
Start by treating background checks for employees as a scoped risk process, not a trust test. Review consent first, confirm each requested field is role-relevant, and send sensitive data only through the official secure upload path. In U.S. employment screening, check for FCRA-required separate disclosure and signed authorization. In GDPR or UK GDPR contexts, apply data-minimization logic. After submission, get a copy of the report, verify key details, and challenge errors through the listed dispute process.
How elite consultants and contractors transform a compliance hurdle into a strategic advantage. For an independent professional operating at a high level, a client-requested background check can feel like an awkward last hurdle. After weeks of strategic conversations, proposal refinement, and building peer-level rapport, a formal request for personal data can change the tone. It does not have to.
This is not a test of your worth. It is a standard risk step inside a larger buying process. If you run your practice like a business, it is also a chance to show the same qualities the client is paying for. Diligence, organization, and a clear grasp of professional protocol.
This guide treats screening as something you manage, not something you simply endure. Done well, it becomes part of the final handshake. A controlled process that reinforces trust instead of introducing friction.
Do this before any screening request arrives. The goal is simple: remove mismatches, gather proof, and separate routine requests from ones that are broader than they need to be.
Start with consistency, not polish. A screening team may compare names, dates, titles, credentials, and public signals across easy-to-find profiles, and may review domains like work history, education, criminal-record context, financial history, medical history, and social media.
Check identity details first. Use your legal name consistently where required, and make sure prior names, initials, or common short forms are easy to reconcile. That cuts down on avoidable confusion, including wrong-person criminal matches.
Then reconcile role history line by line. If titles or dates differ across profiles, correct them or prepare a clear explanation. Do the same for degrees, certifications, and issuing bodies. Use official credential names rather than shorthand.
Run a simple test. Export your recent roles and credentials into one file, then compare that file to what a screening team could find in minutes. If the names, titles, and dates do not match, fix it now.
Do not wait until a request comes in to start hunting for documents. Keep a compact evidence pack that you can use under time pressure.
| Evidence area | What to keep ready |
|---|---|
| Identity | One current government ID, your exact legal name, and any prior names used professionally |
| Credentials | Degree confirmations, certification records, license details, and renewal dates with official naming |
| Work history | A master list of client names, role titles, start and end dates, and scope summaries |
| References | Current contacts who agreed to be reached, plus what each person can verify |
| Compliance documents | If you use a consumer reporting agency for employment checks, maintain your FCRA workflow materials, including stand-alone disclosure, written authorization handling, and pre-adverse-action materials |
Before you move on, check five things. Profile identity details match. Role dates reconcile. Credential names are official. References are current. Supporting files are stored in one accessible place.
The legal frame depends on jurisdiction and context. In the U.S., FCRA applies when a company uses a consumer reporting agency for employment screening. In the EU and UK, GDPR or UK GDPR requires a valid lawful basis and limits data collection to what is necessary.
| Framework | Purpose and trigger | Consent or legal basis | Access and correction rights | Data minimization and local checks |
|---|---|---|---|---|
| FCRA | U.S. employment screening through a consumer reporting agency | Written permission required; disclosure must be stand-alone | Before final adverse action, the person should receive the report copy and FCRA rights summary to review and dispute accuracy | Federal baseline; verify state and local rules, especially for credit-report use |
| U.S. state/local overlay | Additional limits on certain report types | Varies by state or municipality | Varies by jurisdiction | Confirm current local restrictions before assuming a report type is allowed |
| GDPR / UK GDPR | Processing personal data for a specific stated purpose | Consent is one option among six lawful bases; basis depends on context | Article 15 access right; Article 16 rectification right without undue delay | Collect only data that is adequate, relevant, and limited to necessity; verify current UK guidance where updates are in progress |
If a request looks broader than the role, ask why each data point is necessary.
If you think a report may surface an issue, write your explanation before anyone asks for it. The strongest format is short and structured: issue summary, context, remediation, and relevance to the role.
