
Use a paid discovery phase first when ownership mapping or AWS Cost Explorer visibility is incomplete, then quote the main engagement after evidence is verified. For a stable scope, fixed fee can work; for uncertain upside, use value-based or hybrid terms with limits. Keep software charges like Security Command Center or Audit Manager outside your labor line, and lock Statement of Work assumptions, Acceptance Criteria, and Milestone Invoicing before kickoff.
Price the decision the client needs to make, not the hours you expect to spend. A cloud infrastructure audit is not just a pass through cloud usage or a list of savings ideas. The client is paying for a decision-ready view of where budget is going, which resources are inefficient, and who owns the spend that needs to change.
That distinction matters. Cloud cost analysis means tracing spend down to the resource level and testing whether usage is efficient. In practice, waste often sits in unused instances, overprovisioned resources, and forgotten test environments. If your quote does not say whether you are identifying waste, mapping costs to teams or projects, or aligning spend to business goals, the client is buying a vague review rather than a clear outcome.
The hard part is not finding optimization advice. The hard part is turning audit uncertainty into a quote the client can approve and pay against.
A risk-first structure helps because it ties scope, deliverables, and payment terms to what is still unknown. Your first checkpoint is simple: verify what evidence exists before you offer a full scope. Usually that means confirming access to billing data, at least one reliable spend view, and some way to map costs to teams, projects, or owners. If ownership is fuzzy or cost allocation data is inconsistent, the estimate is not failing because you priced badly. It is failing because the input data is incomplete.
One failure mode is simple: you quote "audit and recommendations," then discover you are also cleaning data, untangling environments, and explaining why nobody can prove who owns a large share of the bill. That is where margin disappears and invoices stall. Put those uncertainty points into the Statement of Work (SOW) as assumptions, exclusions, and change triggers instead of absorbing them silently.
The goal here is practical. By the end, you should have a reusable pricing sequence, a stronger SOW, and fewer payment surprises after kickoff.
Use this rule early: if the client wants a hard number before access, ownership mapping, or basic billing evidence is available, sell discovery first. If the evidence is complete, accountability is visible, and the audit outcome is specific, you can quote the main engagement with more confidence.
That approach runs through the rest of this article. Build the quote around uncertainty you can name, artifacts the client can approve, and payment terms that protect both delivery margin and collection risk. Related reading: How to Price a Copywriting Project.
Do not price from a verbal brief. Price only after you confirm baseline evidence and deal controls, so you know whether the work is analysis, cleanup, or both.
Map the footprint first: AWS scope, any Google Cloud Audit Manager involvement, and whether the work touches SOC 2 evidence.
If compliance is in scope, confirm what audit readiness means in this environment: current evidence quality, resource visibility, and whether live resources match infrastructure-as-code definitions. Your output at this stage is a short scope note with accounts, environments, providers, and compliance obligations.
Request billing exports, shared AWS Cost Explorer views, and existing AWS cost allocation tags. Then test one practical checkpoint: can you see spend by service, account, and owner without manual detective work? If not, scope discovery first instead of forcing a fixed quote.
Log effort multipliers in plain language before pricing:
These gaps can turn a focused audit into a broad inventory exercise, especially when spend visibility is already weak.
Write the SOW shell before you set the fee. Include access assumptions, exclusions for remediation work, Acceptance Criteria tied to named deliverables, and Milestone Invoicing checkpoints.
If you cannot define those control points yet, treat that as a scope warning and keep the engagement in discovery until you can. For a step-by-step walkthrough, see How to Price a UI/UX Audit for a SaaS Company.
Price this as two purchases: your audit engagement and the client's software subscription. Keep advisory labor separate from tools like Security Command Center and Google Cloud Audit Manager, and do not roll subscription costs into your service fee.
Treat the audit as advisory work first. Audit Manager is a Google Cloud product, and Security Command Center is sold in three tiers (Standard, Premium, Enterprise). A client can buy your analysis, evidence review, and findings before they finalize a product tier.
