
Start by treating delegation as a control rollout, not a quick handoff. To delegate work to virtual assistant support safely, run the 15-minute readiness gate first, then assign only reversible tasks with clear done-state rules. Keep sensitive actions approval-gated through Days 31-60, and expand responsibility only after clean execution evidence. Use completion packs each cycle so outputs, exceptions, and next owners are traceable before you widen scope.
As a professional, you are the engine of your business. Your expertise brings in revenue, your standards shape quality, and your judgment sets direction. That is a strength, but it is also a limit. When growth is capped by the number of hours you can personally work, you are not operating as a CEO. You are operating as a high-performing bottleneck.
Most advice stops at "delegate," which is where the real concerns begin. The hesitation is usually not laziness or ego. It is the risk of losing control, lowering quality, or creating avoidable security and payment mistakes. The practical answer is not to let go and hope for the best. It is to put controls in place first.
This guide follows three pillars: fortify the foundation, build the system, and scale trust in stages. Done well, delegation stops being a leap of faith and becomes a controlled way to create capacity.
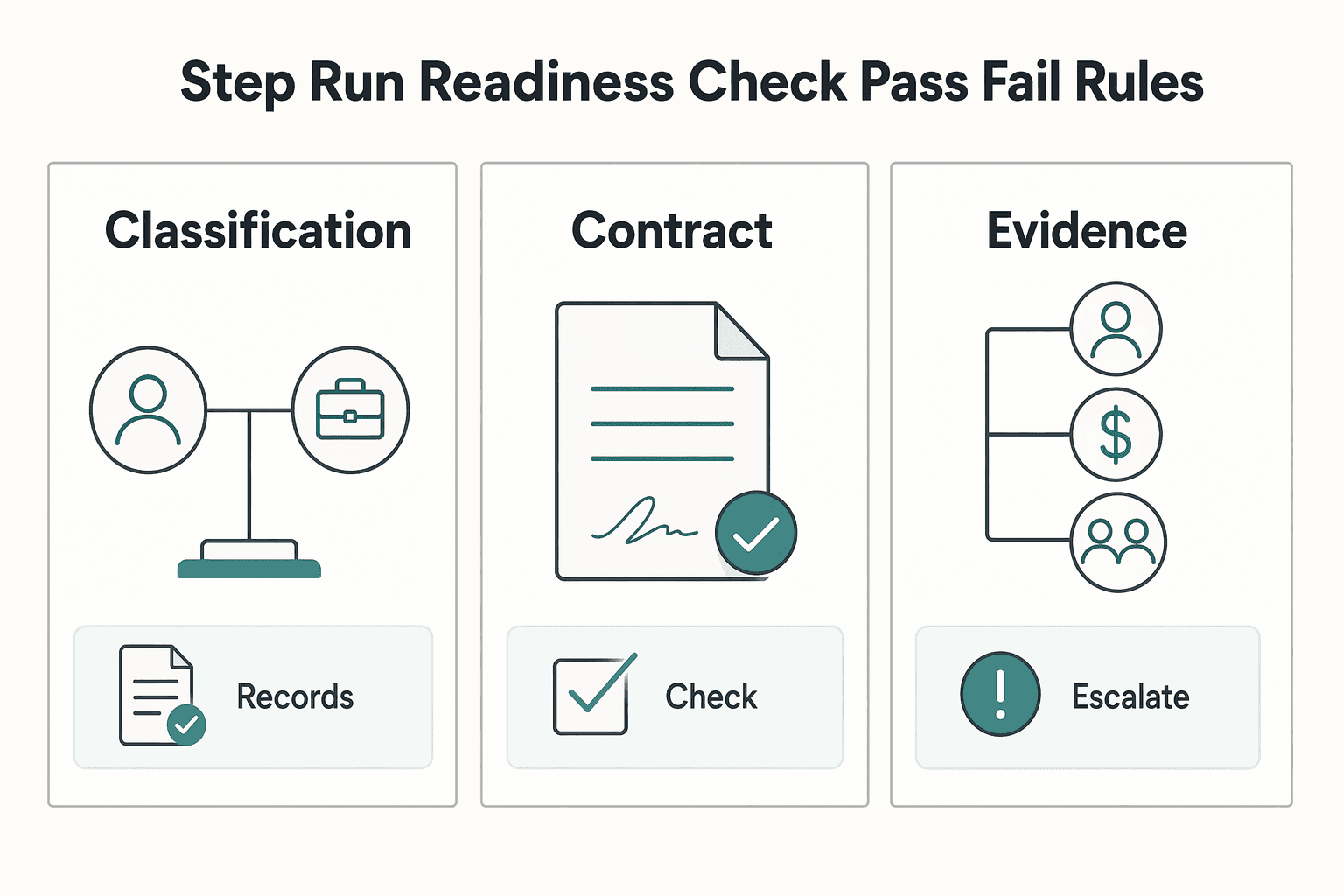
Set a hard readiness gate before you hand off anything. If you want outside support without cleanup later, do not delegate until you can show four things in one place: classification notes, a contract draft with open items clearly called out, a narrow access plan, and a written spend policy.
