
Yes - treat ISO 27001 certification as a contract decision first, then an evidence exercise. If a buyer requires an accredited certificate in contract terms, alignment documents alone will not close the gap. If the requirement is preference or due diligence, submit a compact pack built from your SoA, policy excerpts, and one current record for each material questionnaire response.
When a buyer asks about ISO 27001 certification, treat it as a third-party risk decision. They want to see that your security approach is documented, repeatable, and reviewable.
ISO 27001:2022 is a globally recognised standard for an Information Security Management System, or ISMS. In practice, that means a managed system across people, processes, and technology to protect confidentiality, integrity, and availability. Certification gives buyers an external trust signal that your information security risk management is being taken seriously. It is not a claim of perfect security.
The better move is to identify what the reviewer is actually deciding, then answer to that decision:
| Buyer question | What they are deciding | Evidence they can review now |
|---|---|---|
| "Are you certified?" | Whether certification is required to proceed | Clear yes or no, plus current status and scope if applicable |
| "Do you follow ISO 27001?" | Whether your risk work is systematic | Brief ISMS explanation and current documentation showing repeatable risk management |
| "Please complete our security review." | Whether your responses are credible and consistent | Completed review materials with supporting documentation that aligns with your responses |
If you are not certified, alignment evidence may still help move diligence forward. But some B2B buyers treat ISO 27001 certification as a prerequisite, especially in IT, healthcare, and finance. If certification is being treated as a prerequisite, state that only after the requirement text has been verified against the contract, procurement policy, or other source record.
A simple response pattern works:
What matters most is consistency. Your questionnaire answers and attached documents should tell the same story.
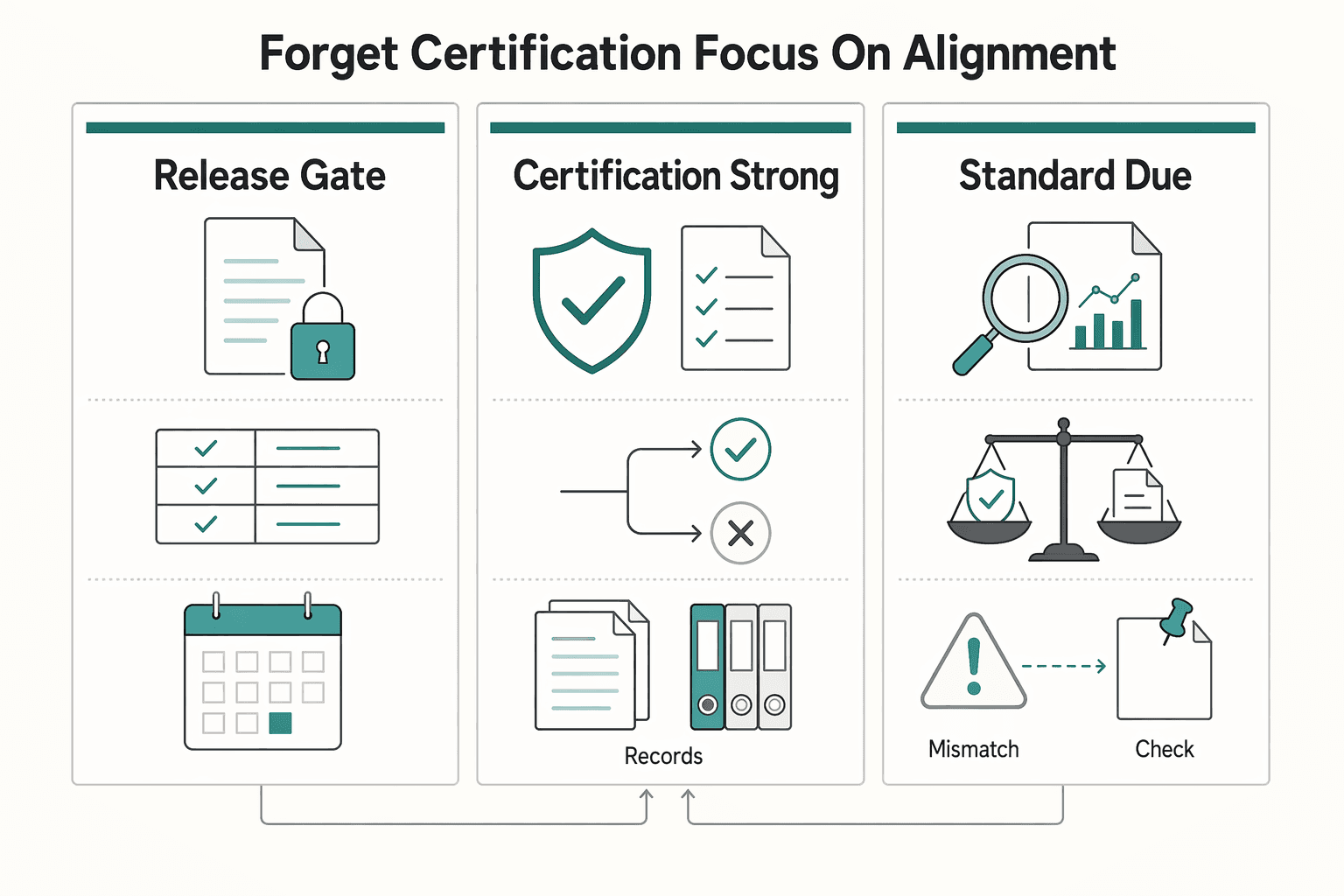
Start by confirming whether certification is a contract gate or a due diligence preference. That check determines your path. If the buyer has a hard requirement in the contract, security terms, or procurement policy, this becomes a yes-or-no commercial decision. If they do not, lead with alignment evidence and keep the deal moving.
Do not promise certification off a sales call or questionnaire. Ask for the exact source of the requirement and verify the text. Until you confirm it, treat the requirement language as pending source-record verification. Some buyers will not budge. Others may simply be asking for reviewable security evidence.
| Situation | Practical buyer signals | Decision trigger | What you do next |
|---|---|---|---|
| Certification is a gate | Contract language, security addendum, or procurement policy says a certificate is mandatory; buyer says they will not proceed without it | Current requirement language pending certification-body or source-record verification. | Decide whether the revenue and strategic value justify the audit path. Do not argue that alignment is equivalent. |
