
Yes. Put ownership in signed contract language before work starts: client rights to the final deliverable, your pre-existing prompts and methods carved out as background IP. In U.S. deals, watch work-made-for-hire and assignment wording because delivery alone does not transfer copyright. Keep dated drafts, revision history, and a Human Authorship Log to document your edits. Share only necessary prompt fragments, and require NDA or confidentiality terms before exposing reusable systems.
Your real asset is rarely a one-off prompt. It is the reusable instruction system behind the work. From day one, split that system into two buckets: what you deliver to the client, and what you keep as your underlying method, including templates, chains, workflow logic, and process know-how.
That line matters because ownership does not work the way many teams assume. In U.S. law, rights generally vest in the author by default, but contracts can reallocate ownership when a work qualifies as made for hire or when assignment language is explicit and signed. Delivering files or outputs also does not, by itself, transfer copyright in the underlying IP. And with AI-assisted work, prompting alone is not enough to secure U.S. copyright in the output.
The biggest risks are usually easy to spot:
Quick self-check.
| Protected workflow | Exposed workflow |
|---|---|
| Contract says client owns final deliverables; you retain pre-existing prompts and methods | Contract sweeps in "all materials" with no carveout |
| Prompt library is access-controlled | Core prompts are broadly shared in client-facing spaces |
| You keep dated versions and revision records | No timestamped record of what you created |
| You share only necessary prompt fragments | You share full reusable chains by default |
Run two checks now. First, confirm whether your contract uses work-made-for-hire or assignment language. Second, confirm where your best prompt assets are stored and who can access them. Those two checks usually tell you where the real exposure is. Contract terms shape ownership, evidence control supports your authorship position, and secrecy control protects the reusable parts that create long-term value.
You might also find this useful: Ethical Considerations of Using AI in Creative Freelance Work.
Ownership often turns on three things: your human contribution, your relationship to the hiring party, and the contract you signed. If you blur those together, small drafting mistakes can turn into ownership fights later.
Start with definitions, because ownership disputes often come from people using the same words to mean different things in the same contract or email chain.
| Term | Meaning | Key point |
|---|---|---|
| Human authorship | Your own creative contribution, such as creative arrangements or modifications | Prompting alone is not enough, and there is no fixed edit count that guarantees protection |
| AI-assisted output | Work created with AI as part of your process | AI use does not automatically block protection for the human-authored parts of a larger work |
| Prompt text | Your written instruction to the model | It is an input, not automatic proof that you own the output |
| Final deliverable | What you hand over, such as a file, deck, or document package | Owning that file is legally different from owning copyright in it |
For U.S. copyright analysis, keep those labels distinct. Human authorship means your own creative contribution, such as creative arrangements or modifications. AI-assisted output is work created with AI as part of your process. Prompt text is the instruction you give the model, and final deliverable is what you hand over. Prompting alone is not enough, AI use does not automatically block protection for the human-authored parts of a larger work, and owning a file is legally different from owning copyright in it.
Work through ownership in sequence, not by instinct. That keeps delivery, authorship, and transfer from getting collapsed into the same question.
If you plan U.S. registration and the work includes AI-generated material, you must disclose that inclusion.
The default starting point can change quickly depending on whether you are an employee or an independent contractor, and which jurisdiction governs the work.
| Relationship type | Jurisdiction example | Default starting point | Verify before signing |
|---|---|---|---|
| Employee acting in course of employment | U.S. | Employer or hiring party may be treated as author under work-made-for-hire rules | Job scope, IP policy, and any written carveout for your pre-existing materials |
| Independent contractor | U.S. | Author generally starts as owner by default unless rights are reallocated by signed writing | Work-made-for-hire language, assignment terms, and carveouts for your pre-existing prompts/methods |
| Employee acting in course of employment | UK | Employer is first owner for in-scope employment works | Whether the work is within employment duties and whether contract terms change the default |
| Freelancer/contractor under a contract for services | UK | Creator usually retains copyright unless otherwise agreed; commissioned work does not automatically vest in the commissioner | Whether the contract includes assignment or license language; do not assume payment alone transfers ownership |
If your contract labels you a contractor but also includes work-made-for-hire and assignment language, treat those clauses as the control point.
