
Yes. The defend trade secrets act dtsa can apply to freelancers and consultants when confidential information has value because it is not public, you protect it with real controls, and the work connects to activity across states or countries. Start by naming exact assets such as pricing logic or delivery playbooks, then document access limits, contract terms, and project closeout records. If misuse appears, preserve evidence first and involve counsel early before choosing an injunction or damages path.
If you run a solo or small service business, the more common legal risk is not dramatic theft. It is routine exposure of non-public know-how during everyday client work. It shows up in shared folders, subcontractor access, proposal drafts, copied templates, reused code, or a former collaborator reusing your method.
That is where the DTSA can matter. In plain terms, it creates a federal civil path when a trade secret is misappropriated. An individual can qualify as an owner because the statute covers a "person or entity." The limits are straightforward: the information must have economic value because it is secret, you must take reasonable measures to keep it secret, and the claim must involve information used in, or intended for use in, interstate or foreign commerce.
For freelancers and consultants, assets that may qualify as trade secrets are often hiding in plain sight: client lists, pricing logic, delivery playbooks, code, and internal workflows. These matter because they can improve margins, speed delivery, improve quality, or make your scoping more accurate than competitors.
Your first job is not to think about litigation. It is to identify what is protectable, apply reasonable controls, and prepare for misuse. Use this checkpoint: can you name the exact assets, explain their business value, show who had access, and produce the confidentiality terms that applied? Before enforcement matters, you need a defensible inventory and documented controls. Related: How to Protect Trade Secrets When an Employee Leaves.
You do not need to be a large company to think about the DTSA. The real question is whether you can identify and document specific information, show how it connects to work used in interstate or foreign commerce, and show what reasonable measures you used to protect it.
That is why the inventory step is not optional. In a dispute, one of the first questions is usually whether you can identify the exact information and show how you safeguarded it.
Your NDA is the contract promise around confidentiality obligations. The DTSA is the federal civil enforcement path for misappropriation.
Use them together. The NDA can help set notice and scope. The DTSA can provide a federal cause of action when the facts support a trade secret claim. But an NDA breach does not automatically become a DTSA case, especially if the information was public, loosely handled, or not protected with reasonable measures.
Since May 11, 2016, the DTSA has provided a federal civil remedy for trade secret misappropriation. If your client work spans states or countries, a federal forum can be easier to coordinate than relying only on separate state routes.
Keep the limit in view. The DTSA does not replace state trade secret law. Also, emergency ex parte seizure exists only in "extraordinary circumstances," and a wrongful request can create damages exposure.
Nothing qualifies by label alone. The same kind of information may qualify in one fact pattern and fail in another.
| Asset type | Why it may qualify as a trade secret | Common freelancer scenario |
|---|---|---|
| Documented non-public information | Specifically identified and documented before a dispute starts | A consultant keeps a dated inventory that describes the exact information treated as secret |
| Information tied to interstate or foreign commerce work | Related to a product or service used in, or intended for use in, interstate or foreign commerce | A freelancer provides services across state lines or to international operations |
| Information protected with reasonable measures | Safeguarded with concrete confidentiality and access controls | A contractor limits access, uses confidentiality terms, and tracks who can view sensitive material |
This does not cover public know-how, public processes, or methods already disclosed without protection. From here, the practical move is to identify your specific protectable assets and separate them from general experience.
Start with an intake process. Your position is stronger when you can identify specific information, show its value comes from secrecy, and show you have rights in it.
Create one intake row per asset and capture three basics first: where it lives, who can access it, and how secrecy creates commercial value. Then record ownership clearly (your title, license, shared rights, or client-owned). DTSA definitions are broad enough to cover business, financial, technical, economic, and engineering information in physical or electronic form, but broad categories alone are not enough.
