
Build your process around the trust-to-transaction business model by proving reliability before work starts, removing approval friction before signature, and standardizing delivery after kickoff. In practice, that means sending correct invoice data, handling required forms such as W-8BEN or VAT reverse-charge wording when relevant, and giving clients a clear onboarding path with named contacts and decision points. The model works because buyers are judging both your skills and the operating setup behind them.
If you sell your work across borders, clients are buying certainty as much as skill. The trust-to-transaction model is a simple operating rule: make it easy for a client to see that working with you will be orderly, legible, and low drama. The real friction is usually not whether you can do the work. It is whether hiring you will create admin, payment, or communication problems they will have to clean up later.
Treat it as the way your business runs, not a branding idea. Trust is not a vague feeling. In practice, it is the reduction of perceived risk through signals a client can check: clean invoicing, early document handling, a clear onboarding packet, consistent communication, and tools that do not leave finance or procurement guessing.
Research on trust in information systems is useful here because it separates trust in people from trust in technology. In plain English, a client is judging both you and the machinery around you. They may like you on a call but still hesitate if your document flow feels improvised, your payment method looks awkward, or your files arrive with no structure.
That distinction matters. The underlying construct was empirically examined with convergent, discriminant, and nomological validity tests. The useful takeaway is simpler: "I seem trustworthy" and "my operating setup feels trustworthy" are not the same thing. In cross-border work, you usually need both.
The pattern is straightforward. A client often starts with risk questions: Will this supplier invoice correctly, send the needed paperwork, communicate clearly, and fit our internal process? You address those concerns with operational proof, not reassurance alone. Once that proof is visible, the engagement is easier to approve internally and less likely to stall in back-and-forth.
The strongest trust signals are boring on purpose. You send invoices that match the client's stated finance requirements. You provide requested vendor documents early instead of waiting to be chased. You begin with a short onboarding pack that explains who the legal contracting party is, where notices should go, how billing works, what your communication rhythm will be, and what you need from them to start.
Consistency is a useful checkpoint. Before kickoff, verify that your business name, payment details, scope wording, and contact information match across your proposal, contract, invoice template, and onboarding materials. A common failure mode is looking polished in the sales conversation but creating doubt with mismatched details, vague payment instructions, or unclear handoffs once the deal is supposed to become real.
For some clients, data-handling expectations become part of that proof too. It helps to have a clear answer ready and, if relevant, a more detailed reference such as GDPR for Freelancers: A Step-by-Step Compliance Checklist for EU Clients.
| Client concern | Weak practice | Stronger operational behavior |
|---|---|---|
| "Will finance be able to process this supplier?" | Sending a generic invoice and asking the client to fix any issues | Sending invoice details in the format the client requests and confirming requirements with their finance team |
| "Will vendor setup become a chase?" | Waiting until payment is blocked to mention missing documents | Asking upfront what onboarding documents are required and supplying them early, with requirements verified |
| "Will communication become messy once work starts?" | Ad hoc updates spread across email, chat, and calls | Setting a simple reporting rhythm, named points of contact, and a clear place for decisions and approvals |
| "Are this provider's tools and process reliable?" | Using unfamiliar tools with no explanation or fallback | Explaining how contracts, file sharing, approvals, and billing will work so the client trusts both you and the process |
The goal is not to look corporate. It is to make risk legible and manageable for the person buying from you. Transactions are, at root, communication exchanges. Those exchanges usually go better when your patterns are clear and predictable instead of reactive.
As an operating sequence, think in three stages. First, you prove competence with visible signs that you know how to operate. Next, you remove enough financial and administrative friction that saying yes feels easier. Then you make that reliability repeatable so trust survives beyond the first project.
You might also find this useful: A guide to 'Antifragile' thinking for building a resilient freelance business.
In Stage 1, you prove reliability before the first invoice is due. You are not asking to be trusted; you are reducing perceived risk with clear, checkable signals the client can validate quickly.
Clarity is the baseline. When expectations, responsibilities, and admin details are aligned early, you avoid the gaps that create mistrust later.
Your first trust test is operational, not personal: can finance process you without confusion? Use this invoice-readiness checklist before you send anything:
| Check area | What to verify |
|---|---|
| Your details | Legal business name, address, contact email, invoice number, issue date, and payment due date |
| Client details | Client's correct legal entity name, billing address, and any vendor reference or purchase order they requested |
| Service details | Clear service description, billing period or dates, currency, subtotal, taxes (if applicable), and total due |
| Payment instructions | Match your contract and account details |
| Client type and pre-payment documents | Confirm whether the client is an individual, a local business, or a foreign corporate entity, and whether pre-payment tax/vendor documents are required |
| Jurisdiction-specific language | Registration detail pending jurisdiction verification. |
For tax and vendor setup, use a simple decision path and verify requirements before kickoff:
Completeness is the checkpoint. When IRS authorization paperwork is relevant, IRM 21.3.7 explicitly references Form 2848 and Form 8821 and includes an "Essential Elements" subsection. Apply that same discipline to your own document flow: complete beats mostly done.