Cross-border work is where casual assumptions break down. Check three controls separately:
Get local counsel review when those controls point to different countries, when employee versus contractor status is unclear, or when cross-border assignment language is broad but not precise.
Once those basics are clear, turn them into contract language that says exactly what you keep, what the client gets, and what is only licensed.
If you want a deeper dive, read Work for Hire vs. Assignment of Rights: A Freelancer's Guide to Owning Your IP.
If the contract is loose, everything else is cleanup. Your first job is to define what you already own, what the client is actually buying, and what they are only getting permission to use.
Put these definitions near the top of the agreement so later clauses cannot swallow them through ambiguity:
Then state the split plainly. The client gets rights to the deliverable. You retain all rights to your pre-existing or background IP, including prompts, prompt chains, evaluation methods, and reusable structures used to produce it. Under U.S. law, delivery of a file is not the same as transfer of copyright.
| Common contract language | Outcome | How to revise |
|---|---|---|
| "Contractor retains all right, title, and interest in pre-existing IP and background IP. Client receives a nonexclusive license to use the deliverables for the agreed purpose." | Usually protects your tools and keeps the grant narrow | Keep, then specify scope, territory, duration, and reuse rights |
| "All work product, materials, ideas, methods, prompts, and outputs created or used in connection with the services belong to Client." | Overbroad capture of your methods and prompt library | Add a carveout for pre-existing/background IP and limit client rights to deliverables |
| "Work made for hire. If not, Contractor hereby assigns all rights." | Under U.S. law, can shift authorship or ownership to the hiring party if legal conditions and signed writing requirements are met | Remove unless you intend a full transfer; use a defined license if broad use is needed |
A reverse-engineering restriction can help, but it will not carry the whole load. You want a stack of clauses that works together:
If AI vendors are in scope, verify current plan terms before signing. Defaults can differ by product and policy version, so save the plan or policy date in the deal file.
If the client does not need ownership, do not give it away by habit. Rights can be split cleanly, so define only what the project actually needs:
| Element | What to define |
|---|---|
| Scope/field of use | What uses are allowed |
| Territory | Where use is allowed |
| Duration | How long the rights last |
| Exclusivity | Exclusive or nonexclusive |
| Reuse rights | Whether you can reuse your methods and non-client-specific components |
That keeps the grant tied to the engagement instead of handing over more than the work requires.
For exclusive licenses, assignments, or jurisdiction-specific formalities, verify the current local requirements before you sign.
Pre-signing checklist. Use this before every signature, especially when the draft came from the client:
If any of those points are vague, treat that as a risk and tighten the clause before you sign. Related: AI and Copyright: Legal Implications of Using AI Content in Client Work.
Before you sign your next client deal, draft ownership and usage language you can redline fast with the Freelance Contract Generator.
