
Yes. If you offer services to people in India and handle identifiable digital personal data, you are likely in scope and should operate as a Data Fiduciary. Start by recording what you collect and why, tie onboarding to clear notice-and-consent steps, enforce access controls in the tools you use, and keep rights and breach response templates ready. If your workflow depends on overseas cloud vendors, verify current transfer notifications and keep processor contracts aligned with actual practice.
You are likely in scope if your work has an India link and you process identifiable personal data in digital form, including when you offer goods or services to people in India. You are likely out of scope if your processing has no India link, or you do not handle identifiable personal data.
The main trigger is your activity and India link, not just your location. The Act covers digital personal data in India. It can also apply to processing outside India when it is tied to offering goods or services to Data Principals in India, and it can cover data collected offline once it is digitized.
A Data Fiduciary is the person or business deciding why and how personal data is processed. In freelance work, that is usually you. You decide what to collect in onboarding, how project communication is stored, what invoicing details are required, and how support messages are logged.
A Data Principal is the individual the data relates to. In practice, that could be the person who submits your inquiry form, your client contact in chat, the billing contact on an invoice, or a support requester.
| Audit question | If yes | If no / unclear |
|---|---|---|
| Do you offer goods or services to a person in India? | Continue | Likely out of scope unless another India link needs legal review |
| Do you process data about an identifiable individual? | Continue | Likely out of scope |
| Is that data digital, or later digitized? | Continue | Verify with counsel before proceeding if your workflow may digitize it later |
| Do you decide the purpose or means of processing? | You are likely a Data Fiduciary and likely in scope | You may be a Data Processor; verify with counsel before proceeding |
| Is your case limited to a carve-out, such as personal or domestic use, or data made publicly available by the individual or as legally required? | A carve-out may apply; verify with counsel before relying on it | Likely in scope |
Yes: continue. No: likely out of scope unless another India link needs legal review.
Yes: continue. No: likely out of scope.
Yes: continue. No: verify with counsel before proceeding if your workflow may digitize it later.
Yes: you are likely a Data Fiduciary and likely in scope. No, you only process on someone else's instructions: you may be a Data Processor. Verify with counsel before proceeding.
Yes: a carve-out may apply. Verify with counsel before relying on it. No: likely in scope.
Using vendors does not move responsibility off your desk. If a CRM, help desk, or cloud tool processes data for you, you still carry the compliance responsibility, and that processor use should sit under a valid contract.
| Scenario | Likely DPDP impact | What you do next |
|---|---|---|
| You provide services to a client contact in India and store names, emails, and project communications | Likely in scope | Treat yourself as a Data Fiduciary and move to consent and security-safeguard steps |
| Your India-linked work uses only data that cannot identify any individual | Likely out of scope on these facts | Document why it is non-personal data and re-check if datasets change |
| You collect details on paper for India-linked work, then upload to a CRM or spreadsheet | Likely in scope | Treat digitized records as in-scope personal data |
| You only process data under client instructions, using their systems in an India-linked engagement | Needs verification | Confirm role allocation and processor contract terms before proceeding |
If you land in likely in scope, the next step is straightforward. Tighten consent and security safeguards, and make sure any processor use is covered by a valid contract.
You might also find this useful: A Guide to Data Sovereignty and Its Impact on Cloud Storage.
Once scope is clear, do three things in parallel. Lock your contract terms, set a real security baseline in the tools you use, and keep your privacy notice aligned with both. That gives you a defensible operating position without waiting for perfect legal certainty.
| Pillar | Focus | Outcome | Common mistake |
|---|---|---|---|
| Pillar 1 | Get the front-end record right first | Start each India-linked engagement with a documented, plain-language record of what you collect, why, your retention approach, and where rights or grievance requests go | Using broad protective language that your operations cannot honor consistently |
| Pillar 2 | Security only counts if it shows up in live accounts and day-to-day access decisions | Show reasonable safeguards in practice, plus basic vendor discipline, across the systems you use | Assuming your environment is protected because your primary account is protected, while shared or older accounts remain exposed |
| Pillar 3 | Your contract and privacy notice should tell the same story | Keep your contract and privacy notice aligned so your disclosures are clear, accessible, and consistent | Updating one document and forgetting the other |
The timing still needs verification. Materials generally agree that the DPDP Rules provide the operational detail for notice, security safeguards, breach reporting, grievance handling, and processor-contracting obligations. They do not fully align on current status. One timeline describes finalization in November 2025, 2026 as a build year, and broad obligations taking effect by May 13, 2027. Build now, and confirm the current legal wording before you finalize templates.