| Certification is a strong preference | Questionnaire asks about certification, and reviewer also asks for policies, risk handling, and records | No verified clause requiring a certificate | Send your alignment pack first and confirm whether equivalent evidence is acceptable at this stage. |
| It is standard due diligence | Reviewers across security, legal, and procurement focus on evidence quality | Review focuses on evidence quality, not certificate status | Use one concise evidence set so all reviewers see the same facts. |
Timing is often the practical filter. One common estimate is about four months to become audit-ready, plus another two to three months for the audit. Another source says certification often takes 6+ months. If the buyer needs answers this quarter and you are not already far along, alignment is often the only realistic near-term path.
Alignment only works if it looks like a real ISMS, not a stack of policy files. Start with scope boundaries: what is in scope, what is out of scope, and why. Over-scoping wastes resources. Under-scoping leaves gaps. If you exclude something, document the reason.
Then show how you treat risk. A credible risk assessment covers your assets, uses cross-department input, and records mitigation decisions. Keep it broader than IT. Information security also touches vendor management, HR handling of information, physical security, and document disposal.
| Artifact type | What it should show | Review outcome it supports |
|---|---|---|
| Scope statement + asset/data inventory | Clear ISMS boundary, explicit out-of-scope items, and justification | Security can test boundary logic, procurement can classify risk, legal can confirm your statements are bounded and consistent |
| Risk assessment + mitigation plan | Asset coverage, cross-functional input, and documented treatment decisions | Security sees risk methodology, procurement sees a managed program, legal sees support for your claims |
| Control mapping file (questionnaire ask -> policy/record) | Each answer maps to a specific policy section or operating artifact | Reviewers can validate answers quickly without contradictory narratives |
| Live operating record (for example, internal audit + remediation status or another current control record) | Controls are operating now, not only documented | Security can confirm execution, procurement can move diligence forward, legal can rely on current evidence |
Before you send anything, test a few questionnaire answers end to end: answer -> policy excerpt -> current record. If that chain breaks, your pack is not ready.
Once you know which path you are on, build only the evidence you need to support that path.
Your Statement of Applicability, or SoA, is the control-level record of what applies in your ISMS and why. Each row should let a reviewer move from question to control objective, applicability rationale, implementation detail, and exact proof location without guessing.
The SoA is where your security program becomes concrete or stays vague. Under Clause 6.1.3, it records the control "what and why," so use it to translate your actual operations into claims a reviewer can test. It is not a policy summary, and it is not a list of broad statements.