Use one quick check before quoting software assumptions: is the tool already active, still being evaluated, or pending a sales conversation? If that is unclear, keep software pricing out of your labor fee.
| Line item | What drives price | How to show it |
|---|---|---|
| Audit engagement labor | Effort, scope depth, access quality, deliverables | Fixed fee or milestone-based advisory line |
| Platform subscription | Vendor tier, contract term, sales quote, possible indirect charges | Client-purchased assumption, not bundled labor |
| Optional implementation support | Remediation help after findings | Separate optional line or phase-two estimate |
Security Command Center charges are separate from other Google Cloud charges. Enterprise is a fixed-price subscription tier, with a minimum 12-month term, and higher-spend situations (for example above $15 million in annual spend or commitment) can require sales involvement. When totals depend on sales or negotiated terms, present software cost as an assumption, not a fixed line item in your fee.
Separate advisory labor, third-party subscriptions, and optional implementation support into distinct proposal sections. If Audit Manager is included at no additional cost for Security Command Center Enterprise customers, frame that as a dependency, not a guarantee. Your proposal should clearly show who buys each item and which costs can change outside your scope.
If you want a deeper dive, read How to Calculate Your Billable Rate as a Freelancer.
Before you choose fixed fee vs discovery, decide whether the scope is stable enough to estimate without guessing.
Start with AWS account count, environment sprawl, tag quality, and SOC 2 mapping depth. Account count alone is a weak predictor: a few clearly separated environments can be easier than fewer mixed accounts with unclear ownership.
Tag quality is the first hard gate. Cost allocation tags must be activated before they appear in Cost Explorer reporting, and AWS notes this can take up to 24 hours for keys to appear plus up to 24 hours to activate. Even then, tagged resources must incur charges before those tag-based costs appear. If tags were just turned on, treat scope as incomplete.
SOC 2 depth is another real driver. A SOC 2 examination covers controls tied to security, availability, processing integrity, confidentiality, or privacy. Light compliance references and control-level mapping are different scopes, and using the prebuilt SOC 2 framework in AWS Audit Manager still increases evidence and review work.
Use quick hygiene signals before pricing. AWS Trusted Advisor includes cost checks for idle load balancers and underutilized EBS volumes, which helps you see whether cleanup potential exists and whether visibility is good enough for fixed scope.
Storage is where estimates often drift. EBS volume storage is billed on provisioned GB until released, even if underused. Snapshot billing is separate, so charges can continue after volume cleanup. If snapshot archive is involved, account for the 90 day minimum archive period before implying near-term savings. Do not promise deletions or savings until dependencies are validated.
| Scope signal | Why effort changes | Verify before final pricing | Pricing move |
|---|---|---|---|
| Account count and environment sprawl | More cross-account analysis, exceptions, and owner follow-up | In Cost Explorer, confirm spend is visible by account and major environment | If visibility is fragmented, narrow scope or sell discovery |
| AWS cost allocation tags | Weak attribution slows every finding | In Cost Explorer, confirm relevant tags are activated and showing charges, not just created | If tags are recent or sparse, do not quote full fixed scope |
| EBS volumes, snapshots, load balancer hygiene | Cleanup opportunity rises, but dependency validation adds work | In Trusted Advisor, confirm idle load balancer and underutilized EBS checks are available; in Cost Explorer, confirm EBS-related spend is traceable | If signals are noisy, price analysis first and remediation separately |
| SOC 2 mapping depth | Control mapping adds evidence and documentation work | Confirm whether findings need brief references or control mapping tied to SOC 2 expectations | If mapping is required, add a separate compliance workstream |
If tagging is poor and access is partial, sell a paid discovery phase first. Make it explicit: baseline inventory, tag-readiness check, initial Cost Explorer cut, Trusted Advisor export, and a short memo on what can and cannot be priced yet.