Get the front-end record right first. You want every India-linked engagement to start with a documented, plain-language record of what you collect, why, your retention approach, and where rights or grievance requests go.
Outcome: A documented, plain-language record at the start of each India-linked engagement covering what you collect, why, your retention approach, and where rights or grievance requests go.
Implementation checklist:
Common mistake to avoid: Using broad protective language that your operations cannot honor consistently.
Security only counts if it shows up in live accounts and day-to-day access decisions. The practical standard is reasonable safeguards, plus basic vendor discipline, across the systems you already use.
Outcome: Reasonable safeguards in practice, plus basic vendor discipline, across the systems you use.
| Control area | Minimum baseline | Good practice |
|---|---|---|
| Access control | Limit access to only accounts that need personal data | Separate admin and daily-use access, and review access periodically |
| Authentication | Use strong authentication across all tools that hold personal data | Use phishing-resistant methods where available and keep recovery paths current |
| Vendor due diligence | Review vendor security and data-handling commitments before use | Maintain a simple vendor register with tool, purpose, data type, and review date |
| Incident readiness | Define first containment, impact review, and client notification steps | Keep a written breach checklist and confirm you can access it during account lockout |
Common mistake to avoid: Assuming your environment is protected because your primary account is protected, while shared or older accounts remain exposed.
Your contract and privacy notice should tell the same story. The contract can carry engagement-specific terms, but the notice needs to reflect the same core facts in a clear, accessible way.
Outcome: Keep your contract and privacy notice aligned so your disclosures are clear, accessible, and consistent.
The notice should clearly explain what data you collect, why, how people can exercise rights, and how they can lodge complaints. Your contract can capture engagement-specific terms, but your notice must reflect the same core facts.
| Contract clause | Privacy notice |
|---|---|
| Data categories collected for the engagement | Same categories in plain language |
| Purpose tied to service delivery and related operations | Same purpose, without unexplained expansion |
| Retention position | Same retention position |