Clause 7.5 raises the documentation bar further. Documented information needs controlled creation, review, approval, versioning, access, and retention or disposal. If a row points to records that are outdated, unapproved, or hard to find, that row is weak even if the technical control exists. In practice, reviews can fail on unreliable documentation, not just missing controls.
Use one simple test for every row: can someone verify this claim quickly?
| SoA row element | What "good" looks like |
|---|---|
| Control reference | Use the exact control ID or internal mapping reference. |
| Control intent | State the objective in plain language and the risk or activity it addresses. |
| Applicability rationale | Explain why it applies, or does not, within your ISMS scope, tied to your services, data, people, tools, and dependencies. |
| Implementation detail | Describe how it runs now: process, tool, trigger or frequency, and approvals. |
| Exact evidence location | Point to live proof such as a policy section, ticket queue, access review, training log, incident register, or system export. Avoid "available on request." |
| Owner and status | Name the accountable owner and the current operating status. |
Do not start with a generic checklist. Start with your ISMS scope statement. Clause 4.3 makes scope your anchor: what you protect, and what sits outside that boundary.
Define in-scope services, data, tools, roles, and third-party dependencies before you map controls. Keep that boundary aligned with how your ISMS operates across people, processes, and IT systems. If something is out of scope, record it and explain why.
Then map applicable controls inside that boundary. If that mapping is still being validated, verify it against the official standard, certification-body guidance, policy records, or source records before use.
A strong SoA row ties each claim to a current artifact and a named owner. That is what makes it useful in diligence rather than just tidy on paper.
Stronger: "Access to in-scope production systems is limited to approved named accounts. Access requests and periodic access reviews are documented by accountable owners. Evidence: current access review record and approved access request log."
Stronger: "All in-scope personnel complete information security awareness training, and completion is tracked. Evidence: current training log and latest completion or reminder report."
Stronger: "Security incidents are logged, triaged, assigned, and tracked to closure by a named owner. Evidence: incident register, triage checklist, and the latest available exercise note. Verify timestamps across tools before relying on event sequence."
A good internal test is to pick one row and trace it end to end: row text -> linked procedure or policy -> current record -> named owner. If any link breaks, fix the row before you reuse it.
Before you use the SoA in a live review, make sure it can survive a reviewer reading it alongside your questionnaire and attachments. Check three things:
Once your SoA is solid, the questionnaire stops being a writing exercise and becomes an evidence-routing exercise. For each material prompt, state your operating context, answer the control objective, then attach one artifact a reviewer can verify quickly.
Weak responses usually fail in the same way. They sound polished, but they do not show how the control works in your environment. If you are pursuing certification, this is often where reviewers assess whether your documentation is credible.
| Questionnaire intent | Weak answer | Strong answer |
|---|---|---|
| Change control | "N/A, I work alone." | "As a solo operator, I document production changes before release and keep a dated change record. Evidence: policy excerpt, matching SoA row, and a recent change log entry." |
| Access review | "Access is restricted." | "Access to in-scope systems is limited to named accounts and reviewed on a defined schedule. Evidence: access policy excerpt, SoA row, current access list, and latest review record." |
| Security awareness | "N/A, only me." | "As the only in-scope worker, I keep documented security awareness for customer-data handling. Evidence: policy excerpt, SoA row, and a dated training or review record." |
Fast verification matters here. For every material response, include three linked items: the relevant policy excerpt, the matching SoA entry, and one current operational record. Tag artifacts with retrieval metadata such as control ID, collection date, and owner so you can reuse them without rebuilding each packet. That reduces duplicate prep and keeps your answers consistent across reviews.
Some prompts create extra back and forth: data location, subprocessors, cross-border transfers, and customer-data handling. Keep a simple document map ready: service description, system or hosting inventory, subprocessor list, customer-data handling policy, and one current supporting record. If something is still being confirmed, verify the requirement text from legal, contract, policy, or source records before use. Do not guess when legal and procurement language needs to line up.
Before you send the packet, use a real checkpoint instead of a quick skim:
The decision should be clearer now. The reviewer is deciding whether your risk evidence is enough to move the contract forward. In practice, the split is simple: either certification is a contractual gate, or documented alignment evidence is acceptable.