If data is clean and access is complete, offer full fixed scope. Clean means you can validate attribution in Cost Explorer, review Trusted Advisor cost checks, and see enough account and environment structure to estimate effort confidently.
You might also find this useful: How to Price a Technical SEO Audit for an Enterprise Website.
Pick the model that matches uncertainty, not preference. If the client needs a hard cap and scope is stable, use Fixed-Fee Pricing. If upside may be meaningful but the baseline is still uncertain, use Value-Based Pricing with guardrails.
| Decision factor | Fixed-Fee Pricing | Value-Based Pricing |
|---|---|---|
| Project certainty | Scope, deliverables, and assumptions are already clear | Baseline waste and effort are still unclear |
| Audit depth | Primarily a defined findings report | Includes savings-oriented validation work |
| Client maturity | Team can support clean review boundaries and decisions | Team accepts shared-upside mechanics while uncertainty is resolved |
Use this if-then rule in plain language:
Protect downside in every model through the Statement of Work (SOW): define exclusions, dependency assumptions, and Change Order triggers before work starts. This matters most when hidden shared dependencies can change reliability risk and implementation effort after the audit begins.
Related: Value-Based Pricing for Strategic Consultants: A How-To Guide.
Build payment protection into the quote itself: state when payment is due, what the client is approving, and what happens if payment or inputs stall.
Use Milestone Invoicing instead of billing everything at the end. A practical sequence is kickoff deposit, midpoint delivery, and final payment at Acceptance Criteria sign-off. This ties cashflow to clear decisions, not vague progress updates.
| Milestone | Payment trigger | Artifact tied to payment |
|---|---|---|
| Kickoff deposit | Before work begins | Signed SOW, confirmed access list, project start date |
| Midpoint delivery | Submission of initial audit output | Baseline findings pack and prioritized savings backlog |
| Final payment | Client acceptance | Verified remediation list and final walkthrough against Acceptance Criteria |
If your contract setup allows it, require each milestone to be funded before that phase starts. For service work generally, examples like 50% upfront or above 25% are often used, but treat those as examples, not cloud-audit benchmarks.
Checkpoint: keep deliverables, dates, acceptance criteria, and payment schedule in one milestone table so payment triggers are explicit.
Tie payment release to submission and approval of specific artifacts, not elapsed time. For this audit scope, use the baseline findings pack, prioritized savings backlog, and verified remediation list as acceptance anchors.
Define what "accepted" means for each artifact and set a review window so payment does not sit in limbo. A 14-day review window is one concrete reference used in milestone workflows.
Add three written controls in the quote terms.
| Control | When it applies | What it does |
|---|---|---|
| Pause-work clause | Unpaid milestones or missing required feedback or approvals; some clauses use a five-day non-response trigger | Lets work pause |
| Access-delay clause | Required access or inputs arrive late | Timeline and pricing can be adjusted |
| Change Order | Extra work starts or scope expands | Documents scope expansion or repricing before extra work starts |
First, include a pause-work clause for unpaid milestones or missing required feedback or approvals; some clauses use a five-day non-response trigger. Second, add an access-delay clause so timeline and pricing can be adjusted if required access or inputs arrive late. Third, require a written Change Order before extra work starts, so any scope expansion or repricing is documented instead of handled informally.
Fast approvals come from deliverables the client can verify at a glance, with evidence attached to each claim.
Step 1. Define three outputs in plain terms. Keep the package to a findings report, a risk-ranked optimization list, and a remediation plan. Frame the findings report as a current-state assessment, including what was reviewed, what was found, and any access limits.
For the optimization list, rank items by impact and risk, and attach the evidence used for each item. If you are using AWS Cost Explorer or AWS Trusted Advisor in this engagement, reference those evidence points directly so reviewers can trace each recommendation.
Checkpoint: if a recommendation cannot be tied to a dated observation, keep it out of the approved backlog.