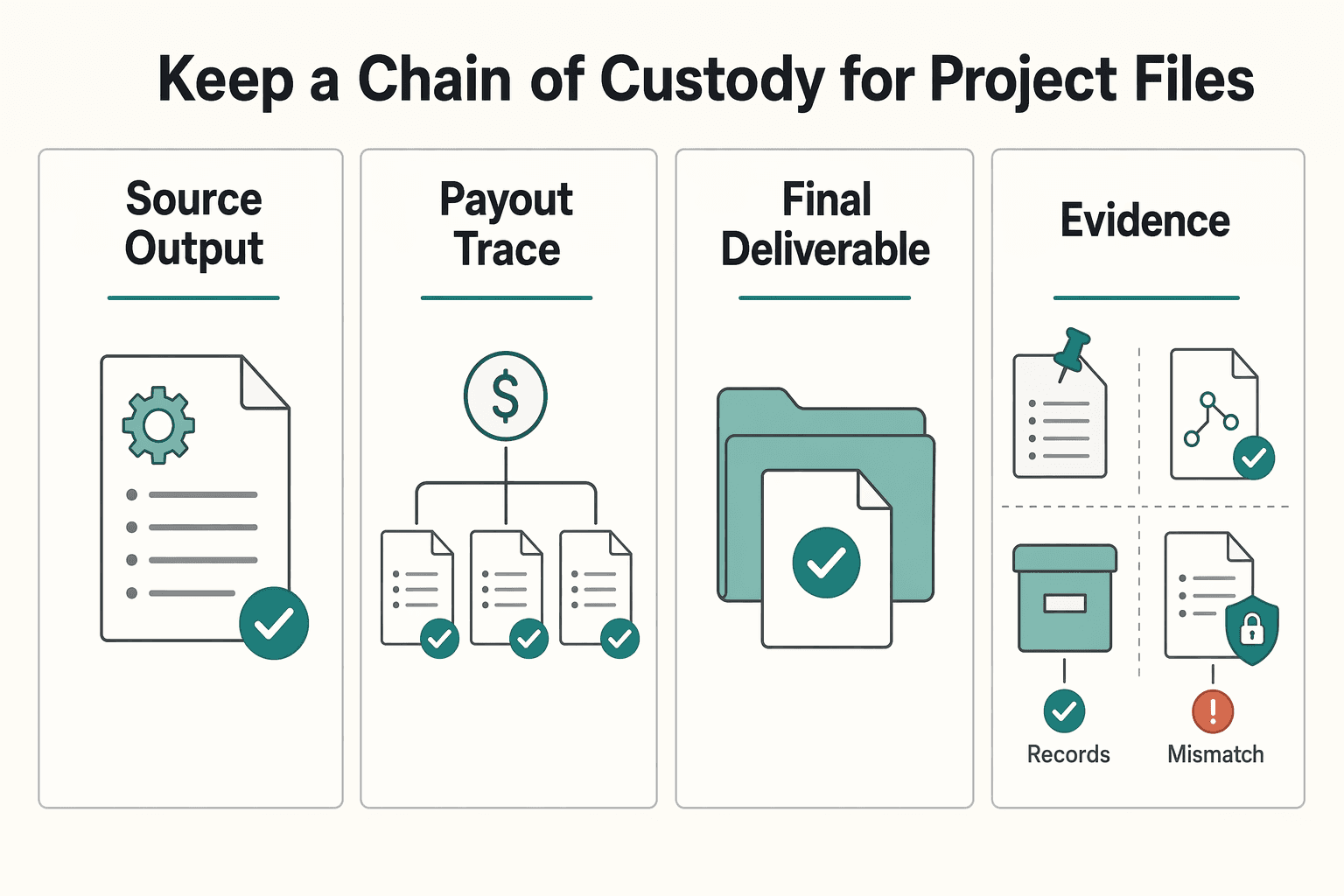
A good contract sets the rights. Your records help prove them. If ownership is ever challenged, a polished final file may not be enough on its own.
Provenance matters. Dated drafts, prompt revisions, raw outputs, and milestone snapshots usually provide stronger support than a summary reconstructed after the fact.
Build three trails on every project. The cleanest approach is to keep three linked trails on every matter:
Think in evidence-pack terms, not portfolio terms. A tidy summary is useful, but a complete bundle of files, notes, and timestamps is usually stronger.
Do not rely on memory here. Use one repeatable log per project and update it at meaningful milestones.
| Field | What to record |
|---|---|
| Prompt intent | What you were trying to achieve, for whom, and key constraints |
| Key human edits | What you changed in prompt, structure, selection, tone, or sequence |
| Why your choices changed the result | How your edits improved fit, clarity, usefulness, or reduced risk |
| Supporting files location | Where raw outputs, drafts, exports, screenshots, and approvals are stored |
Keep entries short and factual. Useful: "Rewrote Section 3 to remove unsupported claims and align to client style guide." Not useful: "Improved quality."
If you used retrieval or client documents, log that too. Your contribution may include how you selected and organized source material, not just the wording of the prompt.
