
Start with a narrow objective tied to a real buyer or partner requirement, then map only the systems and data flows that support that service. Select Security first and add optional criteria only when they match explicit commitments. Set up recurring evidence capture for access, changes, and incidents before fieldwork, and validate readiness with drills. Finally, prepare audience-specific materials so security, procurement, and business reviewers each get what they need.
If you want to avoid unnecessary cost in your first SOC 2 cycle, keep the scope tight. Start with the business objective. Then define the exact service boundary, choose only the criteria that reflect real customer commitments, and pick an independent CPA firm that communicates clearly.
Start by writing one specific objective for the report: the buyer, deal motion, or partner requirement it needs to satisfy. Avoid broad goals like "enterprise growth." Use a target your sales, leadership, and technical teams would interpret the same way.
Keep it narrow. Criteria selection should follow your service commitments and what customers or partners are actually asking for. Your objective should answer two questions:
Scope the examination to the systems and services customers actually rely on. Do not pull in every internal tool by default. Create a short scope memo with:
For cloud vendors and sub-service organizations, document carve-in or carve-out treatment explicitly. Third-party controls are not included unless you choose to carve them in.
Security is required in every SOC 2 audit. Add the other criteria only when they match an actual commitment you make to customers.
| Trust Services Criterion | Choose it when your customer promise is | Typical evidence implications | Common over-scoping mistake |
|---|---|---|---|
| Security | We protect service and data from unauthorized access | Can include access, change, monitoring, and incident controls | Treating Security as only an IT concern and missing process or people controls |
| Availability | We keep the service available as promised | Can include availability objectives, monitoring, and response records | Adding it without a clear availability commitment |
| Confidentiality | We protect sensitive non-public information | Can include data classification, access restrictions, and handling controls | Applying it to all data instead of the confidential data types in scope |
| Processing Integrity | We process data completely, accurately, and on time | Can include processing checks, exception handling, and quality controls | Adding it without a defined processing commitment |
| Privacy | We handle personal information in line with defined commitments | Can include notice, consent (where relevant), and retention/deletion handling | Adding it when personal information handling is minimal in scoped services |
If a prospect asks for "all five," confirm what they actually need before you expand the scope.
The firm matters more than many teams expect. A SOC 2 audit must be performed by an independent CPA firm, and independence is required for attestation engagements. Interview multiple firms before you decide, especially if you plan a Type 2 report, which typically covers six months or more.
Use the same comparison points for every firm:
| Compare point | What to ask |
|---|---|
| Relevant experience | Which similar industries, company profiles, or service models do you audit? |
| Cloud stack familiarity | How do you audit environments built on the providers and architecture we use? |
| Communication clarity | Who is our day-to-day contact, and how are requests, status, and blockers managed? |
| PBC request-list quality | Can you share a redacted sample of your PBC (Provided By Client) request list? |
Watch whether the firm can translate its request list into your environment. If it cannot explain evidence requests clearly in that context, treat that as a warning sign.
Before you move into tooling and evidence operations, confirm these five items are done:
Once the assessment scope is set, the next job is operational. To avoid last-minute chaos, treat evidence capture as part of daily work, not an audit-season project. Set up traceability first, automate repeatable records next, and review assessment findings on a cadence your team can actually sustain.
Start with in-scope systems only, such as identity, cloud, code, ticketing, and HR records that support the service you defined in Phase 1. The goal is traceability, not integration volume. You should be able to follow real events end to end:
If you still need manual screenshot hunts across multiple people to reconstruct a single event, the process is too manual for a clean audit cycle.
Automate the records that should exist every time: access events, change records, approvals, ticket states, and timestamps. Keep people focused on exception review, investigations, and final sign-off. Use a simple decision lens when you choose how much to automate:
| Workflow | Effort burden | Audit readiness | Typical failure points |
|---|---|---|---|
| Manual | High, especially before fieldwork | Inconsistent | Missing approvals, stale screenshots, naming drift, late gaps |
| Hybrid | Moderate | Better if key records sync | Partial coverage, duplicate records, unclear source of truth |
| Connected automated | Lower for routine evidence, higher at setup | Stronger when capture is embedded in normal work | Broken integrations, unmonitored collection failures, false confidence |
Templates do not help unless they match how your team actually works. For each core policy, define the process it covers, who owns it, how it is approved, what evidence it should produce, and where that evidence lives. For each policy, pin down:
Then test recent real events against the policy. A joiner or offboarding event, a production change, and an incident or near miss are usually enough to show whether the policy is real. If the policy says a review happened but no record exists, the policy is not operational yet.