Step 2. Keep compliance notes explicit and narrow. If SOC 2 or AI-control obligations matter to the client, add brief notes on where findings may intersect with their compliance process. Do not present these notes as formal control testing or certification support unless that scope is separately defined in the SOW.
Step 3. Make acceptance criteria observable. In the quote, name what must happen for approval: agreed evidence pack delivered, walkthrough completed, and written sign-off against Acceptance Criteria. Name the evidence pack contents so acceptance is tied to artifacts, not interpretation.
Step 4. Add one short post-change validation pass. After agreed changes are implemented, run a narrow status check on the targets already listed in scope (for example, EBS volumes, EBS snapshots, ALB, or ELB items if they are part of the engagement). If new issues appear, route them through a Change Order instead of expanding the original audit silently.
For a comparable deliverables-first example, read How to Price a Branding Package for a New Business.
Most mid-engagement pricing problems are fixable if you re-scope quickly instead of forcing the original quote to carry new uncertainty.
| Mistake | Recovery | Key shift |
|---|---|---|
| Pricing full scope before access is granted | Shift the live work to a paid discovery phase, document missing access, and re-price the remaining scope once evidence is complete | Stop pricing on assumptions |
| Bundling service labor with tool or access assumptions | Separate your labor from client-side dependencies and state which systems, data access, and platform prerequisites the client must provide | Keep one bundled fee from being misread as everything included |
| Weak acceptance language in the SOW | Tie acceptance to named deliverables and observable checkpoints; treat scope-expanding feedback as a scope change | Keep factual correction review separate from new scope |
| One end-of-project invoice | Move remaining phases to milestone invoicing tied to concrete outputs and a defined review window | Reduce end-stage payment risk |
Mistake 1: Pricing full scope before access is granted. Recover by shifting the live work to a paid discovery phase, documenting missing access, and re-pricing the remaining scope once evidence is complete. This protects you from pricing on assumptions, especially when operational cloud costs become clearer after deployment and change expected ROI.
Mistake 2: Bundling service labor with tool or access assumptions. Recover by separating your labor from client-side dependencies. State clearly which cost-monitoring and analytics systems, data access, and platform prerequisites the client must provide so one bundled fee is not misread as "everything included."
Mistake 3: Weak acceptance language in the SOW. Recover by tying acceptance to named deliverables and observable checkpoints. If feedback is factual correction, keep it in review; if feedback expands scope, treat it as a scope change instead of reopening the original price.
Mistake 4: One end-of-project invoice. Recover by moving remaining phases to milestone invoicing tied to concrete outputs and a defined review window. This reduces end-stage payment risk and surfaces blockers earlier, while work is still easy to steer.
We covered a comparable re-scoping pattern in How to Price a 3D Animation Project. Want a quick next step? Try the free invoice generator.