| Rights or grievance channel | Same contact route and instructions |
| Use of processors or external tools | Same reality reflected at a high level |
Implementation checklist:
Common mistake to avoid: Updating one document and forgetting the other. That creates inconsistent disclosures and avoidable risk.
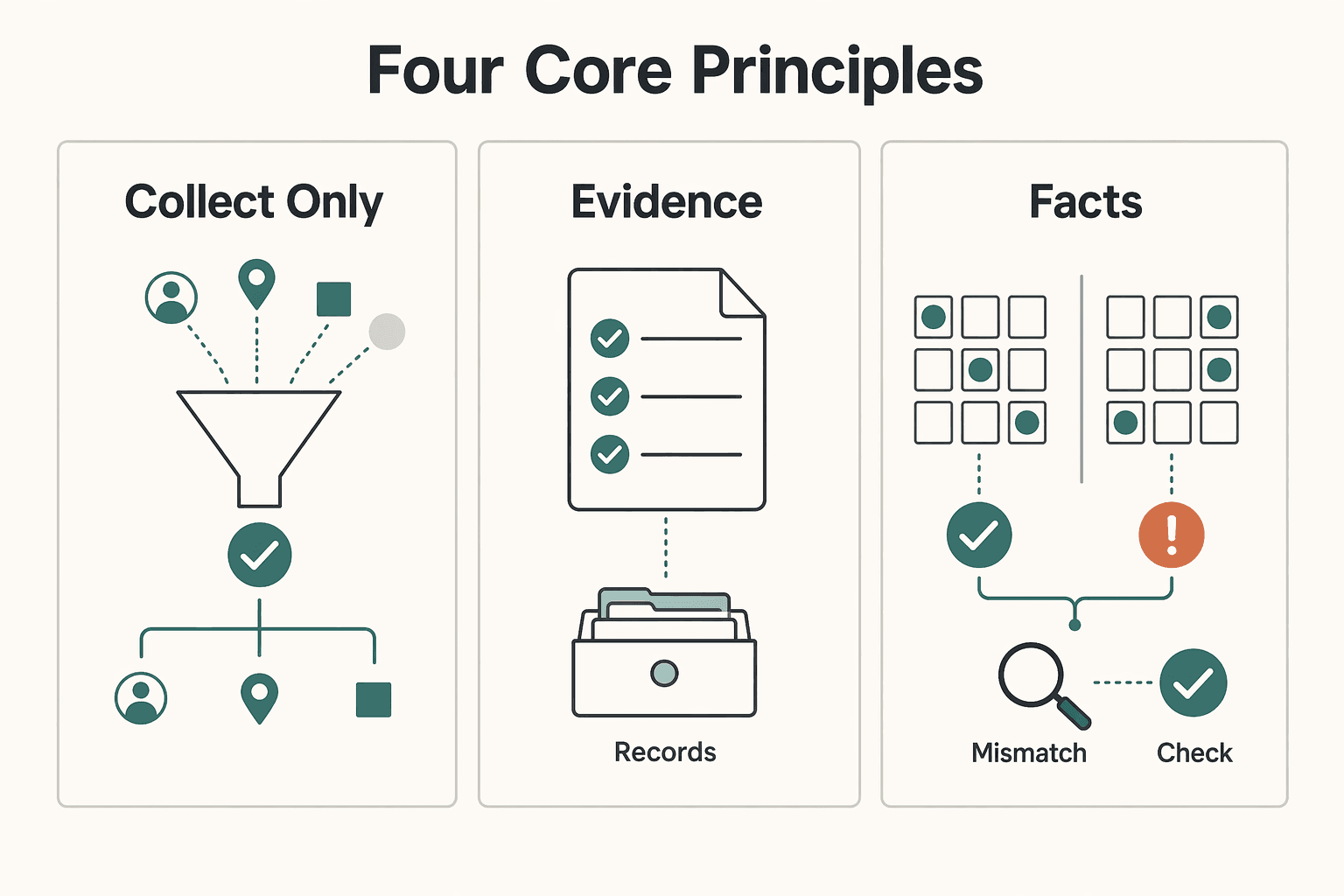
A compliant setup is not enough on its own. What holds up in practice is repeatable handling across onboarding, live delivery, and offboarding. Use the same four rules every time.
| Principle | Rule | Practical step |
|---|---|---|
| Collect only data that survives a hard filter | If a field is not clearly needed for service delivery or legal retention, do not collect it | Compare your actual forms and tool fields against your contract and notice, and keep dated proof of those reviews |
| Store and transfer data only where you can explain it | Know where data is stored, verify whether any transfer restrictions are currently notified, and document processor contracts | Show storage location, transfer-risk checks, and contract coverage for each Data Processor |
| Treat every suspected breach like a timed event | Run a fixed incident sequence immediately, even when the facts are incomplete | Detect, contain, assess, notify, and document |
| Build evidence of good-faith compliance | Show a pattern of careful handling over time | Keep versioned notice and contract records, field-review logs, processor contracts, vendor register updates, access-review notes, incident records, deletion confirmations, and internal handling instructions |
The right default is simple: if a field is not clearly needed for service delivery or legal retention, do not collect it. Processing should stay tied to lawful purpose, and your notice should clearly state what data you collect and why.
Use this filter on every form and workflow: Required to deliver service? Required for legal retention? If not, do not collect.
Apply it to inquiry forms, onboarding questionnaires, CRM records, invoicing profiles, and shared trackers. Common cleanup candidates in many service workflows include date of birth, home address for early-stage calls, ID copies when no legal check applies, duplicate personal phone fields, and emergency contacts unrelated to the engagement.
Then run a live field check. Compare your actual forms and tool fields against your contract and notice, and keep dated proof of those reviews. At offboarding, erase data you no longer need unless retention is required by law. Apply the same deletion logic when consent is withdrawn, unless retention is required by law.