For example, if a title mismatch might appear, state the mismatch first. Then explain why it happened, show what record now standardizes it, and confirm that it does not change scope or authority. Keep it factual, limited, and verifiable. Do not overshare. Give the minimum accurate explanation needed for the specific question and keep unrelated personal details out of scope. If you want a deeper dive, read How to Hire Your First Salesperson.
When the request lands, resist the urge to rush. Before you submit sensitive data, verify three things: who initiated it, what is being checked, and why each field is needed for this engagement. If any of that is unclear, pause and ask.
The sequence stays the same: review consent, ask clarifying questions, then submit through the right channel. What changes here is your level of control.
Start with the sender and the consent document, not the form fields. Confirm the screening provider name, the official submission portal, and the client contact who can validate the request.
A quick alignment check can catch problems early. The sender domain, the provider named in the consent, and the submission URL should all line up. If the request is forwarded informally, sent from a generic address, or asks for identity documents by email, stop until you get confirmation and a secure path. Keep a copy of what you authorized, including the signed consent and any submission confirmation.
Use purpose and minimum necessary data as your filter. Ask for a clear connection between each requested field and the stated check.
| Request area | What to confirm | Potential overreach signal | How to respond |
|---|---|---|---|
| Identity verification | Which exact identifiers are required for this check | Extra identifiers without a clear purpose | Ask which exact identifiers are required and whether a narrower set works |
| License/certification/compliance status | Which claimed credentials are being verified | Requests unrelated to your actual services | Offer the exact credentials you represented and ask to limit review to those |
| Education/work history | Which role-related claims are being verified | Open-ended requests for unrelated history | Ask them to verify only credentials or roles used in your proposal or contract |
| Credit/driving/drug/medical/demographic fields | The specific check and purpose for each field | Broad requests without a clear role-specific reason | Ask how each field is used and request a narrower substitute where possible |
If the scope still feels unclear after clarification, pause and request written scope before submitting additional data. If that issue is already active, read What to Do If You've Been Misclassified as an Independent Contractor.
You do not need a long negotiation every time. A few reusable questions can surface whether the process is well run.
| Focus | Template 1 | Template 2 |
|---|---|---|
| Process clarity | Can you confirm who initiated this request and the screening provider name? | Please send the official submission link and instructions for this engagement. |
| Scope relevance | I see a request for [field]. Which checks will use it, and how is it relevant to this role? | Is there a narrower document or data point that satisfies the same requirement? |
| Data handling and security | I only submit sensitive data through an official secure portal. Please share that link. | Will I receive a copy of the consent and submission confirmation for my records? |
Process clarity
Scope relevance
Data handling and security
If no one can explain what is being checked or why a field is needed, do not submit that field yet.
Loose handling can create improper disclosures. In HIPAA-covered contexts, those disclosures can trigger notifications to individuals, HHS, and sometimes the media. Treat submission like any other sensitive client process: keep the scope tight, use the right channel, and preserve a record of what happened.
A useful security model comes from the HIPAA Security Rule, which is specific to electronic protected health information (ePHI). It emphasizes administrative, physical, and technical safeguards and reinforces the discipline of using official, secure websites for sensitive data. The HHS summary is an overview and does not address every detail of every provision, but the practical takeaway is still clear: reduce avoidable exposure by controlling channel, scope, and documentation. In this phase, the goal is controlled execution: clear scope, minimum necessary data, and proof of what you agreed to.
You might also find this useful: A Guide to 'Duty of Care' for a Company with Global Employees. If you want your screening expectations in writing before onboarding starts, draft a clean scope and data-handling addendum with the SOW Generator.
Submission is not the finish line. Once data is sent, your job is to close the loop: get the result, verify key fields against what was requested, and document all follow-up.
Move quickly here so the process does not drift. Right after submission:
Administrative errors can happen in portal-based workflows. A published Minnesota DHS incident showed incorrect supervision status and notice outputs before correction. Treat every status field and notice as part of your verification, not just the headline result.
Do not skim the report and move on. Compare it to what was requested for the screening and the actual engagement.