Treat findings as readiness signals, not paperwork. Track each one with the issue, owner, status, remediation proof, and retest outcome. Pay especially close attention to:
One failure mode to watch for is silent evidence loss. If logging or evidence collection breaks and no one is alerted, you can miss control failures until someone manually catches the gap.
Before the audit begins, run a short rehearsal to confirm the process holds up under use. Use this pre-audit checklist:
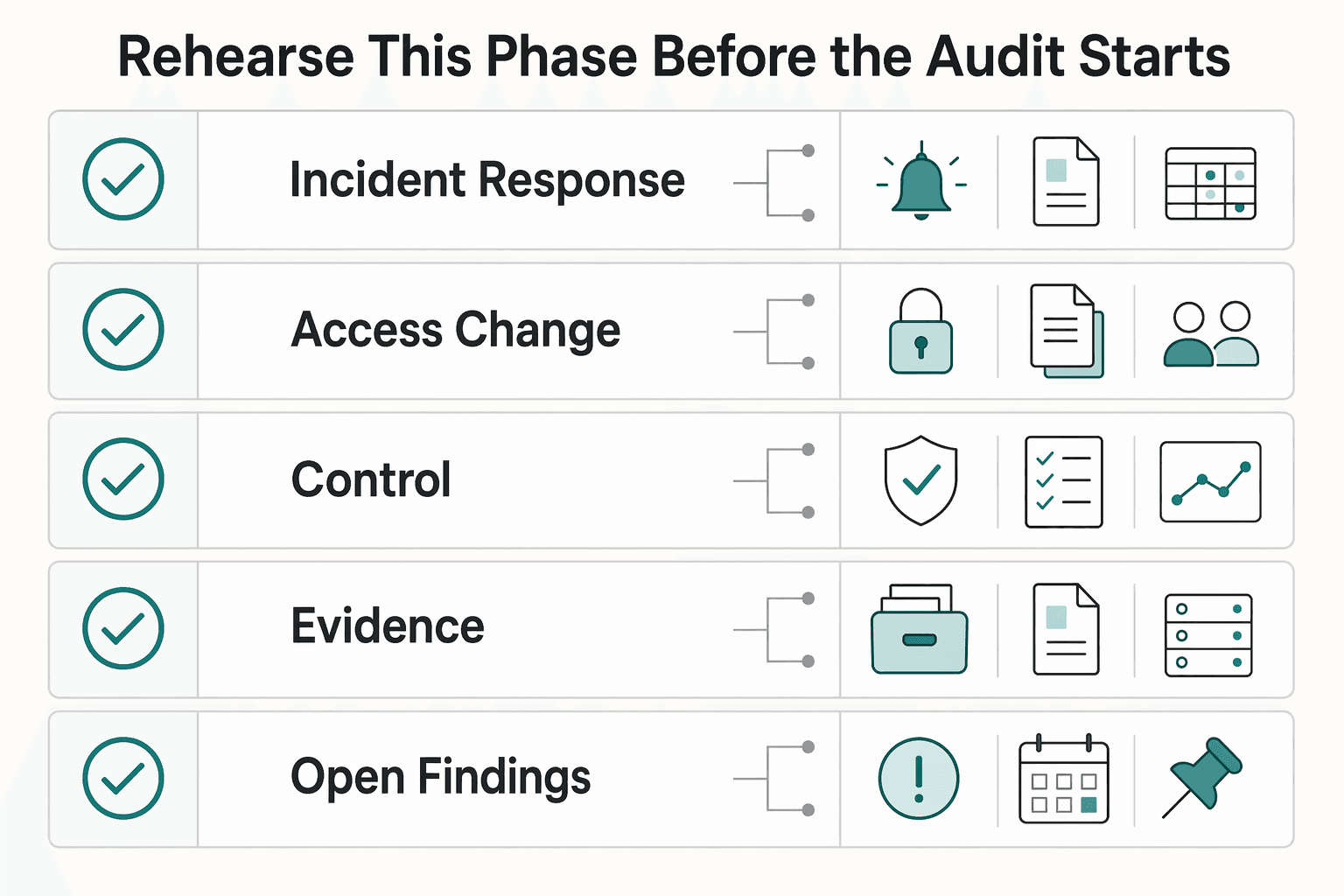
| Check | What to confirm |
|---|---|
| Incident-response drill | Retain the full record, including timeline, decisions, actions, and closure |
| Access-change drill | One grant and one removal, each tied to a triggering event |
| In-scope controls | Each control has a current policy, named owner, approval trail, and recent evidence artifact |
| Change records | They link cleanly across ticketing, code, and deployment history |
| Open findings | Documented remediation, retest evidence, and closure |
| Audit/logging failure alerting | It reaches a named owner |
When this phase is working, evidence is created during normal work and audit readiness becomes a maintenance task instead of a fire drill.
