
Start remote employee offboarding by fixing sequence before speed: approve classification, assign the correct owner path (direct employee, EOR, or contractor), and send written notice only after that record is complete. Then remove access from identity controls outward and require audit logs plus timed rechecks before signoff. Keep the file active until payment handling, handover receipts, communication approvals, and open issues all show named owners and dates; when status is disputed, Form SS-8 is the formal IRS determination route.
A common offboarding failure pattern is doing the right tasks in the wrong order. Treat compliance as a hard sequence: classify the relationship, route the owner path, send written notice, and close only when the evidence file is complete.
Do not send notice until status is documented and approved. Start with how the work actually happened, not just the contract label. For U.S. tax, the IRS standard is the real worker-business relationship. For FLSA analysis, the question is economic dependence. Use a go/no-go gate with named ownership:
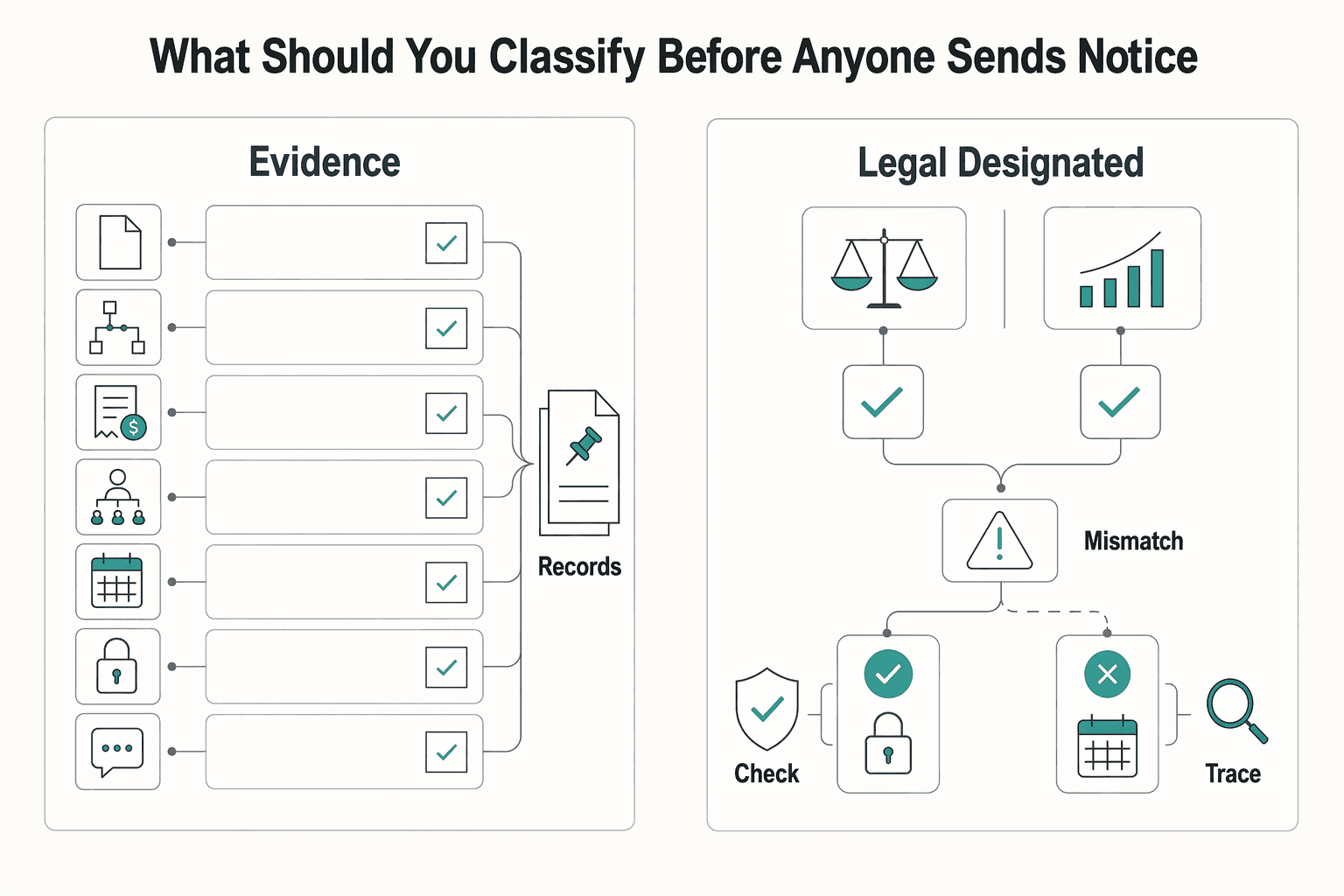
Keep the evidence practical and traceable: contract or employment agreement, SOW, invoices, payment history, manager direction, approvals, schedule expectations, access history, and message threads about work control. If the contract says "contractor" but day-to-day control looks employee-like, treat that as a real risk signal.