Build a small evidence pack before you talk about start dates. Keep it in one folder or doc set you can open quickly. The pass standard is simple: another adult should be able to review it and understand who this person is, what they can touch, what they can spend, and who approves exceptions.
| Evidence pack item | What it should show |
|---|---|
| Classification notes | Why you are treating the role as contractor work, what result you control versus how the work is done, and any open questions for counsel |
| Contract draft | A contract draft with any unresolved legal or compliance item clearly called out for review. |
| Access plan | What the person can touch, what data they will handle, why they need it, and the minimum necessary access on a need-to-know basis |
| Spend policy | What they can spend and who approves exceptions |
Start with worker status. Payment handling and contract terms often depend on it. The IRS says you must determine whether the person providing services is an employee or an independent contractor, and its evidence groups fall into behavioral, financial, and relationship categories. Written contracts help, but the IRS also says there is no magic number of factors and a contract alone does not decide status.
Use this as a pre-handoff checklist:
A common red flag is scope drift. If "calendar help" becomes inbox management, billing support, or client communications, rerun the check before you expand access.
| Area | Basic setup | Mature setup | Upgrade when |
|---|---|---|---|
| Classification and contract | Classification note, draft agreement, and any open confidentiality or IP items called out for review. | Counsel reviewed terms for governing law, data handling, dispute language, and country-specific requirements | Upgrade when duties expand, supervision increases, or the relationship becomes cross border |
| Access control | Separate named logins, least privilege, MFA on every supported account | Permission map by tool, periodic privilege review, end-dated elevated access, offboarding record | Upgrade when admin rights, client data, or financial tools enter scope |
| Money controls | Dedicated spend method, named approver, draft purchase limits, and receipt rules | Separation of duties for request, approval, and reconciliation, plus exception log and monthly review | Upgrade when recurring spend starts, more than one approver exists, or the assistant touches vendor payments |
Treat the contract as a counsel-reviewed draft with open items, not a copied template you assume is current. That matters even more in 2026 because the U.S. Department of Labor replaced the 2021 independent contractor rule with a final rule published on January 10, 2024, effective March 11, 2024. The same rulemaking page shows an active NPRM comment window through April 28, 2026 at 11:59 ET. The takeaway is simple: verify current requirements before you finalize language.
Your draft should clearly identify unresolved terms for counsel review before anyone signs. If the assistant is outside the U.S., note whether payer documentation may be needed. That can include Form W-8BEN for a foreign individual to establish foreign status when applicable. If you need a deeper classification refresher, read What to Do If You've Been Misclassified as an Independent Contractor.
Access setup is where convenience creates risk fastest. Create separate user accounts and keep primary admin ownership with your team. The FTC supports separate accounts and need-to-know access, and NIST supports restricting privileges to the minimum necessary. Turn on MFA anywhere the tool supports it. CISA says accounts using MFA are 99% less likely to be hacked, which makes it a strong safeguard, but not a substitute for narrow permissions.
| Access control | Article guidance |
|---|---|
| Separate accounts | Create separate user accounts and keep primary admin ownership controlled by your team |
| Need-to-know access | Restrict privileges to the minimum necessary |
| MFA | Turn on MFA anywhere the tool supports it |
| Pre-live test | Assign a test task, then confirm the assistant cannot see files, databases, or settings outside that task |
| Password sharing | If a password ever leaves your vault, treat it as a cleanup event |
Before real work starts, run one verification step: assign a test task, then confirm the assistant cannot see files, databases, or settings outside that task. A common failure mode is convenience sharing through messages or spreadsheets. If a password ever leaves your vault, treat it as a cleanup event.
As a control baseline, avoid letting the same person request, approve, and reconcile a purchase. Separation of duties is a checks and balances control, and for critical functions NIST also supports periodic reviews to confirm proper separation. Your control loop should name four things: the policy owner, the approval path, the exception log, and offboarding verification.
At minimum, define approved spend categories, the dedicated payment method, receipt timing, and what happens when something falls outside policy. Then close the loop now. When the relationship ends, verify access revocation, payment method removal, credential rotation, and file ownership transfer before you call offboarding complete.
