
Yes: to protect trade secrets when employee leaves, treat protection as a documented system, not a label. Use the DTSA-style test (nonpublic, commercially valuable because secret, and guarded by reasonable measures), then run a fixed exit order: cut communications access, remove tool permissions, collect return/deletion confirmations, and archive evidence. If you cannot show contracts, access limits, and revocation records, enforcement gets weaker even when the information is sensitive.
If you want to protect trade secrets when someone leaves, start with a blunt rule. Information is protected only if it is nonpublic, valuable because it stays secret, and something you actually kept under control. General skill, public information, and experience honestly gained doing the work are often portable, subject to any confidentiality duties.
Use this short test before you label anything a trade secret. Under the U.S. Defend Trade Secrets Act, trade secrets can include business, technical, financial, and code-related information. That only holds when secrecy and value are real and you took reasonable measures to protect it. WIPO and the EU use the same core idea: limited access, commercial value from secrecy, and active protection.
Use this question set before you label anything a trade secret:
A practical warning: the EU Directive from 8 June 2016 protects trade secrets. It also says trade secret rules should not block an employee's honestly acquired experience and skills. You can take your judgment and craft with you. You cannot assume that lets you walk off with protected files, notes, or client data.
The hard part is usually not the obvious cases. It is the middle ground, where your experience overlaps with someone else's protected material.
| Departure item | Default call | Why |
|---|---|---|
| Your client list with private contacts, buying history, and strategic notes | Protect | Customer information and strategy material can qualify if nonpublic and access was limited. |
| A public prospect list you built from websites and directories | Can use | If it is generally known or readily ascertainable, do not treat it as secret. |
| Your internal pricing logic or margin model kept in restricted files | Protect | Pricing methods, plans, and formulas can qualify when secrecy gives value. |
| A generic workflow template built from your own experience, with no client data | Can use | General know-how and methods are not automatically restricted, unless protected material is embedded. |
| Code or scripts you wrote for a client under a confidentiality duty | Needs permission | Using another party's secret without consent can be misappropriation. |
| Email threads, Slack exports, meeting notes, or communication history from a client project | Needs permission | They often contain nonpublic business information obtained under a secrecy duty. |
| A copied internal playbook from a former employer or client | Needs permission | Even if you know the approach, the actual document may still be protected. |
Verification checkpoint: If you cannot explain in one sentence why an item lands in one column, freeze use until you review the contract and how you obtained the material.
Labels do not help much without proof. Keep a small evidence pack for anything you mark Protect:
A common failure mode is calling something secret only after a dispute starts, even though it lived in shared drives, open chat channels, or personal devices with no restrictions. Once you know what counts, the next step is operational: lock access, collect materials, and document the exit cleanly. You might also find this useful: A Guide to the Defend Trade Secrets Act (DTSA). Want a quick next step on the contract side? Try the SOW generator.
If you might ever need to enforce confidentiality, your protocol starts before the first login. Trade-secret protection depends on secrecy practices you can demonstrate, not labels alone. Your contract terms, access settings, and offboarding steps should work as one system.
Set the controls first, then grant access.
| Data tier | Access rule |
|---|---|
| Critical client data | Named owners and tightly limited access |
| Internal playbooks | Only to people who need the specific material |
| General ops files | Broader access only where necessary |
Use three tiers across every folder, inbox, and tool: critical client data, internal playbooks, and general ops files. Keep critical client data with named owners and tightly limited access. Give internal playbooks only to people who need the specific material. Keep general ops access broader only where necessary. If you cannot classify an item, do not grant access to it.
Your agreement should cover confidentiality, IP assignment, and return or destruction of materials. Then convert those clauses into operating rules: what tools are approved, which data is in scope, whether downloads are allowed, whether personal email or personal cloud use is prohibited, who approves expanded access, and which duties continue after the engagement. Post-engagement duties should be explicit: stop use, return company-controlled materials, confirm deletion where return is not possible, and continue confidentiality. For ownership language, see Work for Hire vs. Assignment of Rights: A Freelancer's Guide to Owning Your IP.