Also treat classification rules as current-state, not static. DOL published a 2024 rule, effective March 11, 2024. It then announced a new NPRM on February 26, 2026, published February 27, 2026, with a comment deadline of April 28, 2026. If your decision depends on a specific federal test, verify current status before relying on template wording. If status is disputed or unclear, Form SS-8 is the formal IRS determination route.
Once classification is approved, lock the owner path before anyone discusses dates, money, or access. If an Employer of Record is involved, keep responsibilities explicit. The EOR can hold legal-employer duties, but you can still carry tax or legal exposure if the setup was weak.
| Path | Accountable owner | Required documents | Payment route | Primary dispute exposure | Required closure proof |
|---|---|---|---|---|---|
| Direct employee | HR/People owner, with payroll and legal support | Employment agreement, approval record, notice, payroll instructions, benefits record (if applicable) | Company payroll with normal withholding/employer obligations | Final-pay timing, notice defects, missed benefits handling | Notice trail, payroll confirmation, acknowledgment, termination record |
| EOR employee | Internal owner for facts/timing; EOR for employer-side actions | EOR notice packet, employment record, payroll instructions, local notice documents (where required) | EOR payroll route | Local termination defects, missed EOR approvals, payroll coordination gaps | EOR correspondence, payroll confirmation, notice trail, required local proof |
| Contractor | Contract owner, ops lead, or hiring manager | Contract/SOW, invoices, acceptance records, written closeout notice | AP under contract; generally no payroll withholding by the business | Misclassification, deliverable acceptance disputes, unpaid invoice claims | Closeout note, payment proof, notice trail, handover receipt, nonemployee compensation reporting evidence (when applicable) |
Stop the case if either of these is true:
Weak entry records often become weak exits. If that keeps happening, tighten the lifecycle earlier with How to Onboard a New Employee in a Remote-First Company.
A good notice is short, approved, and easy to tie back to the case file. Each element should create one concrete record.
| Notice item | What to include | Artifact |
|---|---|---|
| What is ending, and when | Identify the agreement or employment relationship, effective date, and basis used | Approval trail + delivery/acknowledgment record |
| What will be paid, by whom, and on what basis | Include final wages, approved expenses, invoices, accrued items (if applicable), and severance only where policy, agreement, or contract supports it | Payment calculation + payroll/AP confirmation |
| What must be handed over | List files, accounts, client materials, and named recipient or repository | Handover receipt |
| What confidentiality and IP obligations continue | Restate signed obligations and permitted return, delete, or no-use instructions | Written confidentiality/IP confirmation |
| What regulated notices may apply | Check benefits and group-reduction triggers before issuance | Legal or plan-admin confirmation |
Use the table as the checklist. If any item is still unclear, the notice is not ready.
Keep these timing gates explicit:
Scattered proof is one of the easiest ways to create avoidable risk. Keep one consolidated offboarding file instead of spreading the record across chat, email, payroll, and drives.
| Record type | Federal anchor |
|---|---|
| Payroll/related records | 3-year floor |
| Involuntary termination records | 1-year federal floor |
| Form I-9 | 3 years after hire or 1 year after employment ends, whichever is later |
| Contractor closeout | Keep nonemployee compensation reporting evidence when threshold is met (currently $600 or more), with January 31 as the filing or furnishing anchor date |
Minimum fields: case owner, classification memo, owner path, effective date, notice record, payment record, handover record, confidentiality/IP confirmation, and unresolved-items log.
Treat unresolved items as real work, not placeholders. Every open item needs an owner, due date, escalation contact, and current status. Set retention by record type, not one blanket period.
Close the case only when unresolved items have completion proof or written escalation. That discipline carries directly into the access shutdown work in the next pillar. Related: How to Manage a Global Team of Freelancers.