After your contract, access plan, and spend rules are set, your next move is to stop delegating through chat and start delegating through a system. You need one Operations Manual plus SOPs that let your assistant complete repeat work to an auditable finish without depending on you for every clarification.
If recurring work is scattered across docs, messages, and voice notes, you do not have a reliable system. SOPs are meant for routine or repetitive work, so keep one searchable home for all repeatable tasks.
Keep it simple: one index, procedures grouped by function, and the current version clearly labeled. Use this test: can your assistant find the right procedure, confirm it is current, and start without asking where anything lives? If not, fix the structure before you add more tasks.
Write SOPs so execution is clear, not implied. A practical minimum template is:
| Field | What to write |
|---|---|
| Owner | Who is accountable for this SOP staying accurate |
| Version | Current version label |
| Trigger | Exact event that starts the task |
| Inputs | What must exist before work begins |
| Outputs | What must be delivered, where, and in what format |
| Exception path | When to escalate and to whom |
| Review owner | Who reviews quality and updates the SOP |
This is not a universal legal format, but it is a strong operating standard because it covers execution, accountability, and maintenance. Keep your handoff definition consistent: done means output delivered in the agreed location, correctly named, status updated, open issues logged, and next owner identified.
Document tasks in this order: repeatable first, then reversible, then lower-judgment work with visible QA.
| Task example | Repeatability | Reversibility | Judgment load | QA visibility | Document now? |
|---|---|---|---|---|---|
| Calendar scheduling and meeting prep | High | High | Low | High | Yes |
| Publishing approved content | High | Medium | Low to medium | High | Yes |
| Inbox triage with draft replies | High | Medium | Medium | Medium | After response rules are documented |
| Refunds, billing changes, vendor disputes | Medium | Low | High | Medium | Not yet |
| Admin account changes or privileged access work | Low to medium | Low | High | Low | Keep owner-only or tightly gated |
Use a simple rule: tasks with high repeatability and high QA visibility go first. For sensitive workflows, keep segregation of duties intact so one person does not request, approve, and reconcile the same action.
Most errors happen in edge cases, not happy paths. Put escalation criteria directly in each SOP.
| Done-state element | Requirement |
|---|---|
| Output | Delivered in the agreed location |
| Naming | Correctly named |
| Status | Updated |
| Open issues | Logged |
| Next owner | Identified |
Escalate when:
For account-based work, keep least-privilege access and avoid broad shared admin identities. If elevated access is needed, make it specific and removable.
Then run one live cycle and review against your written done-state. Every rescue question usually points to one issue: a missing step, a weak trigger, or an undefined exception.
Do not scale delegation after one clean run. Use ongoing checks and periodic review, and expect multiple test-and-revise cycles before you widen responsibility.
Before each scope increase, review:
If time reclaimed improves but rework or interruptions rise, treat it as a no-go. Tighten the SOP, retest, and expand only after the task runs clean without rescue messages.
Next action sequence: pick one recurring task, write the SOP, run one live cycle, revise from failure points, then move to the next task.
Use this 90-day window as a promotion policy: expand scope only when execution evidence stays consistently clean.
Start with work you can quickly verify and undo, such as calendar scheduling from approved inputs, formatting, meeting notes, research from public sources, and publishing from copy you already approved. In this phase, your goal is process reliability, not speed.
Move forward only when all three readiness signals are stable at the same time: SOP adherence, clean handoff artifacts, and reliable escalation behavior. Clean artifacts mean the output is in the agreed location, named correctly, status updated, open issues logged, and the next owner is clear. Reliable escalation means the assistant flags missing inputs, scope changes, or possible client impact instead of guessing.
If the task is "done" but artifacts are inconsistent or edge cases bounce back without a recommended next step, hold scope where it is and fix the process first.
Expand responsibility only with tightly scoped permissions and explicit approval ownership. Use least privilege and role-based access so access matches the task, not convenience.
Use a quick matrix to decide delegation mode by reversibility and impact:
| Task | Reversibility | Client impact if wrong | Approval owner | Delegation mode |
|---|---|---|---|---|
| Calendar scheduling from approved inputs | High | Low | You approve exceptions only | Assistant owns execution |
| CRM or project updates from approved source data | Medium | Moderate | You approve changes affecting scope or billing | Supervised ownership |
| Publishing approved content | Medium | Moderate to high | You keep final publish approval until stable | Supervised ownership |
| Refunds, billing changes, vendor disputes, admin account changes | Low | High | You approve and execute; assistant may prepare | Prep only |
For money movement, client commitments, or privileged access, keep separation of duties intact so one person is not requesting, approving, and reconciling the same sensitive action. Name one escalation owner, even if that is you, and require each escalation to include: what was found, what is blocked, and the recommended next step.