For each candidate asset, record:
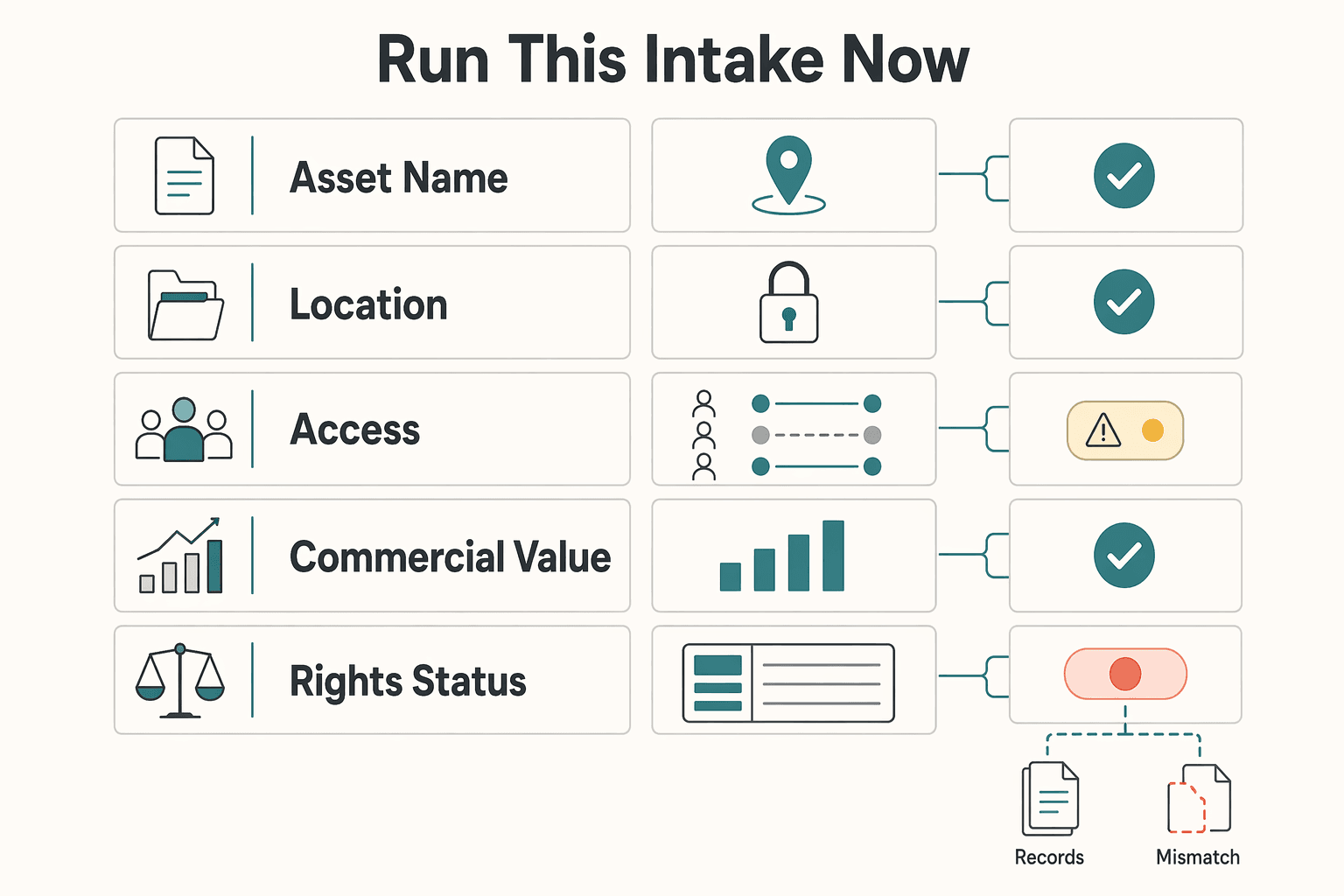
| Field | What to record | Article detail |
|---|---|---|
| Asset name/version | Exact asset name/version | not a vague label like "my process" |
| Location | Current location | drive, cloud folder, repo, CRM, notebook, email, client portal |
| Access | Current access | collaborators and anyone who still has old access |
| Commercial value | Business advantage from secrecy | pricing, speed, quality, delivery consistency, win rate |
| Rights status | Rights status | owned, licensed, shared, or client-owned |
If ownership is unclear, mark it uncertain - legal review instead of force-labeling it as a trade secret.