Technical shutdown needs the same gate discipline as legal closure. Treat it as five hard gates: authorization complete, pre-cutoff snapshot complete, revocation executed, recheck passed, closure approved. If any gate is missing evidence, the case stays open, even when the account appears disabled.
Use the Pillar 1 file as your control plane, then execute identity-first from there. NIST PS-4 sets the baseline: disable access within an organization-defined period. Assign a named owner and reviewer for that deadline.
Do not let one fast click become an unreviewed failure. Separate approval, execution, and closure review before anyone touches the account.
| Role | What they control | Required artifact |
|---|---|---|
| Decision owner | Approves cutoff time, exceptions, and temporary continuity measures | Written authorization with effective time, exceptions, owner, and timestamp |
| Technical executor | Captures pre-cutoff state and performs revocation actions | Snapshot package listing access groups, mailbox delegates, repo access, keys/secrets in scope, device state, log source, executor, and timestamp |
| Closure reviewer | Confirms rechecks, continuity transfer, and unresolved-item handling | Closure note with reviewer name, review time, passed checks, and escalations |
If one person approves, executes, and closes, escalate before final signoff.
The first cut should happen at identity, but revocation is not complete just because you triggered it. Microsoft documents an enforcement gap. Entra access tokens default to a 1-hour lifetime. revokeSignInSessions can still take a few minutes, and Entra cannot directly revoke application-issued session tokens.
| Class | Required revocation action | Evidence artifact | Mandatory recheck |
|---|---|---|---|
| IdP and SSO | Disable sign-in, remove privileged groups, revoke sessions, remove MFA methods | Admin audit entry showing actor, action, target user, and timestamp; session-revocation record | Recheck after your verified interval |
| Email and mailbox access | Block account access, review forwarding, remove delegates | Mailbox settings snapshot plus admin log for delegate or forwarding changes, reviewer noted | Recheck delegation and forwarding after your verified interval |
| Source control | Remove org or repo access, review PATs, review SSH and deploy keys | Org audit log plus credential review note with repositories affected and timestamp | Recheck repo membership and non-user credentials after your verified interval |
| Cloud keys and secrets | Deactivate IAM access keys, rotate shared secrets, replace service identities owned by the user | Key-status record, secret-rotation record, cloud audit event, reviewer | Recheck dependent jobs after your verified interval |
| Devices | Lock, retire, or wipe per policy | MDM action record, Initiated By audit log, device status timestamp | Recheck pending state after your verified interval |
Before you close, call out these common misses explicitly:
Security revocation is only half the job. Closure also requires continuity transfer. CISA flags IT-system access control and remote-worker considerations during separations. NIST PS-4 also requires retaining access to information and systems formerly controlled by the terminated person.
Run a parallel continuity check for work ownership, account ownership, automations, scheduled jobs, and tested replacement credentials. If transfer is blocked, log the dependency, interim control, owner, due date, and approver instead of restoring broad access.
In Google Workspace, keep "access removed" separate from "data exposure controlled." A deleted user cannot access Workspace services, but you should transfer needed Gmail and Drive data first. Also, Drive ownership transfer does not change existing sharing permissions, and direct ownership transfer to or from external accounts is not supported. Make sharing-permission review a separate closure item before final approval.
If continuity failures keep repeating, fix the ownership model earlier in How to Onboard a New Employee in a Remote-First Company. If you want a deeper dive, read Germany Freelance Visa: A Step-by-Step Application Guide. If your offboarding runbook includes final-pay cutoffs and proof of payout status, map that step into your process with Gruv Payouts.
Once access revocation is verified, the people side still needs controls. Treat it as a closure sequence: debrief first, send only trigger-based updates, and close only when the restricted file is complete. If any item lacks an owner, evidence, or disposition, keep the case open.