Make your competence easy to inspect. Each proof asset should close a specific trust gap:
| Proof asset | What it shows |
|---|---|
| Case study | Lowers perceived risk by showing how you handled constraints and decisions in real work |
| Technical note | Shows depth so the buyer can see you can execute without heavy hand-holding |
| Public contribution (article, template, or open project contribution) | Builds credibility by making your thinking visible before purchase |
The rule is fit: choose the proof that answers the buyer's current concern, not the proof that only looks impressive.
Use a fixed onboarding sequence: intake, scope confirmation, compliance documents, then communication cadence. That keeps gaps from surfacing late, when trust is hardest to recover.
| Reactive onboarding | Standardized onboarding |
|---|---|
| Scope is discussed loosely across messages | Scope is confirmed in one written document with responsibilities and deliverables |
| Tax/vendor paperwork appears only after payment gets blocked | Compliance documents are requested and sent before work starts |
| Updates happen ad hoc | Update rhythm, point of contact, and approval path are set at kickoff |
| Client must infer your process | Client sees a repeatable operating pattern |
If you use one Stage 1 rule, use this: anything needed to approve, onboard, or pay you should be ready before the client asks. For a step-by-step walkthrough, see A Guide to Building a 'Trust-First' Product Roadmap.
At this stage, your client is asking one thing: can finance, procurement, and legal approve you without extra risk or rework? Your job is to remove ambiguity before internal review starts.
Cross-border payments get more scrutiny because teams use risk-based review, not the same review for every transaction. That means legitimate payments can still get delayed when names, bank details, contract terms, or tax paperwork do not line up cleanly. In practice, Stage 2 is about making those details consistent and easy to verify.
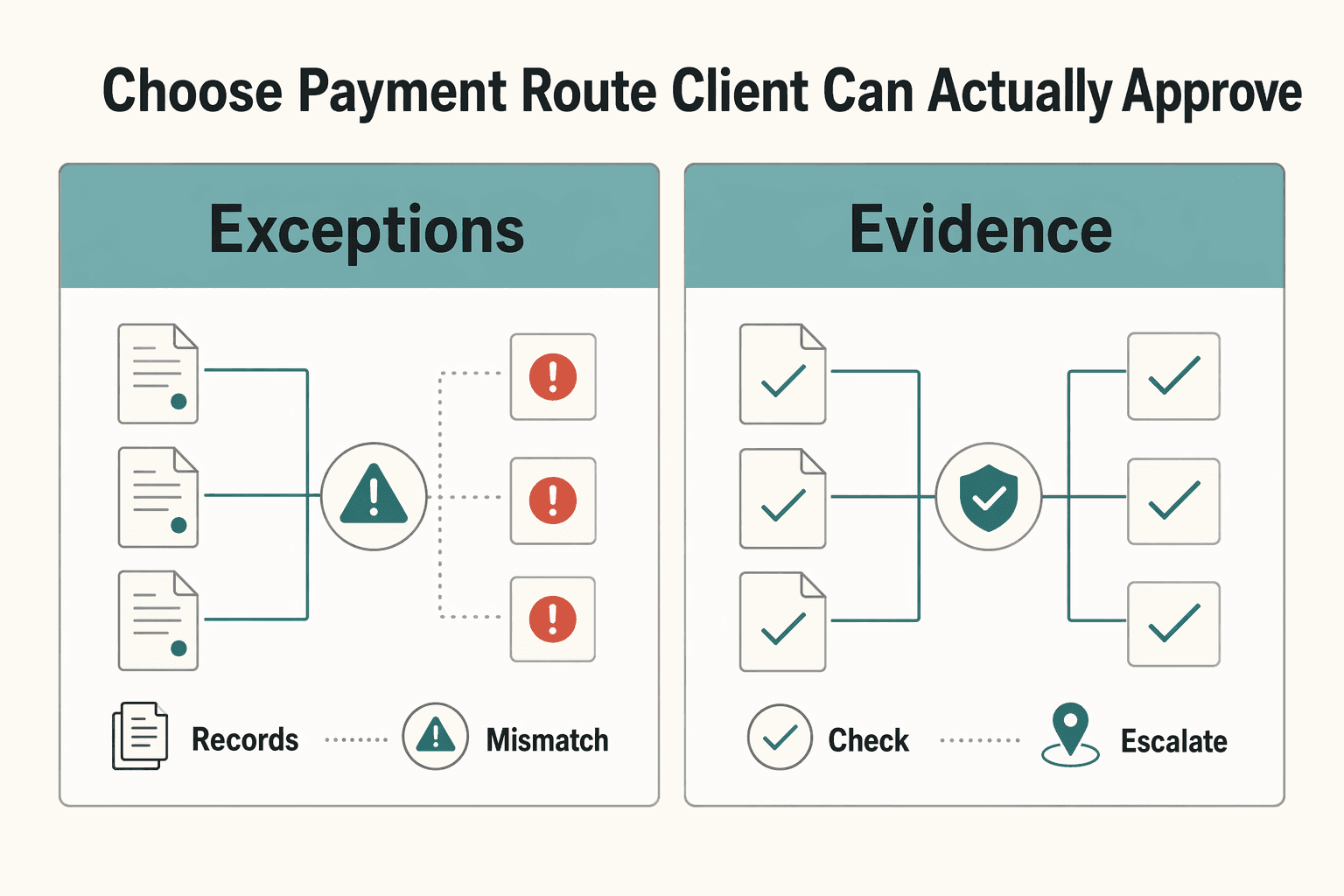
Pick the route your client can process with the fewest exceptions, then explain it in their internal language.
| Payment route | Client risk | Your control | How to communicate it |
|---|---|---|---|
| Direct transfer | Client must validate a foreign vendor, bank details, and supplier/tax paperwork; mismatches can delay payment. | High control over your invoice pack and bank instructions, low control over their internal approvals. | "If your AP team already pays international contractors directly, I can send a complete vendor pack upfront, including the registration, tax, or vendor details your team confirms are required." |
| Platform-managed flow | Client adds a third party to review, but may avoid building a new overseas payee process from scratch. | Medium control. You still own scope and contract terms; the platform manages part of payment operations. | "If direct vendor setup is slow on your side, we can use a managed payment flow so finance can follow a more familiar path. Before we use that route, I will confirm any required registration, tax, or vendor documentation with your finance team." |