Related: A Guide to SOC 2 Compliance for SaaS Companies.
If your SOC 2 evidence still depends on manual screenshots and spreadsheets, review the Gruv docs to map webhook events, ledger history, and payout states into a cleaner control narrative.
Once your evidence is reliable, use it to reduce buyer-review friction, not just to pass the audit. The practical move is to package the same assurance story for different reviewers and send the right version when that team enters the deal.
Do not build one giant master PDF and hope it works for everyone. Build a Trust Packet in audience-specific versions so your materials match how security, procurement, legal, and business stakeholders actually evaluate vendors.
| Audience | What to provide |
|---|---|
| Security reviewers | Controlled access to your SOC 2 examination report, plus a concise scope-and-exceptions summary |
| Procurement and legal reviewers | A lighter packet with core company details, key contacts, and a plain-language summary of what the audit covered |
| Business stakeholders | A one-page summary of operational risk handling and what independent assurance means for onboarding confidence |
Before you send anything, run a quick usability check. Confirm the report period is current and that every asset has a named owner and last review date.
Send trust materials by sales stage instead of waiting for a questionnaire, so the buyer gets the right level of detail before formal review starts. A simple sequence to consider:
| Sales stage | What to share |
|---|---|
| Early evaluation | A business-facing summary or your Trust Center |
| Security or risk review start | Request-based access to SOC 2 and related security documents |
| Questionnaire/SIG stage | Reuse maintained responses and attach supporting SOC material where relevant |
This matters because buyers often request security questionnaires before onboarding, and those can range from 100 to 1,000+ questions. SOC material helps reduce friction in due diligence, but it does not replace the process.
A public-summary-plus-gated-detail Trust Center model is a practical setup. It lets buyers self-serve the basics while keeping sensitive detail controlled.
| Buyer enablement option | Effort to maintain | Buyer clarity | Deal-friction reduction |
|---|---|---|---|
| Full SOC 2 report | Moderate after issuance, plus access-control overhead | High for security/risk teams; low for non-technical stakeholders | Strong during formal review; limited in early-stage evaluation |
| Summary Trust Packet | Moderate ongoing upkeep to stay current | High for procurement, legal, and business stakeholders | Good for moving deals into structured review |
| Public Trust Center assets | Low to moderate if maintained | Good for early buyer orientation | Good for reducing repetitive inbound questions |
Keep broad-distribution content public, such as high-level security posture and SOC 3 if available. Keep detailed SOC 2 sharing gated behind request, authenticated access, or NDA when appropriate.
When pricing or speed objections show up, answer with operational proof instead of broad claims. Keep the conversation anchored to review workflow risk and implementation confidence.
If procurement pushes on price, keep the response tied to review workflow risk and implementation confidence. If security still requires a questionnaire, confirm that process and respond from a reusable evidence base to reduce repeated rewrites of control narratives.
Only make performance claims after you verify your own data. Track:
% of deals that enter security reviewmedian time in vendor/security review: baseline and current benchmarks pending source-record verificationquestionnaire response reuse rate: baseline and current benchmarks pending source-record verificationwin rate when SOC materials are requested: baseline and current benchmarks pending source-record verificationThose are the proof points that show whether your SOC work is helping the business, not just satisfying an audit.
You might also find this useful: What is a Service Organization Control (SOC) 2 Report?.
The throughline is simple: treat SOC 2 as an operating discipline you can verify, not a one-time document chase. To reduce avoidable rework, focus on three outcomes: a defensible scope, evidence-ready control operation, and a report package your team can use in security conversations.
Your first outcome is a scope you can explain and defend. Security is the required common criterion, and any additional Trust Services Criteria should reflect actual service commitments under the 2017 TSC (Revised Points of Focus 2022), not precautionary over-scoping. Use one practical check: does your current system description still match the service you provide today?
Your second outcome is evidence that reflects real operations. Each key control should have a named internal owner, current policy alignment, and a repeatable evidence source. Even when activities are outsourced, accountability stays with you.