A debrief only matters if it turns into assigned work. Run it as a lessons learned checkpoint with explicit authority and ownership, not an open-ended retrospective. Every row should end with a named owner, due date, and inspectable closure artifact.
| Action rule | Required evidence now | Single owner | Closure artifact | If ownership is missing |
|---|---|---|---|---|
| Turn each blocker or repeat risk into one fixable issue | Specific example, affected process/tool, linked ticket or doc, proposed change | Relevant manager or process owner | Closed ticket, updated policy, or implemented control | Escalate to decision owner for interim assignment and due date |
| Identify work still dependent on one person | Open decisions, client context, key file paths, undocumented automations, missing backup contact | Manager | Ownership-transfer note and continuity signoff | Escalate to department lead before case close |
| Clear assets or records still tied to the person | App or account list, inboxes, local files, sponsored accounts, device IDs | Ops or technical owner | Reassignment record, return receipt, or verified removal note | Escalate to operations lead and log as unresolved risk |
| Decide what must change before backfill | One concrete improvement, target date, success measure | Department lead | Completed change or written risk acceptance | Escalate to executive owner for accept or defer decision |
Reject vague entries. If a line says "improve communication," it is incomplete until it names the channel, impact, owner, and change.
Default to minimum-necessary, private-by-default updates. Send messages only when ownership, response routing, approval authority, or service contact changes. If nothing operational changes, skip the broad announcement.
Use one approval flow each time: people-process owner drafts, decision owner approves, designated sender sends, and the record is filed with date, channel, recipient group, and approver. For messages that include sensitive details (for example departure reasons, health details, allegations, settlement terms, or disputed facts), route them through HR or legal review according to your policy and jurisdiction. Include "no side explanations" in the approval note so managers do not add unofficial context afterward. If this is a recurring problem, tighten it in your written communication policy.
References are where you reduce improvisation, not invite it. Handle them with policy defaults because jurisdiction rules vary. In UK guidance, references are usually optional, but if provided they must be fair and accurate. Opinion statements should be evidence-backed and avoid irrelevant personal details.
Default to policy language, for example role and employment dates, unless an approved exception is documented. For any nonstandard wording, require all three in the file: exact statement text, supporting evidence, and rationale for the exception. Escalate statements touching misconduct, protected activity, discrimination complaints, or disputed history.
Do not close the case until the restricted file is complete and access is limited to need-to-know roles. At minimum, include:
accept, mitigate, transfer, or avoid), plus written risk acceptance when remediation is deferred.Use that file as the accountability record, keep it confidential, and retain it only as long as the applicable record type and jurisdiction require. You might also find this useful: How to Review a Remote Employee Handbook as an Independent Contractor.
Close only when each pillar has one owner, one decision, and one evidence trail. The rule is simple: no owner, no proof, no close.
| Pillar | Single owner | Explicit decision | Required artifact | Do not proceed if |
|---|---|---|---|---|
| Compliance | People-process owner | Is the departure path approved, and are policy checks resolved or explicitly assigned? | Approval trail, departure record, and any jurisdiction-specific item logged for verification with owner and due date | Approval path is unclear, or any verification item has no owner and due date |
| Access and continuity | Technical or ops owner | Are revocation, asset handling, and handoff complete enough to close? | Revocation proof, task-level status with success verification, asset receipt or reassignment record, and current work owner confirmation | Any account, mailbox, repo, or critical task lacks verified disposition |
| Communication and file close | Manager or communications owner | Were only necessary messages sent, and is the restricted file complete? | Approved message copy, send record, debrief notes, and unresolved-item disposition marked accept, avoid, transfer, or mitigate | Facts are disputed, approvals are missing, or the restricted file is incomplete |
Use this closeout sequence in order:
For access, automation is execution support, not closure proof. Microsoft Entra can run a real-time offboarding sequence, including removing group access, removing Teams access, then deleting the account. But on-demand lifecycle workflows bypass execution conditions, so prerequisite checks still need manual control. Require task-level status and success verification. If you used revokeSignInSessions, recheck before signoff. It invalidates refresh tokens and browser session cookies, but not every app-issued session, and the default access-token window is 1 hour.
Keep one restricted file as the operating record. At minimum, include the approval trail, revocation proof, communication record, and unresolved-item disposition. Add meeting minutes or formal process notes when they explain decisions. Retention is jurisdiction-specific, but if the file contains U.S. payroll or personnel records, note that baselines can include at least three years for FLSA payroll and one year for EEOC personnel-record contexts.
After this case closes cleanly, align your next hire flow with How to Onboard a New Employee in a Remote-First Company. That way, starts and exits follow the same evidence standard.
If you want a second opinion on offboarding control design and payout operations, talk to Gruv.
