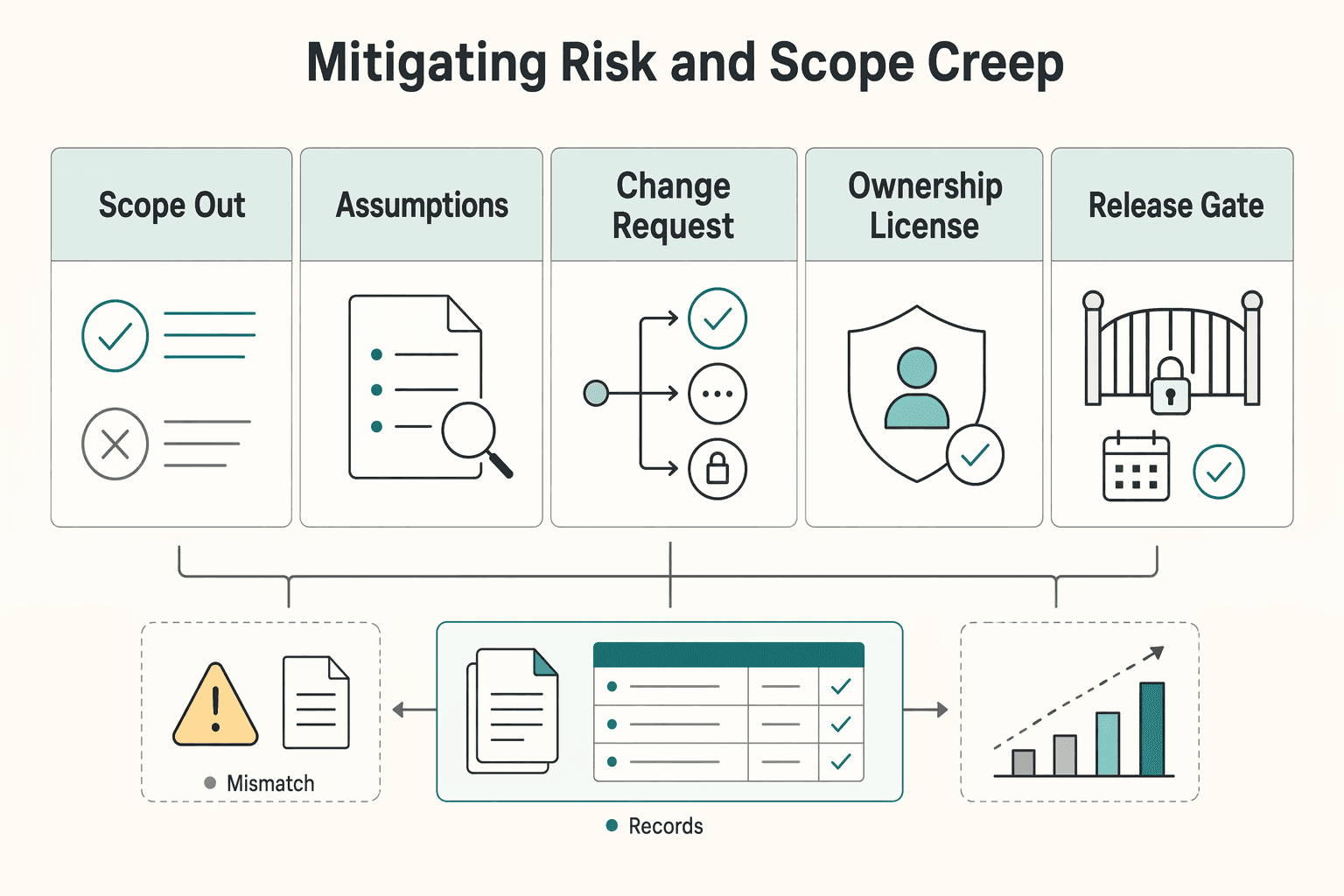
| If your README is missing | Your exposure | Add this control now |
|---|---|---|
| In-scope and out-of-scope lines | Extra asks are treated like included work | Add a short boundary block near the top |
| Assumptions | People plan against unstated conditions | List the conditions your estimate and delivery depend on |
| Change-request path | Work starts in chat with no approval trail | State one intake route and one approval checkpoint |
| Ownership, license, and reuse split | Deliverables and reuse rights get blurred together | Separate them into three labeled notes |
| Contribution rules and review gates | Merge decisions happen with inconsistent expectations | Align CONTRIBUTING.md, PR template prompts, CODEOWNERS, and protected-branch rules |
Step 1: Run the same intake flow every time. Keep scope controls high in the README, not buried below setup commands. Use the same four labels every time: In scope, Out of scope, Assumptions, and Change-request path. Add one enforceable rule: Do not start out-of-scope work before written approval. Then make approval auditable in one line: where the request is filed, who approves it, and where approval is recorded.
Step 2: Separate ownership, license grant, and reuse rights. Do not collapse these into one vague ownership sentence. State: who owns project-specific deliverables, what license applies to repository contents, and what reuse rights apply to your pre-existing components only when those details are verified. If language is not verified, say the exact wording must come from the governing agreement, LICENSE file, counsel note, or approved project record before use.
Step 3: Check that README rules match repo behavior. Compare your written process with what the repository shows in practice. In GitHub's latest commit area, a merged entry like "Merge pull request #42" is a concrete change-control artifact you can audit against your stated review path. If your README requires review but the visible history does not reflect that path, fix the mismatch first.
Step 4: Treat contribution governance as merge control. Use CONTRIBUTING.md to define how work is opened and what a merge-ready PR must include. Use the PR template to request the evidence you expect. Keep CODEOWNERS current so review requests route to the right owners, and keep protected-branch requirements aligned with the process you describe. When these controls drift apart, your README stops being operational and becomes advisory only.
Treat your README as an operating artifact, not a file header. If a new reader cannot understand the project, complete first-time setup, and figure out how to contribute without side messages, your README is adding friction.
Make the first screen answer three questions fast: what this repo is, how it is organized, and what to do next. Include a concise repository description, a short project organization section, and clear next actions such as setup, testing, deployment notes, and contribution guidance.
For private client repos, write this for real roles, not a generic audience: the builder starting setup, the reviewer checking expectations, and the next maintainer handling handoff. Point to governance docs such as CONTRIBUTING.md and CODEOWNERS, and state where to route new requests or blockers in your repo workflow.
Use outcomes, not opinions.
| Signal | Weak README | Strong README | Verify in your repo |
|---|---|---|---|
| Onboarding readiness | Setup depends on memory, chat history, or teammate tips | Setup, dependencies, and testing steps are current, ordered, and runnable | Ask a new reader to run setup and confirm the expected verification step without help |
| Handoff quality | Context lives in meetings or private messages | Repository description and organization explain purpose, structure, and next docs | Ask a new maintainer to summarize the project and identify the next document to read |
| Request triage clarity | New requests start in discussion loops | Collaboration expectations and request-routing guidance are explicit | Give a borderline request and see whether someone can route it from the README alone |
| Repeat support load | The same setup questions keep returning | Common failure points and escalation path are documented | Compare recent repeat questions against what the README already answers |