Start with this decision split:
| Situation | What it means | What you should do next |
|---|---|---|
| Certificate is explicitly required in contract language or onboarding requirements | Certification is part of the approval gate | Confirm required scope, timing, and whether an accredited certificate is required. Validate any presented certificate through IAF CertSearch before relying on it. |
| Buyer asks about ISO/IEC 27001 but does not require a certificate | They are often assessing third-party risk evidence | Submit an alignment pack tied to your SoA, policy excerpts, and current records so each answer can be verified quickly. |
| Questionnaire wording is vague (for example, "ISO 27001 compliant?") | Different teams may be using different criteria | Ask one clarifying question: "Is an accredited certificate contractually required, or will documented alignment evidence be reviewed?" |
If certification is a legal or contractual requirement, an evidence package alone will typically not satisfy that clause. Also remember that ISO does not issue certificates directly. Certification is issued by independent certification bodies.
If the gate is evidence, use one traceability chain for each material response:
questionnaire answer -> policy excerpt -> SoA rationale -> current record
This structure matches common review flow and can reduce avoidable follow-up. Common failure points include:
You do not need a bigger company's documentation style. You need a package that lets legal, security, and procurement verify the same facts with minimal back and forth.
If a contract makes certification mandatory, move directly to the certificate path and confirm scope, issuer expectations, and validation method. If alignment evidence is acceptable, submit a compact evidence pack with explicit traceability and one current record per material claim, including SIG-style prompts.
State why it is not relevant in your operating context and point to the matching SoA rationale. Do not stop at "N/A." If the risk is handled another way, show that method and attach a current record.
Sometimes yes, when the buyer accepts documented alignment evidence. Sometimes no, when certification is written into contract or onboarding requirements. Confirm which path applies early.
Ask whether an accredited certificate is required, what scope it must cover, and at what deal stage it is enforced. That tells you whether you are facing an immediate certificate gate or an evidence review phase.
Do not send isolated policies. Send the full chain: questionnaire answer, policy excerpt, SoA rationale, and one current record. That is a direct way to support a clean review decision.
If you are building your security packet in parallel, these internal resources can help: SOC 2 for SaaS companies, what a SOC 2 report means, document workflows and templates, and the NDA generator for procurement-ready paperwork.
State why it is not relevant in your operating context and point to the matching SoA rationale. Do not stop at "N/A." If the risk is handled another way, show that method and attach a current record.
Sometimes yes, when the buyer accepts documented alignment evidence. Sometimes no, when certification is written into contract or onboarding requirements. Confirm which path applies early.
Ask whether an accredited certificate is required, what scope it must cover, and at what deal stage it is enforced. That tells you whether you are facing an immediate certificate gate or an evidence review phase.
Do not send isolated policies. Send the full chain: questionnaire answer, policy excerpt, SoA rationale, and one current record. That is a direct way to support a clean review decision. If you are building your security packet in parallel, these internal resources can help: SOC 2 for SaaS companies, what a SOC 2 report means, document workflows and templates, and the NDA generator for procurement-ready paperwork.
An international business lawyer by trade, Elena breaks down the complexities of freelance contracts, corporate structures, and international liability. Her goal is to empower freelancers with the legal knowledge to operate confidently.
Priya specializes in international contract law for independent contractors. She ensures that the legal advice provided is accurate, actionable, and up-to-date with current regulations.
Includes 8 external sources outside the trusted-domain allowlist.
Educational content only. Not legal, tax, or financial advice.

Low-stress compliance in Germany comes from decision order, not tax tricks. Use this sequence: confirm core facts, apply conservative temporary assumptions, verify the few points that can break invoices or filings, and keep one evidence file that explains each decision.

**Build your SOC 2 playbook before sales pressure hits, so you control scope, evidence, and audit timing instead of reacting under stress.** If you're pursuing **[soc 2 compliance for saas](https://www.cobalt.io/learning-center/soc-2-compliance-for-saas)**, treat this guide as a system, not a policy exercise. As the CEO of a business-of-one, you need a SOC 2 plan that protects your calendar as much as your customers. Use it to decide what to implement first, keep the right proof, and connect the work to clearer security controls, cleaner buyer conversations, and fewer fire drills.

You are still accountable for [third-party risk](https://www.federalreserve.gov/frrs/guidance/interagency-guidance-on-third-party-relationships.htm), so reviewing a SOC 2 report should be treated as an operating control, not a paperwork task.