| Merchant-of-Record | Some cross-border admin can shift away from the client, but procurement may need clarity on counterparty and documentation trail. | Lower control over buyer-facing payment steps, higher consistency if the provider standardizes invoicing and collection. | "If you want one payment counterparty and standardized documentation, we can route billing through a Merchant-of-Record. We should verify the required counterparty, tax, and vendor documentation with procurement before using that route." |
Before signature, give the client a contract they can defend internally without extra calls. A useful model is the discipline you see in structured clause systems: keep instructions, responsibilities, and clause text explicit so reviewers are not left guessing.
| Contract check | What to define |
|---|---|
| Scope boundaries | What is in scope, out of scope, and what triggers a change request |
| Acceptance criteria | What "done" means, who approves it, and when |
| Payment mechanics | Currency, invoice cadence, due dates, and chosen payment route |
| IP and confidentiality | What transfers, what you retain, and what each side must protect |
| Exit terms | Pause/termination steps, handoff expectations, and treatment of unfinished or prepaid work |
Two checks reduce avoidable friction fast. First, make sure the legal entity name in the contract, the invoice name, and the bank beneficiary name match exactly. Second, if classification concerns come up, describe the work as defined deliverables with review points and a clear end or renewal decision, rather than open-ended support language. Related: The 'Autonomy Premium': Why High-Earners Choose Freelancing Over Stability.
Approval is only the start. Long-term trust comes from reliability the client can see, not reliability that depends on memory or last-minute effort.
The public scrape for Dariusz Pieńkowski's 2011 paper A Holistic Framework for Trust in Online Transactions is login-gated, so it does not add usable operational detail here. What the client can actually evaluate is your visible system.
Use one documented flow from intake to delivery to closeout, and reuse it across engagements:
[scope owner to confirm], [acceptance owner to confirm])[QA method to confirm])[risk trigger threshold to confirm], [escalation contact to confirm])[access-transfer checklist to confirm])Before moving from intake to production, confirm scope, owners, source files, access, and acceptance criteria in one place. If any policy item is client-specific, leave it as a clear placeholder until verified.
| Lifecycle phase | Ad hoc execution | Automated reliability | Client experience | Operational risk | Retention impact |
|---|---|---|---|---|---|
| Intake | Context split across messages | Single intake record and brief | Less repetition | Fewer setup gaps | Stronger first impression |
| Delivery | Progress tracked informally | Reused templates + QA checkpoint | Clearer progress | Lower missed-step risk | More confidence to continue |
| Communication | Updates sent only on request | Agreed update format at agreed checkpoints ([cadence to confirm]) | Less chasing | Earlier issue visibility | Better continuity |
| Closeout | Files sent without a standard package | Final asset transfer + handover notes + re-engagement trigger | Easier handoff | Lower transition friction | Cleaner path to next project |
Keep updates predictable and brief so the client does not need to chase status. At each agreed checkpoint, send:
[decision date to confirm])When risk appears, flag it early and include a proposed path, not just a warning.