Do not send notice until status is documented and approved. Start with how the work actually happened, not just the contract label. For U.S. tax, the IRS standard is the real worker-business relationship. For FLSA analysis, the question is economic dependence. Use a go/no-go gate with named ownership: Keep the evidence practical and traceable: contract or employment agreement, SOW, invoices, payment history, manager direction, approvals, schedule expectations, access history, and message threads about work control. If the contract says "contractor" but day-to-day control looks employee-like, treat that as a real risk signal.
Once classification is approved, lock the owner path before anyone discusses dates, money, or access. If an Employer of Record is involved, keep responsibilities explicit. The EOR can hold legal-employer duties, but you can still carry tax or legal exposure if the setup was weak. Stop the case if either of these is true:
A good notice is short, approved, and easy to tie back to the case file. Each element should create one concrete record. Use the table as the checklist. If any item is still unclear, the notice is not ready.
Scattered proof is one of the easiest ways to create avoidable risk. Keep one consolidated offboarding file instead of spreading the record across chat, email, payroll, and drives. Minimum fields: case owner, classification memo, owner path, effective date, notice record, payment record, handover record, confidentiality/IP confirmation, and unresolved-items log.
Do not let one fast click become an unreviewed failure. Separate approval, execution, and closure review before anyone touches the account. If one person approves, executes, and closes, escalate before final signoff.
The first cut should happen at identity, but revocation is not complete just because you triggered it. Microsoft documents an enforcement gap. Entra access tokens default to a 1-hour lifetime. revokeSignInSessions can still take a few minutes, and Entra cannot directly revoke application-issued session tokens. Before you close, call out these common misses explicitly:
Security revocation is only half the job. Closure also requires continuity transfer. CISA flags IT-system access control and remote-worker considerations during separations. NIST PS-4 also requires retaining access to information and systems formerly controlled by the terminated person. Run a parallel continuity check for work ownership, account ownership, automations, scheduled jobs, and tested replacement credentials. If transfer is blocked, log the dependency, interim control, owner, due date, and approver instead of restoring broad access.
A debrief only matters if it turns into assigned work. Run it as a lessons learned checkpoint with explicit authority and ownership, not an open-ended retrospective. Every row should end with a named owner, due date, and inspectable closure artifact. Reject vague entries. If a line says "improve communication," it is incomplete until it names the channel, impact, owner, and change.
Default to minimum-necessary, private-by-default updates. Send messages only when ownership, response routing, approval authority, or service contact changes. If nothing operational changes, skip the broad announcement. Use one approval flow each time: people-process owner drafts, decision owner approves, designated sender sends, and the record is filed with date, channel, recipient group, and approver. For messages that include sensitive details (for example departure reasons, health details, allegations, settlement terms, or disputed facts), route them through HR or legal review according to your policy and jurisdiction. Include "no side explanations" in the approval note so managers do not add unofficial context afterward. If this is a recurring problem, tighten it in your written communication policy.
References are where you reduce improvisation, not invite it. Handle them with policy defaults because jurisdiction rules vary. In UK guidance, references are usually optional, but if provided they must be fair and accurate. Opinion statements should be evidence-backed and avoid irrelevant personal details. Default to policy language, for example role and employment dates, unless an approved exception is documented. For any nonstandard wording, require all three in the file: exact statement text, supporting evidence, and rationale for the exception. Escalate statements touching misconduct, protected activity, discrimination complaints, or disputed history.
A former tech COO turned 'Business-of-One' consultant, Marcus is obsessed with efficiency. He writes about optimizing workflows, leveraging technology, and building resilient systems for solo entrepreneurs.
Priya is an attorney specializing in international contract law for independent contractors. She ensures that the legal advice provided is accurate, actionable, and up-to-date with current regulations.
Educational content only. Not legal, tax, or financial advice.

Choose your track before you collect documents. That first decision determines what your file needs to prove and which label should appear everywhere: `Freiberufler` for liberal-profession services, or `Selbständiger/Gewerbetreibender` for business and trade activity.

If you want to manage a global freelance team without constant cleanup, use the same intake-to-payout process for every engagement and save an artifact at each gate. Common failure points are instinct-based classification, vague scope, and payments approved in chat with no audit trail.

**Step 1. Treat remote employee onboarding as an operating task, not a welcome gesture.** If you want fewer dropped handoffs, the goal is not a big HR program. It is a lightweight, repeatable way to orient, equip, and connect a new hire across practical stages like pre-start, first week, and early ramp. For most small teams, that means enough structure to prevent obvious misses without creating enterprise overhead you will not keep up with.