Review access quarterly and whenever role scope changes, then remove unneeded accounts promptly.
Shift to outcome ownership only after repeated clean execution in the earlier phases. Assign outcomes with deliverables, deadlines, inputs, quality checks, and approval gates instead of one-off chat instructions.
Require a completion pack each cycle: final deliverable, saved location, status update, exceptions raised, and one improvement note for the next run. If rework repeats, pause trust expansion and diagnose the root cause before you add scope.
Keep root-cause review simple: unclear instructions, access boundaries, or SOP gaps. Then apply corrective action to the actual cause: rewrite the brief, tighten permissions, or update the SOP and retest before the next promotion step.
You might also find this useful: Deep Work for Freelancers Who Run a Business of One.
You scale safely when you keep owner-level decisions and delegate documented execution. Your job is to hold the decisions that change risk, while your assistant runs repeatable work through clear controls.
Use this filter for every handoff:
This split also helps you keep compliance discipline. For U.S. classification context, treat the relationship as a whole: IRS analysis considers behavioral, financial, and relationship factors together, and FLSA analysis is also multi-factor across the full working relationship.
| Operating area | Owner bottleneck mode | Controlled delegation mode |
|---|---|---|
| Execution consistency | Work lives in memory and chat threads | Work runs from a task brief plus SOP/template |
| Review cadence | Reviews happen only after misses | Reviews are scheduled and tied to delivered output |
| Access governance | Permissions expand informally | Access is role-based and least-privilege by default |
| Decision bandwidth | Admin follow-up crowds out strategy | You spend time on approvals, priorities, and risk calls |
Before you trust any delegated workflow, require a completion pack with these artifacts:
Run a capacity check with current numbers, not static math. Fill in:
If repeatable work is still consuming owner time needed for sales, service design, or risk decisions, move one additional task only after access rules, review cadence, and escalation ownership are in place.
If your next gap is permissions and controls, use How to Onboard Your First Virtual Assistant With Boundaries, Least-Privilege Access, and Offboarding. For country/program fit questions, talk to Gruv.
Start with one recurring, tightly scoped task that is easy to review. Businesses often use VAs for recurring work to free internal staff from routine work and expand capacity without adding another full-time role. Your first handoff is a go only if all three checks are true: Scope is clear: the input, expected output, and done state are written down.. Review is easy: you can verify the result quickly without chasing context across messages.. Escalation is named: the assistant knows when to pause and ask for help.
Keep it simple: clear communication and one place to track tasks and deadlines. Many teams use a project tool such as Trello or Asana for this. | Tool category | Simple starting point | Failure signal | Upgrade trigger | | --- | --- | --- | --- | | Task tracking | One shared board or list in a project tool such as Trello or Asana | Deadlines slip or ownership is unclear | Add statuses, due dates, and one owner per task | | Communication | One primary channel with an agreed update format | Updates arrive in different places or lack next steps | Set one reporting cadence and one escalation path | | Task brief | One written brief linked to the task | Rework happens because context lives in chat | Convert repeat work into a simple SOP |
Start with the access needed for the current task, then verify it works before work begins. Cybersecurity risk is a common concern when hiring a VA, so review access as responsibilities expand. When output misses the mark, tighten the brief and communication expectations, then rerun the task on a small scope before widening responsibility.
A former tech COO turned 'Business-of-One' consultant, Marcus is obsessed with efficiency. He writes about optimizing workflows, leveraging technology, and building resilient systems for solo entrepreneurs.
Priya is an attorney specializing in international contract law for independent contractors. She ensures that the legal advice provided is accurate, actionable, and up-to-date with current regulations.
Educational content only. Not legal, tax, or financial advice.

Treat this as a protection problem first, not a label debate. If your work was treated as an independent contractor arrangement even though the relationship functioned differently, your first goal is to protect pay, rights, and records while you choose the least risky escalation path. You can do that without making accusations on day one, which often keeps communication open while you document what happened.

If you want to manage a global freelance team without constant cleanup, use the same intake-to-payout process for every engagement and save an artifact at each gate. Common failure points are instinct-based classification, vague scope, and payments approved in chat with no audit trail.

Move fast, but do not produce records on instinct. If you need to **respond to a subpoena for business records**, your immediate job is to control deadlines, preserve records, and make any later production defensible.