If the report includes medical history or genetic information, including family medical history, escalate. Also treat any sign of selective screening tied to protected characteristics as a compliance issue, not just a data-quality issue.
Once you find an error, treat the dispute like a process, not a complaint. If a third-party background-check company prepared the report, FCRA obligations apply. Use the dispute contact and correction process named in your report or portal. Before you submit a dispute, document the issue and gather the materials your provider asks for, such as:
Then log each interaction by date, channel, contact, and promised next step. For timing, use only the provider's verified timeline in your records and client updates: [provider-stated response timeline after verification].
| Outcome | Recommended action | Owner | Communication goal |
|---|---|---|---|
| No issues found | File report and submission confirmation together | You | Confirm completion with clean records |
| Administrative error | Submit documented correction request and monitor status and notices | You and listed dispute contact | Show procedural control and active resolution |
| Legitimate sensitive finding | Share a factual explanation and relevant corrective context | You | Preserve trust with clear, non-defensive communication |
Client updates should stay simple and steady. Use this structure: fact, action, next update. Example: "I reviewed the report and found an administrative discrepancy in [field]. I submitted a correction request through the listed dispute contact and included supporting documentation. I will provide the next update by [verified date or provider-stated timeline]."
If the finding is accurate but sensitive, keep the same structure and stay focused on relevance, resolution, and timing. Related: How to Check References for a Potential Hire.
The first question is not what form to fill out. It is whether you are being screened as an employee or as a contractor or vendor, and whether the request matches the actual project risk.
A lot of background-check guidance is framed around employee screening. If you are onboarding as a contractor, ask what the client actually needs to verify for this engagement. For contractor engagements, scope is often narrower and tied to what is necessary for the project and access involved. If the request goes beyond that, ask why each category is necessary for this contract.
In the U.S., the distinction matters because FCRA defines employment purposes around evaluating someone as an employee. If a third-party screening company is used for employment decisions, FCRA notice and written-authorization steps apply. If you are not being screened as an employee, ask which business basis is being used and how the scope matches the transaction.
The legal label matters less than the practical checkpoint: match the basis, the scope, and the dispute path before you send sensitive data.
| Issue | U.S. FCRA context | GDPR / UK GDPR context |
|---|---|---|
| Legal basis to run the check | If a third-party company prepares a report for employment decisions, FCRA applies and requires notice and written permission before obtaining the report. FCRA also includes a permissible-purpose path tied to a legitimate business need in a transaction initiated by the consumer. | A lawful basis must be selected before processing starts, and it should be documented. Do not assume a signature always means consent is the lawful basis. |
| Scope limit | Scope should match the stated purpose and permissible use. Ask why each requested category is needed for the engagement. | Data minimisation applies: data must be adequate, relevant, and limited to what is necessary for the stated purpose. |
| Access and correction | In employment screening, before adverse action, you should receive a copy of the report and the FCRA summary of rights. For errors, consumers generally contact both the reporting company and the information furnisher. | Individuals have rights of access and rectification, so you can request a copy of your data and correction of inaccuracies. |
| Who handles disputes | The reporting company investigates disputes submitted to it, and consumers generally contact both the reporting company and the information furnisher. | Use your access and rectification rights with the organization handling your data. In the UK, you can complain to the ICO, but the ICO cannot award compensation. |
Cross-border screening gets messy when the entity, vendor, and data path are vague. Before you share anything sensitive, confirm these four items in writing:
| Checkpoint | What to confirm |
|---|---|
| Client entity jurisdiction | The legal entity, not just the brand or sales office |
| Screening vendor location | Where the vendor is based and whether it matches the entity named in your screening materials |
| Data transfer path | Where data will be sent or made accessible, including transfers outside the UK or EEA under Chapter V conditions |
| Retention expectations | How long reports and submitted identity documents will be kept |
Do not assume the contract-signing country tells the whole story. The client, the screening vendor, and the team with access to your file may all sit in different jurisdictions. Ask where your data will be stored or made accessible. If those routing and handling details are unclear, pause before sending more. If a secure portal is unavailable, ask for an encrypted file process instead of sending unprotected documents.