| Asset | Why it has economic value | Current secrecy controls |
|---|---|---|
| Curated prospect/client list with notes | Non-public relationship context that saves time and improves targeting | Private CRM, limited access, confidentiality terms with assistants/collaborators |
| Pricing or estimating method | Protects margin and improves quote accuracy and speed | Internal file only, restricted access, not shared externally |
| Internal delivery process/checklist | Repeatable execution edge versus generic public processes | Private docs, need-to-know access, confidentiality terms |
| Non-public code architecture/internal tooling | Internal technical advantage not generally visible to outsiders | Private repo, restricted permissions, secured network access |
| Creative production rules/system | Repeatable decision logic that improves output and turnaround | Internal permissions, confidential sharing only |
Do not treat everything valuable as a trade secret. Public portfolio work, broadly known methods, and information others can lawfully reverse engineer or independently derive are weak candidates. Client-owned materials also do not automatically become your trade secrets.
| Item | Why it may fail | Article detail |
|---|---|---|
| Public portfolio work | Weak candidate | public portfolio work |
| Broadly known methods | Weak candidate | broadly known methods |
| Information others can lawfully reverse engineer or independently derive | Others can get it through lawful means | lawfully reverse engineer or independently derive |
| Client-owned materials | Do not automatically become your trade secrets | client-owned materials |
| Information published openly, taught publicly, or shared without limits | Secrecy may be compromised unless you have specific contrary facts | published it openly; taught it publicly; shared it without limits |
If you published it openly, taught it publicly, or shared it without limits, secrecy may be compromised unless you have specific contrary facts.
Use these questions to sort the list:
If a required element fails, classify it as not trade secret. If it is unclear, classify it as uncertain - legal review. Once your list is sorted (likely secret, uncertain, not secret), move to Step 2 and document the controls for each category.
If you ever need to rely on a DTSA claim, you need evidence, not just a claim that you were careful. In practice, your day-to-day handling should make it easier to show who could access sensitive information, what your contracts said, and how information was shared and closed out.
That evidence focus is practical, not theoretical. In Case No. 19-2514-JAR, the DTSA claim was litigated alongside Kansas unfair-competition and breach-of-contract claims. The court applied the Rule 56(a) summary-judgment standard, denied the plaintiff's summary-judgment motion, and granted in part and denied in part the defendant's summary-judgment motion. Those were summary-judgment rulings, not final liability findings. If the record could support the nonmoving side, factual disputes remain. Build your controls so you can show consistent handling, not just good intentions.
Use the checklist below as a practical way to organize proof, not as a court-defined DTSA formula.
| Control area | What to implement | What evidence to retain | Common failure mode |
|---|---|---|---|
| Access control | Controlled storage, unique user access, least-privilege permissions, regular access review, clear revocation steps | Access lists, permission exports/screenshots, dated review notes, revocation confirmations | Overbroad access, shared logins, old collaborator access left active |
| Contract control | Written terms that can cover confidentiality scope, ownership/licensing boundaries, return-or-destruction at closeout, and subcontractor flow-down duties | Signed agreements, version history, subcontractor agreements, closeout communications | Missing signatures, vague ownership/confidentiality language, no downstream terms |
| Sharing control | Approved sharing channels, named recipients, limited link/file permissions, handoff records, offboarding records | Delivery records, share logs, link settings, handoff checklist, return/deletion confirmations | Ad hoc sharing across mixed channels, unclear recipient trail, no closeout record |
Start here: limit access to people who actually need it, and keep records of those decisions. You should be able to show current access and when access changed.