Use the lower-risk model by default. You do not need perfect lockdown, but you do need reasonable secrecy controls and a clear record of who got access, what changed, and when it was removed.
| Tool | High-risk access model | Safe access model | What you log |
|---|---|---|---|
| Full access to your primary inbox | Delegated or role-based access limited to required folders | Date granted, scope, date removed | |
| Cloud docs | Whole-drive sharing | Folder-level access limited to the project/client | Shared folders, permission changes, removal confirmation |
| Password vaults | Sharing master or reusable credentials | Item-level access without exposing underlying passwords when possible | Items shared, recipient, revocation record |
| Project systems | Full workspace visibility | Project-by-project membership with least access needed | Added users, scope, admin changes, deactivation |
Red flags: combining confidential client material with general admin spaces, or allowing personal-device or personal-cloud forwarding "for speed." Data exfiltration often starts there.
Do not improvise offboarding. Run the same sequence each time and keep proof.
| Exit step | What you do | Evidence to keep | Owner |
|---|---|---|---|
| Trigger | Record end/termination event | End notice or internal record | You or engagement owner |
| Access shutdown | Remove access across systems in sequence | Admin logs, screenshots, timestamps | Tool owner |
| Return or deletion | Request return and deletion confirmation | Written confirmation | Engagement owner |
| Final file | Archive all artifacts together | Notice, confirmations, access records | You |
Use calm, clear handover language so the relationship stays intact: "Thanks for your help on this project. Please upload final deliverables to the project folder, confirm you no longer retain copies outside approved tools, and reply confirming return or deletion of confidential materials under our agreement." Keep offboarding open until both access-removal records and written return/deletion confirmation are complete. If sensitive files were handled like ordinary files during the engagement, enforcement gets harder later. For a broader checklist, see How to Offboard an Employee from a Remote Company.
Before final delivery, run one exit checklist: confirm what the client owns, what you can still use, and what you must not reuse or disclose. Your goal is simple: a clean handoff, clear boundaries, and a record you can prove later.
Gather the contract, SOW, amendments, and any written change approvals in one folder. Read IP terms first. If ownership depends on copyright assignment, confirm there is a signed writing (17 U.S.C. § 204). If the contract says "work made for hire," confirm that treatment is expressly agreed in a signed written instrument for commissioned work.
Then label each asset as: client-owned deliverable, your pre-existing material, or unresolved. If anything is unclear, pause and resolve it in writing before sending finals. For ownership mechanics, use Work for Hire vs. Assignment of Rights: A Freelancer's Guide to Owning Your IP.
Do a quick triage before closeout. Broad language is where post-exit disputes usually start, and noncompete enforceability is jurisdiction-sensitive.
| Clause area | Red-flag wording | Safe next action |
|---|---|---|
| IP assignment | "All ideas, know-how, methods, and materials related in any way to the project are assigned" | Request a written carveout for your pre-existing materials, tools, and general know-how |
| Work made for hire | "Everything created is work made for hire" with no signed-writing clarity | Ask whether the clause is work-for-hire, assignment, or both, and confirm in writing |
| Confidentiality | "You may not use any information learned during the project for any purpose" | Separate true confidential assets from general skill and experience before reuse |
| Noncompete | "You may not work for any competing business anywhere" | Escalate for legal review before you rely on enforceability |
| Regulator reporting limits | "You may not report issues to any regulator without approval" | Treat as legal-review language; confidentiality terms cannot impede direct reporting to SEC staff |
Also check whether DTSA whistleblower notice appears. Contractors and consultants are within scope under 18 U.S.C. § 1833(b)(4), and missing notice can limit certain remedies. That is a contract-quality signal, not permission to disclose client secrets.
Keep a private log with two columns: portable know-how and client-confidential assets.
In portable know-how, list your general skills, methods, and process lessons. In client-confidential assets, list unreleased materials, internal strategy, pricing, customer data, drafts, credentials, and other information that had value because it stayed secret. Use this record to filter proposals, samples, and sales calls.
Use three buckets: public, client-approved, confidential.
If public: link to the public version and describe your role. If client-approved: keep the written approval and any limits (what, when, format). If confidential: do not publish yet.