If a dispute ever lands on your desk, you want a record that is easy to follow and hard to pick apart. Save proof at each stage.
| Stage | What to save | What to verify |
|---|---|---|
| Source output | Initial model outputs, prompt inputs, screenshots when history export is unavailable | Captured before edits; timestamps and filenames intact |
| Working drafts | Successive drafts, edit notes, comparison files | Changes are traceable across versions |
| Final deliverable | Exact file/package delivered to the client | Matches agreed scope and delivery timing |
| Approval record | Approval email, resolved comments, acceptance message, or signoff | Approval ties to the exact final version |
Two failure modes to watch for are overwriting the baseline and keeping all records only in client-controlled systems. If your contract and confidentiality terms allow it, keep your own archive copy.
Also avoid records that exist but cannot be interpreted or exported reliably. If the evidence is messy or locked inside a tool, it is harder to defend later.
Choose tools for defensibility, not convenience. Convenience matters less than whether the record will stand up when you need it. Use this check before choosing storage or drafting tools:
If exportable history is weak, add manual checkpoints such as dated exports, screenshots, and milestone snapshots. If output looks near-verbatim from unknown source material, treat it as a provenance risk and revise before delivery.
Documentation helps demonstrate contribution. The next layer protects something different: the reusable methods and prompt assets you need to keep out of general circulation.
For a step-by-step walkthrough, see Retain Portfolio Rights Without Reopening the Whole Contract.
Trade secret protection works only if you treat the material as actually secret. Your prompt library, testing patterns, evaluation notes, and internal methods can be protected when they have economic value because they are not generally known and you use reasonable confidentiality controls.
Set that boundary in every engagement. The client buys the deliverable and the usage rights you agreed to. Unless the contract explicitly says otherwise, they do not buy your full prompt system, internal methods, or reusable library.
Know what you are protecting. A simple working test helps here: if disclosure would let someone skip the time and cost you invested to build the asset, keep it confidential by default. Trade secret protection depends on both value from secrecy and real protection steps, and what counts as "reasonable" depends on context.
| Asset type | Who gets access | What can be reused | What must stay confidential |
|---|---|---|---|
| Trade secret asset | You and approved collaborators on a need-to-know basis | Reusable across clients unless a contract limits reuse | Full prompt library, internal testing methods, decision trees, reusable templates |
| Client-facing deliverable | Client users defined in the contract/SOW | Client use stays within licensed scope | Remove hidden prompts, internal notes, and unused background materials before delivery |
| Background IP | You, unless separately assigned or licensed | Reusable in future work | Nonpublic methods and source materials not included in the licensed deliverable |
Casual sharing can weaken trade secret protection. Require NDA or confidentiality terms before sharing nonpublic methods with prospects, subcontractors, or partners. If they only need proof of approach, share redacted excerpts. If they want the full library, treat that as a separate license with tighter confidentiality and explicit use limits.
Use this rule set:
NDA/confidentiality required: before any nonpublic method, library structure, or reusable system discussion.Redacted excerpt only: when trust-building is the goal, not transfer of your system.Full disclosure by separate license: when the client wants to run your system without you.Storage alone is not enough. Run least-privilege access, keep logs showing who accessed what, when, and from where, and review permissions at milestones and closeout. Apply these controls consistently:
If secrecy controls break down, trade secret status can be lost and may not be recoverable. We covered this in detail in Creative Commons for Freelancers Without Client Contract Conflicts.
Treat this as an operating discipline, not a theory exercise. In client work, protection comes from three controls working together: signed ownership terms, authorship records, and confidentiality controls.
Layer 1. Lock ownership before work starts. Under U.S. copyright defaults, ownership starts with the author unless a valid exception or transfer applies, and assignments must be in signed writing. If a draft uses work-made-for-hire language or sweeps in "all prompts, methods, templates, tools, and know-how," split the final deliverable from your background IP and prompt library in signed terms. Outcome: clear ownership, license, and transfer boundaries.
Layer 2. Make your human contribution provable before delivery. Keep version history, edit notes, and a Human Authorship Log showing your selection, editing, arrangement, rewriting, and other human input. That record supports your position if copyrightability is challenged. It also helps with U.S. registration steps, where machine-generated traditional authorship elements are not treated as human authorship and, where AI-generated material is more than de minimis, disclosure plus a brief explanation of your contribution is required in current guidance. Outcome: evidence you can defend.