For a SOC 2 Type 2 examination, controls are evaluated on whether they operate effectively over time. A readiness assessment before the examination can surface gaps early so you can address issues before the examination period is under review.
| Area | Obligation mode | Strategic mode |
|---|---|---|
| Ownership | Control responsibility is informal | Each key control has a named internal owner |
| Evidence practices | Evidence is assembled late | Evidence is produced and reviewed as part of normal operations |
| Audit readiness | Gaps may be discovered during the audit cycle | Gaps are identified in a readiness assessment before the examination |
| Sales usage | Report is filed away after issuance | Report supports customer security reviews and questionnaire responses |
Your third outcome is a report package that reduces friction with external assurance stakeholders. SOC 2 reports are used by audiences that need detailed assurance information, so treat the package as a working asset. Management's assertion, system description, and the service auditor's report should be organized and ready to share through your approved process.
Assign clear ownership for customer assurance requests. Store the package in a controlled internal location, and keep a recurring compliance cadence so evidence and scope stay current before the next examination.
When you are ready to operationalize audit-ready money movement in your stack, contact Gruv to validate coverage, compliance gates, and implementation fit for your workflow.
Start with scope, not paperwork. Define exactly which service stores, processes, or transmits customer data and why you need SOC 2 now. Then align the scope to the customer commitments you already make so you do not build controls you do not need. Before you begin, confirm clear ownership for access, change management, incident response, and vendor oversight.
Current cost range pending source-record verification. Cost will vary with scope and readiness. Before you budget deeply, verify that you already have current policies, named control owners, and a clean in-scope vendor list.
Current preparation timeline pending auditor and source-record verification. Timing will depend on your readiness and auditor availability. Before you commit to dates, confirm approved policies, a mapped evidence source for each key control, and no unresolved high-risk gaps.
Yes. SOC 2 can be relevant if you store, process, or transmit customer data. It is not generally required by law, but customers, partners, and regulators often expect it, and SaaS and cloud companies are common candidates. Keep the scope tied to real buyer asks so the evidence matches how you actually operate.
Choose based on buyer expectations and auditor guidance. There is no one-size-fits-all sequence confirmed here, so avoid assuming a default path without validating requirements for your engagement.
Pick the criteria that match explicit customer commitments, not every criterion by default. SOC 2 evaluations use five Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy. Over-scoping can create extra controls and evidence work. Use this quick decision aid: | Trust Services Criterion | Include it when | Common over-scoping mistake | | --- | --- | --- | | Security | it is in scope for your service and commitments | defining tools before defining service boundary | | Availability | it is in scope for your service and commitments | adding it without a documented commitment | | Processing Integrity | it is in scope for your service and commitments | adding it without a documented commitment | | Confidentiality | it is in scope for your service and commitments | adding it without a documented commitment | | Privacy | it is in scope for your service and commitments | adding it without a documented commitment |
Before auditor outreach, make sure you can provide a usable evidence pack, not just policy files. At minimum, verify that the entity being audited is clearly defined, the selected criteria are explicit, and each key control has an owner plus sample evidence. Also check that any incident-response references are current and not pointing to withdrawn guidance (for example, NIST SP 800-61r2 was withdrawn and superseded).
A career software developer and AI consultant, Kenji writes about the cutting edge of technology for freelancers. He explores new tools, in-demand skills, and the future of independent work in tech.
Priya is an attorney specializing in international contract law for independent contractors. She ensures that the legal advice provided is accurate, actionable, and up-to-date with current regulations.
Includes 5 external sources outside the trusted-domain allowlist.
Educational content only. Not legal, tax, or financial advice.

Low-stress compliance in Germany comes from decision order, not tax tricks. Use this sequence: confirm core facts, apply conservative temporary assumptions, verify the few points that can break invoices or filings, and keep one evidence file that explains each decision.

**Build your SOC 2 playbook before sales pressure hits, so you control scope, evidence, and audit timing instead of reacting under stress.** If you're pursuing **[soc 2 compliance for saas](https://www.cobalt.io/learning-center/soc-2-compliance-for-saas)**, treat this guide as a system, not a policy exercise. As the CEO of a business-of-one, you need a SOC 2 plan that protects your calendar as much as your customers. Use it to decide what to implement first, keep the right proof, and connect the work to clearer security controls, cleaner buyer conversations, and fewer fire drills.

You are still accountable for [third-party risk](https://www.federalreserve.gov/frrs/guidance/interagency-guidance-on-third-party-relationships.htm), so reviewing a SOC 2 report should be treated as an operating control, not a paperwork task.