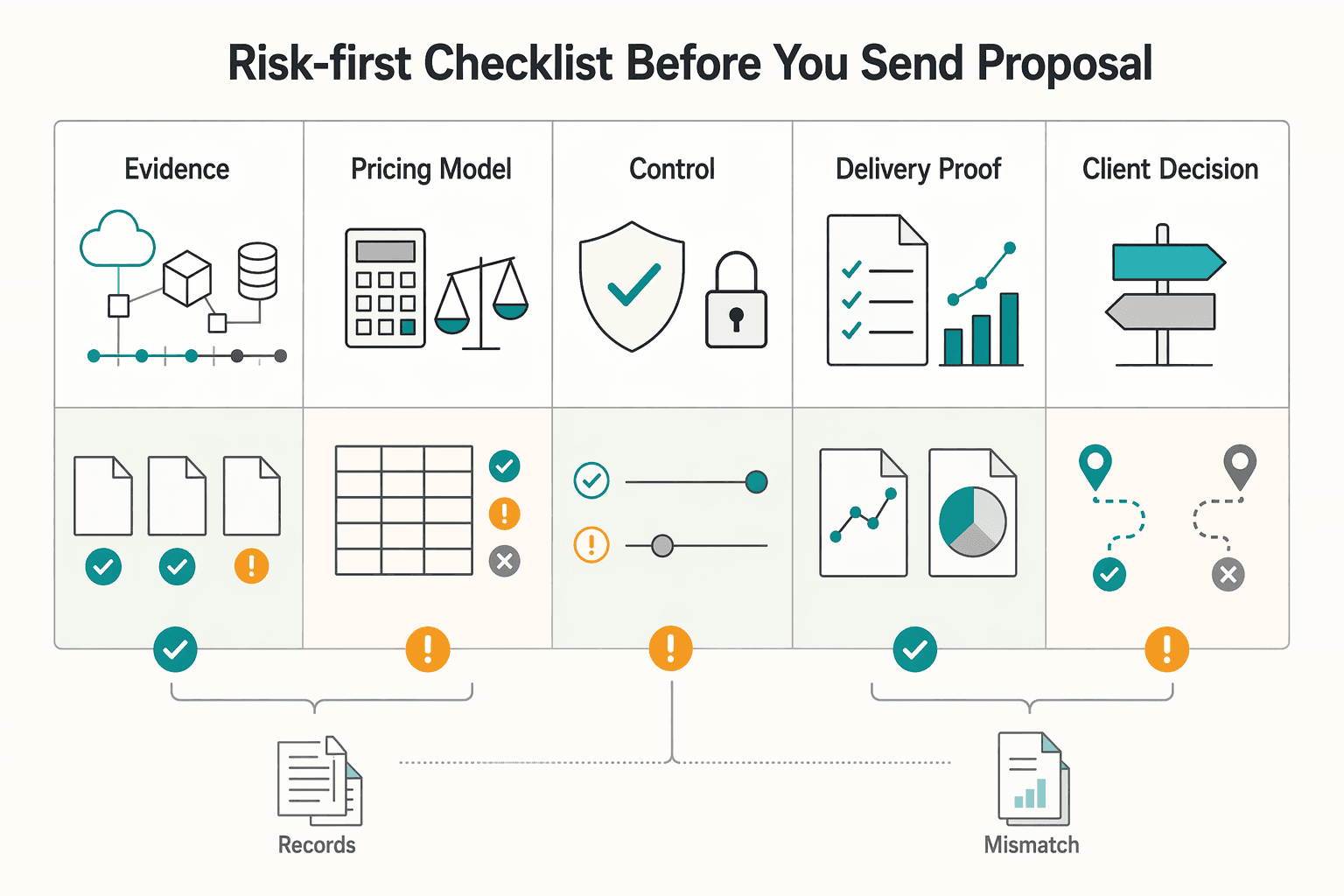
Use this as a stop-or-send gate: if scope evidence, pricing logic, or the acceptance path is still unclear, send a paid discovery option first instead of a full fixed proposal.
| Proposal gate | What to confirm | Action |
|---|---|---|
| Scope evidence | Environment inventory evidence, AWS cost allocation tags activation status, and AWS Cost Explorer baseline views | Treat scope as unresolved if account or region coverage is unclear |
| Pricing model | Whether Fixed-Fee Pricing, Value-Based Pricing, or a hybrid matches how complete and reliable the evidence is | Use a fixed discovery phase if uncertainty is still material |
| Legal and payment controls | Statement of Work (SOW), Acceptance Criteria, Change Order path, and Milestone Invoicing | Lock them before kickoff |
| Delivery proof | The exact artifact, how review happens, and what event counts as acceptance | Make acceptance explicit |
| Client decision | Approve discovery or approve the full quote with assumptions acknowledged in writing | Offer only those two next steps |
Validate environment inventory evidence that shows what exists, how resources relate, and how they were configured over time, not just a point-in-time list. Confirm AWS cost allocation tags activation status before relying on tag-based attribution, and request baseline views from AWS Cost Explorer that show cost and usage over time. If account or region coverage is unclear, treat scope as unresolved.