For client delivery, keep sensitive materials in controlled workspaces, avoid shared accounts, and scope collaborator access to the minimum needed folder, repo, or workspace. If someone only needs one project area, do not give them your broader methods, pricing, or client systems.
Use this checkpoint: can you show who has access now, and who had access before a project ended? If not, fix that first.
Your contract file can prevent confusion early and reduce factual fights later. Consider written terms that address confidentiality scope, ownership or license boundaries, closeout return-or-destruction duties, and matching obligations for any subcontractor handling sensitive information.
Do not leave these points implied. Silence on ownership boundaries or closeout handling can create avoidable disputes about what was protected, who could use it, and what should have been returned or deleted.
If ownership is still unclear from Step 1, resolve that before moving forward with new work and reuse boundaries. If helpful, pair this with Work for Hire vs. Assignment of Rights: A Freelancer's Guide to Owning Your IP.
Most problems come from routine sharing, so treat sharing as a controlled process. Use approved channels, name recipients, and limit access to what each handoff requires.
When you send sensitive materials outside your main workspace, create a written trail of what was shared, with whom, and why. At project end, complete a closeout record that captures handoff completion, access changes, and any return or deletion step you required. The goal is not perfect tools. It is consistent handling you can prove later.
Before Step 3, confirm:
| Baseline item | What to confirm | Article detail |
|---|---|---|
| Storage and access | Each likely trade secret is stored in a controlled location with named access | controlled location with named access |
| Access records | You can produce current and recent access records, including revocations | current and recent access records, including revocations |
| Core agreements | Core agreements clearly address confidentiality scope, ownership or licensing boundaries, closeout return-or-destruction expectations, and subcontractor flow-down terms where relevant | confidentiality scope; ownership or licensing boundaries; closeout return-or-destruction; subcontractor flow-down terms |
| Project files | Project files include sharing and handoff records, plus offboarding evidence at closeout | sharing and handoff records; offboarding evidence at closeout |
If any item is missing, treat it as a priority repair. Once those basics are in place, the next question is what to do when misuse is suspected and speed starts to matter. You can also turn your confidentiality rules into practical contract language with the NDA Generator.
When suspicion starts, do not improvise. Use a repeatable sequence that protects evidence, avoids preventable mistakes, and gets counsel involved early.
If you need the DTSA, start with the gate. The information must still qualify as a trade secret. That means it had economic value from not being generally known and you used reasonable measures to keep it secret. Step 2 built that record. Step 3 is about using it under pressure.
Treat this as a records-and-process problem first.
A defensible offboarding file can include concrete artifacts, not just one final email. Keep dated return-or-destruction confirmations where available, proof of revoked credentials, tokens, or shared-folder access, client acknowledgment, and dated records of what was deleted, returned, or retained. If subcontractors were involved, keep their exit records too. Use a current attorney-approved return/destruction and no-retention clause rather than improvising one during a dispute.
Move quickly, but stay factual and controlled.
| Remedy | When it applies | What proof you'll typically need | What outcome it can deliver | Practical limits |
|---|---|---|---|---|
| Injunction | Ongoing or threatened use or disclosure | Trade-secret status, secrecy measures, misuse evidence, and need for forward-looking relief | Court order restricting use or disclosure | Cannot rely only on what someone knows to block employment; limits apply |
| Actual loss / unjust enrichment damages | Harm already occurred | Loss model, business impact, pricing or economic records, or benefit gained by other side | Monetary damages for loss and unjust enrichment | Damages proof is often fact-heavy and costly |
| Exemplary damages | Willful and malicious misappropriation | Strong evidence of intentional wrongful conduct | Up to not more than 2 times compensatory damages | Unavailable against covered workers if required immunity notice was omitted |
| Attorney fees | Bad-faith claim or defense, or willful or malicious misappropriation contexts | Record supporting bad faith or heightened misconduct | Possible fee shifting | Immunity-notice gaps can block fee recovery against covered workers |
| Ex parte seizure | Extraordinary emergency circumstances | Specific facts, including actual possession and reasonably particular description of items | Seizure without prior notice in narrow cases | Rare and demanding; wrongful or excessive seizure can create applicant liability |
Cross-border disputes add jurisdiction, venue, and governing-law friction quickly. The DTSA can reach some outside-U.S. conduct, but not every fact pattern, and venue still follows federal venue rules. If your project spans countries, early counsel involvement is basic risk control. It helps you set forum strategy and evidence preservation before making accusations or commitments.