Layer 3. Treat internal methods as confidential assets before sharing them. A prompt library can be protectable as confidential business information when it is secret, commercially valuable because it is secret, and protected with reasonable secrecy steps. Use NDA or confidentiality terms before disclosure, limit access to need-to-know people, and share redacted excerpts when full access is unnecessary. Outcome: controlled confidentiality you can enforce.
Your three checkpoints.
Operate this way and you are better positioned to retain control of your background IP, not just act as a one-off output provider. Jurisdiction-specific rules still need to be verified before you rely on any conclusion.
This pairs well with our guide on Structuring the Intellectual Property Clause in an SOW for a Freelance AI/ML Engineer.
If you want to operationalize these IP safeguards in a cross-border money workflow with clear records, talk to Gruv.
Protect clear ownership buckets in the contract so boundaries are explicit. Use prompt for the instruction text you give an AI system and prompt library for your reusable collection. Also define key terms like deliverable, background IP, and whether rights are a license or an assignment so scope is clear. If those labels are missing, broad language like "all work product" can create ambiguity.
Set ownership in the contract instead of assuming defaults. A common structure is for the client to own, or receive broad rights in, the final deliverable while you retain pre-existing methods and reusable prompt assets unless you explicitly transfer them. If a draft gives the client "all prompts, methods, templates, tools, and know-how used or developed," treat it as potentially overbroad and revise it before work starts.
No. Prompt text may be protectable only when it is original and created with at least minimal skill and judgment, and there are also arguments against copyright protection for prompts in some cases. If a prompt is commercially important, do not rely on copyright alone. Trade secret controls are often the more practical path.
Do not assume that entering a prompt, by itself, settles output ownership. The materials here focus on prompt IP and do not provide definitive jurisdiction-specific rules for output authorship. For high-value or cross-border work, get legal advice before relying on ownership assumptions.
Yes. Contract language is a primary control. It can state where prompt IP created for the engagement vests and what, if anything, is transferred beyond the deliverable. If you intend to keep your pre-existing library and methods, say that explicitly.
Refuse transfer when the client needs the result but not your internal method, or when transfer would hand over a core commercial asset without separate value. If they truly need access, treat it as a separate deal and use confidentiality terms, scoped access, and clear use limits.
Yes, if it has economic value because it is not generally known and you apply secrecy measures in practice. A library can often be protected as confidential know-how when secrecy controls are real and consistent. You keep that protection only if you control access and avoid casual disclosure.
You should be able to show reasonable measures to keep the material secret, not just label it confidential. A practical check is whether you used confidentiality terms before disclosure and limited access to people who needed it.
A common failure mode is misappropriation by departing employees or contractors who take prompt assets for their own use or to compete. Protect yourself by keeping records of who had access, what was shared, when access ended, and whether the materials were handled as confidential.
Escalate when ownership language is broad or unclear, when the deal is cross-border, or when the client asks for transfer of your full library. Verify jurisdiction-specific ownership and transfer rules before you sign.
A successful freelance creative director, Sofia provides insights for designers, writers, and artists. She covers topics like pricing creative work, protecting intellectual property, and building a powerful personal brand.
Priya is an attorney specializing in international contract law for independent contractors. She ensures that the legal advice provided is accurate, actionable, and up-to-date with current regulations.
Educational content only. Not legal, tax, or financial advice.

A freelance agreement is not just about price and scope. It decides who controls the rights in the work. If the ownership language is loose, rights can move earlier than you expect, cutting down your control once the work is delivered or used.

You can use generative AI in client work, but only if copyright risk is treated as a delivery requirement from day one. The practical question is not whether you can use AI. It is whether you can defend human contribution, ownership intent, and jurisdiction before production starts.

The ethics of AI in creative work shows up in delivery choices, not theory. Decide AI boundaries, disclosure expectations, and contract terms before work starts.