Choose Fixed-Fee Pricing, Value-Based Pricing, or a hybrid based on how complete and reliable the evidence is. If uncertainty is still material, use a fixed discovery phase and quote the main engagement after evidence is confirmed.
Set the Statement of Work (SOW) so required work is explicit. Define Acceptance Criteria as verifiable success conditions, add a formal Change Order path for scope, cost, or schedule updates, and tie Milestone Invoicing to completed stages.
State the exact artifact, how review happens, and what event counts as acceptance. If this stays vague, work can be operationally complete but commercially disputed.
Offer two next steps only: approve discovery, or approve the full quote with assumptions acknowledged in writing.
This pairs well with our guide on How to Price a Bookkeeping Service for Small Businesses.
Consider starting with a paid discovery phase, not a full fixed quote. In AWS, Cost Explorer visibility can be limited in multi-account setups because member accounts may only see their own cost and usage data. Access is not customizable for each individual member account. If you cannot verify billing views, environment inventory, and the resource set to be assessed, price discovery first and reserve the rest for a Change Order.
Include the Statement of Work (SOW), named deliverables, Acceptance Criteria, dependencies, exclusions, and Milestone Invoicing terms. Also separate your advisory labor from any client-side tooling or third-party subscriptions instead of hiding them inside one number. If an evidence pack will rely on AWS Audit Manager outputs or similar reports, name that as either a deliverable or a client dependency.
Use Fixed-Fee Pricing when the scope is definite enough to describe with reasonably clear specifications and evidence sources. That matters because a firm-fixed-price model puts the contractor at maximum risk for cost overruns and profit loss if your assumptions are wrong. Use Value-Based Pricing when the client cares most about the perceived business value of the outcome, but still set limits around scope, exclusions, and approval points.
Two clients can have similar cloud spend and still require different audit effort. One may have stronger billing visibility and organized evidence, while the other may have partial access, fragmented accounts, or extra review needs before findings are accepted. The failure mode is pricing by headline cloud bill instead of pricing by access quality, evidence quality, and decision friction.
There is no defensible universal timeline. Set the schedule only after you confirm access, evidence availability, reviewer availability, and how many environments or accounts are actually in scope. If those inputs are still unknown, quote a discovery milestone first and only commit to the main timeline after that checkpoint.
Treat scope creep as uncontrolled scope expansion without adjusting time, budget, resources, or approval. In practice, that means your SOW should name the exact outputs, evidence sources, and review boundaries, then route anything new through a Change Order. A good rule is this: factual corrections to delivered findings stay in scope, but new resource classes, deeper compliance interpretation, or added remediation work do not.
Use Milestone Invoicing tied to agreed deliverables or events, not vague progress percentages. One structure is a kickoff deposit, an invoice on delivery of the findings and evidence pack, then final payment at sign-off or expiry of a defined review window. This does not guarantee faster payment, but it does reduce how much value sits unbilled at the end of the engagement.
A former product manager at a major fintech company, Samuel has deep expertise in the global payments landscape. He analyzes financial tools and strategies to help freelancers maximize their earnings and minimize fees.
Educational content only. Not legal, tax, or financial advice.

A workable rate is not the neat number a calculator produces. It is the number that still works after you account for real billable capacity, non-client time, scope drift, and the gap between sending an invoice and receiving cleared cash. Start with hourly math even if you do not plan to bill hourly, then turn that number into a quote with clear `payment terms`.

Undercharging usually starts before the invoice: when you send one attractive number without clear pricing logic, ownership, or controls for scope or rate changes. In value-based consulting, your price and payment structure are one decision, so you need to build them that way.

Move fast, but do not produce records on instinct. If you need to **respond to a subpoena for business records**, your immediate job is to control deadlines, preserve records, and make any later production defensible.