Permission script: "I'd like to reference this project in my portfolio. I will only use publicly available material or excerpts you approve in writing. Please confirm what I may show, if anything, and when." Do not assume redaction alone makes publication safe.
Complete closeout in order: return or transfer deliverables, handle deletion or retention per contract and any legal-hold or compliance duties, revoke your remaining access, then archive confirmations. Offboarding is not complete if you still have active credentials, synced files, or vault access.
Keep an evidence file: handoff email, deletion or return confirmations, access-revocation records, and final closeout note. If a dispute appears later, this record carries more weight than memory. For a broader offboarding checklist, see How to Offboard an Employee from a Remote Company.
The point is control, not just peace of mind. If you want to protect trade secrets when someone leaves, whether that is an employee or a contractor, your edge comes from documented habits that show you took reasonable measures to keep important information secret.
Use the Fortress Inbound Protocol when you hire help. That means signed confidentiality terms before access, need-to-know sharing, clear confidential markings, and return duties with ongoing protection obligations at the end. If your contracts are governed by U.S. trade secret practice, check one detail people often miss: agreements covering confidential use should include the Defend Trade Secrets Act immunity notice under 18 U.S.C. § 1833, and that notice applies to contractors and consultants too. Missing it can limit remedies later.
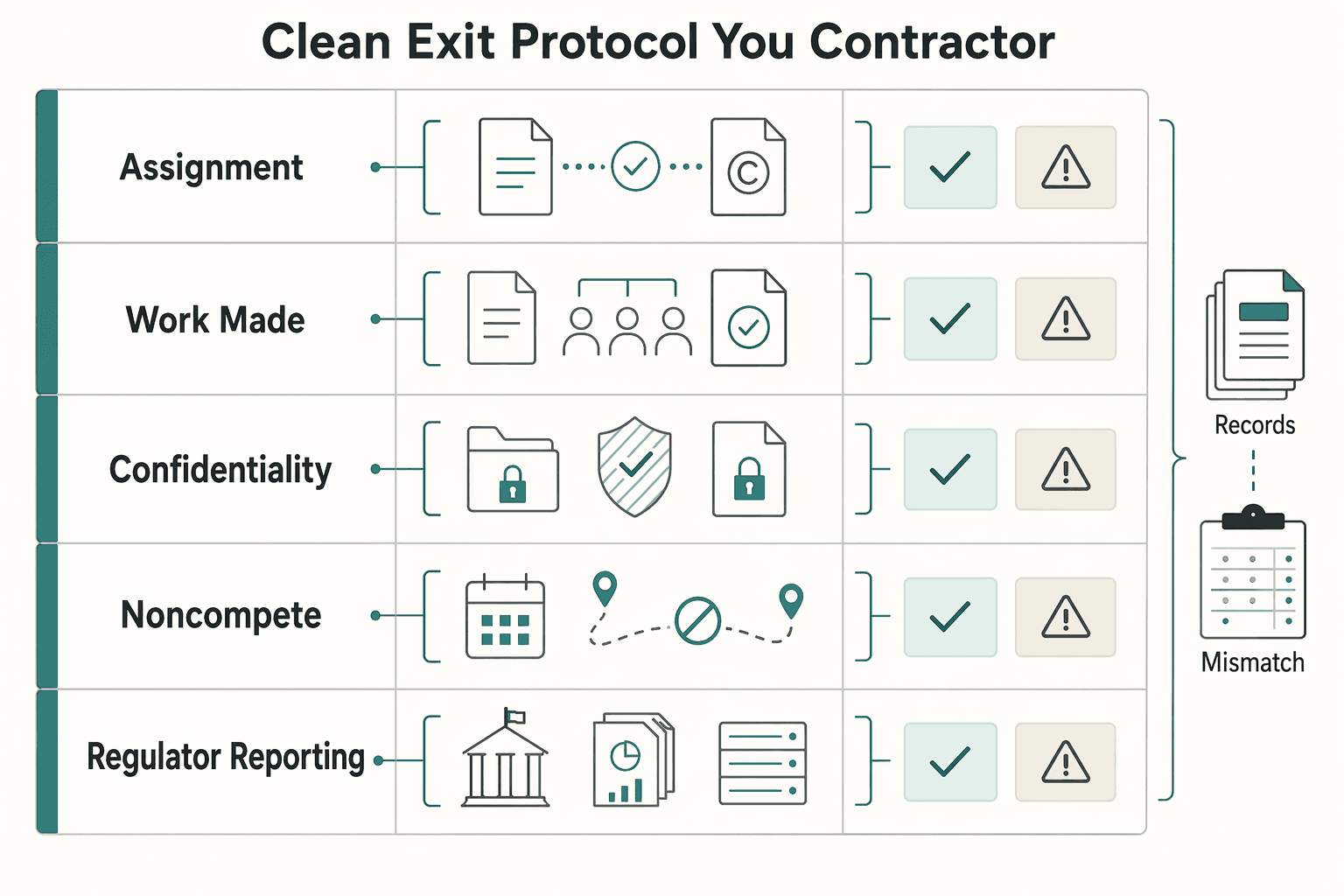
Use the Clean Exit Protocol when you leave client work or when someone leaves yours. Revoke credentials at termination or role change, retrieve company property, and create a written record of what was returned or retained with permission. Your checkpoint is simple: you should be able to produce the signed agreement, the access list, the revocation record, and the exit confirmation without rebuilding the story from memory. A common failure mode is informal trust: broad access during the project, then no evidence pack when there is a dispute about consent or reuse.
Keep four things current:
Do this next: update your template agreement, make a one-page access list, save an offboarding checklist beside each contract, and require written permission before reusing client material. That is how you keep your independence backed by proof, not assumption. Related: How to Offboard an Employee from a Remote Company.
Start with the inbound controls from Part 1 before access is granted. Get a signed agreement in place, limit information on a need-to-know basis, and mark confidential files clearly. If you give broad access without those basics, a court may be less willing later to treat the material as confidential. Keep the signed agreement and a simple access list showing who got access to what.