Start where interruptions are highest. If onboarding breaks, tighten setup, dependencies, testing procedures, and the exact verification step. If handoffs are weak, improve the repository description and project organization. If request handling is messy, make collaboration expectations and routing guidance easier to find near the top.
| Gap | Fix first | Check |
|---|---|---|
| Onboarding breaks | Tighten setup, dependencies, testing procedures, and the exact verification step | A new person can get oriented and verify setup without teammate memory filling gaps |
| Handoffs are weak | Improve the repository description and project organization | Ask a new maintainer to summarize the project and identify the next document to read |
| Request handling is messy | Make collaboration expectations and routing guidance easier to find near the top | Someone can route a new request or blocker without waiting for chat clarification |
Use this mini-checklist to prioritize now:
Use the README for orientation, not for hidden process notes. In a private repo, only people you explicitly share access with can see it, so put the project purpose, setup basics, boundary block, and contact or approval path there. Keep repo-specific instructions in the README, move contributor behavior into CONTRIBUTING.md, and never paste credentials, because committed secrets are a known risk.
Use the README to classify requests before work starts, not to approve change by itself. If something falls outside your in-scope, out-of-scope, or assumptions lines, route it to the named change-request path and stop there until written approval exists. Keep the boundary block in the README, then put pull request expectations in CONTRIBUTING.md, where GitHub surfaces them during issue and PR creation.
There is no single universal section, so optimize the first screen for fast decisions. When a stakeholder is checking risk or asking what happens next, a common need is purpose, current status, scope boundaries, and the approval path near the top. Put that in the README and push implementation detail lower or into separate docs. | If the reader needs | Put it in | | --- | --- | | Quick project summary and current boundaries | README | | Contribution and PR rules | CONTRIBUTING.md | | Version-by-version change history | CHANGELOG.md or release notes |
Keep legal text narrow and verified. If a LICENSE file applies, point to it. If ownership, reuse rights, or disclaimers are still being checked, say the exact wording must be verified from the license file, governing agreement, counsel note, or approved project record before use. Put only confirmed references in the README, and keep any real legal wording in a counsel-reviewed clause.
Do not turn the README into a full release history. If readers need notable changes by version, keep a CHANGELOG.md or GitHub release notes and link to it from the README. That also keeps the README readable and avoids GitHub truncation beyond 500 KiB. Use the README for the current state, not every historical detail.
Keep badges only if they come from real automated checks and you will maintain them. They help when internal readers need a quick pass or fail signal, but a stale or manually curated badge is noise. Verify each badge by clicking through to the live workflow, and remember that badges from private repositories are not accessible externally.
A career software developer and AI consultant, Kenji writes about the cutting edge of technology for freelancers. He explores new tools, in-demand skills, and the future of independent work in tech.
Includes 8 external sources outside the trusted-domain allowlist.
Educational content only. Not legal, tax, or financial advice.

Value-based pricing works when you and the client can name the business result before kickoff and agree on how progress will be judged. If that link is weak, use a tighter model first. This is not about defending one pricing philosophy over another. It is about avoiding surprises by keeping pricing, scope, delivery, and payment aligned from day one.

If you want ROI to help you decide what to keep, fix, or pause, stop treating it like a one-off formula. You need a repeatable habit you trust because the stakes are practical. Cash flow, calendar capacity, and client quality all sit downstream of these numbers.

You want fewer repeated questions, fewer handoff errors, and answers people can find fast without digging through chat, email, or memory. That usually starts with one searchable home for shared knowledge, but it only sticks if someone owns the content and someone checks that it still reflects reality.