Close each project with a repeatable package:
[review window to confirm])If someone new had to pick up the work tomorrow, they should be able to continue without digging through old threads. That is how completed work turns into durable trust and repeatable partnerships.
Your work proves you can solve the problem. Your operating habits show whether clients can hire, pay, and trust you without extra supervision. That is the real shift: you are not just delivering tasks; you are maintaining a business identity every time a client reads your updates or tries to understand how the work will move.
That idea holds up beyond solo work. A May 2024 study of Tideway in the United Kingdom found that organizational identity is both crafted and maintained in a temporary, multi-organization setting, not declared once and left alone. The study describes five crafting dimensions and four maintaining elements as integrated practice. For you, the practical takeaway is to pair consistent operating routines with clear stakeholder communication and adaptation when conditions change.
The systems that support this can stay simple: repeatable workflows, clear communication norms, and lightweight support structures you can run consistently. Treat them as risk controls, not admin clutter. Review them on a schedule and again before each new engagement so your process stays current and coherent. A stale process or mismatched expectation can create doubt fast.
Start with the weakest process first. If prospects go quiet after a proposal, tighten how you communicate scope, responsibilities, and next steps. If deals close but delivery feels improvised, fix onboarding and status updates. Improve one weak point, use the better version repeatedly, and then move to the next. That is how you stop acting like a solo executor and start running a business clients can trust.
We covered this in detail in The Future of the Agency Model in the Age of AI.
Reduce administrative uncertainty before anyone has to chase you. Send the paperwork and payment details early, including your legal business name, payment method, and any client-requested tax form or invoice fields, such as a W-8BEN or EU VAT reverse-charge wording where applicable and verified for that jurisdiction. Keep a current onboarding folder with your tax form, invoice template, bank or payout details, and a short checklist to verify client-country rules each time, because reusing an old template with the wrong tax ID or missing clause can stall approval.
It looks like a controlled buying process, not just good advice. Give the buyer a small proof asset first, then move them through a clear engagement path such as a discovery memo, scoped proposal, contract, and kickoff meeting with named owners and review dates. Before onboarding, have one sample diagnostic, one proposal template, one contract template, and a kickoff agenda that captures scope, source data, decision maker, and acceptance criteria in one place so the brief does not end up split across threads.
Yes. The pattern stays the same, but the proof should match your role. A software developer can show maintained repository contributions, issue responses, and release notes. A brand designer can show a structured intake form and final file handoff checklist, while a solo operations or finance consultant can share a sanitized reporting pack, review memo, or audit checklist.
Make the basics easy to verify. Use a business email, keep your legal or trading name consistent across documents, invoice from a dedicated business account, and run a documented onboarding process with a welcome note, kickoff agenda, and status update cadence. Keep your invoice template, onboarding packet, and compliance notes together, and verify any tax, privacy, or invoicing language that changes by jurisdiction before you send it.
Up front, yes. Over time, it can replace chasing with preparation. Shift more of your effort into reusable proof, paperwork, and onboarding assets, then maintain them instead of relying mainly on repeated pitching and follow-up. Keep a current case study, proposal template, invoice template, and intake-to-kickoff checklist, and re-check any rule-based language before you send it because requirements and interpretations can change over time.
Chloé is a communications expert who coaches freelancers on the art of client management. She writes about negotiation, project management, and building long-term, high-value client relationships.
Educational content only. Not legal, tax, or financial advice.

Start by separating the decisions you are actually making. For a workable **GDPR setup**, run three distinct tracks and record each one in writing before the first invoice goes out: VAT treatment, GDPR scope and role, and daily privacy operations.

Use focused time now to avoid expensive mistakes later. Start with a practical `digital nomad health insurance comparison`, then map your route in [Gruv's visa planner](/tools/visa-for-digital-nomads) so we anchor policy checks to your real plan before pricing pages pull you off course.

Freedom only pays off when control keeps pace. Freelancing happens project by project outside a single employer structure, so you need explicit rules for scope, pacing, and follow-through. Freedom without structure turns into chaos. Durable independence comes from controls you can repeat, not motivation spikes.