It should define what you treat as confidential, confirm that the duty applies during and after the engagement, and tie that duty to how confidential information is handled at exit. If you are unsure how the clause applies in your jurisdiction, verify before relying on it. Keep the latest signed NDA or confidentiality agreement in the same folder as the contract.
Use the confidentiality agreement as your default rule. If material is nonpublic or confidential, do not share it unless the client gives written permission. If the contract is restrictive or unclear, ask first instead of guessing, and keep written permission that states exactly what you may show and when.
Move fast on containment, then document before you argue. Note which files, accounts, devices, or storage locations may be involved. A strong next step is a thorough exit interview covering company devices, personal devices, cloud storage, thumb drives, external drives, and paper copies where confidential material may still exist. Keep an access log and a written exit-interview record.
A trade secret is confidential information that creates business advantage because it is not publicly known. Your general skill is the know-how you carry from project to project. If the value comes from secrecy and you protect it with need-to-know limits, secure storage, confidentiality markings, and anti-copying controls, treat it as protected business information. Keep a two-column record listing portable know-how on one side and client-confidential assets on the other.
Treat physical return and digital cleanup as one exit task, not two separate chores. You want confirmation that equipment came back and that confidential information is not still sitting on a laptop, phone, tablet, home computer, cloud account, external drive, or in paper form. Keep a return confirmation, plus written confirmation of where company material still exists and its deletion or retention status.
An international business lawyer by trade, Elena breaks down the complexities of freelance contracts, corporate structures, and international liability. Her goal is to empower freelancers with the legal knowledge to operate confidently.
Priya is an attorney specializing in international contract law for independent contractors. She ensures that the legal advice provided is accurate, actionable, and up-to-date with current regulations.
Educational content only. Not legal, tax, or financial advice.

A freelance agreement is not just about price and scope. It decides who controls the rights in the work. If the ownership language is loose, rights can move earlier than you expect, cutting down your control once the work is delivered or used.

Choose your track before you collect documents. That first decision determines what your file needs to prove and which label should appear everywhere: `Freiberufler` for liberal-profession services, or `Selbständiger/Gewerbetreibender` for business and trade activity.

**A common offboarding failure pattern is doing the right tasks in the wrong order.** Treat compliance as a hard sequence: classify the relationship, route the owner path, send written notice, and close only when the evidence file is complete.