You do not need a grand IP strategy. You need a repeatable operating rhythm: identify what is valuable, keep it meaningfully restricted, and keep records that can prove both if something goes wrong. Under the DTSA, a solo operator can qualify as an owner, but protection is not automatic and legal fit is always fact-specific.
Start with an asset inventory, not marketing language. List the nonpublic business or technical information you would care about losing tomorrow, and define clear file boundaries for what is restricted versus reusable. If you cannot point to a dated list and clean classification, fix that before you think about enforcement.
Make your reasonable measures visible and consistent. Align confidentiality terms with how you actually work, limit access, and separate restricted project files from reusable templates. Review your paperwork set together (NDA, contractor agreement, SOW), because gaps or inconsistencies, including missing required notice language, can weaken your position. Where notice is required but missing, exemplary damages and attorney fees against that worker may be unavailable.
Prepare your evidence trail before there is a dispute. Preserve version history, transfer records, screenshots, and closeout communications so you can show what was shared, under what restrictions, who had access, and when issues were discovered. Move quickly if misuse appears, because civil claims under this law have a 3-year limitations period tied to discovery, or when discovery should reasonably have happened. Also confirm the DTSA commerce nexus applies: the trade secret must relate to a product or service used in, or intended for use in, interstate or foreign commerce.
For your next contract cycle and project closeout:
That is what running your IP like an owner looks like in practice: clear classification, consistent controls, and documented readiness.
Before your next client engagement, lock scope, deliverables, and ownership terms in writing with the SOW Generator.
The approved material does not establish DTSA coverage for independent contractors or freelancers. Verify the current legal standard with counsel using your NDA, contractor agreement, and SOW.
The approved material does not provide a DTSA definition of a trade secret. Confirm the current legal standard with counsel before relying on labels or internal categories.
The approved material does not define what qualifies as “reasonable measures” under DTSA. Ask counsel to confirm what standard applies to your facts before you rely on a checklist.
The approved material does not set a DTSA misappropriation proof standard. Have counsel identify the current legal elements and what evidence is relevant in your case.
The approved material does not support a DTSA-versus-NDA comparison. Treat this as a separate legal review and have counsel map your contract terms to the current DTSA standard.
The approved material does not establish cross-border DTSA outcomes. Get jurisdiction-specific advice on governing law, forum, and enforceability before relying on assumptions.
The approved material does not confirm whether special DTSA notice language is required in your contracts. Have counsel verify the current rule and update templates accordingly.
An international business lawyer by trade, Elena breaks down the complexities of freelance contracts, corporate structures, and international liability. Her goal is to empower freelancers with the legal knowledge to operate confidently.
Priya is an attorney specializing in international contract law for independent contractors. She ensures that the legal advice provided is accurate, actionable, and up-to-date with current regulations.
Educational content only. Not legal, tax, or financial advice.

A freelance agreement is not just about price and scope. It decides who controls the rights in the work. If the ownership language is loose, rights can move earlier than you expect, cutting down your control once the work is delivered or used.

Choose your track before you collect documents. That first decision determines what your file needs to prove and which label should appear everywhere: `Freiberufler` for liberal-profession services, or `Selbständiger/Gewerbetreibender` for business and trade activity.

If you want to protect trade secrets when someone leaves, start with a blunt rule. Information is protected only if it is nonpublic, valuable because it stays secret, and something you actually kept under control. General skill, public information, and experience honestly gained doing the work are often portable, subject to any confidentiality duties.