Before you argue about tool brands, get the basics straight. Know where data is stored, verify whether any transfer restrictions are currently notified, and document processor contracts. Section 16 supports a restriction-by-notification model, so avoid absolute statements until you verify current notifications.
In plain language, cross-border tools may still be usable. You need to show storage location, transfer-risk checks, and contract coverage for each Data Processor.
| Where data is stored | Risk check | What you document |
|---|---|---|
| Primary cloud workspace or file storage | Confirm hosting region and check current notified transfer restrictions. Current restricted-jurisdiction status pending official verification. | Vendor name, storage region, purpose, contract or DPA, review date |
| CRM, project, or support tool | Confirm cross-region processing and sub-processor flow, and ensure notice language still matches | Vendor register entry, processor contract, notice wording used |
| Local device, backup drive, or synced archive | Check for uncontrolled copies and validate access controls | Device inventory note, encryption or access setting, deletion timing |
Speed matters more than certainty in the first pass. Run a fixed incident sequence immediately, even when the facts are incomplete. A personal data breach can include unauthorized processing or accidental disclosure, acquisition, sharing, use, alteration, destruction, or loss of access.
Stress-test this flow by assuming your main account is unavailable. If you cannot quickly reach admin controls, recovery paths, or vendor contacts, the playbook is not ready.
Good-faith compliance is easier to defend when you can show a pattern of careful handling over time. Penalties are not automatic outcomes. Imposition follows inquiry and hearing, and Schedule bands use "may extend to" language. Current penalty bands pending legal or official verification.
Keep practical evidence tied to real operations: versioned notice and contract records, field-review logs, processor contracts, vendor register updates, access-review notes, incident records, deletion confirmations, and internal handling instructions. Keep it simple, but keep it current.
A lightweight evidence folder is enough if you update it whenever you change data fields, review access, sign processor terms, or handle an incident.
Turn your consent and privacy terms into a client-ready first draft with the freelance contract generator, then have counsel finalize it for your DPDP process.
All of this only helps if you can produce it quickly. Treat documentation as part of delivery, not as a separate compliance project. The standard is simple: at any point, you should be able to show informed consent, stated purpose, retention logic, and how you handled a Data Principal request.
Keep a minimal evidence register in the same workspace as your client notice and signed contract versions, and update it at onboarding, scope changes, and offboarding.
| Record type | Why it matters | Where you store it | Owner |
|---|---|---|---|
| Consent record | Shows agreement to collection and processing with informed notice | Contract folder or e-sign archive | You |
| Processing purpose note | Links each data field or tool to a real service purpose | Client file, intake sheet, or matter note | You |
| Retention note | Shows why data is kept, when review happens, and when deletion is due | Offboarding checklist or retention tracker | You |
| Rights-request log | Shows you acknowledged, verified, fulfilled, or closed access, correction, or deletion requests | Shared tracker or secure admin folder | You |
Each time you change intake fields or add a new tool, run a quick checkpoint. Update the purpose note, confirm your notice still matches, and log the review date. This habit matters because the law has been described as different from global benchmarks, and the cited material described DPDP Rules 2025 as draft and open for consultation. Do not hardcode response deadlines you have not rechecked.
For rights requests, prepare four short templates in advance, and include an identity-check step before you disclose, correct, or delete anything:
| Priority | Records |
|---|---|
| Must keep | Signed contract or consent proof, notice version used, purpose note, rights-request log, deletion or retention note |
| Nice to keep | Training notes, internal handling instructions, field-review screenshots, vendor review notes |
Use clear onboarding language: "We use a documented privacy process for consent, access requests, and deletion. Here is our policy link, a one-page process summary, and our response protocol." It signals professionalism because it is specific. Related: A Guide to Data Localization Laws for Global Freelancers.
If you treat DPDP as part of how you run client work, it becomes a trust and delivery issue, not just a legal one. That reframes onboarding, security checks, and data-use conversations as part of delivery quality.