A cooperative tone works best here. You can keep the deal moving without giving up control. The process is usually smoother when the entity, purpose, and data path are clear before documents leave your hands.
For a step-by-step walkthrough, see Performance Reviews for Remote Employees When You Work as a Contractor.
The throughline is straightforward: treat screening as a controlled risk process, not as a trust test. Confirm scope, share only the data that is necessary, protect it during transfer and storage, and verify the result before you close the file.
Start with consent and scope. In U.S. employment screening, third-party checks are consumer reports under the FCRA. You should see a written stand-alone disclosure and be asked for written permission before a report is pulled. Where GDPR applies, use the same practical filter through data minimization: data should be adequate, relevant, and limited to what is necessary for the stated purpose. If a request is broad, bundled, or unclear, pause and ask before you sign.
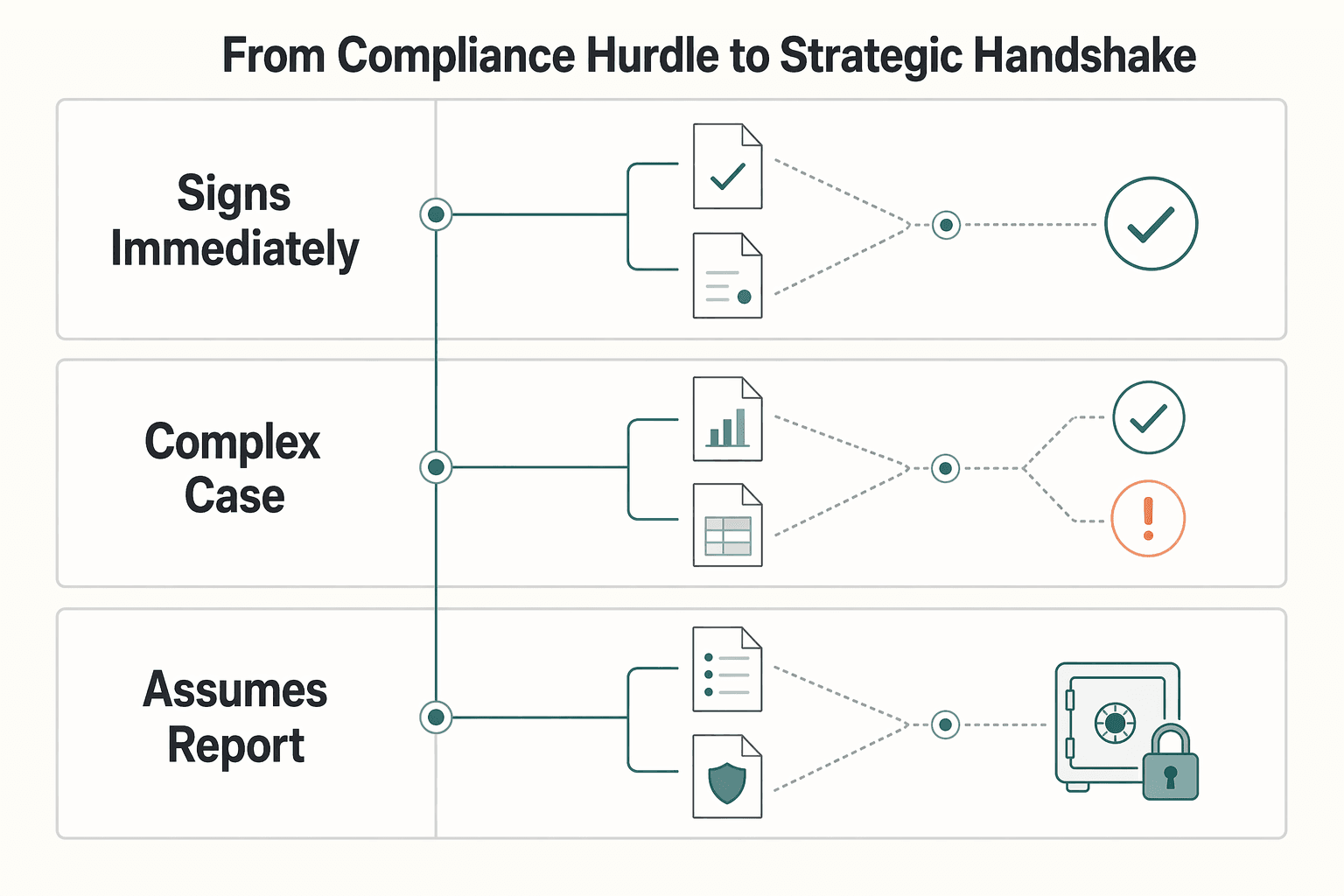
| Reactive behavior | Controlled, process-driven behavior | What this signals to the client |
|---|---|---|
| Signs immediately without reviewing scope | Reviews disclosure, purpose, and requested data categories first | You treat compliance as an operating process, not paperwork |
| Sends full identity documents through ordinary channels | Uses the employer's approved channel and shares only required information | You handle sensitive data responsibly |
| Assumes the report is final | Reviews the report when it affects a decision, checks for errors, and documents communications | You verify outcomes instead of leaving loose ends |
Many issues come from loose process, not from saying no. Over-sharing raises privacy risk, unclear consent expands scope, and skipping report review can leave inaccurate or incomplete information unchallenged. If a report is used in an employment decision, you should receive a copy before adverse action and can dispute inaccuracies with the reporting company. If you want an additional free copy after the decision, request it within 60 days.
Close it the same way every time: confirm scope, submit through the approved channel with appropriate safeguards, document the key communications, and close the loop after the report is issued.
For related context, see A Guide to Severance Pay for International Employees.
If your client checks now span multiple countries, map your compliance gates and payout flow with Gruv by starting a contact request.
If you earn more than £1,000 in a tax year as a sole trader, check whether you need to register. GOV.UK describes sole trader status as simple to set up and keep records for, but you still need to confirm whether registration applies to your case. Total your tax-year sole trader income and register if you meet the threshold.
For the tax year 6 April 2024 to 5 April 2025, the excerpt says you must tell HMRC by 5 October 2025, and late notification could lead to a penalty. Do not assume later years use the same deadline without checking current HMRC guidance. Verify the deadline for your tax year and put it in your calendar now.
If this is your first time filing, you must register for Self Assessment before using the online filing service. You also need your Unique Taxpayer Reference (UTR) to sign in and file. Confirm whether you already have a UTR before you start the filing process.
You may need to reactivate your Self Assessment account before filing. If you file without reactivating, your return may be delayed. Test account access early so you can fix issues before deadlines.
Keep records such as bank statements or receipts so you can complete your return correctly. You can file online on or after 6 April following the end of the tax year, and the tax bill is due by 31 January. Collect your records in one place before you begin your return.
An international business lawyer by trade, Elena breaks down the complexities of freelance contracts, corporate structures, and international liability. Her goal is to empower freelancers with the legal knowledge to operate confidently.
Priya is an attorney specializing in international contract law for independent contractors. She ensures that the legal advice provided is accurate, actionable, and up-to-date with current regulations.
Educational content only. Not legal, tax, or financial advice.

Treat this as a protection problem first, not a label debate. If your work was treated as an independent contractor arrangement even though the relationship functioned differently, your first goal is to protect pay, rights, and records while you choose the least risky escalation path. You can do that without making accusations on day one, which often keeps communication open while you document what happened.

The decision to bring on your first salesperson begins not with a job description, but with a hard look in the mirror. This hire is an investment that goes far beyond salary; it's a strategic commitment of cash, time, and trust. Get this wrong, and you risk not only a significant financial loss but also damage to your brand and morale. Get it right, and you build the foundation for scalable growth.

If you are searching for **how to check references**, you probably are not trying to complete a hiring formality. You are trying to understand what could go wrong if the hire goes wrong. A good process will not remove all hiring risk. It can reduce selection errors by verifying critical employment information and testing whether past performance fits the work you actually need done.