The shift comes from visible habits, not legal wording alone. DPDP, operationalized through the 2025 Rules, is described as an enforceable baseline for collecting, processing, retaining, and transferring digital personal data. A reactive, deadline-only approach can leave teams catching up. In day-to-day work, each handoff across your form, inbox, cloud tools, contractors, and client contacts can be a potential weak point. You should be able to explain who has access, why, and for how long.
| What clients notice | Compliance-only posture | Trust-building posture |
|---|---|---|
| Consent | Generic language buried in terms | Plain notice tied to a clear yes action, with the version you used saved |
| Security controls | Broad claim that systems are "secure" | Clear least-privilege access, defined access paths, and monitoring habits |
| Transparency | Different answers from different people | One consistent explanation of what you collect, why, where it goes, and your retention approach |
| Incident response | Unclear next step if something happens | Documented breach response, rights-response process, and vendor-governance contacts |
A quick operational check: take one India-related client file and trace it from intake to storage to retention review. Confirm the notice and consent path, verify access settings, and check that your processor or fiduciary role assumptions and vendor-governance records still match reality.
This approach strengthens trust and risk control, but it is not a substitute for legal advice on complex, sensitive, or high-risk engagements.
If you want cross-border invoicing and payouts with policy controls and traceable records where supported, talk to Gruv.
Yes, it can. The Act applies to some processing outside India when it is related to offering goods or services to Data Principals in India. In practice, if your services involve personal data of people in India, treat those files, forms, and tools as in scope and note why.
If you decide the purpose and means of processing, you are the Data Fiduciary. Your storage, CRM, e-sign, or project platform may act as a Data Processor, but that does not remove your core duties. Keep a short vendor-purpose log, and do not assume tool providers absorb your compliance risk.
No. The Act also allows certain legitimate uses, and the consent standard is strict when you rely on consent. Use plain-language notice text, connect it to clear affirmative action, and archive proof.
Potentially yes, but do not treat foreign hosting as permanently cleared. Transfers may be restricted by government notification, so your decision depends on current restrictions and your controls, not just the tool brand. Recheck official transfer notifications, and keep evidence of your access and sharing settings.
On a personal data breach, the Data Fiduciary must intimate the Board and each affected Data Principal. Data Principals also have a right to readily available grievance redressal for acts or omissions by the Data Fiduciary or Consent Manager. The Board can direct urgent mitigation, inquire into a breach, and impose schedule-linked monetary penalties after inquiry. Prepare breach and grievance templates now, and verify the current penalty framework from official or legal records before use.
Because rollout has been phased and updated through notifications and rules material. The Act is dated 11 August 2023, a commencement notification is dated 13 November 2025, and some provisions were deferred by one year or eighteen months from gazette publication, with MeitY postings dated 14.11.2025 and a corrigendum dated 16.12.2025. Verify the currently operative text before you state deadlines, transfer limits, or penalty amounts.
Aim for a defensible baseline in five steps: map India-related data flows, finalize the notice-plus-consent path, tighten access, prepare rights and breach templates, and log retention review dates. That gives you a practical starting record if someone asks for a processing summary, correction, or erasure. Run this sequence once now, then repeat it whenever your intake fields, vendors, or workflows change.
An international business lawyer by trade, Elena breaks down the complexities of freelance contracts, corporate structures, and international liability. Her goal is to empower freelancers with the legal knowledge to operate confidently.
Priya is an attorney specializing in international contract law for independent contractors. She ensures that the legal advice provided is accurate, actionable, and up-to-date with current regulations.
Includes 4 external sources outside the trusted-domain allowlist.
Educational content only. Not legal, tax, or financial advice.

Low-stress compliance in Germany comes from decision order, not tax tricks. Use this sequence: confirm core facts, apply conservative temporary assumptions, verify the few points that can break invoices or filings, and keep one evidence file that explains each decision.

Treat this move as a verification project, not a booking sprint. If you are planning a remote-work move in Latin America, the first practical step is to separate what is clearly supported now from what still needs direct government confirmation before you spend money or lock dates.

You can work within **data localization laws** without stalling a cross-border deal, but only if you scope data location before price and timelines are set. For freelancers, the goal is simple: make assumptions explicit, tie them to contract language, and update them when facts change.